
In today's digital landscape, small and medium-sized businesses (SMBs) confront a formidable challenge: navigating the intricate world of IT services that are vital for their success. Understanding the essential IT services available is not just beneficial; it’s crucial for enhancing operational efficiency and protecting sensitive data from escalating cybersecurity threats.
With a plethora of options and diverse service providers, how can SMBs ensure they choose the right IT partner that aligns with their unique needs and objectives?
This article explores the key criteria for selecting IT services that empower SMBs to thrive in 2025 and beyond.

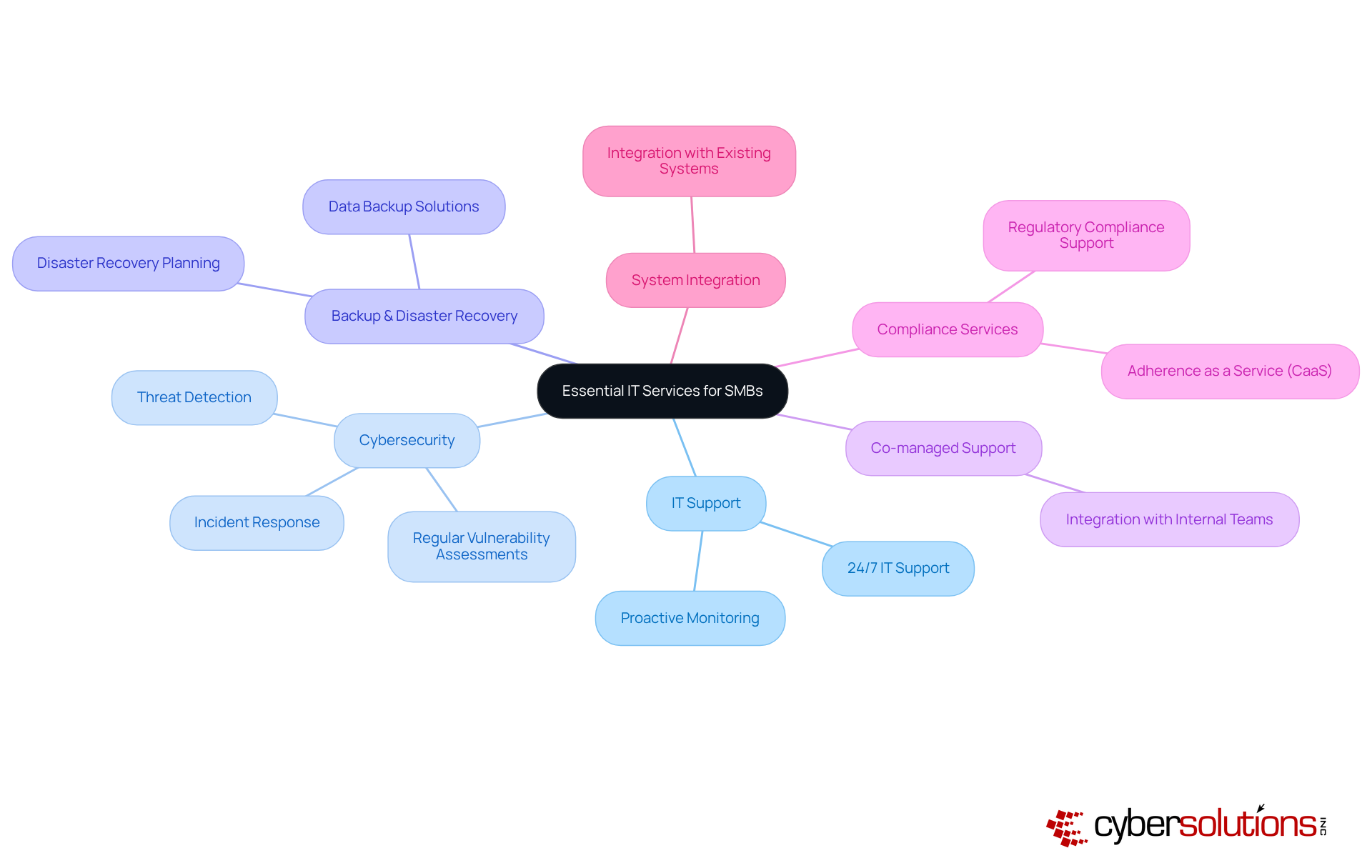
In today's digital landscape, the importance of a robust cybersecurity framework cannot be overstated, especially for organizations handling Controlled Unclassified Information (CUI) and Federal Contract Information (FCI). Ensuring compliance with rigorous regulatory standards is not just a requirement; it’s essential for maintaining eligibility for lucrative government contracts. Organizations must seek suppliers that provide proactive threat detection and monitoring, including extensive 24/7 network oversight and alert services to thwart potential threats before they escalate.
Moreover, evaluating a supplier's incident response plan and recovery strategies is crucial. A strong incident response capability, such as a 24-hour on-site support team, can significantly mitigate damage during a cybersecurity incident. This layered approach - encompassing endpoint isolation, malware removal, and user training - facilitates a faster and more complete recovery.
It's imperative to verify that the provider adheres to relevant regulations and standards, such as NIST guidelines and CMMC levels, which are critical for federal data protection. Regular security audits and evaluations should be integral to their protocol, ensuring ongoing adherence and security effectiveness.
Additionally, employee training programs on cybersecurity best practices are vital. These initiatives should focus on enhancing staff cyber hygiene and emphasizing the importance of application allowlisting, which proactively prevents unauthorized software from executing. This not only reduces vulnerabilities but also ensures compliance with data protection protocols.
Finally, confirm that advanced security technologies, such as firewalls and encryption, are in place to bolster network security. A comprehensive cybersecurity strategy that incorporates these elements will not only safeguard sensitive data but also enhance overall organizational resilience.

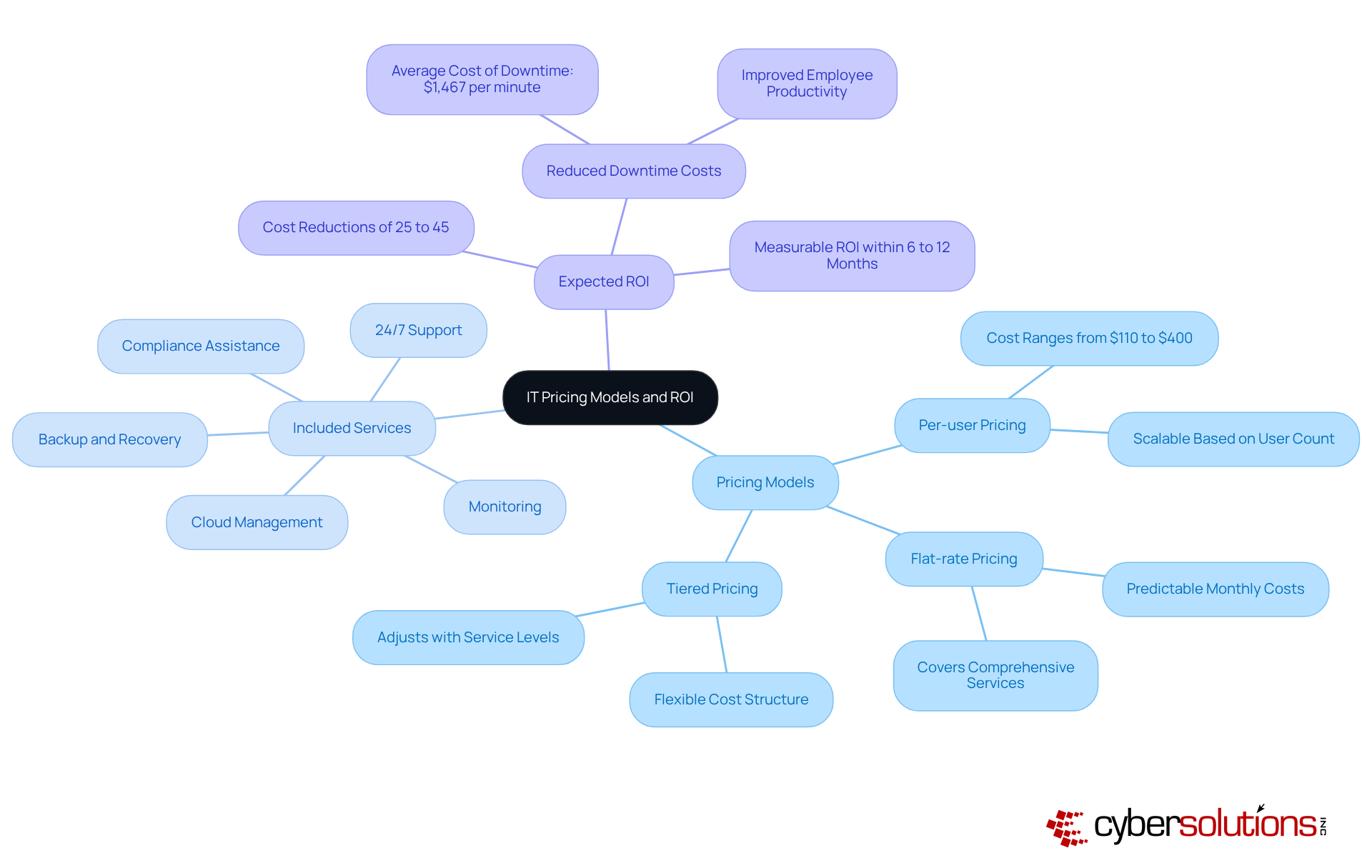
Understanding how IT services SMB is crucial for making informed decisions in today’s fast-paced business environment. With various pricing models available - flat-rate, per-user, and tiered pricing - organizations can choose the one that best fits their needs. Flat-rate pricing, for example, offers predictable monthly costs, simplifying budgeting and eliminating unexpected IT expenses. This model covers everything from email licenses to advanced cybersecurity measures, including comprehensive firewall and network security solutions, providing peace of mind in a single package.
Evaluating the offerings included in each pricing model is essential. Standard managed IT expenses should cover critical services such as:
However, some providers may exclude vital services, leading to unforeseen costs down the line. A thorough review of contracts is necessary to uncover any hidden fees or additional charges that could disrupt your budget.
Calculating the potential ROI from managed IT solutions is vital, especially when considering how IT services SMB by reducing downtime and enhancing operational efficiency. Research indicates that transitioning to managed solutions can lead to cost reductions of 25% to 45% for small and mid-sized companies, which highlights how IT services SMB can provide measurable ROI within 6 to 12 months. For instance, the average cost of downtime was $1,467 per minute in 2022, and managed service providers (MSPs) can significantly reduce unexpected network downtime through continuous monitoring and alerting. This proactive approach ensures that suspicious activities are detected and addressed before they escalate into serious threats, underscoring the financial benefits of effective IT management.
Adaptability in agreements and the capacity to scale offerings are also critical factors. As your business evolves, the ability to adjust IT resources without significant delays can be transformative. An MSP should provide scalable and flexible solutions that grow alongside your organization, ensuring your technology infrastructure aligns with your business objectives.
Ultimately, the long-term financial impact of IT services SMB can be profound. By partnering with a reliable managed service provider, organizations can shift their IT operations from a cost center to a strategic advantage, fostering innovation and efficiency while protecting against the complexities of modern cybersecurity threats.
Selecting the right IT services is not just important; it’s essential for the success of small and medium-sized businesses (SMBs). In today’s digital landscape, a strategic approach to choosing an IT service provider aligns directly with business goals while enhancing operational efficiency and security. By prioritizing criteria such as industry experience, service variety, and robust cybersecurity measures, SMBs can establish a solid IT framework that supports their growth and resilience against evolving threats.
Key factors stand out in this discussion:
These ensure that businesses are not only protected but also equipped to adapt to future challenges. Moreover, understanding pricing models and calculating potential ROI empowers organizations to make informed decisions that drive both financial and operational success.
Ultimately, investing in the right IT services transcends tactical choice; it signifies a strategic commitment to innovation and sustainability. By prioritizing cybersecurity and compliance, SMBs can safeguard their assets and enhance their competitive edge. Embracing these essential IT services is not merely advisable; it’s a call to action for businesses aiming to thrive in an increasingly digital landscape. This commitment ensures they remain agile and resilient in the face of ongoing challenges.
What is the first step in selecting an IT service provider?
The first step is to clearly outline your business requirements and goals to ensure alignment with IT solutions, which is crucial for establishing a robust cybersecurity framework.
Why is it important to investigate potential suppliers' industry experience?
Investigating potential suppliers' industry experience is important because familiarity with your sector can significantly enhance their relevance and effectiveness in addressing your unique challenges.
What should I assess regarding the variety of services offered by IT providers?
You should assess the variety of services and specialties available from professionals to ensure they can fulfill your specific needs, particularly in the context of evolving cybersecurity threats.
Why are certifications and compliance important when selecting an IT service provider?
Certifications and compliance with industry standards are essential for maintaining security and operational integrity in your organization.
How important is customer support when choosing an IT service provider?
Customer support and response times are vital for minimizing downtime and addressing issues promptly, especially in critical situations.
What should I look for in client testimonials and case studies?
Look for client testimonials and case studies to evaluate the entity's track record and effectiveness in similar circumstances, providing insight into their capabilities.
Why should I ensure the provider offers scalable solutions?
Ensuring the provider offers scalable solutions is important so that they can grow alongside your operations and accommodate future needs without significant disruptions.
What security measures should I verify with an IT service provider?
You should verify their security measures and incident response capabilities, particularly in light of increasing cyber threats that can impact your organization.
How can I avoid unexpected expenses when selecting an IT provider?
To avoid unexpected expenses, consider their pricing model and clarity to ensure a clear understanding of agreements, which is crucial for financial planning.
Why is it beneficial to schedule consultations with potential IT providers?
Scheduling consultations allows you to gauge their understanding of your needs and their ability to provide tailored solutions, ensuring a partnership that aligns with your strategic goals.