
In a world where cyber threats hide in the shadows of the internet, the importance of dark web monitoring is more critical than ever. Organizations can gain invaluable insights into potential breaches and compromised data, empowering them to take decisive action against increasingly sophisticated cybercriminals.
But with a multitude of providers offering different features, benefits, and pricing structures, how can businesses determine which dark web monitoring service aligns best with their specific needs?
This comparative analysis explores the offerings of four leading companies, equipping readers with the knowledge necessary to make informed decisions in protecting their digital assets.
In today's digital landscape, the importance of cybersecurity cannot be overstated, especially when it comes to dark web monitoring. This ongoing examination of the concealed parts of the internet - known as the hidden web - plays a crucial role in detecting and tracing compromised information, such as stolen credentials and sensitive corporate data. By adopting this proactive strategy, organizations can identify potential threats before they escalate into significant breaches. In fact, by 2025, entities with compromised credentials found on the hidden web will face a staggering 2.56 times greater risk of experiencing a cyberattack.
At Cyber Solutions, we offer services that combine automated tools with human intelligence. Our approach gathers insights from various underground web sources, including forums and marketplaces where illegal activities thrive. These services provide early warnings about data breaches, enabling businesses to take swift action to mitigate risks and protect their assets. Starting in 2025, more organizations are recognizing the necessity of these services, with many integrating them into their cybersecurity strategies.
Experts agree that dark web monitoring is vital for maintaining a robust security posture. The alarming surge in data breaches - a staggering 82% increase in 2022, totaling an estimated 15 billion - underscores the persistent threat posed by cybercriminals. Moreover, identity theft accounts for over 65% of all illegal activities observed on the hidden web, further emphasizing the urgency of these oversight services. By leveraging deep web surveillance alongside our comprehensive security solutions - such as continuous network monitoring, alerts, threat intelligence, email security, and firewalls - companies can stay ahead of potential breaches and enhance their overall cybersecurity framework. This proactive stance ensures they are better equipped to respond to incidents. As Baber Amin, Chief Product Officer at Anetac, aptly notes, organizations must address threats to both human and non-human identities to effectively safeguard their data.

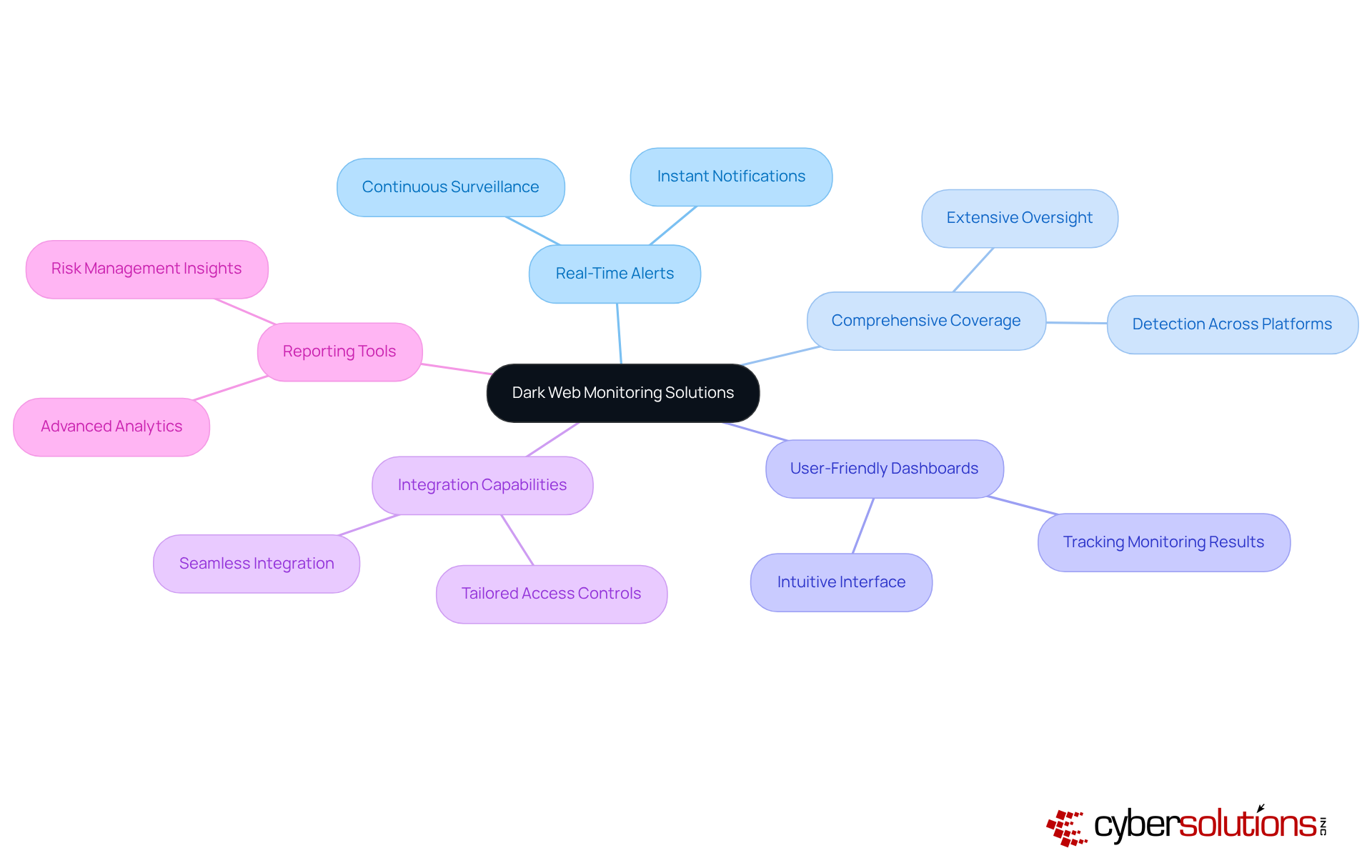
In today's digital landscape, cybersecurity is paramount, especially for organizations navigating the complexities of the dark web. When evaluating solutions, several key features emerge as essential:
By carefully assessing these attributes, organizations can pinpoint which companies best meet their operational needs and security objectives.
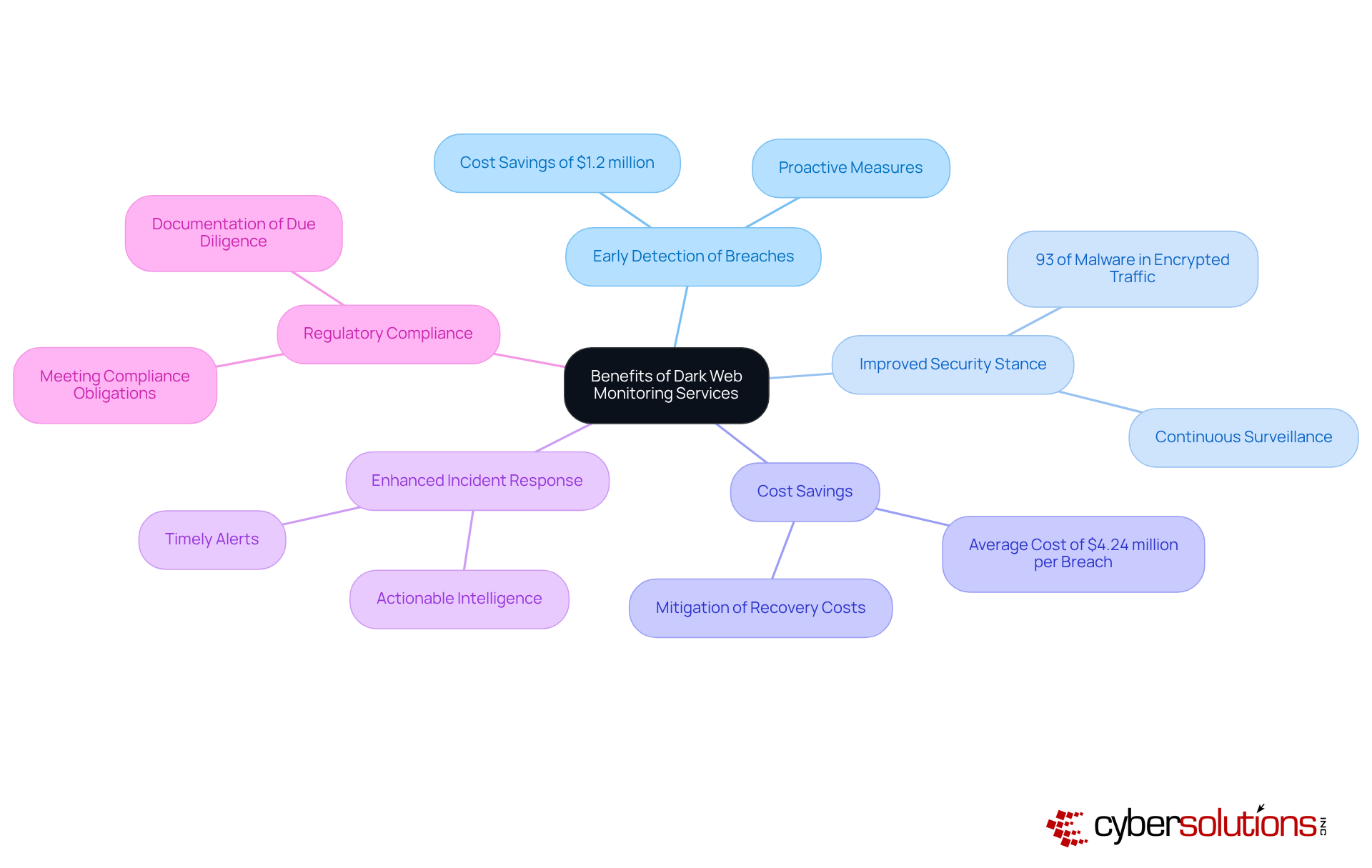
The advantages of dark web monitoring services are not just beneficial; they are essential in today’s cybersecurity landscape:
These advantages underscore the necessity of investing in dark web monitoring services as a critical element of a robust cybersecurity strategy, especially as organizations confront evolving risks in 2025.
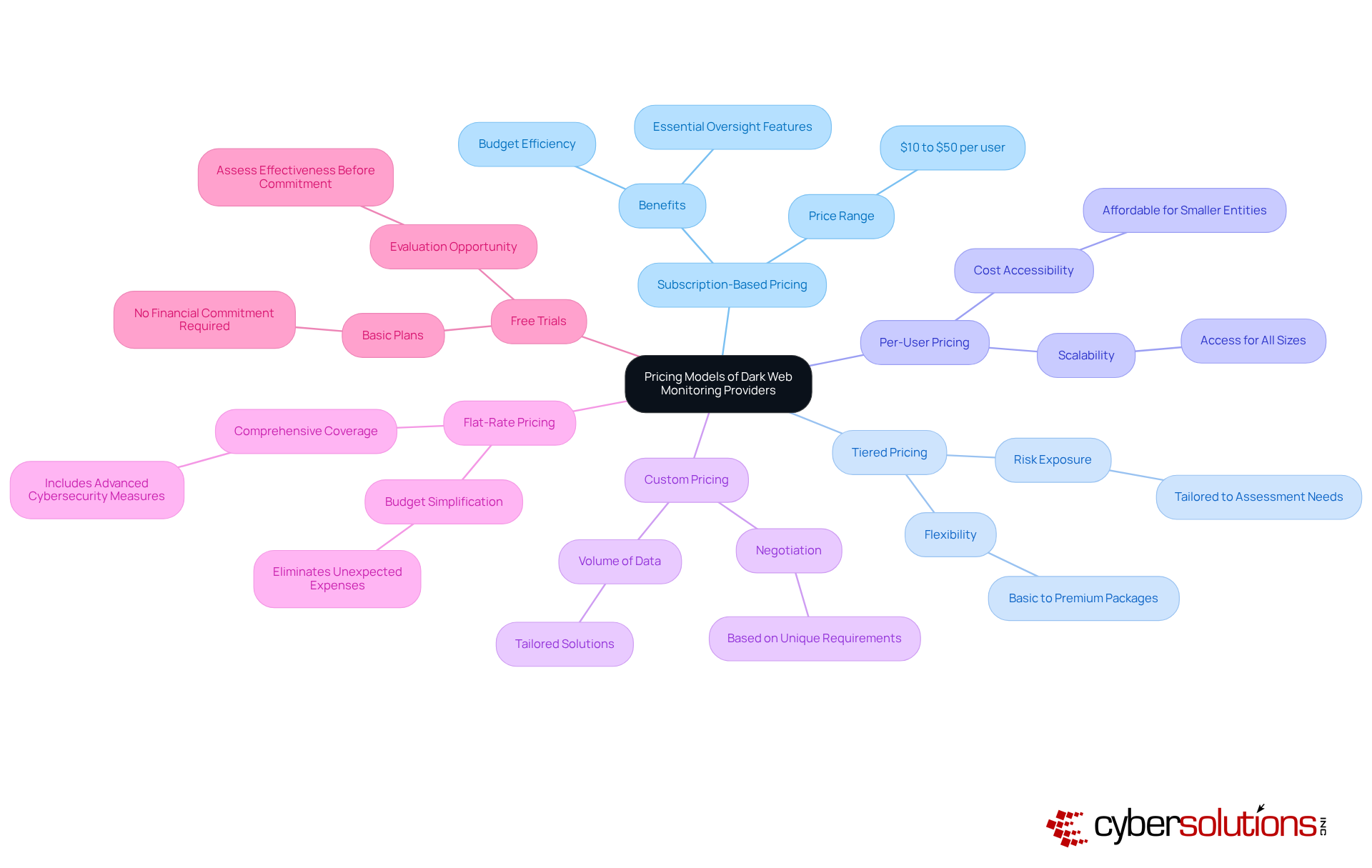
In today's digital landscape, understanding the pricing models for dark web monitoring services is essential for organizations aiming to safeguard their assets against cyber threats. With the increasing prevalence of data breaches, it's crucial to make informed decisions.
By carefully analyzing these pricing models, organizations can identify options that provide solutions aligning with their budget while ensuring robust protection against evolving cyber threats. Are you ready to take the next step in securing your organization?
In today’s digital landscape, the importance of cybersecurity cannot be overstated. Organizations are increasingly aware of the critical need to protect sensitive data from emerging threats, particularly through dark web monitoring. By leveraging advanced monitoring solutions, businesses can proactively identify vulnerabilities and respond to potential breaches before they escalate. This proactive approach not only strengthens their security posture but also safeguards their assets in an ever-evolving threat environment.
This article has delved into the essential features of dark web monitoring services, including:
These elements are crucial for effective cybersecurity. The benefits of these services-such as early detection of breaches, improved incident response, and significant cost savings-underscore their vital role in defending against the sophisticated tactics employed by cybercriminals. Moreover, understanding various pricing models allows organizations to make informed decisions that align with their operational needs and budget constraints.
As the threat landscape continues to evolve, investing in dark web monitoring services is not merely a strategic choice; it is an essential step toward securing organizational assets and ensuring compliance with regulatory demands. Embracing these solutions empowers businesses to navigate the complexities of cybersecurity effectively, keeping them one step ahead of potential threats. Taking action now can significantly mitigate risks and enhance overall security in the face of an uncertain future.
What is dark web monitoring?
Dark web monitoring refers to the ongoing examination of the hidden parts of the internet to detect and trace compromised information, such as stolen credentials and sensitive corporate data.
Why is dark web monitoring important for organizations?
It helps organizations identify potential threats before they escalate into significant breaches, reducing the risk of cyberattacks associated with compromised credentials.
What services does Cyber Solutions offer for dark web monitoring?
Cyber Solutions offers underground web surveillance services that use automated tools combined with human intelligence to gather insights from various underground web sources, including forums and marketplaces.
How does dark web monitoring benefit businesses?
It provides early warnings about data exposures, enabling businesses to take swift action to mitigate risks and protect their assets.
What is the expected trend in dark web monitoring by 2025?
By 2025, more organizations are expected to recognize the necessity of dark web monitoring services and integrate them into their cybersecurity strategies.
What alarming statistics highlight the need for dark web monitoring?
There was an 82% increase in stolen account credentials in 2022, totaling an estimated 15 billion, and identity theft accounts for over 65% of all illegal activities observed on the hidden web.
How can companies enhance their cybersecurity framework alongside dark web monitoring?
Companies can leverage deep web surveillance along with comprehensive cybersecurity solutions such as continuous network monitoring, alerts, endpoint protection, email security, and firewalls to stay ahead of potential breaches.
What is the overall goal of implementing dark web monitoring?
The goal is to ensure organizations are better equipped to navigate the evolving landscape of cyber threats and effectively safeguard both human and non-human identities.