
In today's world, where cyber threats are more prevalent than ever, the importance of cybersecurity compliance is paramount—especially for C-suite leaders who are responsible for maintaining organizational integrity. The intricate web of regulations, including HIPAA, PCI-DSS, and GDPR, presents both a formidable challenge and a unique opportunity for executives. By navigating these complexities, leaders can not only protect their organizations from potentially devastating breaches but also enhance their reputation and build trust with clients.
However, as compliance costs continue to rise and the stakes become increasingly high, how can leaders effectively implement strategies that safeguard their data? The answer lies in understanding the current landscape of cybersecurity threats and recognizing the implications for healthcare organizations. Cyber Solutions can play a crucial role in addressing these challenges, providing the necessary tools and expertise to fortify defenses.
By prioritizing cybersecurity compliance, executives can transform a daunting obligation into a strategic advantage, ensuring their organizations are not just compliant but resilient in the face of evolving threats.
is not just a technical requirement; it’s a critical component of operational integrity, especially in healthcare. With the rise of cyber threats, organizations face unique challenges that demand immediate attention from C-suite leaders. The stakes are high: a data breach can cost an organization millions and irreparably damage its reputation.
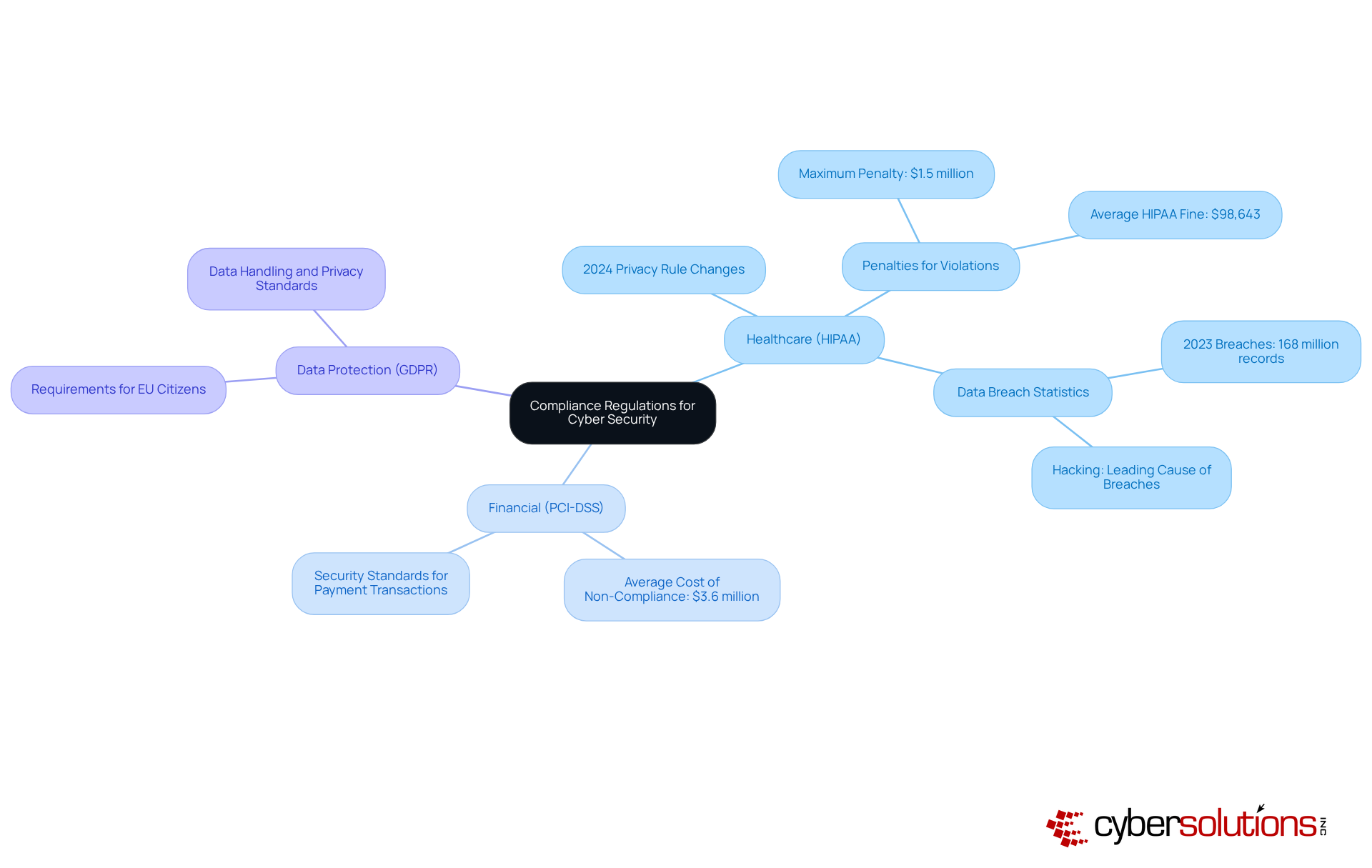
Key frameworks like HIPAA, PCI DSS, and GDPR provide essential guidelines for data management, which are vital for achieving compliance and helping entities mitigate risks associated with cyber incidents. For CFOs, the implications of non-adherence extend beyond financial penalties; they encompass the safeguarding of the organization’s reputation and the trust of clients and partners.
To navigate these complexities, efficient adherence strategies such as risk assessments and employee training emerge as invaluable solutions. CaaS offers comprehensive support for regulatory obligations, including evaluations, policy creation, oversight, and audit readiness. This approach allows small and medium-sized enterprises to access enterprise-level regulatory expertise, enhancing their compliance posture without the burden of hiring internal personnel, streamlining compliance while protecting against potential penalties. Sectors like healthcare, finance, manufacturing, and legal particularly benefit from CaaS due to their stringent regulatory standards.
Moreover, allowlisting is considered a gold standard in cybersecurity. By proactively preventing malware and unauthorized software from executing, this method not only reduces vulnerabilities but also ensures compliance with strict regulatory requirements. Allowlisting ensures that only authorized applications run on systems, further enhancing operational efficiency and overall security.
The financial implications are significant. For instance, the average cost of a data breach reached $4.45 million in 2023, with the industrial sector seeing the highest increase in breach costs. Non-adherence can be nearly three times as costly as compliance, underscoring the financial necessity of strong adherence measures. Organizations recognized for strong adherence practices often enjoy a competitive advantage, making them more appealing to clients and investors alike.
By prioritizing regulations and investing in ongoing training for cybersecurity teams, leaders can foster a culture of trust and resilience. This commitment not only enhances security but also positions organizations as leaders in their fields.

C-suite leaders must understand the critical regulations governing their organizations, especially in the context of cybersecurity in today's landscape. For healthcare organizations, compliance is non-negotiable; it enforces stringent protections for patient information. Recent updates, including the Health Insurance Portability and Accountability Act, have fortified these protections, particularly concerning reproductive health information.
On the other hand, there is the Payment Card Industry Data Security Standard, which outlines essential security standards for payment card transactions. In 2023, the average cost of non-compliance with PCI DSS was a staggering $3.6 million. This figure underscores the financial ramifications of inadequate security measures. Additionally, there is the General Data Protection Regulation, which protects the rights of EU citizens, imposing rigorous requirements on data handling and privacy.
By comprehending these frameworks, leaders can make informed decisions to allocate resources effectively and establish necessary controls, mitigating legal risks while enhancing operational resilience. Real-world examples, such as the successful implementation of compliance programs in various financial institutions, illustrate the effectiveness of adhering to these standards in safeguarding sensitive information.
Ultimately, by prioritizing compliance, businesses not only avoid hefty penalties but also build trust with clients and stakeholders. Are you prepared to navigate these complex regulations and protect your organization?
In today’s digital landscape, the importance of cybersecurity in healthcare cannot be overstated. C-suite leaders must take decisive action to safeguard their organizations against ever-evolving threats. A risk assessment is essential to identify vulnerabilities within the organization, laying the groundwork for a robust compliance program that meets industry standards.
Human errors account for a significant portion of data breaches, making training crucial. Organizations that prioritize cybersecurity awareness can achieve an impressive reduction in incidents. This statistic underscores the necessity of fostering an educated workforce, which is vital in defending against attacks.
Moreover, leveraging technological solutions that automate oversight can streamline processes and ensure ongoing compliance with regulations. Tools like Security Information and Event Management (SIEM) systems enable real-time monitoring, which are indispensable as regulatory requirements and threats evolve. Regular audits and evaluations are necessary to assess the effectiveness of regulatory measures, allowing organizations to make essential adjustments and maintain a proactive stance toward potential risks.
By cultivating a culture of security awareness and implementing structured training programs, organizations can significantly enhance their defenses and mitigate the risks associated with emerging cybersecurity threats. Are you ready to take the necessary steps to protect your organization?
Ongoing monitoring is not just important; it’s essential for evaluating the effectiveness of cybersecurity measures and adherence protocols. C-suite leaders must establish a robust framework for compliance, leveraging tools that deliver real-time insights into both security posture and risk management. This proactive approach empowers organizations to swiftly identify and address vulnerabilities before they can be exploited.
With a staggering 80% of data breaches involving cloud-stored information, continuous monitoring is crucial for adapting adherence strategies effectively. By fostering an environment of continuous improvement and vigilance, organizations can significantly enhance their resilience against cyber threats while ensuring compliance in an increasingly complex landscape.
Tools and compliance measures are indispensable for maintaining oversight and ensuring adherence to frameworks like SOC 2 and ISO 27001. These tools not only streamline processes but also provide organizations with the agility needed to respond to evolving regulations and security challenges.
In a world where cyber threats are ever-present, the question remains: Are you doing enough to protect your organization? Embrace ongoing monitoring and the right tools to safeguard your data and ensure compliance.

Mastering cybersecurity compliance is not just a technical obligation; it’s a critical component of operational integrity that C-suite leaders must prioritize. In an era where cyber threats are escalating, understanding and implementing compliance frameworks like HIPAA, PCI-DSS, and GDPR is essential for safeguarding sensitive data and maintaining trust with clients and stakeholders.
Effective compliance strategies, such as Compliance as a Service (CaaS) and application allowlisting, can significantly mitigate risks and streamline adherence processes. Ongoing education and training for employees, along with continuous monitoring and assessment of cybersecurity measures, are crucial in fostering a culture of security awareness. The financial implications of non-compliance highlight the necessity of these strategies, as organizations excelling in compliance often enjoy enhanced reputational benefits.
C-suite leaders are called to take decisive action to strengthen their organizations' cybersecurity compliance. By embracing robust compliance frameworks, investing in employee training, and leveraging modern technology for continuous monitoring, leaders can protect their organizations from severe penalties while positioning them as trusted entities in their respective fields. The evolving landscape of cyber threats demands a proactive approach—are you prepared to lead your organization toward a secure and compliant future?
What is cybersecurity compliance?
Cybersecurity compliance refers to the adherence to key frameworks and regulations that guide data management and protect organizations from cyber threats. It is essential for maintaining operational integrity, particularly in industries like healthcare.
Why is cybersecurity compliance important?
Compliance is crucial because it helps organizations mitigate risks associated with cyber threats, protects their reputation, and avoids significant financial penalties. A data breach can cost millions and damage an organization's credibility.
What are some key frameworks for cybersecurity compliance?
Important frameworks include HIPAA (Health Insurance Portability and Accountability Act), PCI-DSS (Payment Card Industry Data Security Standard), and GDPR (General Data Protection Regulation). These provide essential guidelines for data management.
What is Compliance as a Service (CaaS)?
Compliance as a Service (CaaS) is a solution that offers comprehensive support for regulatory obligations, including evaluations, policy creation, oversight, and audit readiness. It allows small and medium-sized enterprises to access regulatory expertise without the need for internal personnel.
Which sectors benefit most from CaaS?
Sectors such as healthcare, finance, manufacturing, and legal particularly benefit from CaaS due to their stringent regulatory standards.
What is application allowlisting and why is it important?
Application allowlisting is a security measure that prevents malware and unauthorized software from executing by ensuring that only authorized applications can run on systems. It is considered a gold standard in compliance cybersecurity and helps meet strict regulatory requirements.
What are the financial implications of non-compliance?
Non-adherence to cybersecurity regulations can be nearly three times as costly as maintaining compliance. The average cost of a data breach was $4.45 million in 2023, highlighting the financial necessity of strong adherence measures.
How can organizations enhance their compliance cybersecurity?
Organizations can enhance their compliance cybersecurity by prioritizing regulatory adherence, investing in ongoing training for cybersecurity teams, and fostering a culture of trust and resilience, which can lead to better business outcomes and improved reputational status.