
In today’s rapidly evolving digital landscape, server managed services stand as a critical pillar of robust IT infrastructure. C-suite leaders have a unique opportunity to not only enhance operational efficiency but also strengthen cybersecurity and ensure compliance with industry regulations through these specialized services. Yet, as cyber threats grow increasingly complex, the real challenge emerges: how do executives choose the right managed service provider and implement effective practices that align with their organizational goals?
Navigating this intricate landscape is essential for securing the future of their organizations while optimizing performance and reducing costs. With the stakes higher than ever, it’s crucial for leaders to consider the implications of their choices in managed services. Are they prepared to face the evolving challenges head-on? The right partner can make all the difference in achieving a secure and efficient operational environment.
In today’s digital age, the significance of robust server management in healthcare cannot be overstated. Managed services provide comprehensive oversight of IT infrastructure, delivered by specialized third-party providers. This ensures not only optimal performance but also heightened security and compliance. For organizations, grasping the critical nature of these offerings is essential, as they enable IT operations to run smoothly, allowing firms to concentrate on their core business activities without the burden of managing complex IT environments.
Effective server management is a game changer. It enhances operational efficiency while safeguarding sensitive data against ever-evolving cyber threats. With regulations in play, adherence to compliance standards is non-negotiable. By leveraging outsourced solutions, companies can realize significant cost savings. Research indicates that enterprises utilizing these options experience up to a 40% decrease in downtime, which translates to increased productivity and operational strength.
As the landscape of technology continues to evolve, the necessity for robust server management becomes increasingly clear. It’s not just a technical requirement; it’s a strategic priority for organizations aiming to thrive in a competitive environment. Are you ready to fortify your organization against potential threats and ensure compliance? Embrace managed services today and position your firm for success.
When it comes to managed services, the stakes couldn't be higher. Organizations must navigate a landscape fraught with unique challenges and regulatory requirements. This is where choosing the right managed service provider becomes crucial. An MSP must not only demonstrate expertise in the industry but also deliver a comprehensive suite of solutions that includes support and security.
A proven track record in delivering results is essential. Leaders should assess the MSP's ability to align with their organization's goals and compliance mandates. This involves a thorough inquiry into the provider's security measures, protocols, and customer support structure. For example, Cyber Solutions' rapid incident response team effectively restored 4,500 endpoints after a ransomware attack in a healthcare setting. This case highlights their capability to enhance security through a structured response plan and specialized expertise.
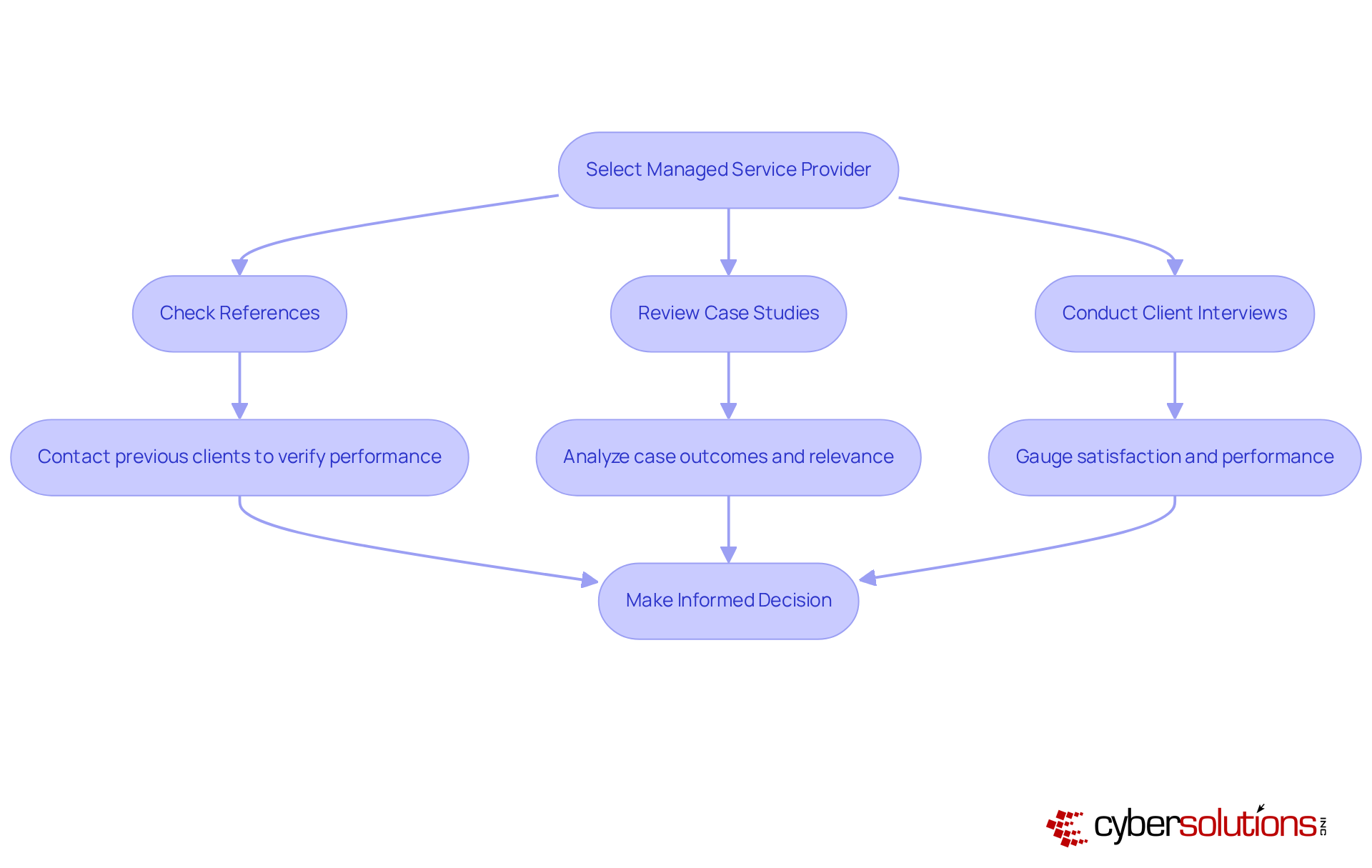
To make a well-informed decision, organizations should engage in a rigorous evaluation process. This may include:
By ensuring that the chosen MSP can effectively address both present and future needs, organizations can forge a partnership that significantly improves their IT infrastructure and security posture through proactive measures, ultimately driving business success.
The managed solutions market is projected to expand considerably, reaching $69.55 billion by 2025. This underscores the necessity of making informed decisions in this evolving environment. Cyber Solutions stands out as a robust contender for enterprises looking to enhance their IT infrastructure, ensuring they are well-equipped to tackle the challenges of today and tomorrow.
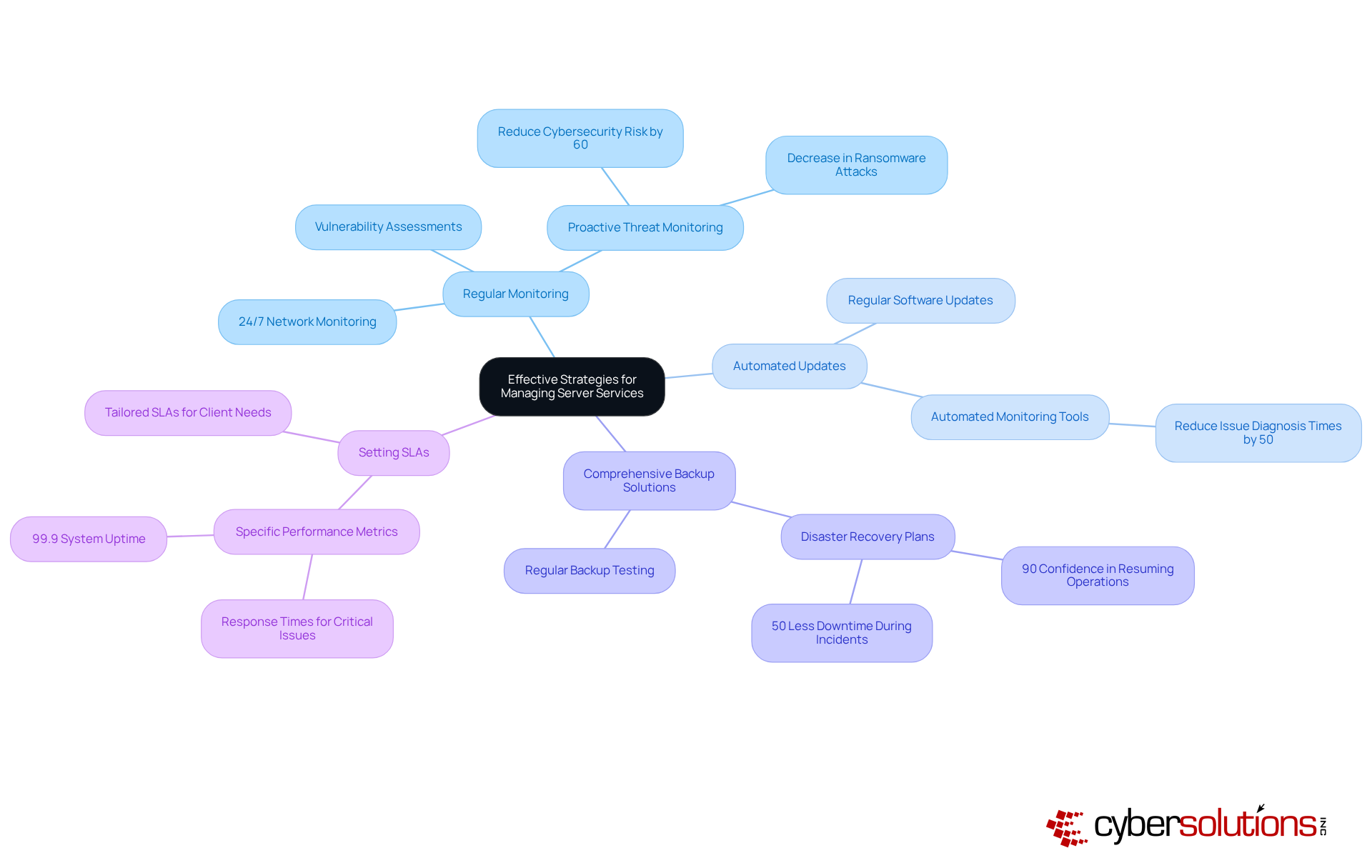
In today's digital landscape, the importance of cybersecurity cannot be overstated, especially in healthcare. Organizations must adopt a proactive strategy that encompasses:
Cyber Solutions stands out by offering monitoring and alert capabilities, ensuring that anomalies and potential vulnerabilities are swiftly identified. This enables prompt action to prevent downtime or breaches, safeguarding sensitive information.
Establishing clear communication is crucial for ensuring accountability and transparency. Tailoring SLAs to meet the unique needs of each client not only enhances service quality but also demonstrates a commitment to client success. Furthermore, robust security measures, including firewalls and intrusion detection systems, are essential for defending against cyber threats. Cyber Solutions' comprehensive firewall and network security solutions provide proactive protection against ransomware, phishing, and other malware attacks, adapting seamlessly as businesses grow.
Proactive strategies are vital practices that help identify and mitigate potential risks. They are more effective compared to reactive approaches. In fact, 98% of entities utilizing proactive IT monitoring report fewer system outages than those lacking it. For regulated sectors, understanding compliance requirements is essential; it streamlines the compliance process while protecting organizations from potential penalties.
By fostering a culture of continuous improvement and collaboration with the MSP, organizations can significantly enhance their server managed services. This ultimately leads to long-term operational success, ensuring that healthcare organizations remain resilient in the face of evolving cybersecurity threats.
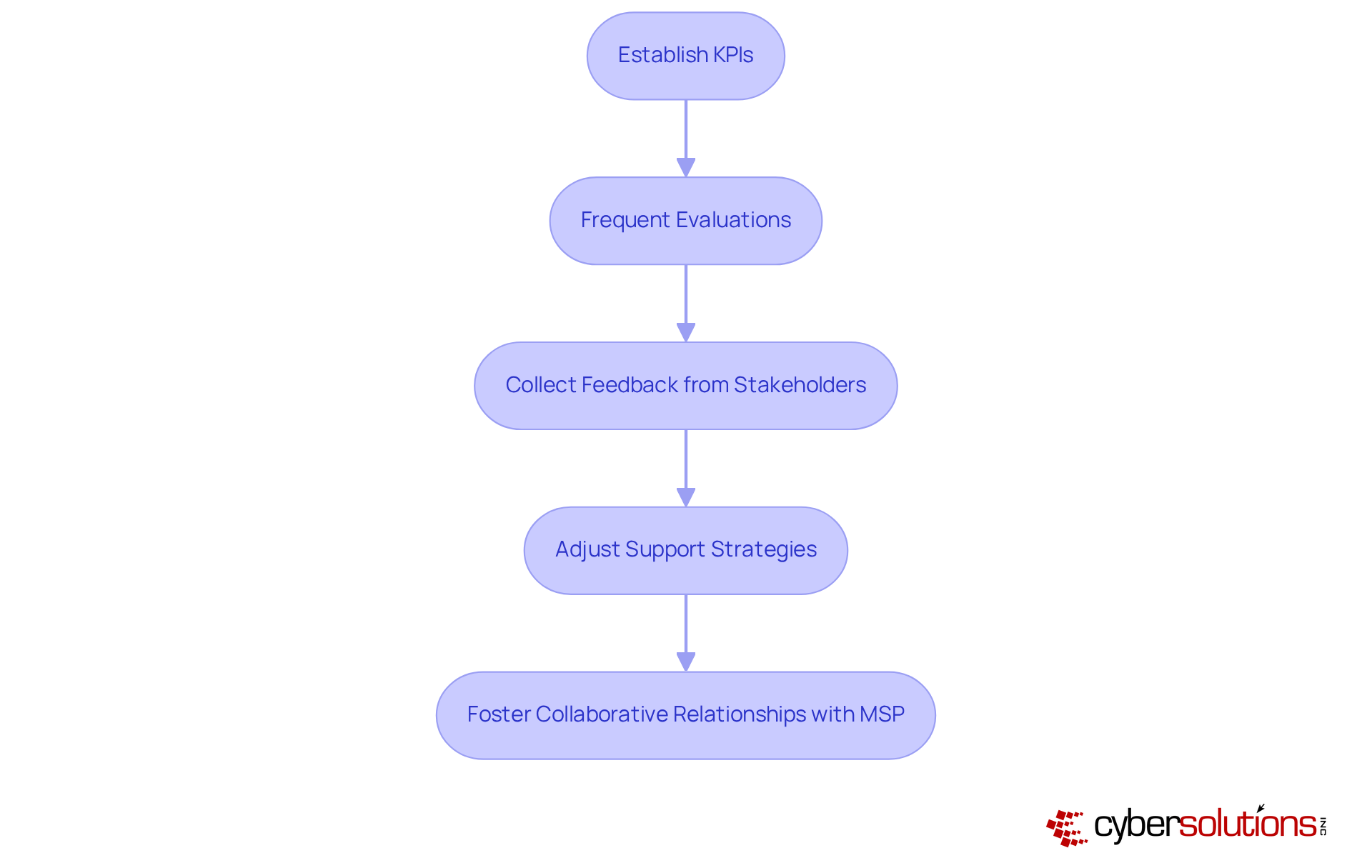
To effectively assess and enhance managed services, businesses must establish metrics that align with their strategic goals. Why is this crucial? Frequent evaluations of these metrics empower leaders to gauge the performance of their server and pinpoint areas for improvement. For instance, companies should aim to reduce Mean Time to Resolution (MTTR) from 6 hours to 3 hours. Achieving this goal can significantly boost efficiency and elevate customer satisfaction.
Collecting feedback from internal stakeholders and end-users is essential, as it yields valuable insights into service quality and user satisfaction. As Debra Garcia, an IT content writer, aptly states, "Clear KPIs help build accountability, guide resource allocation, and ensure the MSP’s work aligns with business objectives." Furthermore, organizations must remain agile, ready to adjust their support strategies in response to evolving business needs and technological advancements.
The shift towards outcome-based services is particularly noteworthy, emphasizing measurable results and value. By fostering a collaborative relationship with the MSP and prioritizing performance metrics, organizations can ensure their managed services remain effective and aligned with long-term objectives.
Robust server managed services are not just beneficial; they are essential for C-suite leaders who want to elevate their organizations' IT infrastructure. These services streamline operations and provide critical security and compliance, enabling businesses to concentrate on their core activities while alleviating the complexities of IT management. By grasping the strategic significance of server management, executives can position their firms to adeptly navigate the challenges of an ever-evolving digital landscape.
Key insights throughout this discussion underscore the importance of:
The focus on proactive cybersecurity measures, tailored SLAs, and ongoing collaboration with MSPs illustrates the comprehensive approach necessary to protect sensitive data and ensure operational efficiency. Furthermore, the potential for substantial cost savings and reduced downtime highlights the undeniable value of investing in these services.
The call to action is unmistakable: C-suite leaders must treat server managed services as a strategic imperative. By adopting these best practices and cultivating strong partnerships with capable providers, organizations can enhance their cybersecurity posture and drive long-term success and resilience in a competitive environment. The future of IT management hinges on proactive engagement, making it crucial for leaders to act decisively in optimizing their server management strategies today.
What are server managed services?
Server managed services refer to comprehensive oversight of server infrastructure provided by specialized third-party providers, ensuring optimal performance, security, and compliance with industry regulations.
Why are server managed services important for IT infrastructure?
They enhance operational efficiency, safeguard sensitive data against cyber threats, and allow companies to focus on core business activities without the complexities of managing IT environments.
How do server managed services contribute to cybersecurity in healthcare?
They provide robust cybersecurity measures, ensuring compliance with regulations like HIPAA and GDPR, which are critical for protecting sensitive healthcare data.
What are the benefits of using outsourced server management solutions?
Companies can achieve significant cost reductions, improved ROI, and experience up to a 40% decrease in downtime, leading to increased productivity and operational strength.
Why is server management considered a strategic priority for organizations?
As cyber threats evolve, effective server management becomes essential for organizations to thrive in a competitive environment and ensure compliance with regulations.
How can organizations benefit from embracing server managed services?
By fortifying their infrastructure against potential threats and ensuring compliance, organizations can position themselves for long-term success.