
The Cybersecurity Maturity Model Certification (CMMC) marks a crucial turning point in how organizations must tackle cybersecurity, especially those working with the Department of Defense. With the compliance deadline of November 10, 2025, fast approaching, C-Suite leaders face an urgent challenge: how to navigate this complex framework to protect sensitive information and retain eligibility for vital contracts.
Are executives prepared to align their strategies with CMMC requirements while confronting the numerous challenges of compliance? This article explores essential steps and best practices that leaders must embrace to ensure their organizations are not only compliant but also resilient against the ever-evolving landscape of cyber threats.
The CMMC framework is not just a framework; it’s a critical mandate from the Department of Defense designed to bolster the security of defense contractors. With the shift to digital operations, it’s imperative for organizations to fully understand the intricacies surrounding the compliance requirements.
This model comprises three distinct tiers, each delineating specific security criteria that organizations must satisfy to qualify for DoD contracts:
Leaders must align their strategies with these standards, as this alignment not only mitigates risks but also enhances overall security.
Organizations that actively engage with the Cybersecurity Maturity Model can significantly fortify their security posture, ensuring they remain competitive and eligible for future contracts. Are you prepared to meet these evolving challenges head-on?

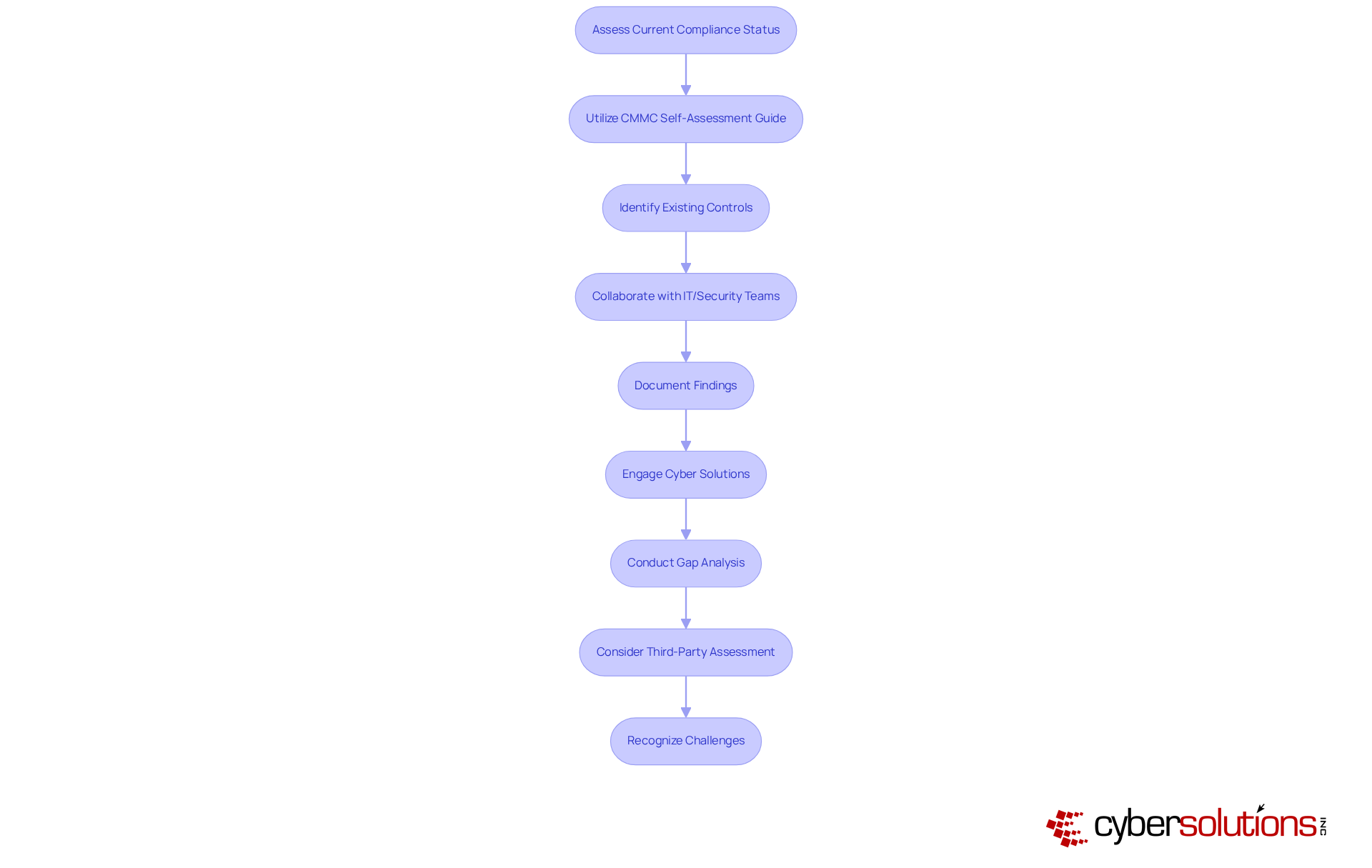
To navigate the complex landscape of compliance, organizations must prioritize their adherence to established frameworks. A comprehensive self-assessment aligned with your assigned level is essential. Start by utilizing the checklist from the Department of Defense, a vital resource for evaluating your current compliance status. Identify existing controls and pinpoint areas needing enhancement. Collaborate closely with your IT and security teams to gather data on current policies, procedures, and technologies in place. Thoroughly document your findings, as this will lay the groundwork for your regulatory roadmap.
Consider engaging Cyber Solutions for an in-depth initial evaluation and compliance strategy. This partnership can help identify discrepancies and provide tailored remediation strategies, including necessary policy revisions and system enhancements. Our offerings also include continuous adherence monitoring and risk evaluations, ensuring your business remains aligned with relevant standards. Additionally, enlisting a third-party consultant or a Registered Provider Organization (RPO) can yield an unbiased assessment of your adherence status, guaranteeing a comprehensive understanding of your preparedness for certification.
It's crucial to recognize the challenges within the certification framework, such as the increasing demand for assessors and rising costs, which can impact your adherence efforts. Furthermore, having a compliance plan is vital for managing and protecting sensitive information as part of the regulatory process. The complexity of compliance can vary significantly based on your entity's development and current practices, making it essential to assess your readiness. Statistics indicate that a significant number of organizations are conducting assessments due to the approaching deadline, underscoring the urgency for action. Lastly, consider insights from industry experts on evaluating compliance for regulatory alignment, which can be directly linked to the services offered by Cyber Solutions to enhance your strategy.
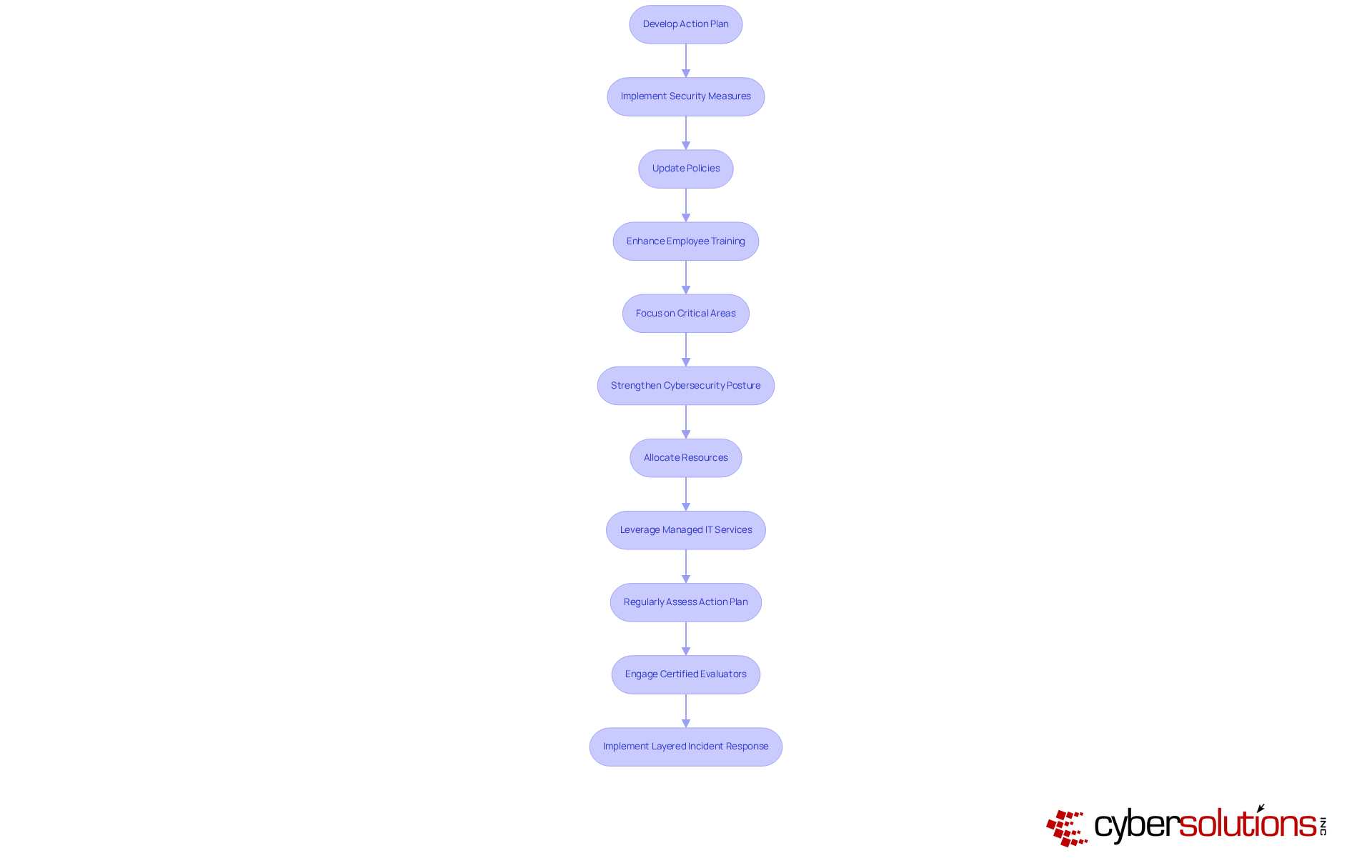
To effectively tackle regulatory gaps, it’s essential to develop a strategy that prioritizes the implementation of new security measures, updates to existing policies, and enhancements to employee training programs. Focus on critical areas such as access management, incident handling, and data security - these are vital for meeting compliance standards.
Given that compliance necessitates advanced security protocols to safeguard sensitive data, strengthening your security infrastructure is crucial. This not only mitigates risks but also provides a competitive edge in the defense contracting sector. Allocate resources judiciously, ensuring that your regulatory initiatives are in sync with your organization’s financial capabilities.
Consider leveraging technology solutions to facilitate the deployment of essential technologies and processes. This approach can bolster your regulatory efforts through continuous monitoring and automated notifications. Regularly assess and adjust your action plan to ensure alignment with upcoming deadlines, particularly the deadline for the effective November 10, 2028. Additionally, contractors must conduct audits and maintain records for at least six years post-assessment submission.
Engaging with Certified Evaluators (CCA) early in the process can provide invaluable insights and support throughout your compliance journey. Be aware of potential challenges in achieving compliance, especially given the increasing complexity and breadth of regulations. Implementing a layered approach to security, as demonstrated in successful case studies, can significantly enhance your organization’s recovery capabilities and overall security posture.
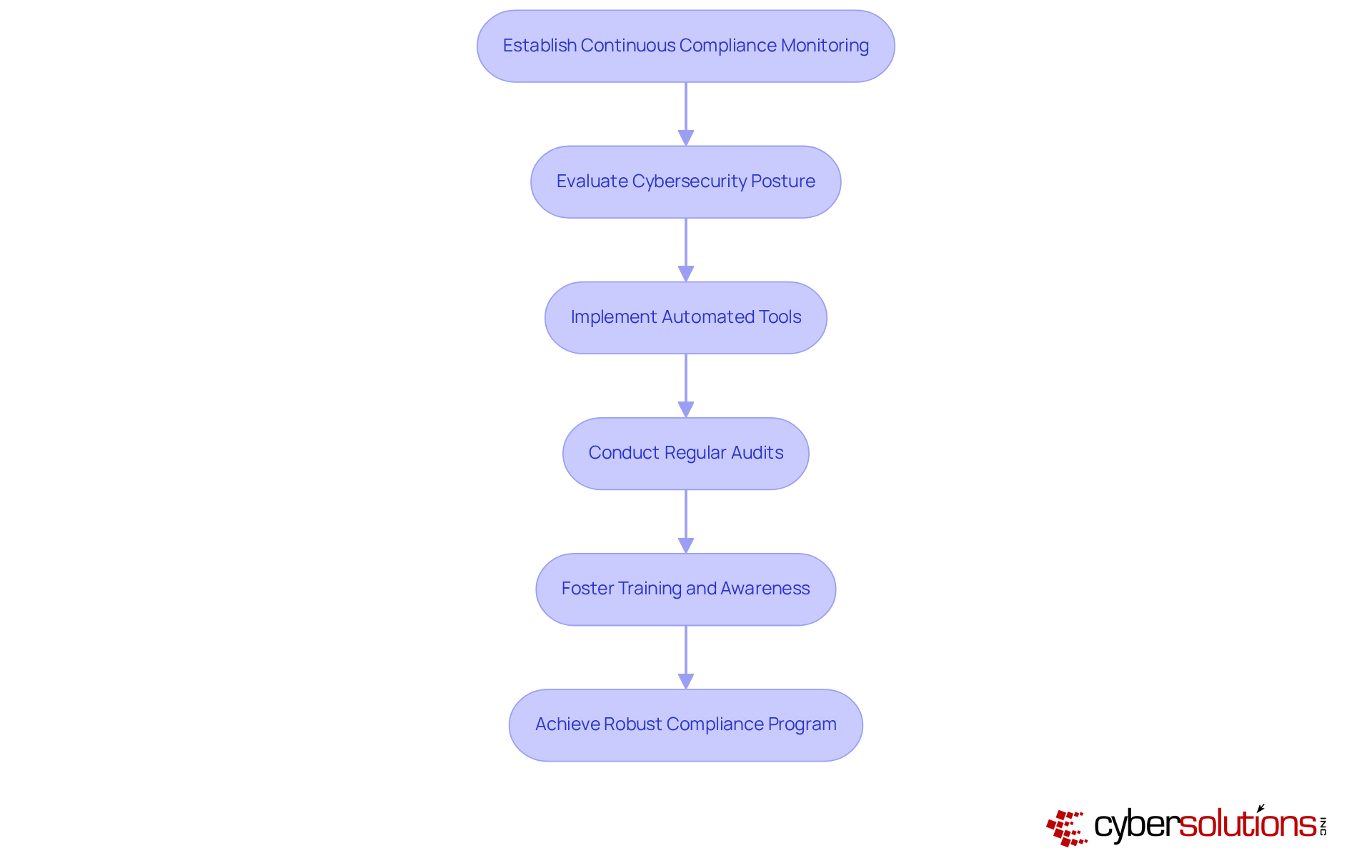
To maintain compliance with regulations, establishing a robust compliance program is vital. This program should regularly evaluate your security posture, ensuring that your organization remains vigilant against evolving threats. Monitoring tools are essential in this process, providing real-time monitoring of security controls and significantly enhancing compliance efforts. These tools not only simplify adherence efforts but also equip organizations with the agility needed to adapt to changing regulatory demands.
Regular audits and reviews are crucial to assess the effectiveness of your compliance measures. Scheduling these evaluations ensures that any gaps are promptly identified and addressed. Furthermore, fostering a culture of compliance through ongoing training keeps your team informed about the latest requirements and best practices. By prioritizing these strategies, organizations can effectively navigate the complexities of compliance and ensure they meet the standards to secure their eligibility for DoD contracts.
In a landscape where cyber threats are ever-present, the implications for organizations are profound. Are you prepared to face these challenges head-on? By implementing a comprehensive compliance strategy and leveraging advanced security tools, your organization can not only meet but also enhance its overall security posture.
Understanding the CMMC compliance framework is not just important; it’s essential for C-Suite leaders who must navigate the intricate landscape of cybersecurity regulations. With the deadline looming on November 10, 2025, organizations must prioritize their readiness to meet the stringent requirements set forth by the Department of Defense. This proactive approach not only safeguards sensitive information but also positions companies advantageously within the competitive realm of defense contracting.
To achieve compliance, organizations should follow essential steps:
Key insights highlight the importance of thorough self-assessments, the development of comprehensive action plans, and the integration of automated tools for ongoing compliance. By collaborating with IT teams and leveraging external expertise, organizations can effectively address gaps and enhance their cybersecurity posture.
The significance of CMMC compliance transcends mere regulatory adherence; it is a cornerstone of organizational resilience against evolving cyber threats. Embracing these strategies ensures compliance while fortifying an organization's overall security framework. C-Suite leaders must take decisive action now, reinforcing their commitment to cybersecurity excellence and securing their eligibility for future DoD contracts.
What is the Cybersecurity Maturity Model Certification (CMMC)?
The CMMC is a compliance framework mandated by the Department of Defense aimed at improving the cybersecurity posture of organizations that handle Controlled Unclassified Information.
What is the significance of the CMMC compliance deadline?
The CMMC compliance deadline, with mandatory audits starting on November 10, 2025, is critical for organizations to understand in order to align their cybersecurity strategies and remain eligible for DoD contracts.
How many tiers are there in the CMMC framework?
The CMMC framework comprises three distinct tiers, each with specific security criteria that organizations must meet to qualify for DoD contracts.
What does Level 1 of the CMMC focus on?
Level 1 of the CMMC emphasizes fundamental safeguarding practices.
What do Levels 2 and 3 of the CMMC entail?
Levels 2 and 3 introduce increasingly sophisticated security measures beyond the basic practices of Level 1.
Why is it important for leaders to align their cybersecurity strategies with CMMC standards?
Aligning cybersecurity strategies with CMMC standards helps mitigate risks and enhances overall compliance, which is essential for maintaining competitiveness and eligibility for future contracts.
How can organizations benefit from engaging with the CMMC?
Organizations that actively engage with the CMMC can significantly strengthen their security posture, ensuring they remain competitive and eligible for future contracts.