
Cybersecurity stands as a critical pillar of operational integrity amid the rising tide of digital threats. At the forefront of this battle is Endpoint Detection and Response (EDR), a technology that not only monitors and mitigates risks on endpoint devices but also revolutionizes how organizations formulate their security strategies. As businesses navigate an ever-evolving landscape of cyber threats, one pressing question emerges: how can a deep understanding and effective implementation of EDR solutions empower organizations to proactively defend against increasingly sophisticated attacks?
In today’s digital age, the stakes are higher than ever. Cyber threats are not just a nuisance; they pose significant risks to operational continuity and data integrity. For organizations, particularly in sensitive sectors like healthcare, the implications of a breach can be devastating. This is where EDR comes into play, offering a robust defense mechanism that not only detects threats but also responds in real-time, ensuring that organizations can maintain their operational integrity.
As we delve deeper into the unique challenges faced by organizations, it becomes clear that understanding EDR is not just beneficial - it’s essential. By leveraging EDR solutions, organizations can transform their approach to cybersecurity, turning potential vulnerabilities into fortified defenses. This proactive stance is crucial in a world where cyber threats are becoming more sophisticated and pervasive.
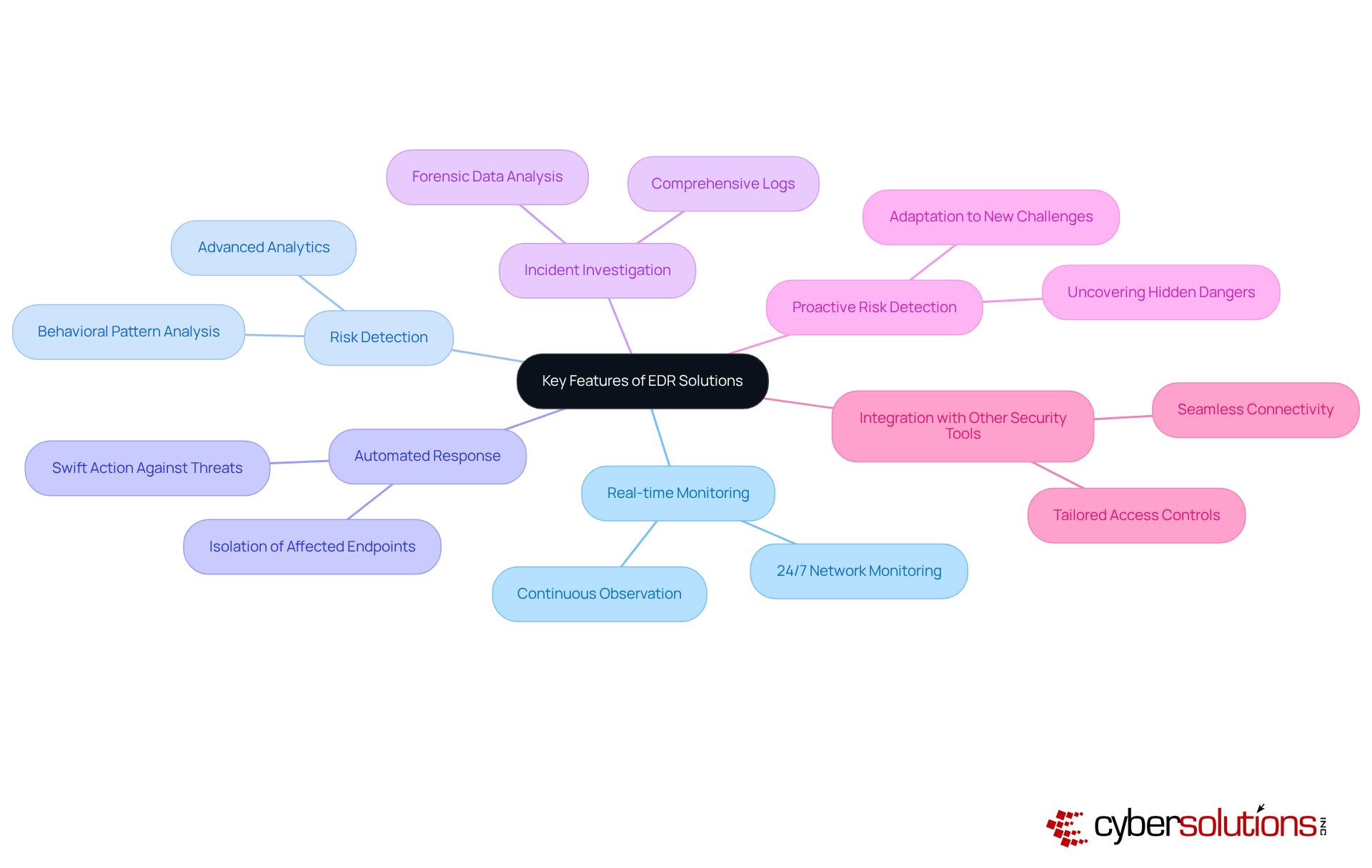
Cybersecurity is not just a necessity; it’s a critical component of modern business resilience. The definition of Endpoint Detection and Response (EDR) highlights how EDR stands at the forefront of this battle, continuously monitoring, detecting, and reacting to risks on endpoint devices like laptops, desktops, and servers. Unlike traditional solutions that rely heavily on malware signatures, EDR employs advanced detection techniques. This significantly enhances a company's security posture, making it indispensable in today’s threat landscape.
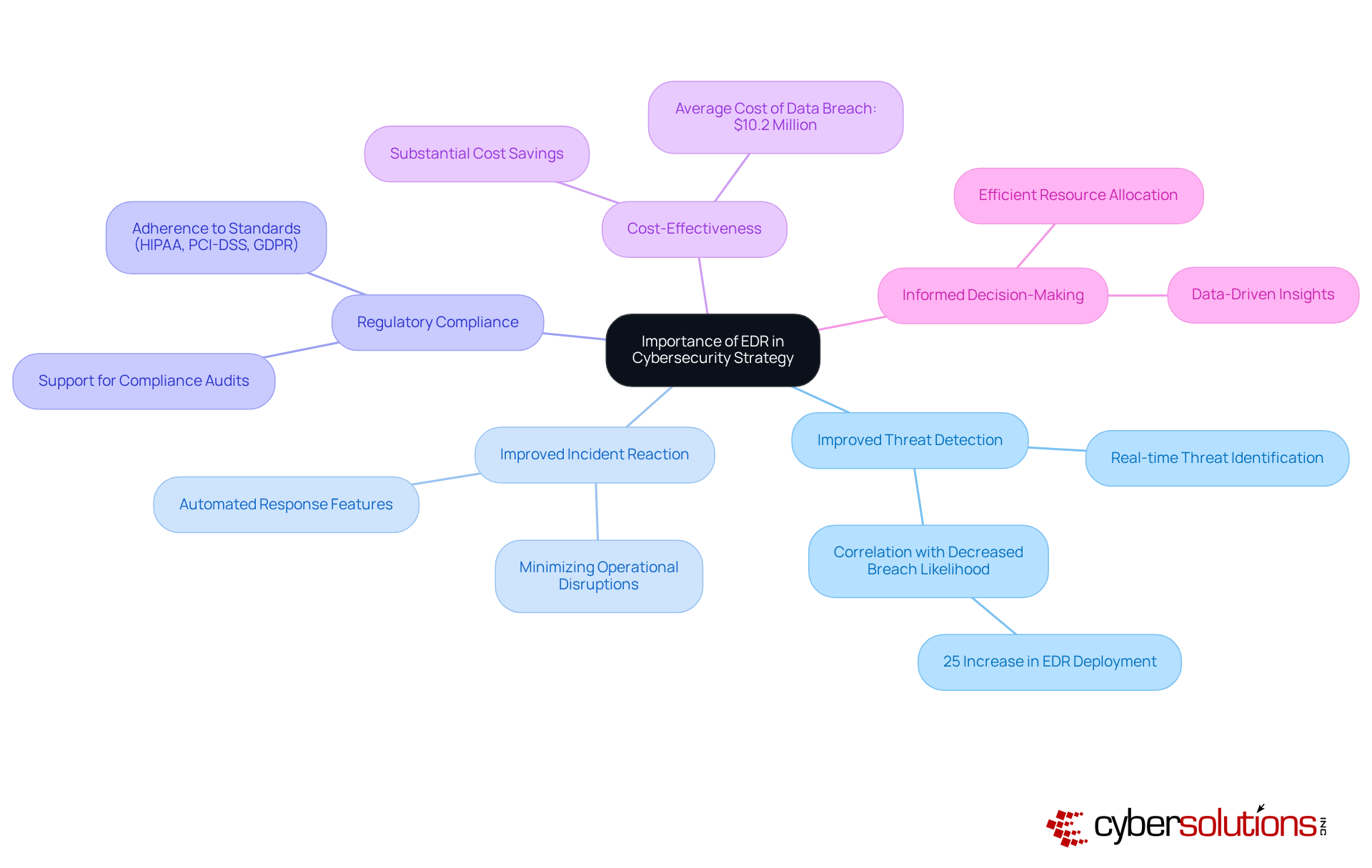
The impact of EDR on mitigating cybersecurity incidents is profound. Organizations that implement EDR can drastically reduce incident response times, with the average cost of downtime soaring above $53,000 per hour. By detecting and neutralizing attacks early, EDR can save businesses hundreds of thousands, if not millions, in damages. Furthermore, EDR provides visibility into endpoint actions, allowing teams to uncover incidents that might otherwise go unnoticed, thus responding effectively to emerging threats.
Key features of EDR technology include:
These capabilities empower teams to prioritize significant threats and respond swiftly, ensuring operational efficiency while effectively managing risks. For instance, a medium-sized company successfully leveraged EDR to isolate a PC during a ransomware attack, preventing data loss and maintaining uninterrupted operations.
In the words of cybersecurity experts, the consensus highlights that EDR solutions are essential for modern security strategies. They not only provide real-time insights into endpoint activities but also facilitate proactive measures, enabling organizations to shift from a reactive to a proactive cybersecurity stance. As cyber threats continue to evolve, understanding the importance of EDR is crucial for businesses that aim to bolster their resilience and protect sensitive data. Additionally, Cyber Solutions' EDR offerings are designed to adapt to new challenges and scale with business operations, ensuring tailored access controls and restrictions that meet specific organizational needs.

In today’s digital landscape, organizations face an unprecedented surge in cyber threats, including ransomware and malware. The shift to remote work and the growing number of connected devices have expanded the attack surface, making cybersecurity more challenging. The Endpoint Detection and Response (EDR) solution has emerged as a vital solution to these challenges, equipping organizations with the tools needed to identify and mitigate threats that slip past conventional defenses.
By integrating EDR into their cybersecurity frameworks, businesses gain enhanced visibility into endpoint activities, highlighting the potential risks. This capability allows them to detect and neutralize threats before they escalate into significant incidents. Such a shift represents a move towards a more proactive security posture, where understanding the threat landscape, along with continuous monitoring and rapid response, are paramount. For instance, organizations utilizing EDR have reported a marked reduction in the impact of ransomware attacks, with many successfully thwarting phishing attempts that exploit vulnerabilities associated with remote work.
As remote work continues to proliferate, the current situation highlights the increasing critical demand for robust cybersecurity measures. This underscores the necessity of implementing EDR solutions to protect sensitive data and uphold operational integrity. Are you prepared to safeguard your organization against these evolving threats?
Cybersecurity is not just a necessity; it’s a critical pillar for safeguarding healthcare organizations against evolving threats. With the rise of cyber attacks, the stakes have never been higher. Organizations must be equipped with robust solutions to protect sensitive data and maintain operational integrity, which is underpinned by understanding the importance of EDR.
The significance of EDR is evident in its impact on response times. Companies that incorporate investigation features in their detection tools have seen a 38% reduction in time-to-contain risks. In today’s fast-paced threat landscape, this efficiency is crucial. Organizations utilizing EDR report enhanced protective measures through automation and orchestration, enabling them to maintain operational integrity while effectively managing risks.
In today's digital landscape, understanding the importance of EDR is crucial in a cybersecurity strategy, especially as organizations face increasingly sophisticated cyber threats. The implementation of EDR indicates that it not only enhances security posture but also provides several key benefits that are vital for any organization.
Incorporating EDR into cybersecurity frameworks reflects the commitment to security, as it not only strengthens defenses but also aligns with broader business objectives, making it an essential component of modern security strategies. Additionally, leveraging Cybersecurity as a Service (CaaS) can provide businesses with the necessary support for audit preparation and continuous monitoring, ensuring adherence to regulatory standards and enhancing overall cybersecurity resilience.
Understanding Endpoint Detection and Response (EDR) is crucial for organizations determined to strengthen their cybersecurity measures in an increasingly complex digital landscape. EDR is not just an option; it’s a vital component of modern security frameworks, providing proactive monitoring, rapid response capabilities, and enhanced visibility into endpoint activities. As cyber threats continue to evolve, the importance of implementing EDR solutions becomes undeniable, empowering businesses to effectively combat potential vulnerabilities.
This article explores the multifaceted advantages of EDR, showcasing its ability to:
By integrating EDR into their cybersecurity strategies, organizations not only bolster their defenses but also align their security efforts with broader business objectives. Real-world examples illustrate how EDR can mitigate the impact of cyberattacks and support operational continuity.
As the digital threat landscape shifts, investing in EDR technology is imperative for organizations aiming to protect sensitive data and maintain operational integrity. Embracing these advanced solutions transcends mere compliance; it represents a strategic move towards resilience in the face of evolving cyber threats. Organizations are urged to evaluate their current cybersecurity posture and consider the integration of EDR solutions as a fundamental step in enhancing their overall security strategy.
What is Endpoint Detection and Response (EDR)?
Endpoint Detection and Response (EDR) is a cybersecurity solution that continuously monitors, detects, and responds to risks on endpoint devices such as laptops, desktops, and servers, enhancing a company's cybersecurity posture.
How does EDR differ from traditional antivirus solutions?
Unlike traditional antivirus solutions that rely heavily on malware signatures, EDR employs advanced techniques such as behavioral analysis and machine learning to provide a more proactive defense against threats.
What are the benefits of implementing EDR in an organization?
Implementing EDR can drastically reduce downtime and potential losses from cyberattacks, with the average cost of downtime exceeding $53,000 per hour. EDR helps detect and neutralize attacks early, saving businesses significant amounts in damages.
What key features does EDR technology offer?
Key features of EDR technology include continuous monitoring, automated attack containment, and the ability to provide forensic records of incidents.
How does EDR improve incident response times?
EDR enhances visibility into endpoint actions, allowing teams to uncover incidents that might otherwise go unnoticed, significantly shortening response times to emerging threats.
Can you provide an example of EDR in action?
A medium-sized company successfully used EDR to isolate a PC during a ransomware attack, preventing data loss and maintaining uninterrupted operations.
Why is understanding the EDR cyber security meaning important for businesses?
Understanding the EDR cyber security meaning is crucial for businesses aiming to bolster their resilience and protect sensitive data, as EDR solutions enable organizations to shift from a reactive to a proactive cybersecurity stance.
How do Cyber Solutions' EDR offerings adapt to organizational needs?
Cyber Solutions' EDR offerings are designed to adapt to new challenges and scale with business operations, ensuring tailored access controls and restrictions that meet specific organizational needs.