
In today's landscape, where cyber threats are not just common but increasingly sophisticated, the urgency for robust cybersecurity measures is paramount-especially for healthcare organizations that manage sensitive patient data. SSL Deep Packet Inspection (DPI) stands out as an essential tool for C-suite leaders, providing a comprehensive approach to bolster data protection, streamline operations, and ensure compliance with regulations. But here's the pressing question: how can executives effectively harness SSL DPI to not only protect their organizations but also inform strategic decision-making?
This article delves into ten key benefits of SSL DPI, illustrating how it empowers leaders to navigate the intricate challenges of modern cybersecurity while strengthening their enterprises against potential threats. By understanding the unique challenges faced by CFOs and other executives, we can better appreciate the transformative role that SSL DPI plays in safeguarding healthcare organizations.
As we explore these benefits, consider the implications of failing to address cybersecurity threats. The stakes are high, and the consequences of inaction can be dire. SSL DPI not only enhances security but also provides valuable insights that can drive informed decision-making.
Join us as we uncover how SSL DPI can be a game-changer in the fight against cyber threats, ensuring that healthcare organizations remain resilient and compliant in an ever-evolving digital landscape.
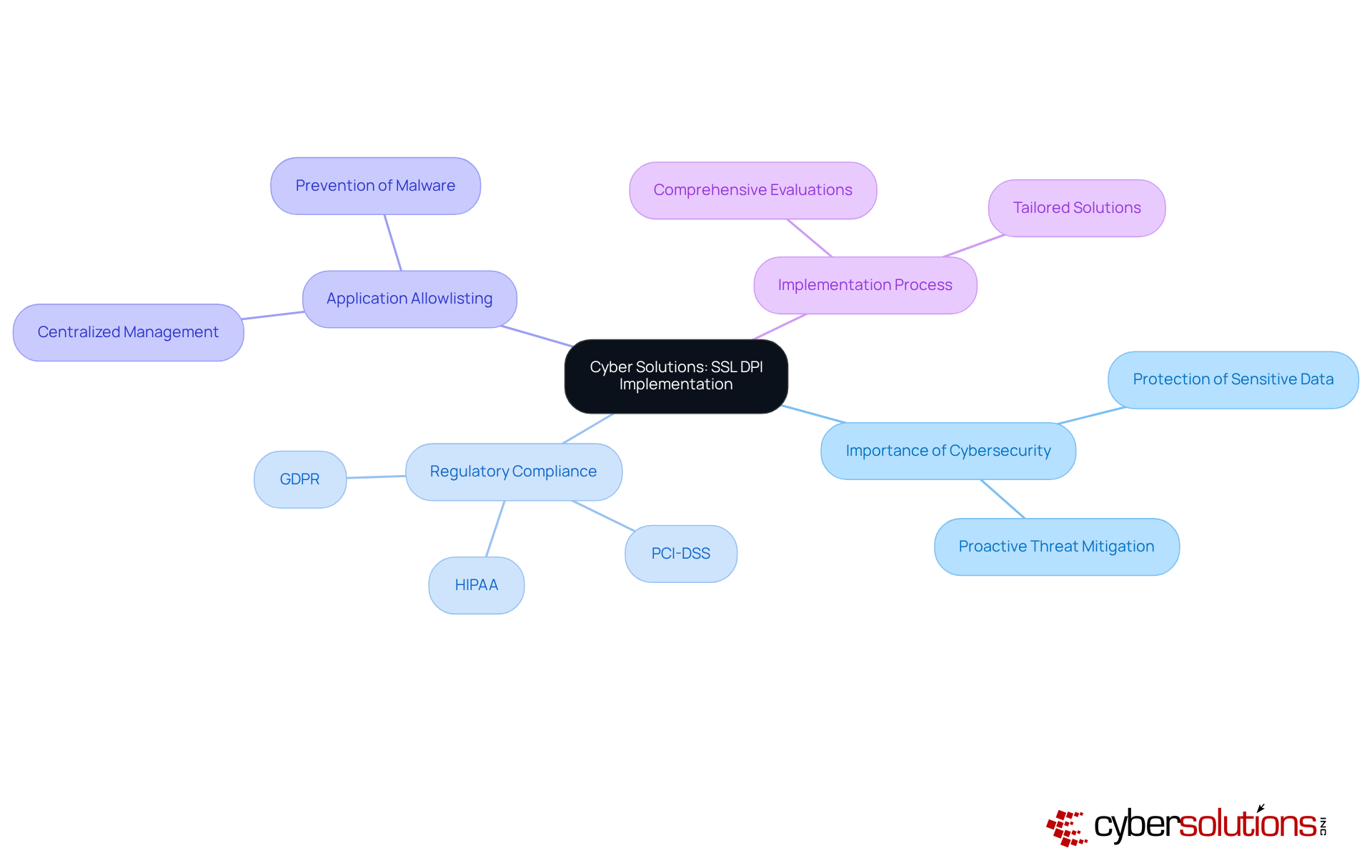
In today's digital landscape, the importance of cybersecurity cannot be overstated. Cyber Solutions Inc. offers a powerful implementation of SSL DPI that significantly enhances protection by decrypting and analyzing SSL traffic. This proactive strategy empowers organizations to identify and mitigate threats that may lurk within encrypted communications.
Healthcare organizations face unique challenges when it comes to cybersecurity. With sensitive patient data at stake, regulatory compliance is not just a requirement - it's a necessity. By leveraging advanced technologies, Cyber Solutions ensures that businesses can maintain a secure environment while meeting these stringent standards.
Moreover, the integration of SSL DPI into Cyber Solutions' security strategy underscores a commitment to data protection. SSL DPI effectively prevents malicious applications from executing, continuously monitors application activity, and facilitates centralized management of allowlists. This approach not only reduces vulnerabilities but also enhances compliance assurance.
The implementation process involves comprehensive evaluations and tailored solutions that align with the specific needs of each organization. This ensures optimal safeguarding against evolving threats while supporting compliance with federal regulations. Are you ready to fortify your cybersecurity measures and protect your organization from potential breaches?
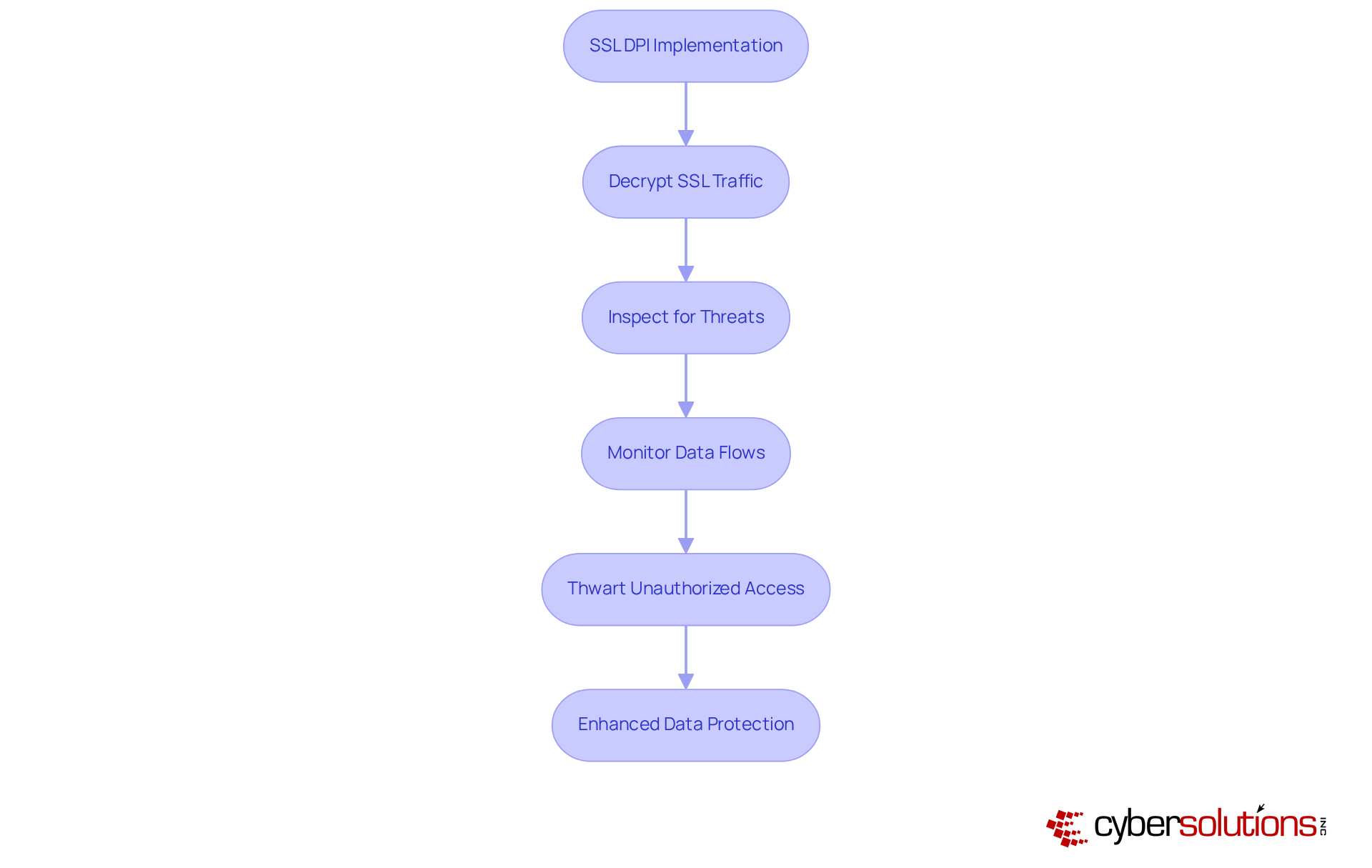
In today's digital age, data protection is a necessity, especially in healthcare. SSL DPI plays a pivotal role in safeguarding sensitive information by meticulously inspecting encrypted traffic for potential threats. By decrypting SSL traffic, organizations can effectively monitor data flows and prevent data breaches. This capability is particularly critical in sectors like healthcare and finance, where security lapses can lead to significant financial loss and irreparable reputational damage.
Consider this: in 2025, the average cost of a data breach reached a staggering $7.42 million. This statistic underscores the urgent need for robust protective measures. Cyber Solutions Inc. stands at the forefront of this battle, guaranteeing that its implementations adhere to the highest standards of security. This commitment significantly enhances the overall security posture of organizations.
The use of SSL DPI has proven instrumental in threat detection by identifying and mitigating threats before they can exploit vulnerabilities in encrypted traffic. As companies increasingly rely on digital communications, the role of SSL DPI in data protection is becoming even more crucial. Are you prepared to implement strategies for governing sensitive data? With Cyber Solutions, you can confidently navigate these challenges and protect your organization from potential threats.
In today's digital landscape, the importance of robust cybersecurity cannot be overstated. Implementing SSL DPI is a game-changer for organizations that aim to streamline their operations. By utilizing Cyber Solutions' technology, organizations can identify anomalies and potential vulnerabilities in real-time. This not only reduces the time spent on manual monitoring and incident response but also allows IT teams to concentrate on strategic initiatives rather than merely reacting to threats.
Cyber Solutions effectively combines SSL DPI with existing protection frameworks to enhance visibility and control over network traffic. This proactive approach leads to improved security and minimizes downtime. But why is this crucial? The rise of sophisticated threats like ransomware and phishing demands that organizations stay ahead of the curve. By adopting SSL DPI, businesses can significantly bolster their defenses while simultaneously boosting overall productivity.
Consider this: recent data reveals that companies implementing automated security solutions, such as SSL DPI, reported an average savings of $2.22 million compared to those that did not. This statistic underscores the value of proactive security measures. Are you ready to elevate your organization's security posture and reap the rewards? With Cyber Solutions, you can implement SSL DPI with confidence, ensuring your organization is not just reactive but proactive in its defense strategies.
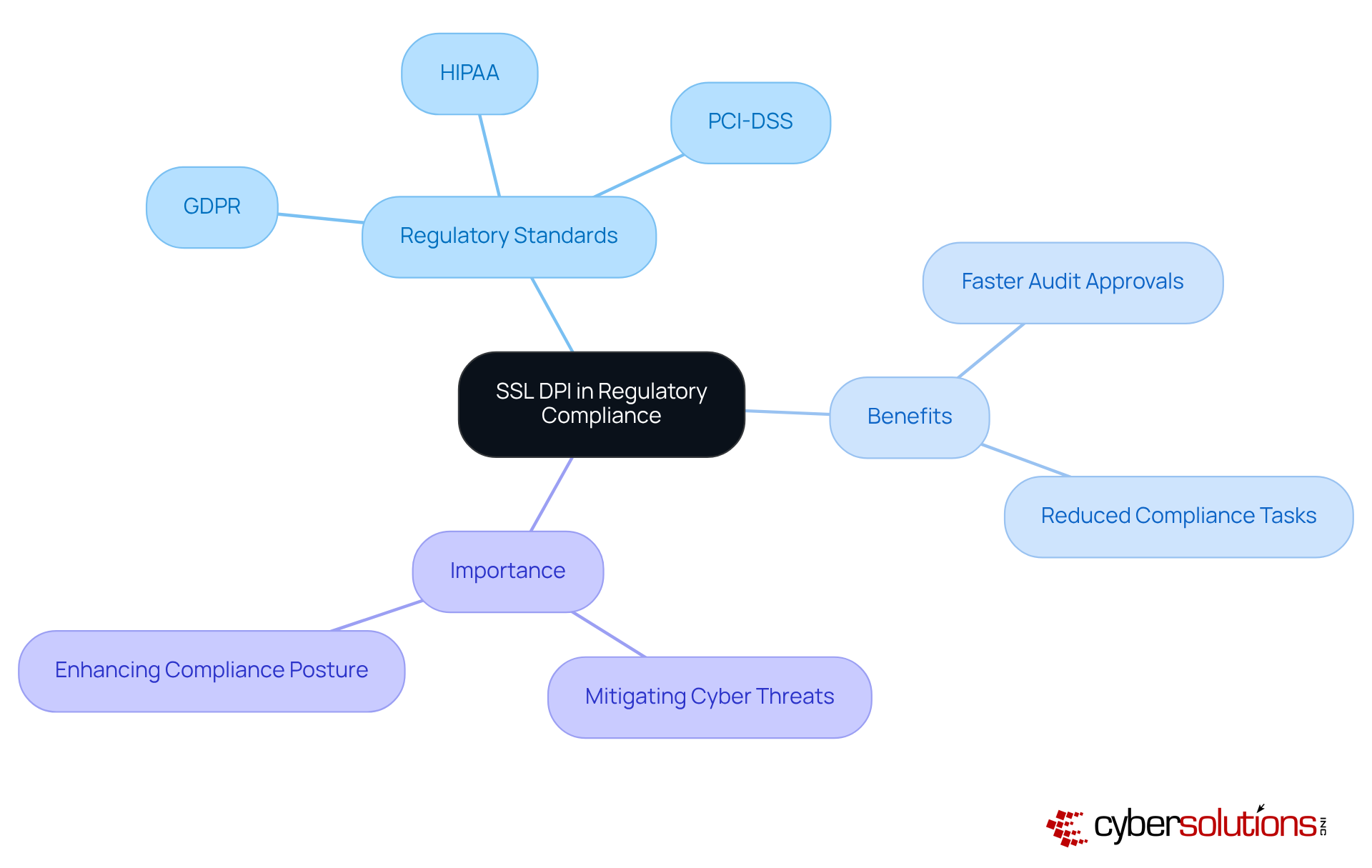
SSL DPI is not just a tool; it’s a critical asset for organizations striving to meet stringent regulatory standards like GDPR. In an era where data breaches are rampant and regulatory scrutiny is intensifying, SSL DPI plays a crucial role in inspecting encrypted traffic. This capability ensures that sensitive data is transmitted in compliance with regulations, addressing the pressing need for data security. With the global economy projected to reach a staggering $10.5 trillion annually by 2025, the importance of SSL DPI in mitigating these threats cannot be overstated.
Organizations that utilize SSL DPI can significantly bolster their security posture. By effectively identifying and mitigating risks associated with encrypted traffic, businesses can demonstrate adherence to:
Recent data reveals that entities utilizing SSL DPI report enhanced compliance outcomes, including faster audit approvals and reduced time spent on compliance tasks. Isn’t it time your organization considered the advantages of SSL DPI?
Compliance officers recognize that SSL DPI is essential during audits, as it offers clear visibility into data flows and ensures that all transmitted information aligns with regulatory requirements. This proactive approach not only strengthens data protection but also simplifies compliance reporting, making it easier to navigate the complexities of regulatory frameworks. Thus, SSL DPI emerges as a critical component of a robust compliance strategy for organizations operating in highly regulated environments.
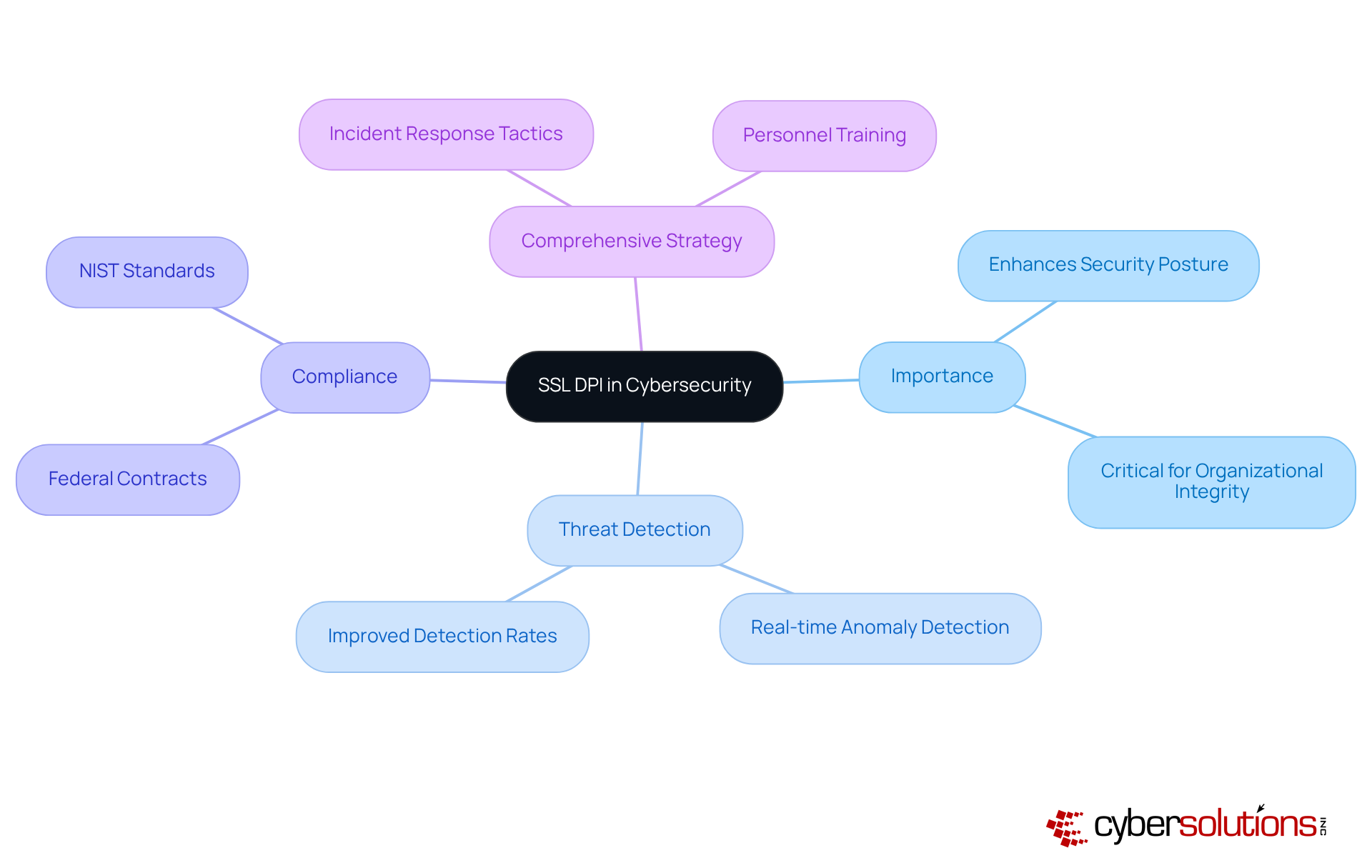
In today's digital landscape, SSL DPI is a critical component of organizational integrity, especially in sectors like healthcare. SSL DPI is a powerful tool that significantly enhances a company's security posture. SSL DPI is essential for threat detection by enabling visibility into encrypted traffic.
By meticulously analyzing encrypted traffic, organizations can uncover malicious activities that might otherwise remain hidden. Cyber Solutions employs sophisticated algorithms and machine learning techniques to identify anomalies and potential threats in real-time. This proactive strategy not only improves detection rates of previously undetectable threats but also empowers organizations to respond swiftly to emerging risks, effectively minimizing the chances of a security breach.
Consider this: organizations that utilize SSL DPI have reported a marked increase in detection rates, showcasing its critical role in modern cybersecurity. Furthermore, our tiered approach to cybersecurity, which includes advanced tactics and personnel training, ensures that organizations are better equipped to handle incidents such as data breaches. This comprehensive strategy ultimately enhances security measures, fostering a resilient security environment.
Investing in SSL DPI is not just a choice; it's a necessity for organizations aiming to enhance security. With the soaring costs of data breaches reaching $4.45 million in 2023, the stakes have never been higher. By implementing SSL DPI, organizations can proactively identify and mitigate threats within encrypted traffic, significantly lowering the risk of data breaches and financial losses.
Cyber Solutions stands ready to provide solutions that align with your budget while maximizing security benefits. Imagine demonstrating the ROI of SSL DPI through the reduction of expenses and the improvement of operational efficiency with SSL DPI. This not only justifies your investment to stakeholders but also positions your organization as a leader in security.
Consider the 2017 Equifax data breach, which cost over $1.38 billion. This incident starkly illustrates the financial impact of inadequate cybersecurity. In contrast, companies that invest in SSL DPI not only protect their digital assets but also enhance their reputation—two critical components for long-term success.
Financial analysts emphasize the importance of viewing cybersecurity as a strategic investment, akin to property insurance. This perspective can facilitate board approval for essential initiatives. Ultimately, the savings from SSL DPI can far exceed initial costs by preventing significant financial losses and ensuring compliance with evolving regulations.
Are you ready to take the next step in securing your organization? The time to act is now.

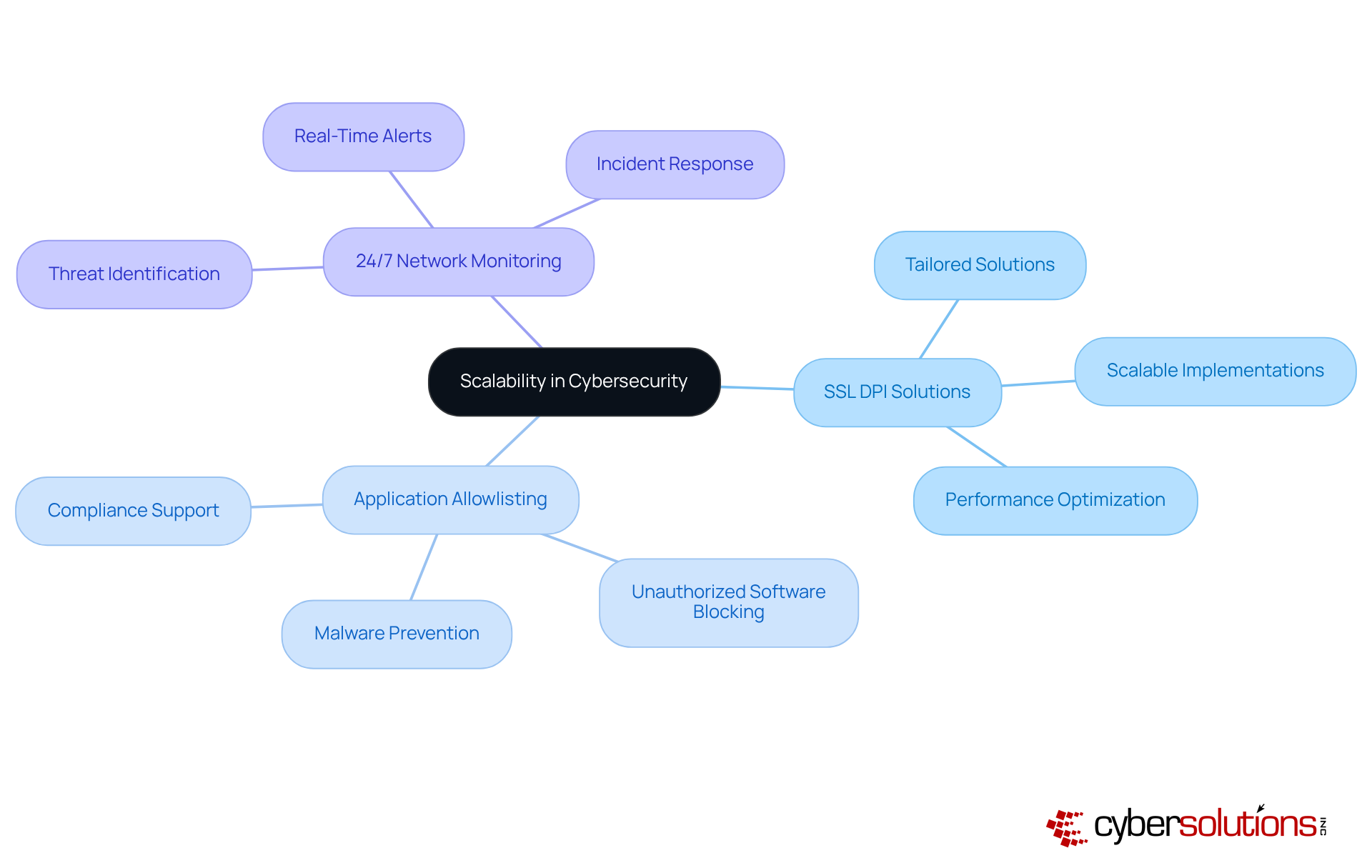
In today's rapidly evolving business landscape, the importance of robust cybersecurity cannot be overstated. As organizations expand, their cybersecurity needs become increasingly complex. Cyber Solutions offers services that are not only scalable but also tailored to meet the dynamic demands of businesses, ensuring effective performance. Whether facing increased threats or the integration of new technologies, Cyber Solutions ensures that SSL DPI implementations evolve in tandem with your business. This adaptability is crucial for maintaining strong protection in ever-changing environments.
Moreover, the role of threat detection is vital; it proactively prevents attacks from executing, significantly reducing vulnerabilities and aiding organizations in meeting compliance requirements. When combined with monitoring and alert services, Cyber Solutions delivers a comprehensive cybersecurity strategy. This approach guarantees that potential threats are swiftly identified and addressed, thereby safeguarding your business operations effectively.
In a world where cyber threats are constantly on the rise, can you afford to overlook the importance of a scalable solution? With Cyber Solutions, you can ensure that your organization is not only protected but also resilient.
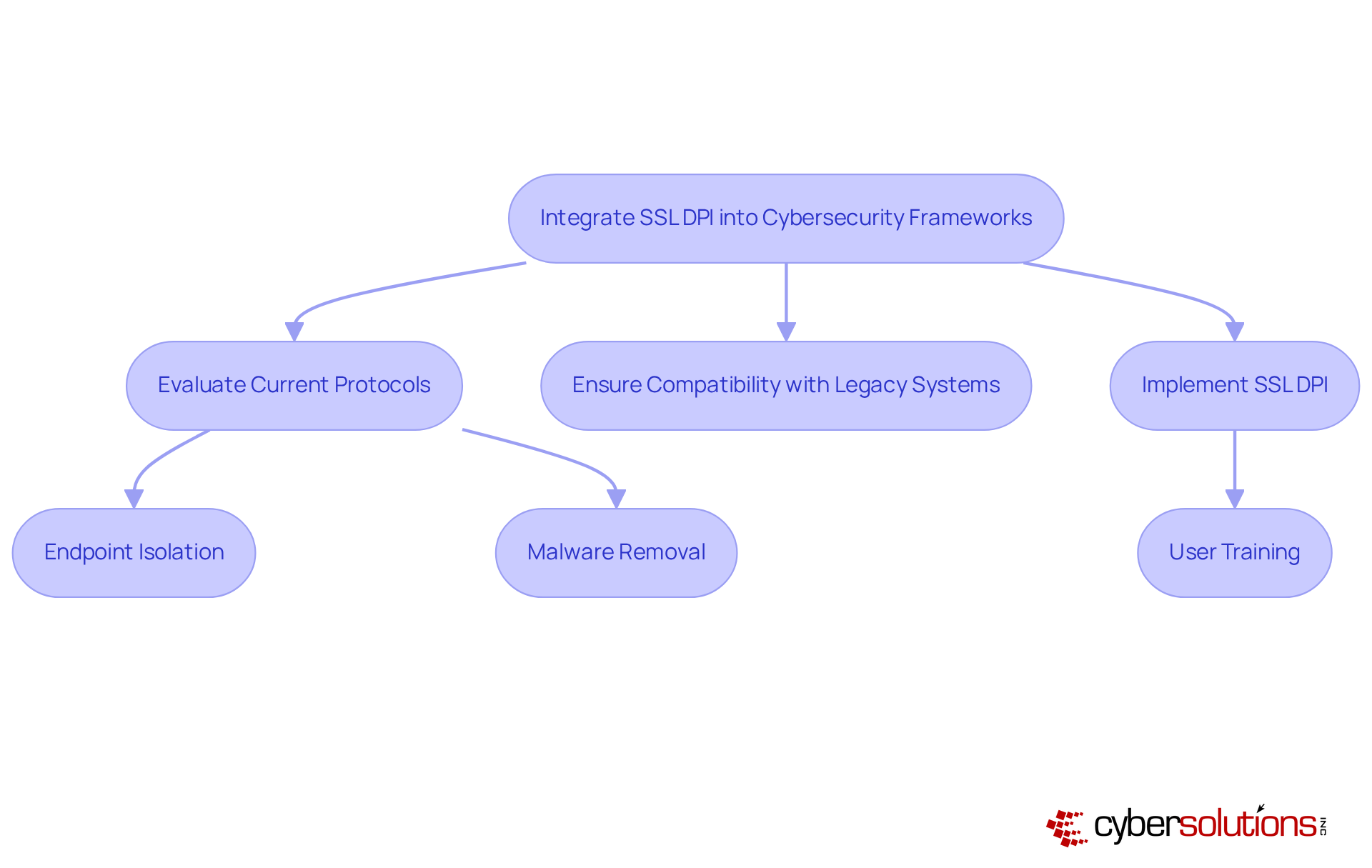
In today's digital landscape, the importance of cybersecurity in healthcare cannot be overstated. With the rise of cyber threats, healthcare organizations face unique challenges that demand robust solutions. Incorporating SSL DPI into existing frameworks is essential for enhancing efficacy and ensuring comprehensive threat detection.
Cyber Solutions collaborates closely with clients to seamlessly integrate SSL DPI into their overall security strategy. This integration significantly boosts security posture, enabling organizations to detect and respond to threats more effectively. By aligning SSL DPI with other security measures, businesses can establish a unified defense against cyber threats, ultimately reducing the risk of data breaches and operational disruptions.
Optimal strategies for integration involve thorough evaluations of current protective protocols and ensuring compatibility with legacy systems. Organizations that have successfully implemented SSL DPI have reported enhanced security measures and a stronger protective stance. For instance, companies leveraging SSL DPI have reported a 50% increase in their ability to identify and mitigate potential threats before they escalate, which is a critical advantage given the alarming rise in cyberattacks reported globally.
Cyber Solutions employs a layered approach, including:
to enhance recovery and cultivate strong partnerships with clients. This strategy not only improves security measures but also reinforces cybersecurity confidence, particularly in sectors like healthcare where data protections are paramount. As Piyush Sharma, CEO of Tuskira, stated, 'Integrating SSL DPI with existing protective tools not only enhances visibility but also streamlines processes, allowing teams to act swiftly against emerging threats using real-time data.' This sentiment resonates throughout the sector, where companies increasingly recognize the importance of a cohesive protection ecosystem.
Successful examples of integration can be observed in the finance and healthcare sectors, where the enhanced visibility provided by SSL DPI has led to significant reductions in response times to security incidents. By adopting SSL DPI, these entities have fortified their defenses, ensuring compliance with stringent regulatory requirements while safeguarding sensitive data. Ultimately, the strategic integration of SSL DPI into cybersecurity frameworks empowers organizations to navigate the complexities of modern threats effectively.
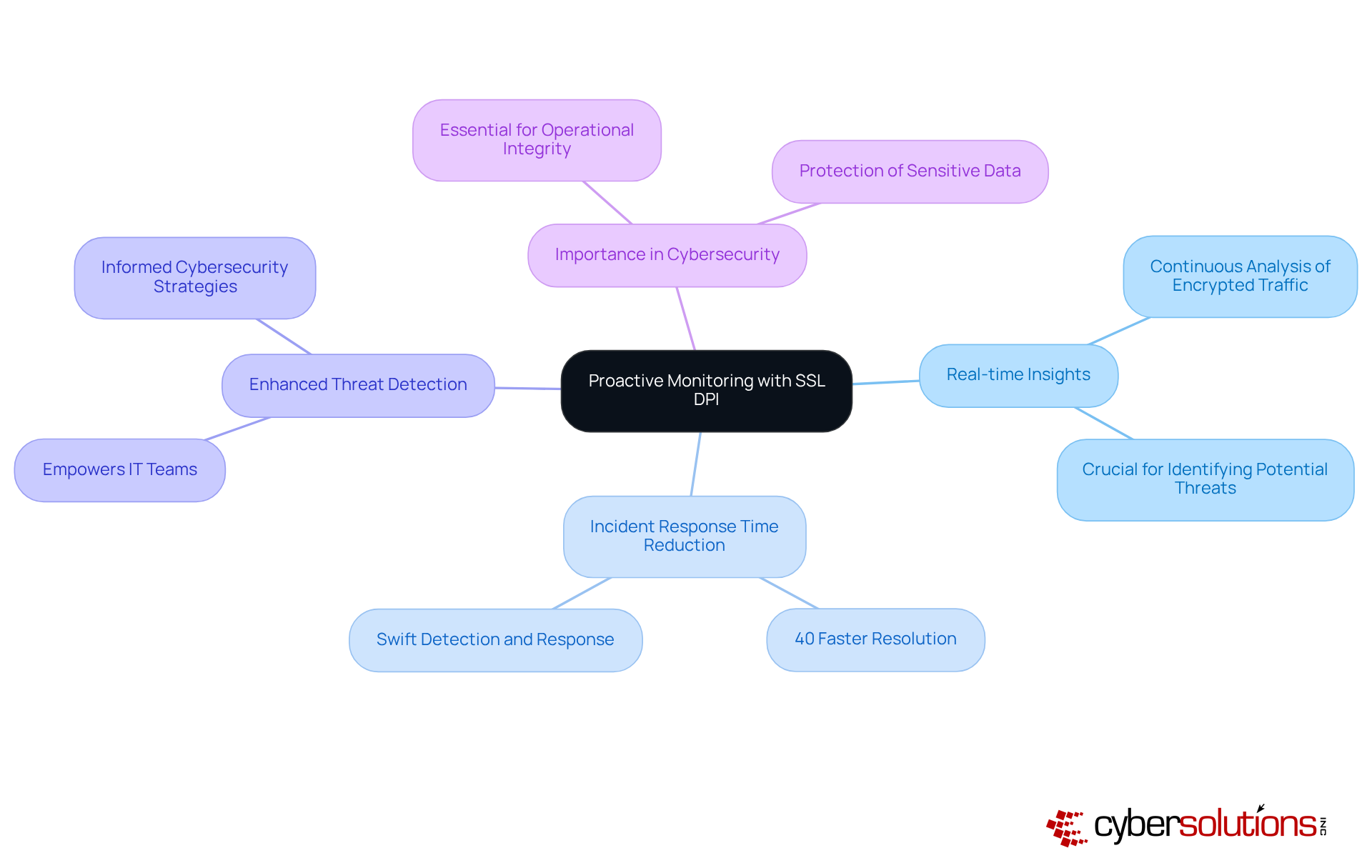
Proactive monitoring is not just important; it’s essential for effective cybersecurity, especially in today’s rapidly evolving threat landscape. SSL DPI is at the forefront of this effort, providing tools that are crucial for identifying potential threats. Cyber Solutions leverages advanced monitoring tools that utilize analytics to continuously analyze encrypted traffic, ensuring that organizations can swiftly detect and respond to incidents, often before they escalate into significant breaches. In fact, organizations employing SSL DPI have reported a remarkable reduction in response times by up to 40% compared to those that do not utilize these capabilities.
The insights gained from proactive monitoring enhance visibility and empower IT teams to make informed decisions about their cybersecurity strategies. Cybersecurity experts stress that real-time analysis is vital in a landscape where the window from disclosure to exploitation can be alarmingly short—measured in mere hours. By integrating SSL DPI into their defenses, organizations can uphold a strong security posture, ensuring they are adequately prepared to navigate the ever-changing threat environment.
Consider the organizations that have embraced SSL DPI; they have successfully identified and mitigated threats that might have otherwise gone unnoticed. This underscores the effectiveness of this technology in providing comprehensive security. As cyber threats grow increasingly sophisticated, it is essential to incorporate proactive monitoring into security frameworks to preserve operational integrity and resilience.
In today's digital landscape, the importance of cybersecurity cannot be overstated, especially for organizations handling sensitive information. To fully leverage SSL DPI, companies must prioritize training for employees on best practices. SSL DPI offers comprehensive programs designed to empower teams with the knowledge and skills necessary to effectively utilize SSL DPI. By fostering a strong culture of security awareness, organizations can significantly enhance their security posture and mitigate the risks associated with human error, which often leads to breaches.
Training sessions focus on threat identification and developing effective responses to potential threats. This ensures that employees are not just passive observers but active contributors to the organization's cybersecurity initiatives. Alarmingly, in 2024, only 52% of organizations conducted employee training, revealing a critical gap that SSL DPI can effectively address. Moreover, organizations that implement ongoing training programs can achieve a remarkable 70% reduction in security incidents, underscoring the necessity of continuous education.
Case studies illustrate how SSL DPI training has successfully reduced incidents and improved response times, reinforcing the value of investing in employee education. As cyber threats continue to evolve, the question remains: is your organization prepared to face these challenges head-on? Investing in robust training initiatives is not just a recommendation; it’s a necessity for safeguarding your organization’s future.

The implementation of SSL Deep Packet Inspection (DPI) is not just a technical upgrade; it’s a strategic imperative for C-suite leaders aiming to fortify their organization’s cybersecurity framework. In today’s digital landscape, where threats are increasingly sophisticated, integrating SSL DPI allows businesses to safeguard sensitive information, enhance operational efficiency, and comply with stringent regulatory standards. This comprehensive approach not only mitigates risks but also equips organizations to adeptly navigate the complexities of modern cyber threats.
Key benefits of SSL DPI are numerous and compelling:
Moreover, the importance of employee training cannot be overstated. By adopting SSL DPI, organizations not only strengthen their defenses against potential breaches but also streamline operational processes, significantly improving their overall security posture. Financially, the implications are substantial; evidence suggests that implementing SSL DPI can lead to considerable savings and increased ROI.
In conclusion, embracing SSL DPI is essential for organizations striving to thrive in an increasingly digital world. C-suite leaders must prioritize the adoption of SSL DPI solutions, recognizing that robust cybersecurity is vital for protecting sensitive data, maintaining compliance, and fostering trust with stakeholders. The time to act is now-securing an organization’s future begins with proactive measures today.
What is SSL DPI and how does it enhance cybersecurity in healthcare?
SSL DPI (Secure Sockets Layer Deep Packet Inspection) enhances cybersecurity by decrypting and analyzing SSL traffic, allowing organizations to identify and mitigate threats hidden within encrypted communications.
Why is cybersecurity particularly important for healthcare organizations?
Cybersecurity is crucial for healthcare organizations due to the sensitive nature of patient data and the need to comply with industry regulations such as HIPAA, PCI-DSS, and GDPR.
How does Cyber Solutions Inc. help healthcare organizations maintain compliance?
Cyber Solutions Inc. leverages advanced technologies to ensure businesses can maintain a secure environment while adhering to stringent regulatory standards.
What is application allowlisting and how does it contribute to cybersecurity?
Application allowlisting is a security strategy that prevents unauthorized or malicious applications from executing. It continuously monitors application activity and facilitates centralized management of allowlists, reducing vulnerabilities and enhancing compliance assurance.
What does the implementation process of SSL DPI involve?
The implementation process includes comprehensive evaluations and tailored solutions that align with the specific needs of each organization, ensuring optimal protection against evolving cyber threats.
How does SSL DPI safeguard sensitive information?
SSL DPI safeguards sensitive information by inspecting encrypted traffic for potential threats, decrypting SSL traffic, and monitoring data flows to prevent unauthorized access to confidential information.
What are the financial implications of data breaches in healthcare?
The average cost of a data breach in healthcare reached approximately $7.42 million in 2025, highlighting the urgent need for robust protective measures.
How does SSL DPI contribute to operational efficiency?
SSL DPI streamlines operational processes by automating threat detection and response, enabling organizations to identify anomalies in real-time and allowing IT teams to focus on strategic initiatives rather than just reacting to threats.
What financial benefits have organizations experienced from implementing automated security solutions like SSL DPI?
Organizations that implemented automated security solutions, such as SSL DPI, reported an average savings of $2.22 million compared to those that did not invest in such technologies.