
Cybersecurity has become a pressing issue for small businesses, increasingly targeted by cybercriminals at alarming rates. The financial implications of cybersecurity are significant, with costs varying widely based on factors such as industry regulations and business size. With a staggering 60% of small businesses failing within six months of a cyberattack, the critical question arises: how can these organizations effectively balance the need for robust cybersecurity measures with their budget constraints?
This article explores the complexities of cybersecurity costs for small businesses, offering valuable insights and strategies to help them navigate this challenging landscape. By understanding the current cybersecurity threats and their implications, small businesses can take proactive steps to safeguard their operations and ensure their longevity in an increasingly digital world.
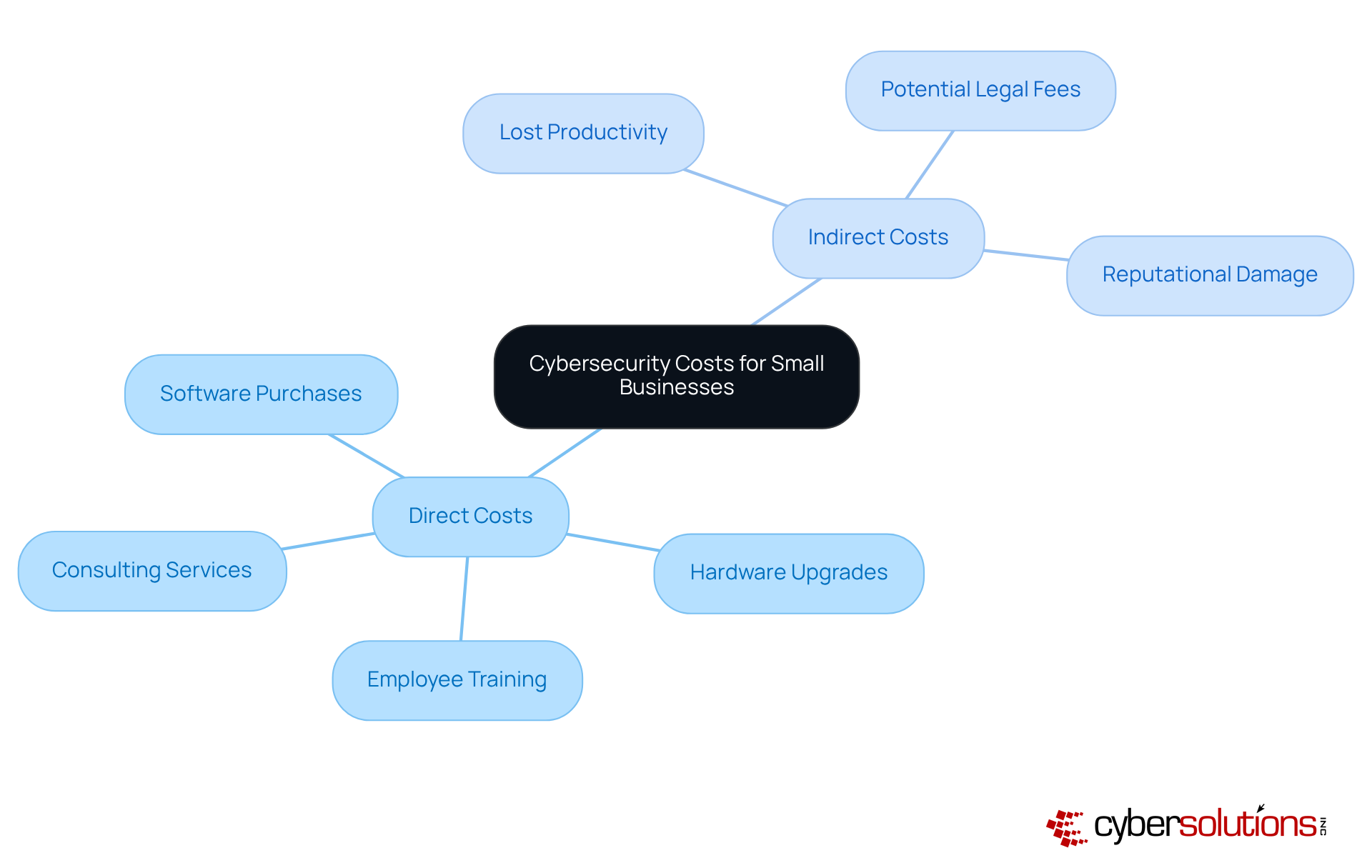
is not just an option for small enterprises; it’s a necessity. With small enterprises facing greater risks than larger firms, the stakes have never been higher. The costs can be categorized into direct and indirect expenses, both of which can significantly impact operations.
Direct costs encompass:
Typically, small enterprises allocate between $5,000 and $50,000 annually for cybersecurity, influenced by their size and industry requirements. However, the implications of neglecting cybersecurity can be severe. A data breach can incur costs ranging from $120,000 to $1.24 million. This stark reality underscores the importance of investing in cybersecurity.
Indirect expenses also play a crucial role, including:
Alarmingly, 74% of small enterprise owners either self-manage their online security or rely on unqualified individuals, which can exacerbate vulnerabilities. How can these businesses mitigate such risks?
Enter Cyber Solutions, offering a flat-rate pricing model that simplifies budgeting and eliminates unexpected IT costs. This model covers everything from email licenses to advanced security services, ensuring comprehensive protection. Additionally, understanding cybersecurity solutions is vital for small-sized enterprises. CaaS provides robust solutions to meet regulatory requirements, helping organizations remain compliant and shielded from potential penalties.
This comprehensive approach not only safeguards operations but also enhances overall security strategies. By investing in cybersecurity measures, small enterprises can protect their assets and ensure a more secure future.
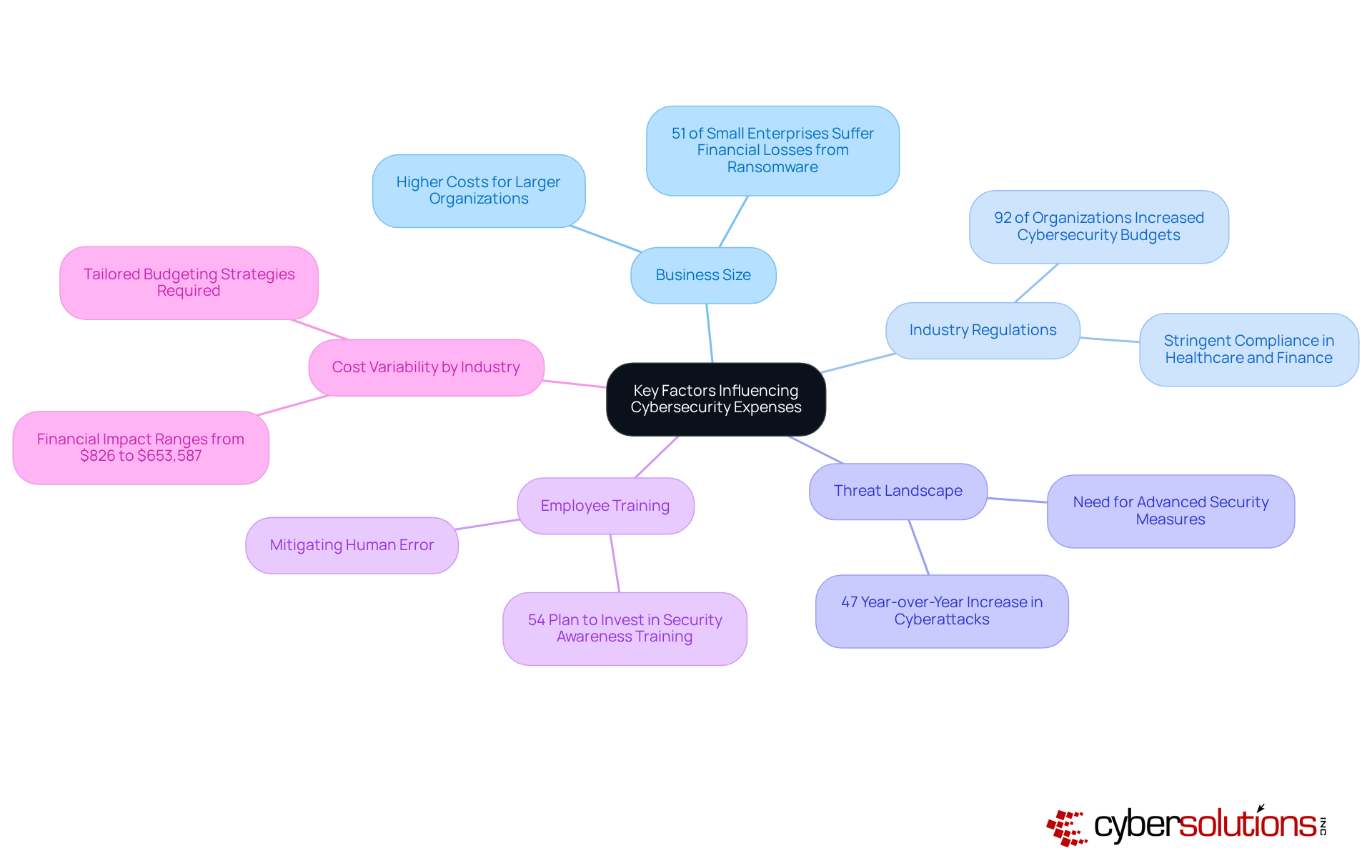
Cybersecurity is not just a technical necessity; it’s a critical investment for small businesses navigating today’s digital landscape. Understanding the factors that influence the costs of cybersecurity for small businesses is essential for making informed decisions and safeguarding sensitive information.
By comprehending these factors, small enterprises can navigate the complexities of cybersecurity funding more effectively, ensuring they allocate resources wisely to protect against potential threats.
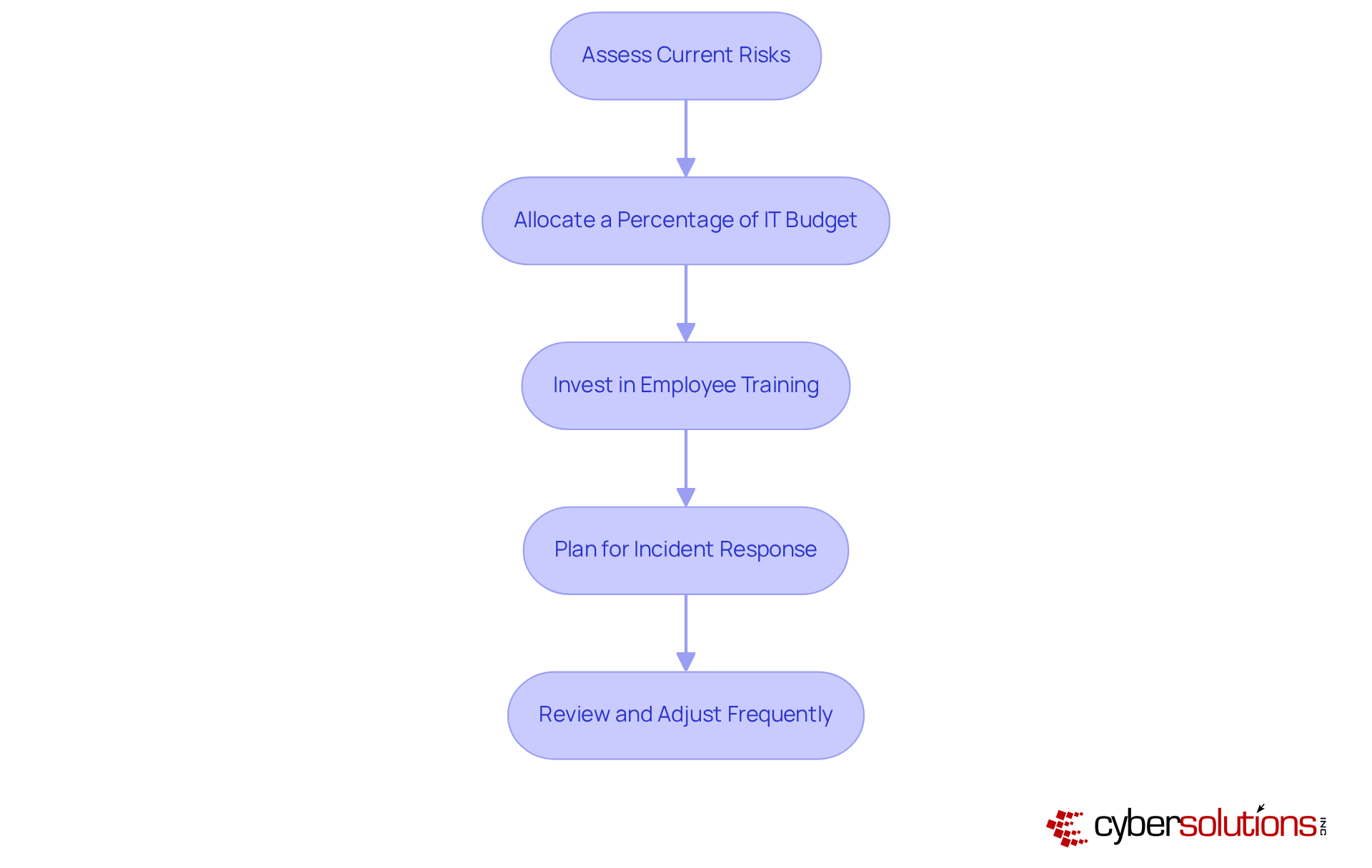
To establish a robust cybersecurity budget, small businesses must recognize the critical importance of understanding the risks to safeguard their digital assets. With cyber threats on the rise, it’s essential to adopt strategies that not only protect sensitive information but also ensure business continuity.
The staggering costs emphasize the importance of cybersecurity. In 2025, the average cost is expected to be between $120,000 and $1.24 million due to an average data breach. This figure includes expenses like recovery efforts and legal fees, as well as indirect costs such as lost revenue and customer trust. Alarmingly, 60% of small enterprises that suffer a data breach close within six months due to the financial burden.
These statistics underscore the necessity to consider the implications when investing in cybersecurity. By taking proactive measures in their operations, they can mitigate the risk of future breaches; it's a critical business imperative that demands attention and action.

Investing in cybersecurity is not just an option for small businesses; it’s a vital necessity that can determine their survival in an increasingly digital and threat-filled landscape. The multifaceted costs associated with cybersecurity - ranging from direct expenses like software and employee training to indirect costs such as reputational damage - must be understood to make informed financial decisions.
Small businesses face a significantly heightened risk of cyberattacks. Many owners mismanage their security or rely on unqualified individuals, leaving them vulnerable. By adopting a comprehensive approach that includes:
small enterprises can effectively mitigate risks and protect their assets. The staggering potential costs of cyber incidents further emphasize the importance of prioritizing cybersecurity as a core component of business strategy.
The financial implications of neglecting cybersecurity can be devastating, potentially leading to closures within months of an attack. Small businesses must recognize this reality. By embracing a proactive mindset and committing to robust cybersecurity measures, organizations can safeguard their operations and secure a more resilient future. The time to act is now; investing in cybersecurity today can save small businesses from catastrophic losses tomorrow.
Why is cybersecurity important for small businesses?
Cybersecurity is crucial for small businesses because they face cyberattacks 210 percent more often than larger firms, making them more vulnerable to potential threats.
What are the direct costs associated with cybersecurity for small businesses?
Direct costs include software purchases, hardware upgrades, employee training, and consulting services.
How much do small businesses typically spend on cybersecurity annually?
Small businesses typically allocate between $5,000 and $50,000 annually for cybersecurity costs, depending on their size and industry requirements.
What are the potential financial repercussions of neglecting cybersecurity?
Neglecting cybersecurity can lead to severe financial consequences from a data breach, with costs ranging from $120,000 to $1.24 million.
What are some indirect expenses related to cybersecurity for small businesses?
Indirect expenses can include lost productivity during a cyber incident, potential legal fees, and reputational damage.
What percentage of small business owners manage their own online security?
Alarmingly, 74% of small business owners either self-manage their online security or rely on unqualified individuals, which can increase vulnerabilities.
How can small businesses mitigate cybersecurity risks?
Small businesses can mitigate risks by utilizing services like Cyber Solutions, which offers a flat-rate pricing model that covers various security needs and simplifies budgeting.
What is Compliance as a Service (CaaS)?
Compliance as a Service (CaaS) provides robust solutions to help organizations meet regulatory requirements, ensuring they remain compliant and protected from potential penalties.
What benefits does investing in cybersecurity provide for small businesses?
Investing in cybersecurity helps protect business assets, enhances overall security strategies, and ensures a more secure future for the organization.