
In an era where digital threats are more pronounced than ever, organizations must approach the complex landscape of technology use with unwavering vigilance. An Acceptable Use Policy (AUP) serves as a crucial framework, delineating the boundaries of acceptable behavior regarding technology resources while protecting both the organization and its employees. But how can a well-structured AUP not only reduce risks but also cultivate a culture of accountability and security awareness?
This article explores the essential components of an AUP, its influence on employee conduct, and the substantial benefits it offers to organizational security. By understanding the transformative potential of this policy, readers are invited to consider its vital role in today’s digital environment.
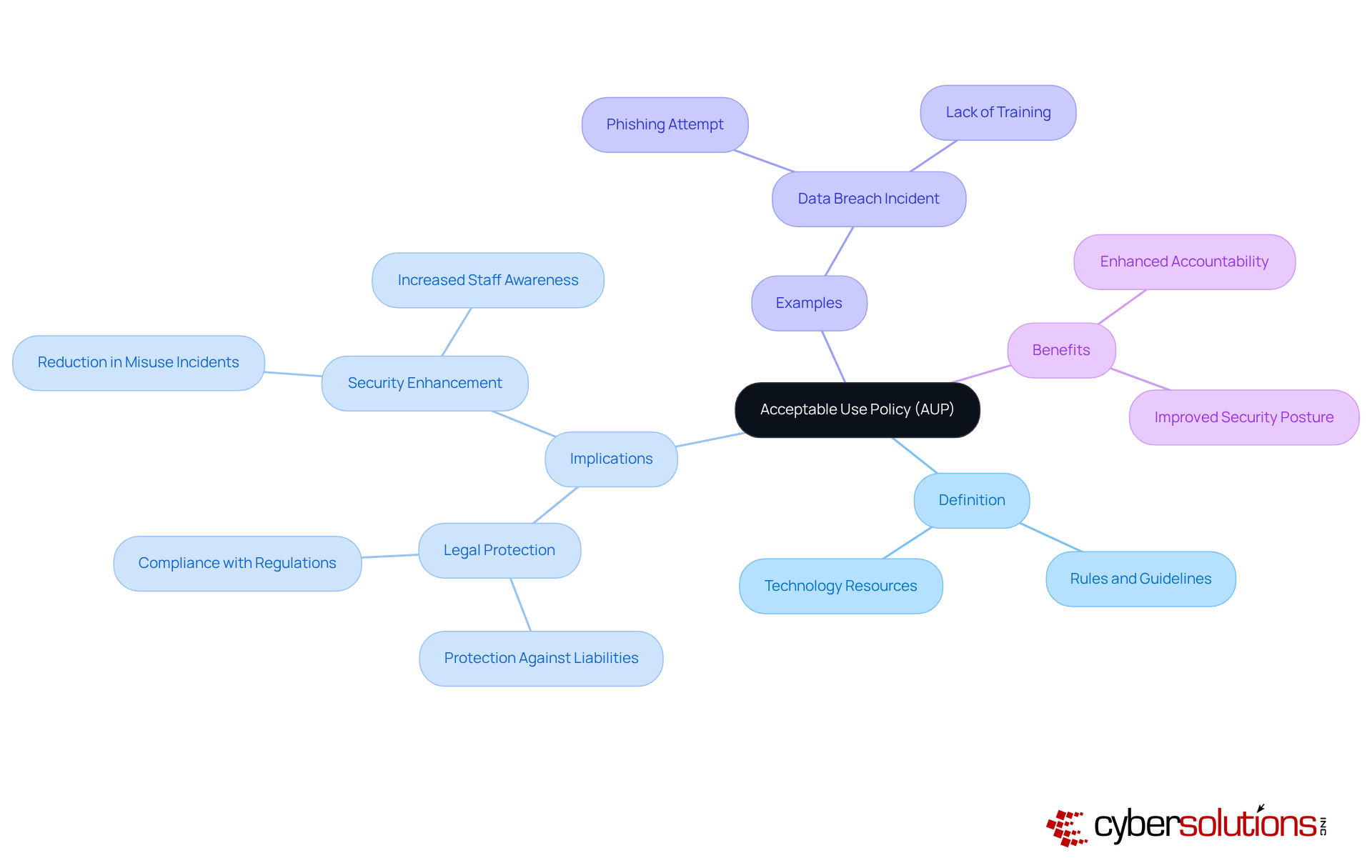
An Acceptable Use Policy (AUP) is a general policy that acts as a critical safeguard for any organization navigating the complexities of technology use, not just a formal document. The AUP is a general policy that delineates the rules and guidelines governing acceptable behavior regarding a company’s technology resources, including computers, networks, and internet access. With 71% of entities adopting an AUP, it’s clear that organizations recognize its importance in security.
The implications of having a well-defined AUP are profound. By clearly defining acceptable use, companies protect themselves against legal liabilities and security breaches. For instance, consider a multinational corporation that faced a significant loss due to a staff member's failure to recognize a phishing attempt. This incident underscores the dangers associated with inadequate policies. In contrast, organizations that have implemented AUPs report increased compliance and a reduction in misuse incidents, demonstrating the effectiveness of these frameworks in mitigating risks and ensuring safety.
In conclusion, the AUP is a general policy that is essential for any organization aiming to safeguard its resources while promoting responsible technology use. The adoption of such policies not only enhances security but also cultivates a culture of accountability, ultimately leading to a more secure operational landscape.
In today's digital landscape, organizational security is paramount, and it is essential to recognize that an Acceptable Use Policy (AUP) is a general policy that serves as a cornerstone of a robust cybersecurity strategy. This policy acts as a crucial safeguard against the potential threats that arise from personnel misusing technology. By clearly defining acceptable behaviors, organizations can significantly reduce the risk of data breaches, malware infections, and other cyber threats.
Moreover, the AUP is a general policy that is essential for compliance with various regulatory frameworks, including GDPR and HIPAA, ensuring that staff understand their responsibilities regarding data protection. Aligning the AUP with organizational goals is vital for safeguarding Federal Contract Information (FCI), particularly for businesses managing non-critical federal data. The integration of security measures within the AUP framework further fortifies security by proactively preventing unauthorized software from executing, thus minimizing vulnerabilities and ensuring adherence to stringent standards.
Additionally, leveraging technology offerings can streamline the implementation and management of AUPs, providing organizations with the necessary tools and support to maintain compliance efficiently. This approach not only protects the organization's assets but also cultivates a culture of accountability and security awareness among employees.
In conclusion, the AUP is a general policy that is not merely a policy; it is a vital component of an organization's security framework that fosters a secure environment and promotes responsible technology use.

An Acceptable Use Policy (AUP) is a general policy that is crucial for organizations aiming to safeguard their digital assets and foster a secure environment. It sets clear expectations for technology use, which is essential in today’s landscape of increasing cyber threats.
Purpose Statement: The AUP's purpose is to protect the entity's digital resources while promoting a secure digital atmosphere. This foundational element underscores the policy's significance in maintaining data integrity.
Scope: This section specifies who the policy applies to, including employees, contractors, and third-party users. By ensuring comprehensive coverage, organizations can effectively manage technology use across all levels.
Authorized Use: Here, acceptable uses of technology resources are outlined. Guidelines for internet browsing, email communication, and software installation are provided to encourage responsible behavior among users.
Prohibited Activities: This component clearly defines unacceptable behaviors, such as accessing inappropriate content or using unauthorized software. By outlining these activities, organizations can protect themselves from potential risks.
Monitoring and Enforcement: Organizations reserve the right to monitor usage, and this section details the consequences for policy violations. This reinforces accountability and ensures users understand the repercussions.
Review and Updates: Establishing a procedure for regular evaluations and revisions ensures that the AUP remains relevant in the face of evolving technologies and emerging threats.
Legal Compliance: The AUP must align with applicable laws and compliance requirements, ensuring that penalties for violations are legally enforceable.
Continuous Dialogue: Regular communication about the AUP is vital for maintaining staff awareness, promoting ongoing mindfulness, and ensuring compliance.
Training and Assessment: Ongoing training sessions, along with quizzes or True/False questions, can help staff grasp the AUP and its implications for their roles.
An Acceptable Use Policy (AUP) is a general policy that organizations can create by integrating these components to enhance security, improve compliance, and encourage responsible use among all users. Given that 88% of data breaches stem from human error, a well-structured AUP is not just beneficial - it's essential for minimizing risks associated with user behavior.

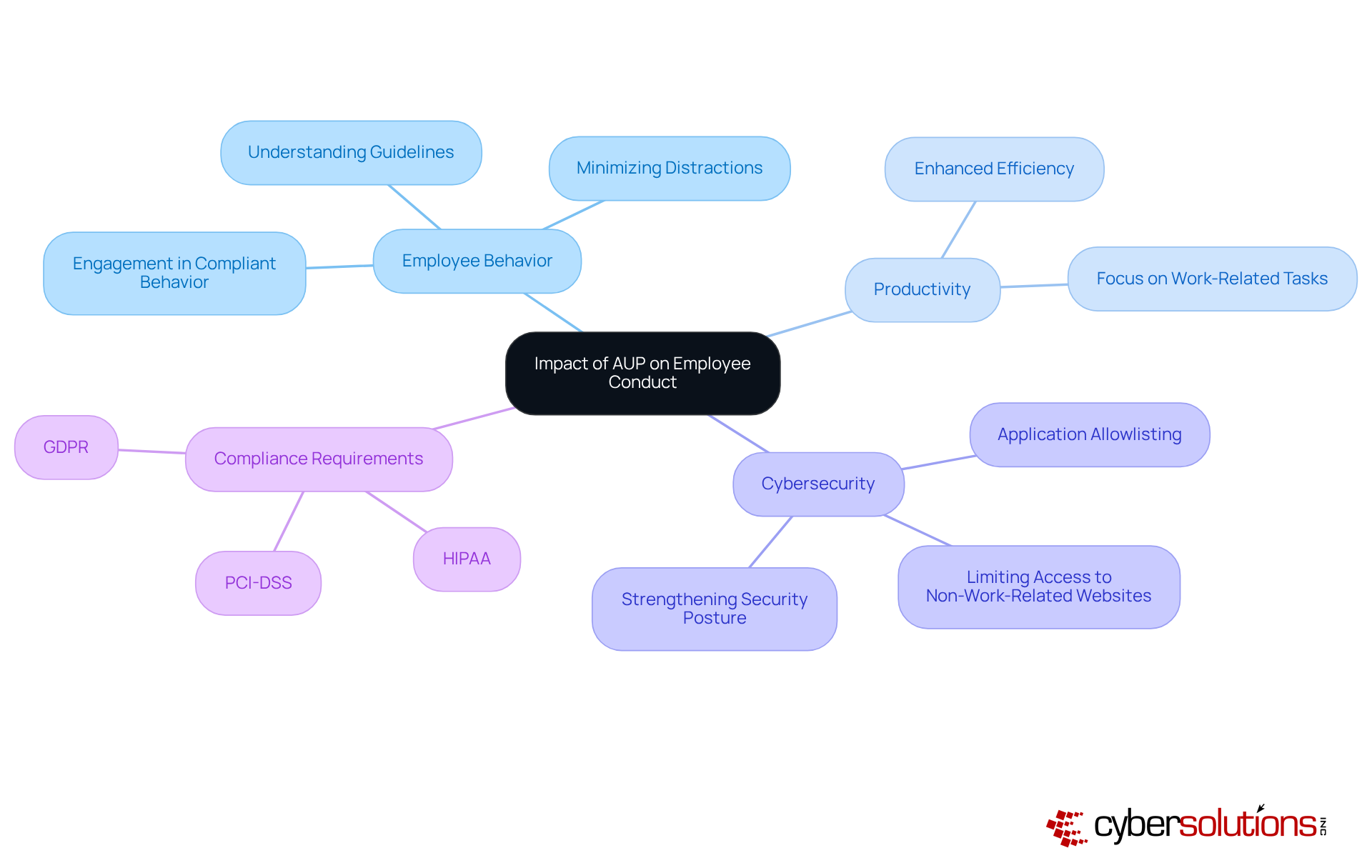
The enforcement of an Acceptable Use Policy is a general policy that is crucial in shaping staff behavior within an organization. An Acceptable Use Policy is a general policy that cultivates a secure environment by clearly outlining expectations and consequences. When employees understand the policy, they are more likely to adhere to security protocols. This understanding not only minimizes distractions but also ensures that staff focus on work-related tasks, ultimately enhancing productivity.
Consider this: by limiting access to non-work-related websites, companies can significantly reduce the likelihood of security breaches while boosting overall efficiency. Furthermore, when staff members are aware of the monitoring practices in place, they tend to comply with guidelines, which strengthens the organization's security posture. Coupled with software restrictions, which proactively prevents unauthorized software from executing, an AUP can greatly diminish the attack surface.
This dual approach not only safeguards sensitive data but also helps organizations meet compliance requirements:
In doing so, it reinforces a culture of cybersecurity awareness among employees, making them active participants in the organization's cybersecurity efforts. The Acceptable Use Policy is a general policy that is not just a policy; it is a strategic move towards a more secure and efficient workplace.
An acceptable use policy (AUP) is not just a document; it’s a cornerstone for organizations aiming to foster a secure and responsible technological environment. By laying down clear guidelines for acceptable behavior regarding technology use, the AUP safeguards organizational assets and cultivates a culture of accountability among employees. Its importance transcends mere compliance; it’s essential for maintaining a secure operational landscape.
This article has delved into various facets of the AUP, including its definition, key components, and its significant impact on organizational security and employee conduct. The policy serves as a protective barrier against potential cyber threats, ensuring that employees grasp their responsibilities while adhering to regulatory frameworks. By delineating both permissible and impermissible actions, the AUP effectively reduces risks associated with human error, ultimately boosting productivity and security.
Given the escalating complexities of the digital landscape, the necessity of implementing a robust AUP cannot be overstated. Organizations must prioritize the development and enforcement of such policies - not only to shield their digital assets but also to nurture a workforce that is informed and vigilant. Investing in a comprehensive AUP allows organizations to significantly mitigate risks, enhance compliance, and foster a culture of security that empowers employees to actively engage in safeguarding their workplace.
What is an Acceptable Use Policy (AUP)?
An Acceptable Use Policy (AUP) is a general policy that outlines the rules and guidelines governing acceptable behavior regarding an organization's technology resources, including computers, networks, and internet access.
Why is an AUP important for organizations?
An AUP is important because it helps organizations protect themselves against legal liabilities and security breaches by clearly defining permissible and impermissible actions.
What are the benefits of having a robust AUP?
The benefits of having a robust AUP include heightened staff awareness, a reduction in misuse incidents, enhanced security, and the cultivation of a culture of accountability within the organization.
How prevalent is the adoption of AUPs among organizations?
Approximately 71% of entities have adopted an AUP, indicating that organizations recognize its vital role in fostering a secure and efficient work environment.
Can you provide an example of the consequences of not having an AUP?
An example of the consequences of not having an AUP is a multinational corporation that experienced a significant data breach due to a staff member's failure to recognize a phishing attempt, highlighting the dangers associated with inadequate policies.
What is the overall conclusion regarding AUPs?
The overall conclusion is that an Acceptable Use Policy is essential for organizations aiming to safeguard their resources while promoting responsible behavior among employees, leading to a more secure operational landscape.
Key Elements of an Acceptable Use Policy | TechInsurance (https://techinsurance.com/resources/acceptable-use-policy)
How to write an acceptable use policy: key guidelines and template 2025 (https://community.trustcloud.ai/docs/grc-launchpad/grc-101/governance/crafting-an-effective-acceptable-use-policy-guidelines-and-considerations)
Best Practices
Case Studies (https://ors.od.nih.gov/OD/OQM/benchmarking/bestpractice/Pages/case_studies.aspx)
secureframe.com (https://secureframe.com/blog/acceptable-use-policy)