
The landscape of cybersecurity is increasingly precarious, especially in the healthcare sector, where recent funding cuts threaten the vital Common Vulnerabilities and Exposures (CVE) initiative. This program is essential for cataloging and managing cybersecurity weaknesses, yet it now faces significant challenges that could disrupt the flow of critical vulnerability information. As organizations grapple with the implications of these funding reductions, they must explore strategic approaches to safeguard their systems and maintain compliance.
How can cybersecurity leaders adapt to this evolving threat environment while ensuring robust defenses against emerging vulnerabilities? The answer lies in understanding the unique challenges posed by these cuts and taking decisive action to fortify defenses. By prioritizing cybersecurity investments and leveraging innovative solutions, healthcare organizations can navigate this turbulent landscape effectively.
In this context, it’s crucial to recognize that the stakes are high. Cyber threats are not just a technical issue; they can compromise patient safety and organizational integrity. Therefore, cybersecurity leaders must act swiftly and strategically to mitigate risks and protect sensitive information.
As we delve deeper into this pressing issue, we will explore actionable strategies that can empower healthcare organizations to enhance their cybersecurity posture and ensure compliance in an increasingly complex environment.
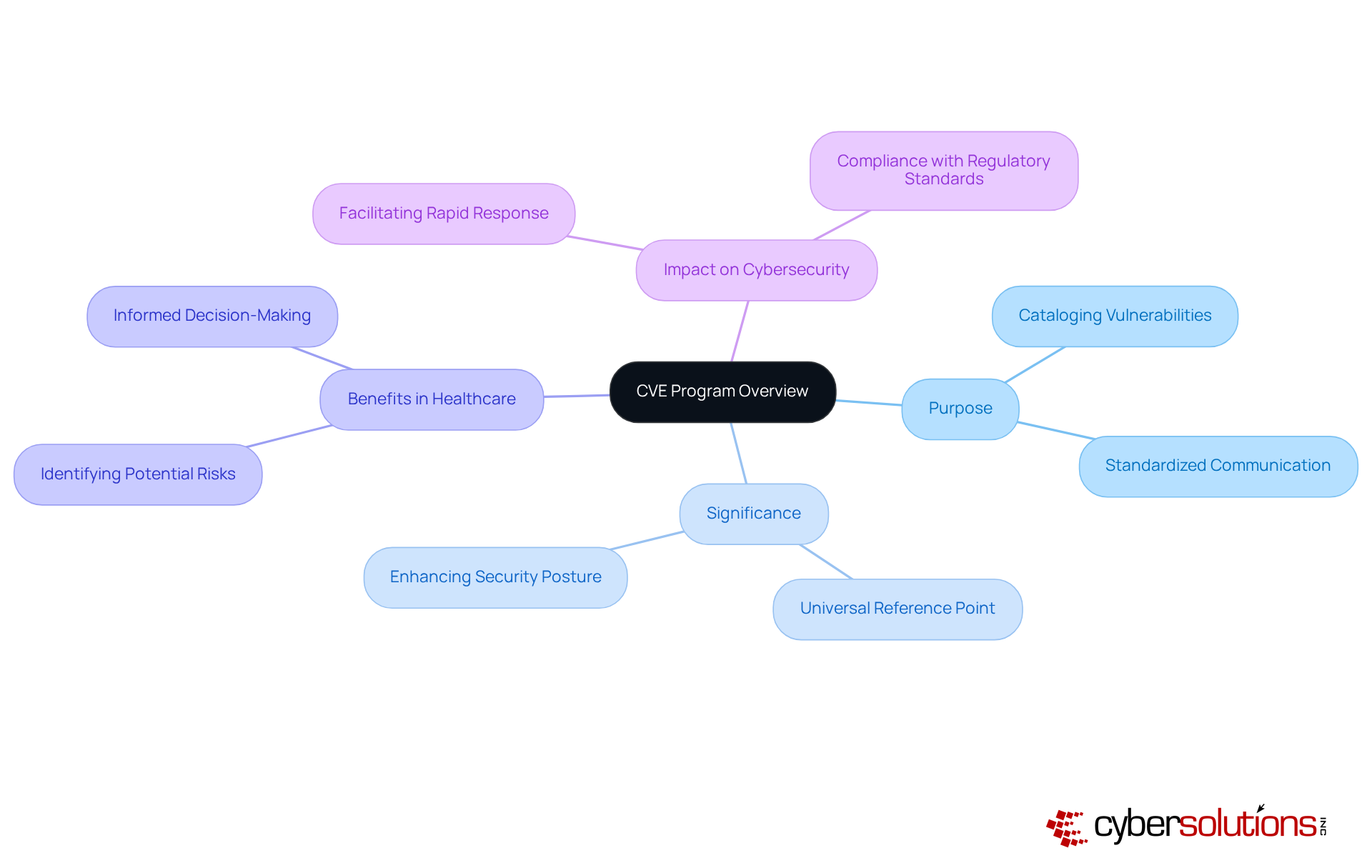
In today's digital landscape, cybersecurity is not just a technical concern; it's a critical priority for every organization, especially in healthcare. The Common Vulnerabilities and Exposures (CVE) initiative plays a pivotal role in this arena, recognizing and cataloging publicly disclosed cybersecurity weaknesses. Overseen by MITRE, the CVE initiative provides a standardized approach for entities to exchange information about these vulnerabilities, enabling them to prioritize and address security threats effectively.
The significance of the CVE initiative lies in its function as a universal reference point for weakness management. It fosters communication among security experts, ensuring that organizations can respond swiftly to emerging threats. By maintaining a comprehensive database of vulnerabilities, the CVE initiative empowers organizations to enhance their security posture and comply with regulatory standards. This makes it an indispensable component of modern cybersecurity strategies.
As healthcare organizations face unique challenges in safeguarding sensitive data, leveraging the CVE initiative can be a game-changer. It not only aids in identifying potential risks but also facilitates informed decision-making in security investments. In an era where threats are constantly evolving, the CVE initiative stands as a vital resource for organizations striving to protect their assets and maintain trust with their stakeholders.
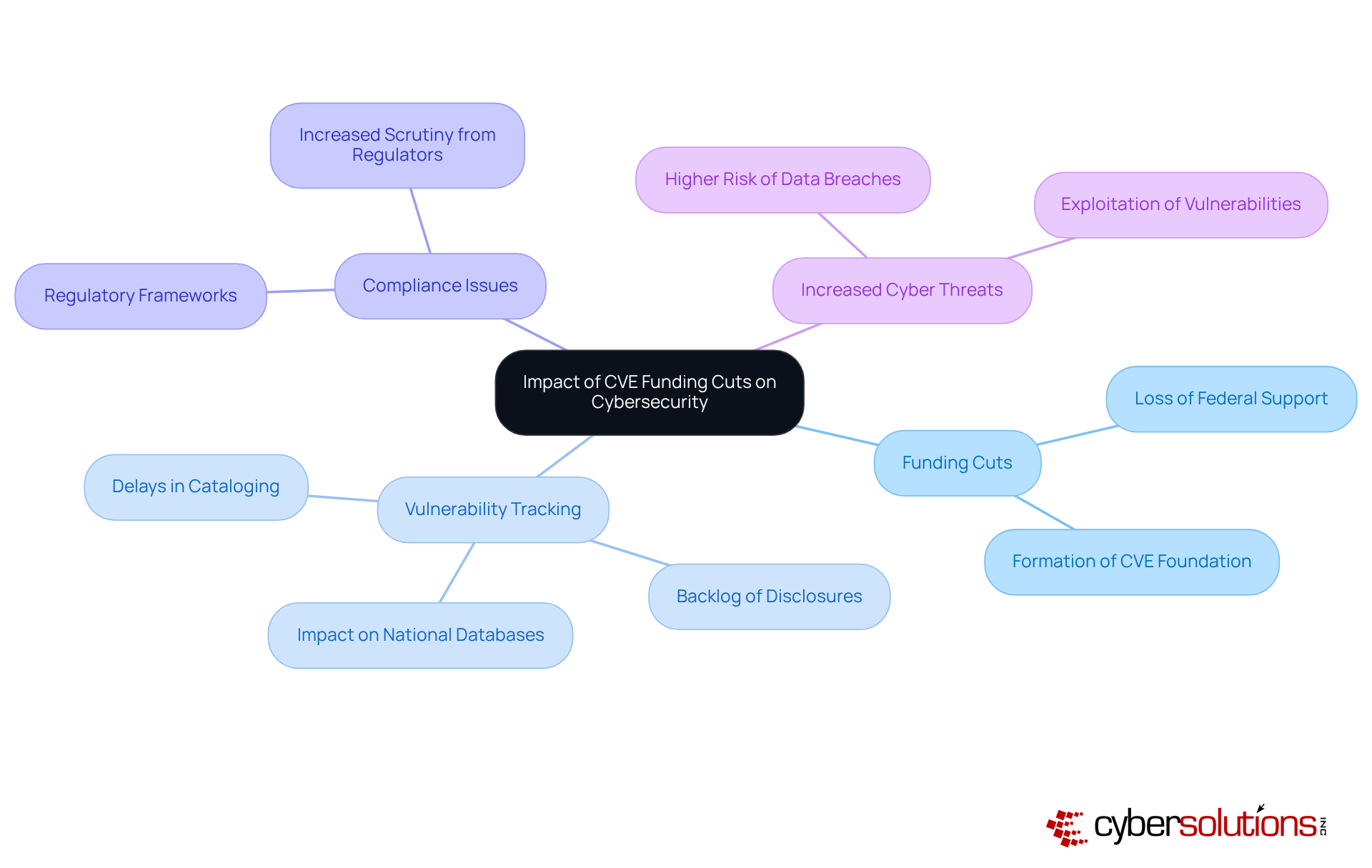
The recent cve funding cut to the CVE initiative has raised significant concerns within the cybersecurity community. As of April 16, 2025, the expiration of federal funding for MITRE's management of the CVE program threatens to disrupt essential processes for tracking and reporting weaknesses. Without adequate financial support, the cataloging of new vulnerabilities may face considerable delays, leading to a backlog of disclosures and advisories. This disruption can create a ripple effect, complicating companies' efforts to recognize and prioritize weaknesses, thereby increasing their exposure to cyber threats.
Moreover, the absence of a robust CVE system can severely impact compliance efforts. Numerous regulatory frameworks depend on precise and timely weakness data to ensure organizations adhere to security standards. For instance, the finance sector experienced a staggering 744 known data breaches in 2023, marking a 177% increase from the previous year. This alarming statistic underscores the urgency of effective vulnerability management.
Experts warn that the potential for increased cyberattacks and data breaches stemming from the cve funding cut highlights the critical need for sustainable financial support for the CVE initiative. The establishment of the CVE Foundation aims to address these challenges by ensuring the initiative's long-term sustainability and independence, thus mitigating the risks associated with relying on a single funding source. As organizations navigate this unpredictable landscape, they must prioritize diversifying their threat intelligence sources and monitoring vendor-specific risk feeds to maintain robust cybersecurity protections.
In light of the cve funding cut for the CVE program, cybersecurity leaders must adopt robust strategies to effectively manage vulnerabilities and mitigate risks. The importance of cybersecurity in today’s landscape cannot be overstated, especially as organizations face evolving threats. Here are several key approaches that can help navigate these challenges:
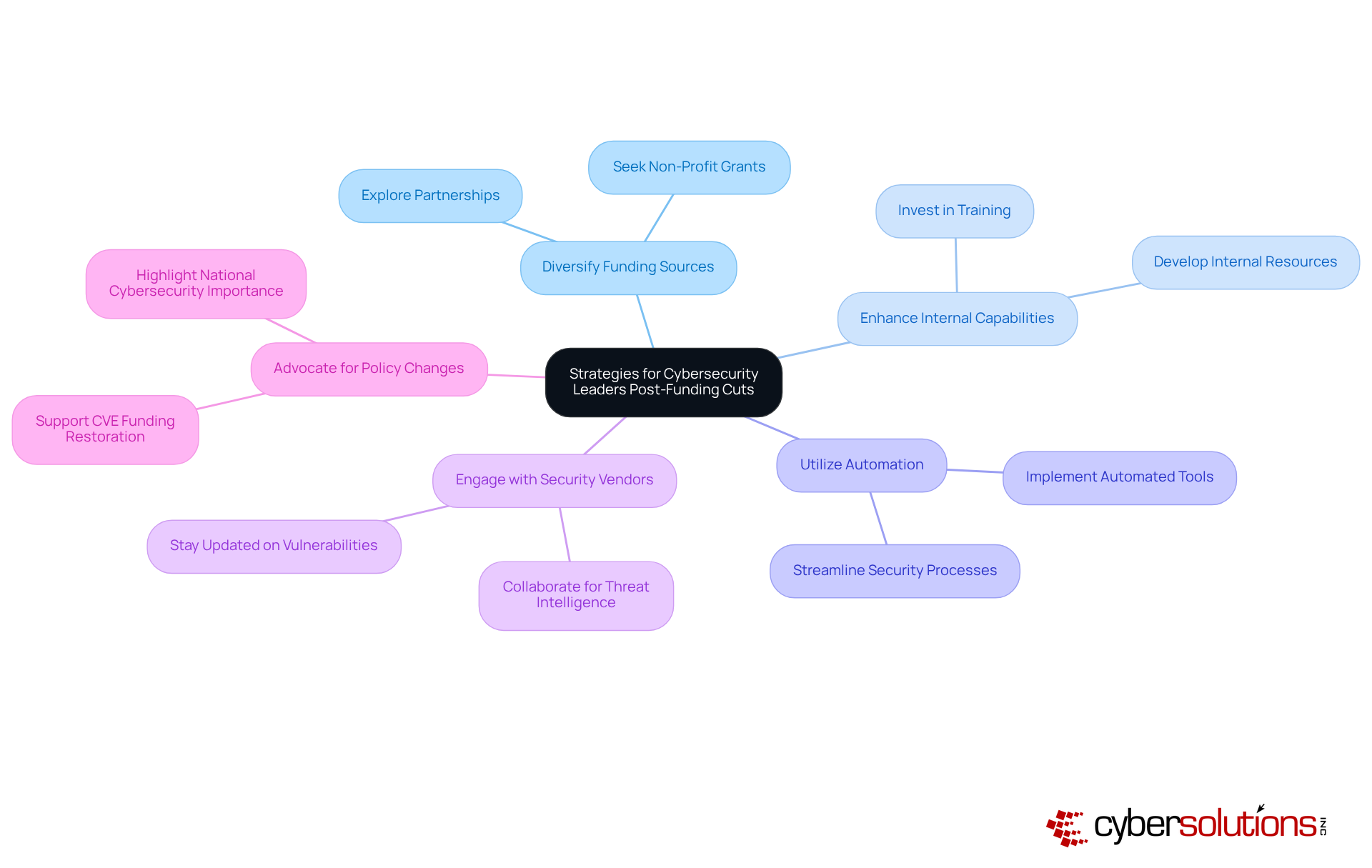
Diversify Funding Sources: Organizations should explore alternative funding models, such as forming partnerships with private sector entities or seeking grants from non-profit groups. This diversification can ensure the continuity of risk management initiatives despite the cve funding cut from federal support.
Enhance Internal Capabilities: Investing in training and resources for internal teams is crucial. By equipping personnel with the skills needed to handle vulnerabilities independently, organizations can reduce their reliance on external databases and strengthen their overall security posture. Data shows that companies actively training staff on minimizing internal risks experience a significant drop in security incidents.
Utilize Automation: Implementing automated tools for security flaw scanning and management can streamline processes and alleviate pressure on security teams. Automation not only boosts efficiency but also allows teams to concentrate on more strategic tasks, improving response times to emerging threats.
Engage with Security Vendors: Collaborating with security vendors is essential for staying informed about their strategies to address vulnerabilities in the absence of new CVEs. This engagement ensures that organizations are aware of emerging threats and can adjust their strategies accordingly. Notably, 51% of organizations are increasingly relying on commercial threat intelligence providers, underscoring the trend towards external collaboration.
Advocate for Policy Changes: Cybersecurity leaders should work with industry groups to support the reinstatement of funding for the CVE initiative. Highlighting the program's critical role in national cybersecurity can help garner support for its restoration, especially following the disbandment of the Cyber Safety Review Board, which has weakened information sharing.
By adopting these strategies, cybersecurity leaders can effectively navigate the challenges posed by cve funding cut and continue to protect their organizations against evolving cyber threats.
The CVE initiative stands as a cornerstone in cybersecurity, especially for organizations dedicated to protecting sensitive information. In an ever-evolving landscape, the ramifications of funding cuts to this essential program are profound. Disruptions in tracking and reporting vulnerabilities could pose significant risks, particularly in sectors like healthcare, where timely information is crucial for compliance and defense against cyber threats.
This article underscores the CVE program's vital role in vulnerability management. Funding cuts could delay vulnerability disclosures, increasing exposure to cyberattacks. Cybersecurity leaders must adopt key strategies:
These measures are not just about sustaining the CVE initiative; they empower organizations to bolster their cybersecurity posture amid uncertainty.
The call to action is unmistakable: organizations must prioritize resilience in their cybersecurity strategies. By actively pursuing diverse funding models and fostering collaboration within the cybersecurity community, leaders can ensure the CVE initiative's critical functions continue to thrive. This proactive approach is essential for maintaining robust defenses against the ever-evolving landscape of cyber threats, reinforcing the CVE program's significance in safeguarding valuable assets and building trust with stakeholders.
What is the CVE program?
The Common Vulnerabilities and Exposures (CVE) program is an initiative that recognizes and catalogs publicly disclosed cybersecurity weaknesses, providing a standardized approach for entities to exchange information about these vulnerabilities.
Who oversees the CVE initiative?
The CVE initiative is overseen by MITRE.
Why is the CVE initiative important for organizations?
The CVE initiative serves as a universal reference point for weakness management, fostering communication among security experts and enabling organizations to prioritize and address security threats effectively.
How does the CVE initiative help healthcare organizations?
The CVE initiative aids healthcare organizations in identifying potential risks and facilitates informed decision-making in security investments, which is crucial for safeguarding sensitive data.
What role does the CVE initiative play in enhancing security posture?
By maintaining a comprehensive database of vulnerabilities, the CVE initiative empowers organizations to enhance their security posture and comply with regulatory standards.
How does the CVE initiative support organizations in responding to threats?
The CVE initiative ensures that organizations can respond swiftly to emerging threats by providing a standardized method for sharing information about vulnerabilities.
In what way is the CVE initiative a vital resource for organizations?
The CVE initiative is a vital resource for organizations as it helps them protect their assets and maintain trust with their stakeholders in an era where cybersecurity threats are constantly evolving.