Introduction
Maximizing return on investment (ROI) in today’s competitive landscape is crucial for organizations aiming to thrive. The strategic alignment of IT solutions with industry-specific needs is not just beneficial; it’s essential. Tailored IT strategies enhance operational efficiency and ensure compliance with ever-evolving regulatory demands. But here’s the pressing question: how can companies effectively navigate the complexities of their unique environments while safeguarding against cybersecurity threats?
This article explores best practices for leveraging customized IT solutions and managed services to drive measurable ROI. By doing so, organizations can empower themselves to thrive amidst uncertainty. The landscape of cybersecurity threats is constantly changing, and healthcare organizations face unique challenges that require immediate attention.
As we delve deeper, we’ll uncover how Cyber Solutions can effectively address these challenges, ensuring that organizations not only protect their assets but also maximize their investment in technology.
Assess Industry-Specific Needs for Tailored IT Solutions
To maximize ROI through IT solutions and services, companies must conduct a thorough evaluation of their needs. This involves focusing on the unique challenges and regulatory requirements that different sectors face. For example, with healthcare technology, while financial institutions are required to adhere to strict compliance standards. Additionally, sectors such as manufacturing and government have specific regulations to protect operations and ensure security.
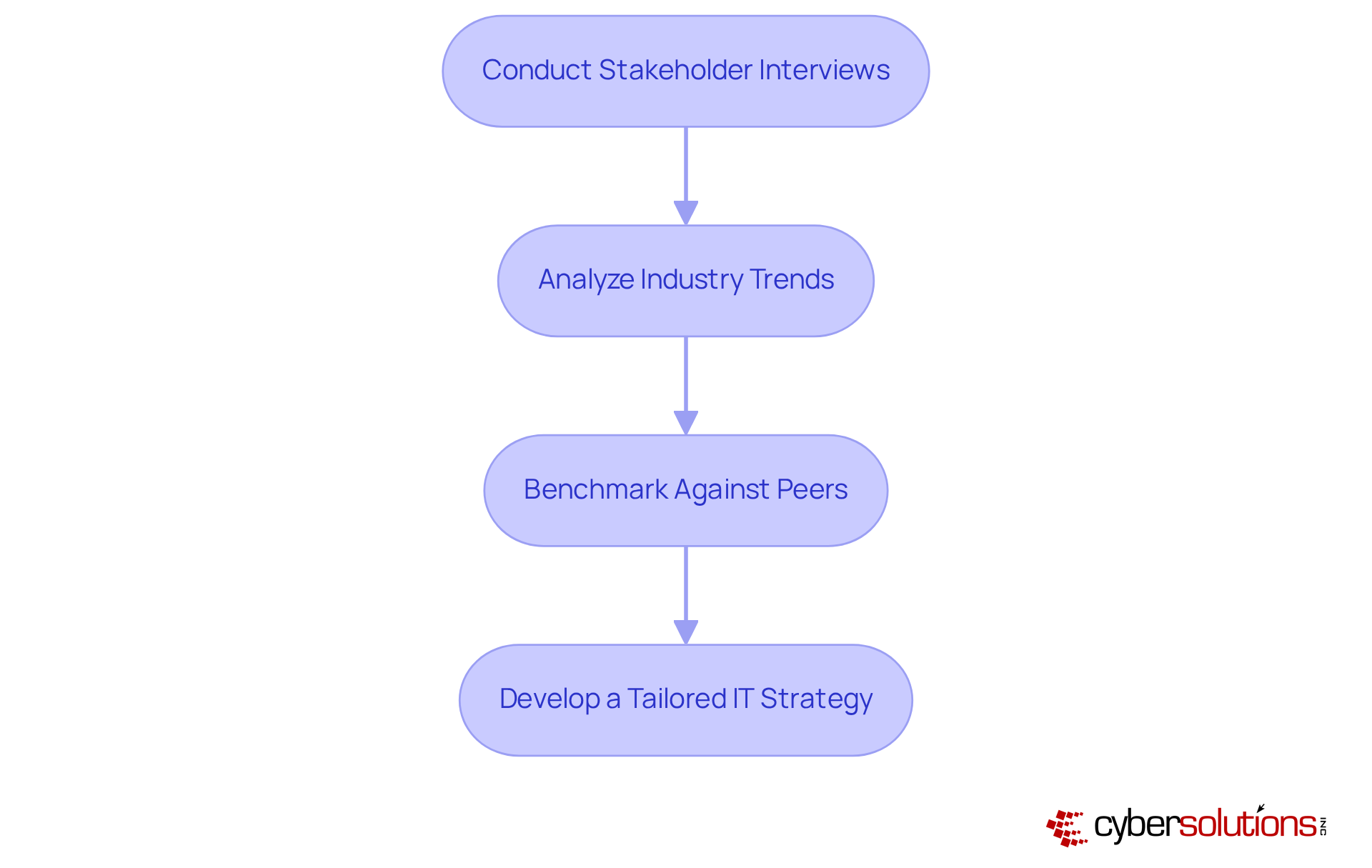
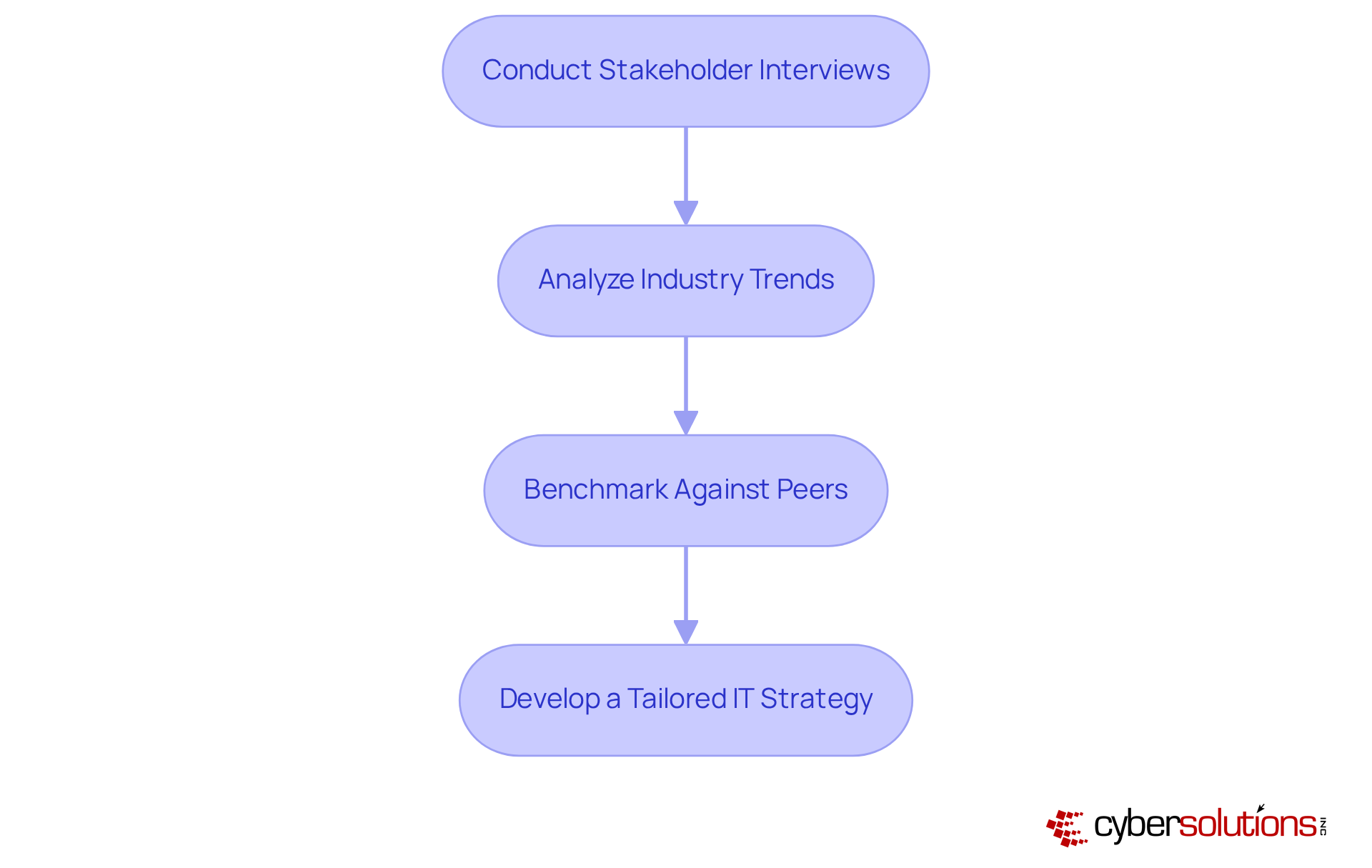
Action Steps:
- Conduct Stakeholder Interviews: Engage with key stakeholders to gather insights on their specific IT challenges and requirements. This step is crucial, as 76% of entities leverage technology solutions, underscoring the need for informed decision-making.
- Analyze Industry Trends: Stay updated on industry trends and regulatory changes that may impact IT needs. With 72% of entities utilizing technology for operational efficiency, understanding these trends is vital for compliance.
- Benchmark Against Peers: Compare your entity’s IT capabilities with those of industry counterparts to identify gaps and opportunities for improvement. This benchmarking reveals that 41% of entities report enhanced collaboration among teams due to technology expenditures, highlighting the importance of shared insights.
- Develop a Tailored IT Strategy: Based on the assessment, create a strategy that aligns with the entity’s goals and industry standards. This strategy should incorporate solutions like cloud services to streamline regulatory alignment, as 82% of entities plan to increase spending on technology to support adherence activities in 2025.
By focusing on these steps, entities can ensure their IT solutions and services are not only relevant but also strategically aligned with their operational objectives, ultimately leading to improved ROI. Customized IT strategies are essential for navigating the complexities of regulations, particularly in the evolving landscapes of healthcare and finance.
Implement Proactive Monitoring and Incident Response Strategies
Cybersecurity is not just a technical necessity; it’s a critical component of operational integrity in healthcare. With the rise of sophisticated cyber threats, organizations must prioritize cybersecurity measures and incident response as foundational elements of their strategy. By continuously monitoring systems and networks, entities can identify potential threats early, preventing them from escalating into significant incidents that could disrupt operations.
- Deploy Monitoring Tools: Implement advanced monitoring solutions, such as Cyber Solutions' cutting-edge technology, that deliver real-time insights into system performance and security threats. This enables swift detection of anomalies, ensuring that potential issues are addressed before they escalate.
- Establish an Incident Response Plan: Create a plan detailing the procedures to follow in the event of a security breach. This plan should ensure clarity in roles and responsibilities while meeting regulatory requirements, which is crucial for maintaining trust and accountability.
- Conduct Regular Drills: Regularly test the plan through simulated exercises. This practice allows team members to refine their response strategies and ensures that everyone knows their role during an actual incident.
- Utilize Threat Intelligence: Leverage threat intelligence to stay informed about emerging threats and vulnerabilities pertinent to your industry. This proactive approach enhances preparedness and allows for the adaptation of access controls, ensuring that only authorized users have access.
By adopting these strategies, companies can significantly mitigate the impact of cyber incidents, which can be achieved through effective planning, resulting in reduced recovery costs and improved ROI. The average cost of a data breach has reached $4.56 million in 2025, underscoring the necessity of effective cybersecurity measures. Furthermore, entities with mature cybersecurity practices tend to incur lower costs when breaches occur, highlighting the financial advantages of proactive measures. Are you prepared to safeguard your organization against these escalating threats?

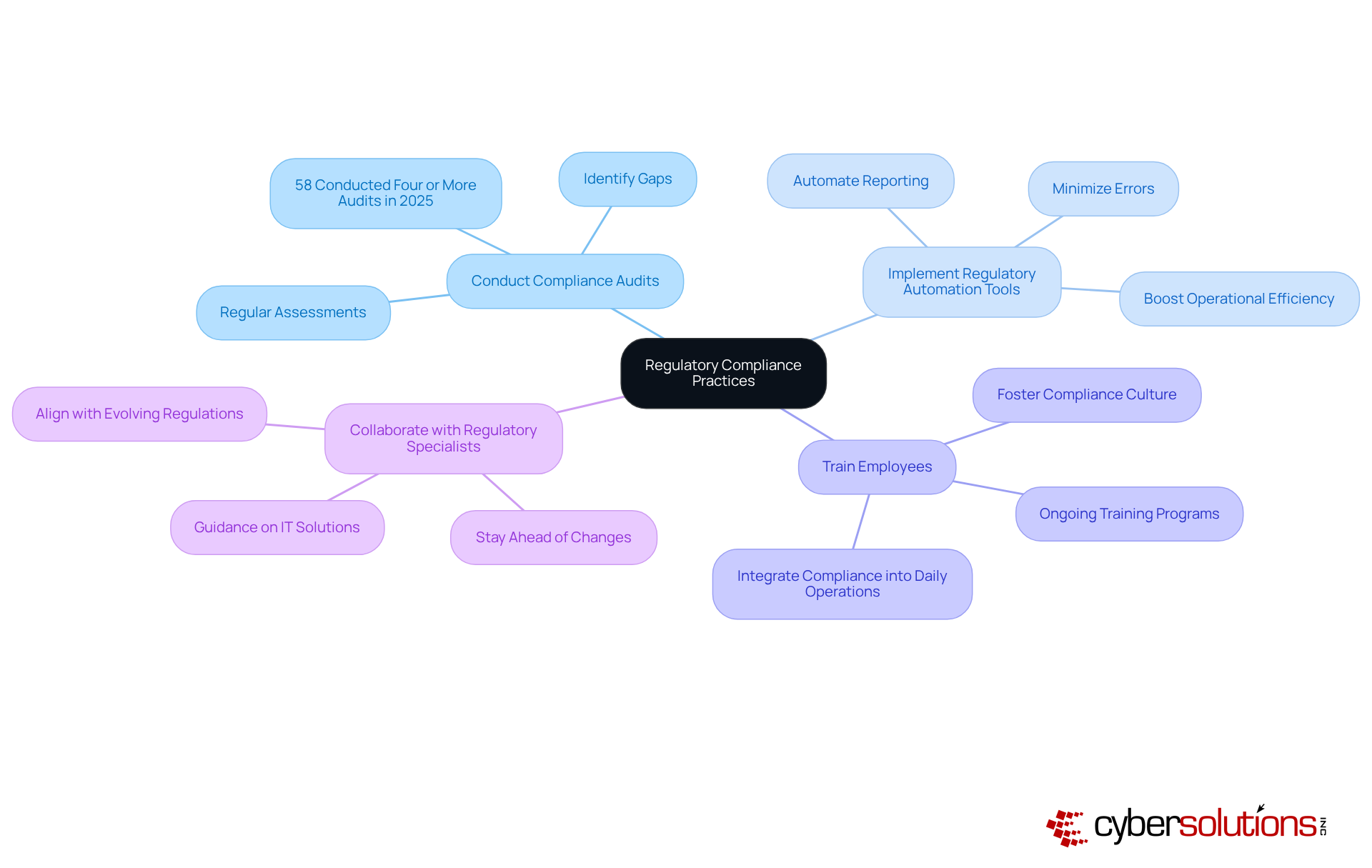
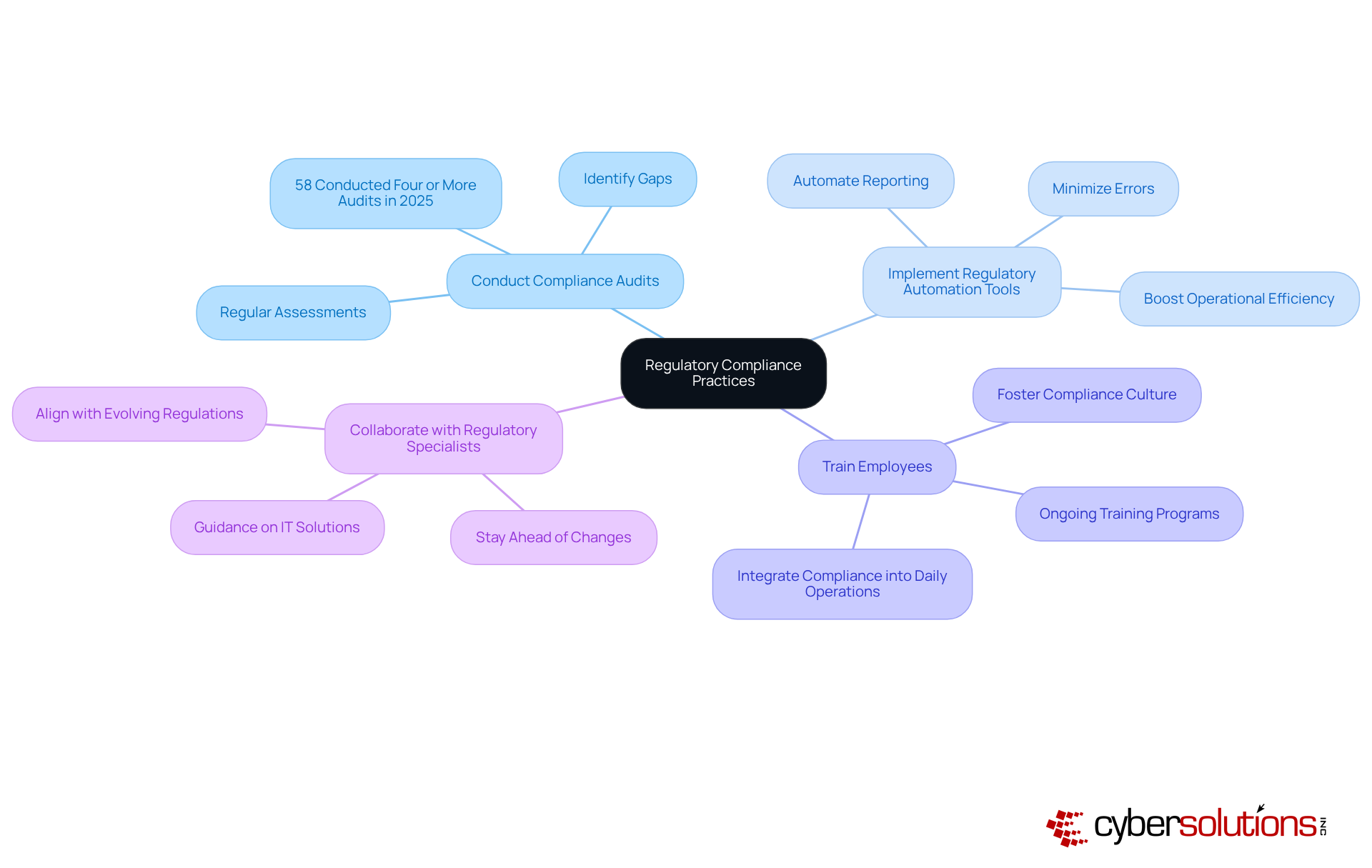
Navigate Regulatory Compliance with Effective IT Practices
Regulatory adherence is not just a necessity; it’s a critical challenge that organizations must navigate skillfully to avoid penalties and uphold stakeholder trust. By implementing effective strategies, compliance efforts can be streamlined, significantly enhancing overall security.
- Conduct regular assessments: Regular assessments of your organization’s adherence to relevant regulations are vital for pinpointing gaps and areas needing improvement. In 2025, a notable 58 percent of organizations conducted four or more audits, reflecting the growing intensity of compliance scrutiny.
- Implement automation: Leverage technology to automate reporting and monitoring for regulations. This not only eases the burden on staff but also minimizes errors, boosting operational efficiency. The increasing adoption of automation tools has become essential, with firms recognizing their role in transforming compliance from a burden into a strategic advantage.
- Provide training: Ongoing training for staff on regulatory requirements and best practices fosters a culture of adherence within the organization. This proactive approach is crucial as compliance becomes integrated into daily operations across various sectors.
- Collaborate with experts: Partnering with regulatory experts can help your organization stay ahead of changes and requirements. Their insights can guide effective strategies that are in alignment with the evolving regulatory landscape.
By embracing these practices, organizations can not only fulfill but also strengthen their compliance posture, ultimately leading to improved ROI.
Demonstrate ROI Through Strategic IT Investments
To maximize ROI, companies must effectively showcase the value of their IT investments. This is crucial not just for tracking financial metrics but for articulating the broader impact of IT on business objectives. A tailored solution, such as the one offered by Cyber Solutions, can simplify budgeting and enhance financial planning. By eliminating unforeseen IT costs and surprises, companies can plan their budgets with confidence.
- Establish Clear Metrics: Define metrics that align with business goals to assess the success of IT initiatives. In 2025, organizations are increasingly focusing on KPIs that reflect both financial performance and employee productivity. Notably, 64% of executives are using ROI as a primary metric for measuring ROI.
- Utilize Financial Models: Implement financial models that consider both direct and indirect advantages of IT solutions, such as increased productivity and reduced risk. With these models, organizations must ensure their financial strategies are robust.
- Regularly Report on ROI: Create regular reports that highlight the ROI of IT projects, showcasing both quantitative and qualitative benefits. This practice not only informs stakeholders but also reinforces the strategic value of IT initiatives.
- Engage Stakeholders: Involve key stakeholders to ensure alignment with organizational goals and secure ongoing support. Engaging C-suite leaders can facilitate a shared understanding of how IT contributes to overall business success.
By following these steps, organizations can effectively demonstrate the ROI of their IT solutions and managed services investments, leading to improved financial outcomes.

Conclusion
Maximizing ROI through tailored IT solutions and managed services is not just beneficial; it’s essential for organizations striving to enhance operational efficiency and navigate the complexities of their specific industries. In today’s rapidly evolving landscape, a thorough assessment of industry-specific needs allows companies to align their IT strategies with unique regulatory requirements and operational challenges. This alignment ultimately drives better financial outcomes.
Consider the strategies outlined in this article:
- Conducting stakeholder interviews
- Implementing proactive monitoring
- Establishing effective incident response plans
These steps do more than facilitate compliance with critical regulations; they significantly enhance cybersecurity measures, reducing the risk and financial impact of potential breaches. Furthermore, demonstrating the ROI of IT investments through clear metrics and regular reporting empowers organizations to articulate the value of their technology expenditures to stakeholders.
As digital transformation accelerates, organizations must prioritize tailored IT solutions that address their unique challenges. Investing in customized strategies and proactive measures not only improves compliance and security posture but also yields significant financial benefits. Embracing these best practices is not merely a strategic choice; it’s a necessary step toward sustaining growth and competitiveness in an ever-evolving market.
Frequently Asked Questions
Why is it important to assess industry-specific needs for IT solutions?
Assessing industry-specific needs is crucial to maximize ROI through IT solutions and managed services. It helps companies address unique challenges and regulatory requirements specific to their sectors, such as compliance with HIPAA in healthcare or PCI-DSS in finance.
What are some action steps for evaluating IT needs?
Key action steps include conducting stakeholder interviews to gather insights, analyzing industry trends and regulatory changes, benchmarking against peers to identify gaps, and developing a tailored IT strategy that aligns with the entity’s goals and industry standards.
How can stakeholder interviews help in assessing IT needs?
Engaging with key stakeholders helps gather insights on specific IT challenges and requirements, which is essential for informed decision-making. This is highlighted by the fact that 76% of entities leverage technology for risk assessments.
Why is it important to analyze industry trends?
Staying updated on industry trends and regulatory changes is vital for compliance, as 72% of entities utilize technology for disclosures and reporting. Understanding these trends helps organizations adjust their IT needs accordingly.
What is the benefit of benchmarking against peers?
Benchmarking against peers allows entities to compare their IT capabilities with those of industry counterparts, helping to identify gaps and opportunities for improvement. It has been shown that 41% of entities report enhanced collaboration among teams due to technology expenditures.
What should a tailored IT strategy include?
A tailored IT strategy should align with the entity’s goals and industry standards, incorporating solutions like Compliance as a Service (CaaS) to streamline regulatory alignment. Additionally, 82% of entities plan to increase spending on technology to support adherence activities in 2025.
How do customized IT strategies impact ROI?
Customized IT strategies ensure that IT solutions and managed services are relevant and strategically aligned with operational objectives, ultimately leading to improved ROI by navigating the complexities of regulations, especially in sectors like healthcare and finance.
List of Sources
- Assess Industry-Specific Needs for Tailored IT Solutions
- Three Critical Healthcare Compliance Trends for 2025 (https://virsys12.com/three-critical-healthcare-compliance-trends-for-2025)
- verisys.com (https://verisys.com/resources/november-2025-legislative-and-compliance-healthcare-updates)
- 110 security and compliance statistics for tech leaders to know in 2025 (https://vanta.com/resources/compliance-statistics)
- Healthcare Regulatory Compliance Challenges in 2025 (https://onec1.com/blog/healthcare-regulatory-compliance-challenges-in-2025)
- 2025 HIPAA Journal Annual Survey Published: Key Insights into Compliance Challenges (https://hipaajournal.com/2025-hipaa-journal-annual-survey-results)
- Implement Proactive Monitoring and Incident Response Strategies
- Industry Insights: Building resilience into broadcast cybersecurity (https://newscaststudio.com/2025/12/18/industry-insights-building-resilience-into-broadcast-cybersecurity)
- What is an Incident Response Plan? Know the 5 Basic Steps (https://bitsight.com/blog/how-create-incident-response-plan-5-steps)
- CSIRP Guide 2025: Build a Modern Incident Response Plan (https://blog.rsisecurity.com/a-guide-to-create-a-security-incident-response-plan-csirp)
- Incident Response Best Practices For 2025 (https://purplesec.us/learn/incident-response-best-practices)
- Surviving an Attack: Incident Response Plans, Business Continuity Best Practices, and More (https://allcovered.com/blog/surviving-an-attack-incident-response-plans-business-continuity-best-practices-and-more)
- Navigate Regulatory Compliance with Effective IT Practices
- 2025 Regulatory Compliance and Enforcement Recap: Recalibration, Not Retreat | Smarsh (https://smarsh.com/blog/thought-leadership/2025-regulatory-compliance-enforcement-recap)
- Wolters Kluwer Indicator survey finds lower concern levels following significant drop in regulatory penalties (https://wolterskluwer.com/en/news/indicator-survey-finds-lower-concern-levels-following-significant-drop-in-regulatory-penalties)
- beinformed.com (https://beinformed.com/2025-compliance-upheaval-key-lesson-for-a-strong-strategy-in-2026)
- Reflecting on 2025 Compliance Trends: 7 Key Regulatory Developments and Shifts - Tetra Tech Sustainable Markets (https://sustainable-markets.com/2025-compliance-trends)
- frost.com (https://frost.com/growth-opportunity-news/security/cybersecurity/compliance-reimagined-how-automation-is-turning-regulatory-burden-into-business-advantage-in-2025-sec02_tg01_compliance-automation_nov25-cim-pb)
- Demonstrate ROI Through Strategic IT Investments
- How Are Businesses Calculating ROI On AI Investment? (https://forbes.com/sites/forbes-research/2025/10/08/ai-roi-measurement-challenges-forbes-survey-2025)
- deloitte.com (https://deloitte.com/us/en/insights/topics/digital-transformation/ai-tech-investment-roi.html)
- From Caution to Core Strategy: New Study Shows CFOs Going All In on AI (https://salesforce.com/news/stories/cfos-invest-ai-for-growth)
- Sensor data is key to generating ROI from AI investments (https://facilitiesdive.com/news/sensor-data-is-key-to-generating-roi-from-ai-investments/806901)
- How to maximize AI ROI in 2026 | IBM (https://ibm.com/think/insights/ai-roi)