
In today’s world, where cyber threats escalate daily, organizations face an urgent need to safeguard their IT infrastructure and data. The stakes are high, and the consequences of inaction can be devastating. A managed services consultant emerges as a pivotal ally for leaders, offering expertise that not only enhances cybersecurity measures but also streamlines operational efficiency.
However, with so many providers available, how can decision-makers discern the true value that a managed services consultant brings to their organization? This article delves into the essential roles and responsibilities of these consultants, exploring how they empower businesses to navigate the complexities of the digital landscape while mitigating risks and optimizing performance.
By understanding the unique challenges posed by cyber threats, organizations can better appreciate the critical support that managed services consultants provide. They are not just service providers; they are strategic partners in ensuring the security and efficiency of your operations.
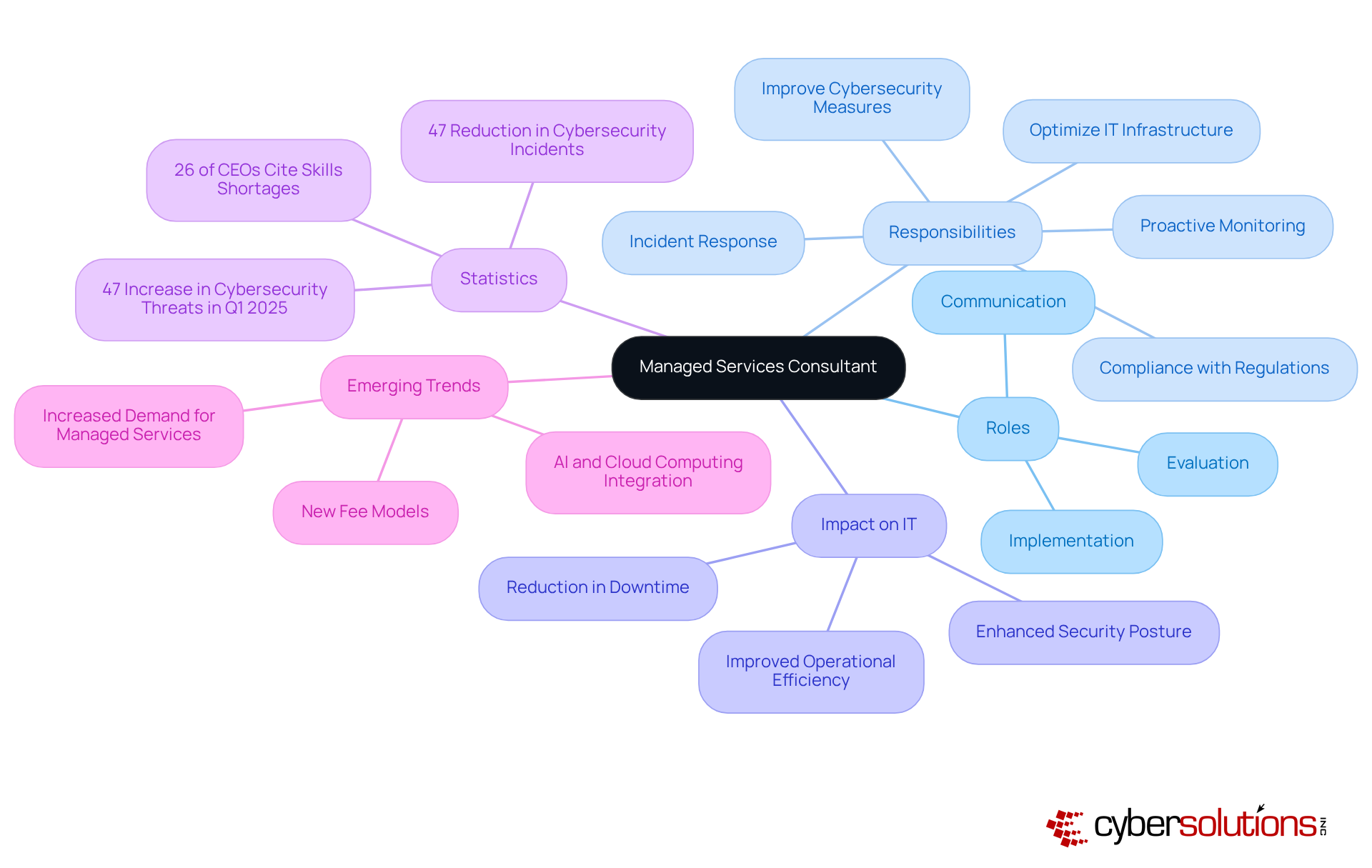
A Managed Services Consultant (MSC) plays a crucial role in guiding organizations to optimize their IT infrastructure and improve cybersecurity measures. With the current landscape of technology becoming increasingly complex, the role of a consultant has never been more critical. As a trusted advisor, their primary responsibilities encompass a thorough evaluation of the existing IT environment, pinpointing vulnerabilities, and proposing customized solutions that align with the organization's strategic objectives.
Managed service companies oversee the implementation of these services, ensuring that businesses benefit from proactive monitoring, incident response, and risk management. By serving as a vital link between technical teams and executive leadership, a consultant fosters effective communication and strategic alignment, which are essential for bolstering the overall IT posture of the organization.
Statistics underscore the effectiveness of these services in driving IT optimization. Organizations that leverage managed services report a notable decrease in downtime and improved operational efficiency. For instance, proactive IT management, supported by managed service providers offering advanced threat detection, has led to a remarkable 47% reduction in cybersecurity incidents. This enables businesses to focus on their core functions rather than being bogged down by technical challenges.
Moreover, managed service companies provide critical insights into emerging technologies. This empowers organizations to harness advancements like AI and cloud computing, enhancing both productivity and security. In today’s rapidly evolving digital landscape, the role of Managed Service Companies is not merely beneficial; it is essential for organizations striving to thrive amidst increasing complexity and cyber threats.
Furthermore, with 26% of CEOs identifying skills shortages as a significant risk to their operations, managed service companies are becoming indispensable in bridging these gaps and ensuring compliance with industry-specific regulations, such as CMMC Level 2 for safeguarding Controlled Unclassified Information (CUI). The demand for constant vigilance against cyber threats, which saw a reported 47% increase in Q1 2025, further highlights the importance of managed services in mitigating these risks. As the managed services landscape continues to evolve, innovation is key, allowing managed service companies to tailor their offerings to better meet client needs.
In the current digital landscape, cybersecurity is not just an option; it’s a necessity, especially in healthcare. A managed services consultant is crucial in helping organizations navigate the complexities of escalating and stringent regulatory requirements. Their expertise empowers businesses to adopt a proactive IT management approach, significantly reducing the risk of cyber threats. By implementing industry best practices and advanced security measures, managed service companies ensure robust protection.
Consider the impact of partnering with managed services consultants. Companies that do often report enhanced security frameworks and improved compliance, both essential in mitigating the effects of cyber incidents. A recent case involving a healthcare provider recovering from a ransomware attack underscores the importance of swift action and specialized expertise. Thanks to rapid deployment and teamwork, the provider not only recovered ahead of schedule but also fortified its security measures to protect patient data against future threats. This incident highlights that acting quickly is vital to minimizing damage, and having an incident response team on-site can significantly contain threats through a layered approach, including endpoint isolation, malware removal, and user training.
Moreover, implementing application whitelisting is a proactive strategy that Managed Service Companies (MSCs) can employ to prevent unauthorized software from executing. This approach reduces vulnerabilities and ensures compliance with regulations. By allowing only authorized applications to run, organizations can effectively block malware and ransomware before they inflict damage. This method not only enhances security but also aids companies in meeting stringent compliance requirements.
With the rise of sophisticated attacks, including phishing campaigns and malware targeting vulnerabilities, the urgency for cybersecurity measures has never been more pressing. Alarmingly, 65% of leading AI firms have been found with confirmed leaks of sensitive information, underscoring the need for organizations to strengthen their defenses.
Additionally, MSCs provide strategic insights that enable organizations to allocate resources effectively, ensuring that IT investments yield maximum returns while minimizing risks. This is particularly crucial as 26% of CEOs identify skills shortages as a significant risk to their businesses, emphasizing the value of leveraging external expertise. Furthermore, the Cybersecurity Maturity Model Certification (CMMC) is required for handling contracts with the U.S. Department of Defense, further illustrating the importance of compliance. By collaborating with a managed services consultant, organizations can focus on their core operations, confident that their IT and security needs are managed by skilled experts. Recent incidents, such as the data breach alert from Spanish airline Iberia, demonstrate the consequences of inadequate online security practices, highlighting the critical role of Managed Security Companies in preventing such events. Ultimately, these partnerships enable organizations to thrive in an increasingly regulated and perilous environment.

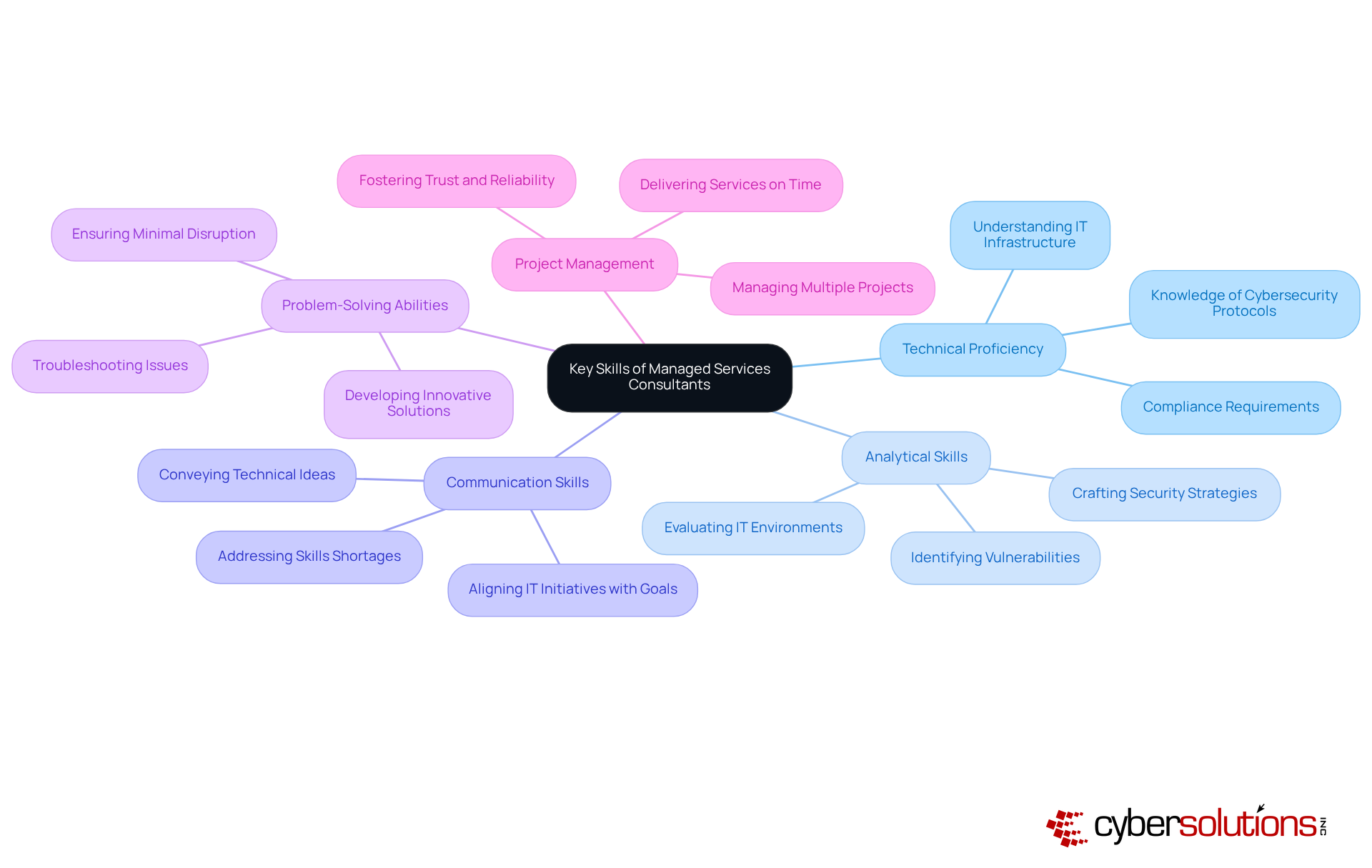
In today's rapidly evolving digital landscape, the importance of managed services consultants cannot be overstated. An effective consultant embodies a unique combination of technical expertise and interpersonal skills, essential for navigating the complexities of IT and information security. Here are the key competencies that set them apart:
These traits enable consultants to effectively assist healthcare organizations in achieving their IT and security objectives, ultimately promoting commercial success. By leveraging these competencies, they can navigate the complexities of cybersecurity, ensuring that healthcare providers can focus on what they do best—caring for patients.
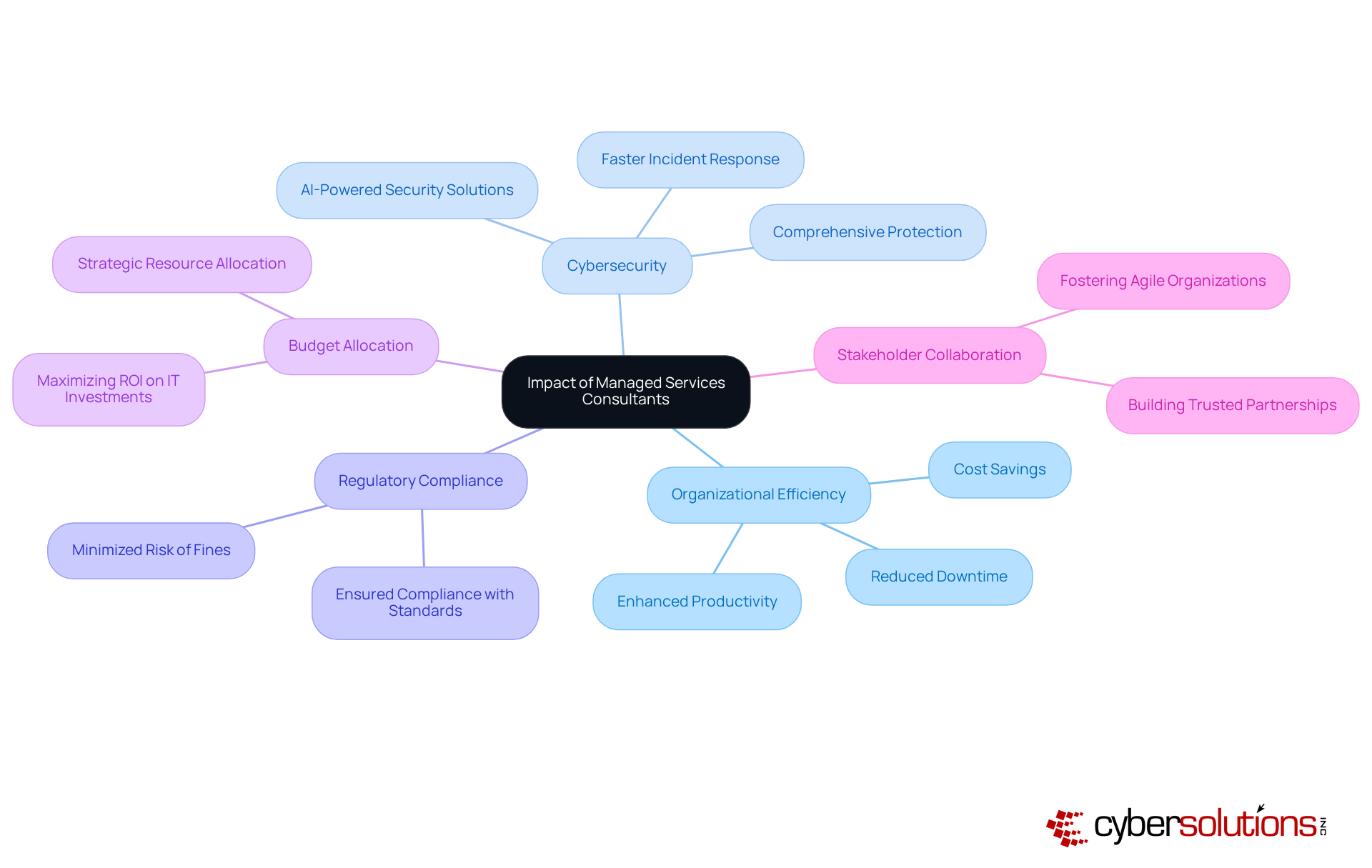
The impact of managed services consultants on organizational efficiency and security is profound. In today’s digital landscape, where cyber threats are prevalent, organizations must prioritize robust and comprehensive cybersecurity strategies. By partnering with a managed services consultant, businesses can significantly reduce downtime and enhance productivity.
For instance, organizations that collaborate with managed service providers often report faster response times, which can dramatically mitigate the effects of cyber threats. This is particularly crucial in sectors like healthcare, where the stakes are high. Furthermore, MSCs play a vital role in ensuring data protection, thereby minimizing the risk of breaches.
Their expert insights empower companies to make informed decisions, directing resources toward initiatives that promise the highest returns. Ultimately, fostering collaboration among multiple stakeholders cultivates a more resilient and agile organization, well-prepared to navigate the complexities of today’s digital environment.
As the cybersecurity market is projected to grow by 15% in 2024, the demand for managed services consultants (MSCs) is set to rise, underscoring their essential role in modern business strategies. Are you ready to leverage the expertise of MSCs to fortify your organization against emerging threats?
The role of a managed services consultant is not just important; it’s essential for organizations striving to bolster their IT infrastructure and cybersecurity measures. In a landscape fraught with digital threats and regulatory challenges, these consultants provide invaluable guidance and strategic insights, helping businesses navigate complexities while ensuring resilience and compliance.
Key responsibilities of managed services consultants include:
Their expertise mitigates risks associated with cybersecurity threats and empowers organizations to harness advanced technologies, optimizing operational efficiency. Statistics reveal the tangible benefits of partnering with managed service providers, such as reduced downtime and enhanced incident response capabilities.
Ultimately, managed services consultants are more than just IT support; they are pivotal partners in driving organizational success. As businesses confront escalating cyber threats and stringent regulatory requirements, leveraging the expertise of managed services consultants is not merely a strategic advantage - it’s a crucial step toward safeguarding operations and ensuring sustainable growth. Organizations should reflect on how these partnerships can elevate their security posture and operational performance, paving the way for a more secure and efficient future.
What is the role of a managed services consultant (MSC)?
A managed services consultant guides organizations in optimizing their IT infrastructure and improving cybersecurity measures by evaluating existing IT environments, identifying vulnerabilities, and proposing customized solutions.
How do managed service companies support organizations?
Managed service companies oversee the implementation of services, providing proactive monitoring, incident response, and ensuring compliance with industry regulations.
What benefits do organizations experience from managed services?
Organizations that utilize managed services report decreased downtime and improved operational efficiency, including a 47% reduction in cybersecurity incidents due to proactive IT management.
What kind of insights do managed service companies provide?
Managed service companies offer insights into emerging technologies and robust firewall and network security solutions, helping organizations leverage advancements like AI and cloud computing.
Why are managed service companies essential in today's digital landscape?
They are essential for organizations to thrive in a complex digital environment, helping them address increasing cybersecurity threats and skills shortages, as well as ensuring compliance with industry-specific regulations.
What is the significance of skills shortages for managed service companies?
Skills shortages pose a significant risk to operations, making managed service companies vital in bridging these gaps and ensuring compliance with regulations such as CMMC Level 2 for safeguarding Controlled Unclassified Information (CUI).
How has the demand for cybersecurity vigilance changed recently?
The demand for vigilance against cybersecurity threats has increased, with a reported 47% rise in such threats in Q1 2025, highlighting the importance of managed security companies in mitigating these risks.
Are there new fee models emerging in the managed services landscape?
Yes, new fee models are emerging, allowing managed service companies to tailor their offerings to better meet client needs as the managed services landscape continues to evolve.