
Creating a robust Acceptable Use Policy (AUP) is not just important; it’s essential for organizations, particularly in the healthcare sector where sensitive information is at stake. With cyber threats evolving at an alarming rate, how can organizations ensure their policies remain effective and relevant? This guide outlines a step-by-step approach to developing an AUP that not only meets legal compliance but also fosters a culture of cybersecurity awareness among users. By exploring these essential steps, organizations can proactively safeguard their digital assets while clarifying user responsibilities and mitigating risks.
In today’s landscape, the stakes are higher than ever. Cybersecurity threats are not merely a possibility; they are a reality that healthcare organizations must confront head-on. The implications of inadequate policies can be severe, leading to data breaches that compromise patient trust and incur hefty fines. Therefore, it’s crucial for CFOs and decision-makers to understand the unique challenges they face in this environment.
By implementing a well-structured AUP, organizations can create a framework that not only protects sensitive information but also empowers users to act responsibly. This proactive approach not only enhances compliance but also cultivates a culture of vigilance and accountability. As we delve deeper into the essential steps for crafting an effective AUP, consider how these measures can fortify your organization against the ever-present threat of cyberattacks.
In today's digital landscape, the importance of cybersecurity in healthcare cannot be overstated. Protecting sensitive information is not just a goal; it's a fundamental responsibility that organizations must embrace. An acceptable use policy serves as a critical framework for cybersecurity, ensuring compliance with legal standards such as HIPAA, and fostering a secure environment.
The purpose of this acceptable use policy (AUP) is to outline acceptable practices for using company resources to protect sensitive information and maintain data integrity. By implementing this policy, organizations can prevent unauthorized software from executing, significantly reducing vulnerabilities and enhancing their security posture. This proactive approach not only protects the organization but also instills confidence among users, clarifying their responsibilities and the rationale behind the guidelines.
Ultimately, a well-defined AUP contributes to a more secure and compliant organizational environment. As healthcare organizations face increasing cyber threats, it is imperative to adopt robust policies that address these threats effectively. By prioritizing cybersecurity, CFOs can lead their organizations toward a safer digital future.

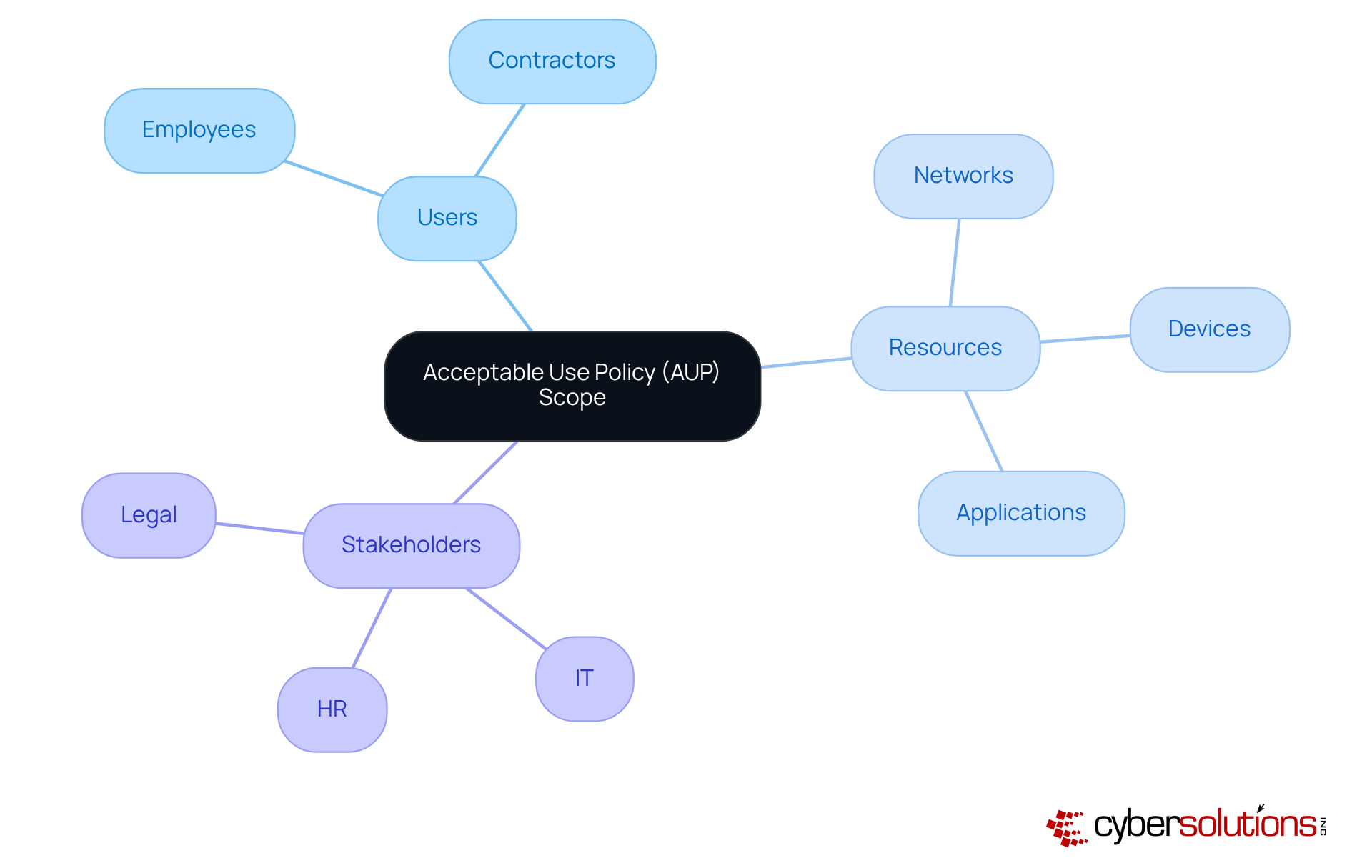
To effectively define the scope of your Acceptable Use Policy, it’s essential to specify which users - such as employees and contractors - and resources, including networks, devices, and applications, the policy will cover. Cybersecurity is not just a technical issue; it’s a critical component of safety in today’s digital landscape. Engaging with key stakeholders is vital for gathering feedback and ensuring that the guidelines comprehensively address all relevant issues.
For instance, you might state: 'This guideline pertains to all employees and contractors utilizing company-owned devices and networks.' This collaborative approach not only fosters buy-in but also enhances the policy's effectiveness. It aligns with Cyber Solutions' commitment to security and tailored solutions, including training and support, which are crucial for maintaining security and compliance.
In a world where threats are ever-evolving, organizations must remain vigilant. How can your organization ensure that its policy is not only compliant but also effective in practice? By implementing these guidelines, you take a proactive step towards safeguarding your resources and maintaining trust with stakeholders.
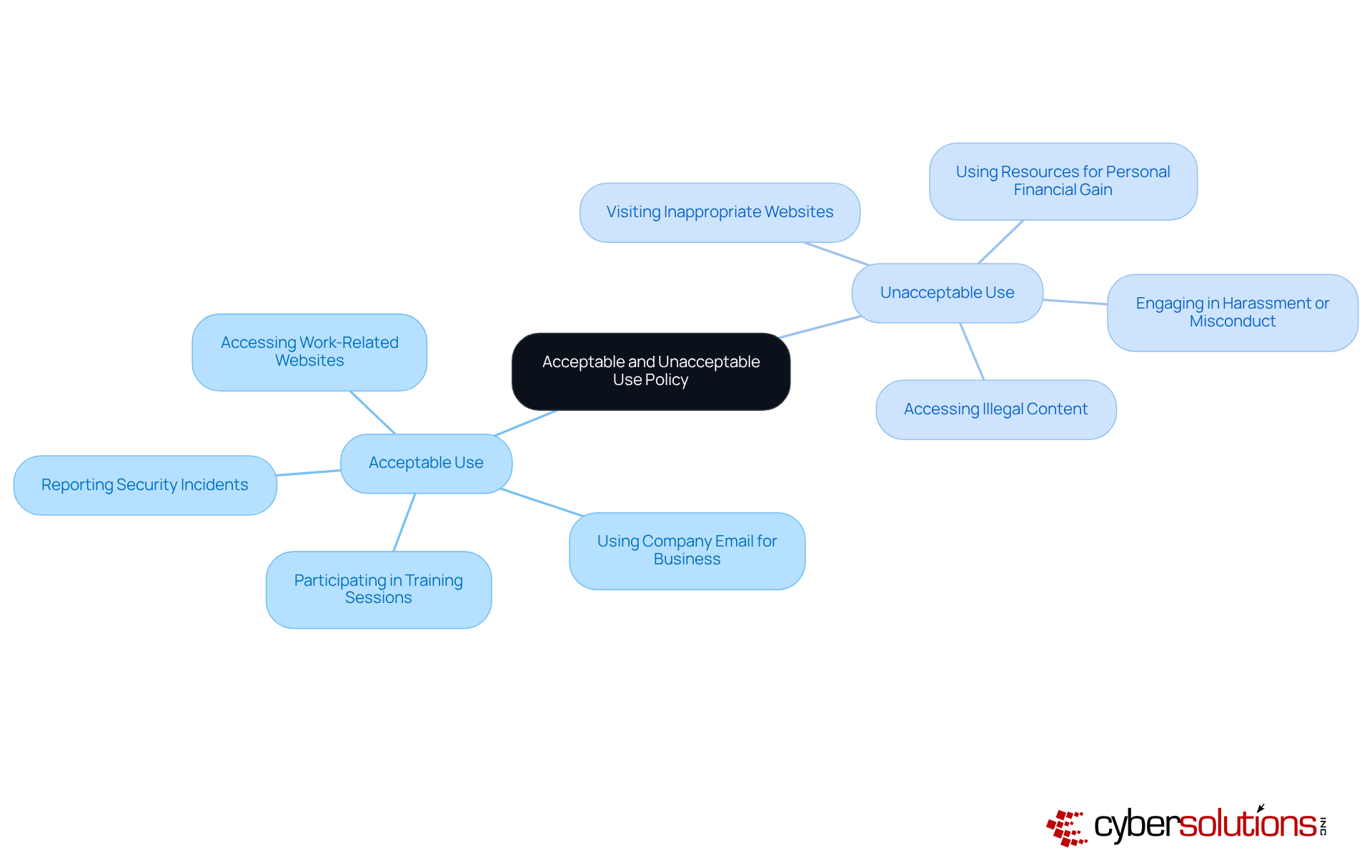
In this section, it is crucial to explicitly define what constitutes acceptable and unacceptable use. Acceptable use may include accessing work-related websites and utilizing company email for business communication. In contrast, unacceptable use could involve visiting inappropriate websites or using company devices for personal financial gain. For instance, employees must not use company resources to access illegal content or engage in activities that could harm the organization’s reputation. This clarity is essential for helping users understand the boundaries of acceptable behavior.
Data breaches, with a staggering 88% of data breaches attributed to such mistakes. Therefore, effectively communicating these guidelines is essential. Organizations should offer training and share written guidelines that explain the policy in clear language, ensuring that all employees comprehend their responsibilities. Regular reminders and updates can reinforce these policies, fostering a culture of compliance and accountability. As Emily Bonnie states, 'An acceptable use policy establishes your information technologies in a way that keeps both the entity and employees safe.' Additionally, outlining the consequences of non-compliance is crucial to ensure accountability among users.
Establishing clear security expectations in your organization is essential for cultivating a robust culture of cybersecurity awareness among users. In today’s landscape, where threats are increasingly sophisticated, organizations must prioritize guidelines that encompass critical practices such as:
For instance, consider specifying: 'Users are required to create passwords that are at least 16 characters long, change them regularly, and report any security incidents immediately.' This proactive approach not only empowers users to take responsibility but also aligns with findings that reveal 42% of hacked individuals relied on weak passwords.
Moreover, emphasizing the importance of security training can significantly reduce the risk of breaches. Security awareness training is essential for modern organizations. By integrating these expectations into the acceptable use policy, organizations can fortify their overall security framework and mitigate potential risks associated with user behavior.
In conclusion, a well-defined acceptable use policy not only sets clear security expectations but also fosters a culture of accountability, ultimately enhancing the organization’s resilience against cyber threats.

Incorporating relevant legal and compliance requirements into your policy is essential for safeguarding sensitive information and ensuring adherence to industry regulations. This is particularly critical in sectors like healthcare, where regulations such as HIPAA come into play. For instance, your AUP might state: 'All users must adhere to relevant laws when managing sensitive information.' This establishes clear expectations and underscores the importance of compliance.
Legal experts emphasize that integrating these regulations into your policy can significantly enhance your organization's protection policies. GDPR, for example, mandates that organizations implement strict handling protocols, which should be clearly outlined in the AUP to mitigate risks associated with breaches. Similarly, CCPA necessitates transparency, which requires that your policy includes explicit guidelines regarding the management of such data.
Moreover, consider adopting application whitelisting as a key component of your cybersecurity strategy. This proactive measure not only prevents unauthorized software from executing but also aids in risk management. By allowing only approved applications to run, application whitelisting minimizes vulnerabilities that attackers could exploit, effectively reducing the attack surface. Continuous monitoring of application activity and centralized management of allowlists can further bolster your security posture.
Consulting with legal counsel during the development of your policy is advisable to ensure that the framework is comprehensive, enforceable, and aligned with current legal standards. This collaboration can help identify potential gaps and provide insights into best practices for effectively addressing legal, regulatory, and PCI-DSS requirements. By doing so, organizations can cultivate a culture of compliance and accountability, ultimately enhancing their overall security posture.

Non-compliance with the policy can have serious implications. From verbal warnings to termination, the repercussions vary based on the severity of the violation. For instance, repeated offenses may lead to disciplinary action, up to and including dismissal.
Education is crucial for awareness within the organization, particularly in relation to the acceptable use policy. When employees recognize the consequences of their actions, they are more likely to adhere to the guidelines. This not only protects the organization but also promotes a secure and productive environment.

Establishing a timetable for the review of the AUP is crucial in today’s cybersecurity landscape. Regular reviews, ideally on a yearly basis or whenever significant changes occur within the organization or its technology, ensure that the policy remains effective. For instance, you might declare: 'This policy will be reviewed to ensure its effectiveness and relevance.'
Involving stakeholders in this process is essential. Their feedback can provide valuable insights, allowing for adjustments that ensure the policy continues to meet the needs of the organization. By fostering collaboration, you not only enhance the policy's effectiveness but also strengthen the organization's overall security posture.

Establishing an effective Acceptable Use Policy (AUP) is not just a fundamental step for organizations; it is a critical necessity, especially in the healthcare sector where safeguarding sensitive information is paramount. In an era where cyber threats are increasingly sophisticated, a well-crafted AUP serves as a cornerstone for fostering a culture of cybersecurity awareness and compliance among users. By prioritizing a structured AUP, organizations can significantly bolster their defenses against the ever-evolving landscape of cyber threats.
Key steps in developing a robust AUP include:
Regular reviews and updates ensure that the AUP remains relevant and effective, adapting to new challenges as they arise.
In a landscape where data breaches can lead to devastating consequences, implementing a well-crafted AUP transcends regulatory obligation; it becomes a strategic necessity. Organizations must take proactive measures to protect their digital assets and foster a culture of accountability among users. By doing so, they not only safeguard sensitive information but also build trust with stakeholders, ultimately enhancing their resilience against cyber threats.
What is the purpose of an Acceptable Use Policy (AUP)?
The purpose of an AUP is to outline acceptable practices for using company resources to protect sensitive information, ensure compliance with legal standards, and foster a culture of responsible technology use.
Why is cybersecurity important in healthcare?
Cybersecurity is crucial in healthcare because it protects sensitive information, which is not only a regulatory requirement but also a fundamental responsibility of organizations.
What are some legal standards that an AUP helps organizations comply with?
An AUP helps organizations comply with legal standards such as HIPAA, PCI-DSS, and GDPR.
How does application allowlisting enhance cybersecurity?
Application allowlisting prevents unauthorized software from executing, significantly reducing vulnerabilities and enhancing an organization's cybersecurity posture.
Who should be involved in establishing the scope of an AUP?
Key stakeholders such as IT, HR, and legal divisions should be involved in establishing the scope of an AUP to gather feedback and ensure comprehensive guidelines.
What resources should an AUP specify?
An AUP should specify which users (e.g., employees and contractors) and resources (e.g., networks, devices, and applications) the policy will cover.
How can organizations ensure their AUP is effective in mitigating risks?
Organizations can ensure their AUP is effective by engaging stakeholders, gathering feedback, and continuously updating the policy to address evolving cybersecurity threats.
What is the role of CFOs in relation to cybersecurity and AUPs?
CFOs can lead their organizations toward a safer digital future by prioritizing cybersecurity and implementing robust policies like AUPs that address security threats effectively.