
In today's digital landscape, the threat of cyberattacks looms larger than ever, making robust security measures not just important, but essential for C-suite leaders responsible for safeguarding sensitive information. As we move into 2025, organizations face a myriad of cybersecurity challenges, and dark web scanners have emerged as critical tools in this fight. These scanners provide invaluable insights into potential data breaches and compromised credentials, helping leaders stay one step ahead of the ever-evolving risks that lurk in the shadows of the internet.
But with so many options available, how can executives determine which scanners deliver the most effective protection? The stakes are high, and the consequences of inaction can be devastating. It's time for leaders to take a proactive stance in their cybersecurity strategies, ensuring they have the right tools to combat these threats head-on.
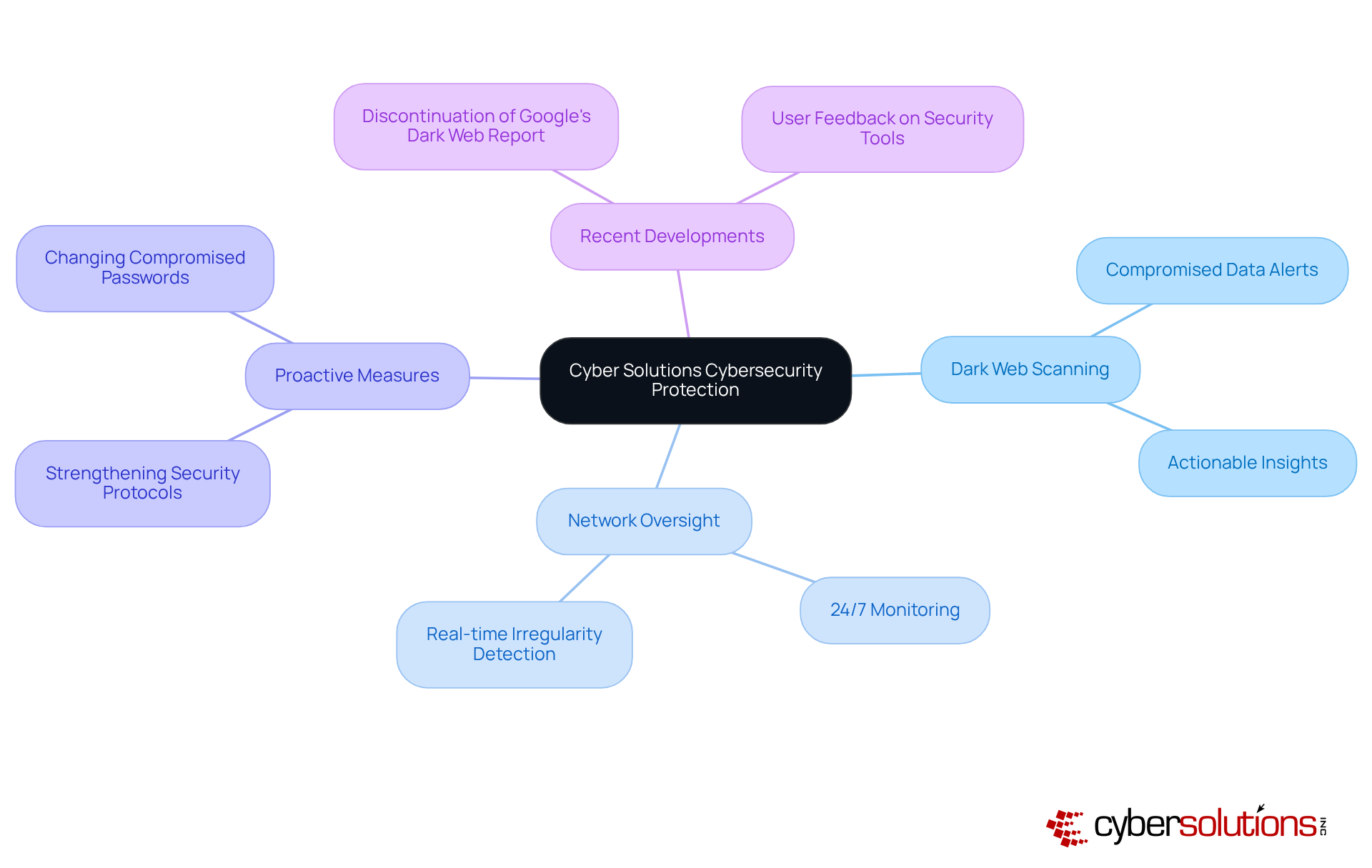
In today’s digital landscape, the importance of cybersecurity cannot be overstated, especially for healthcare organizations. With cyber threats evolving at an alarming rate, CFOs face unique challenges in cybersecurity. Cyber Solutions offers a cutting-edge deep web scanner that vigilantly monitors the concealed corners of the internet for any compromised data associated with your organization. This tool not only alerts you to potential breaches but also delivers actionable insights to effectively mitigate risks. By employing sophisticated algorithms combined with expert human analysis, the scanner safeguards your sensitive information, enabling you to concentrate on your core business operations without the persistent anxiety of cyber threats.
Alongside deep web surveillance, Cyber Solutions provides thorough assessments that identify irregularities and possible weaknesses in real-time. This ongoing observation guarantees that suspicious activities are recognized and handled before they develop into serious threats. Organizations employing these tools together with network oversight have reported significant enhancements in their security posture. For instance, companies that adopted such oversight have been able to detect and respond to data breaches before they escalate, thereby minimizing potential damage. The proactive nature of concealed web oversight, combined with robust network alerts and customized access controls, is vital in today’s environment, where cybercriminals are becoming more sophisticated and relentless.
Specialists in cybersecurity stress the importance of monitoring as a crucial element of a strong security strategy. They observe that being aware of compromised credentials and sensitive information on the concealed web enables organizations to take immediate actions, such as changing passwords and strengthening security protocols, ultimately decreasing the risk of data breaches and financial losses.
In light of recent developments, including the rise in cyberattacks, the need for effective cybersecurity solutions cannot be overstated. Google’s decision to phase out its service due to user feedback about its limitations underscores the need for tools that provide comprehensive protection. Cyber Solutions' deep web scanner, along with our 24/7 network monitoring services that include tailored restrictions, act as a vital line of defense, ensuring organizations remain vigilant and prepared against the ever-present risks lurking in the shadows of the internet.
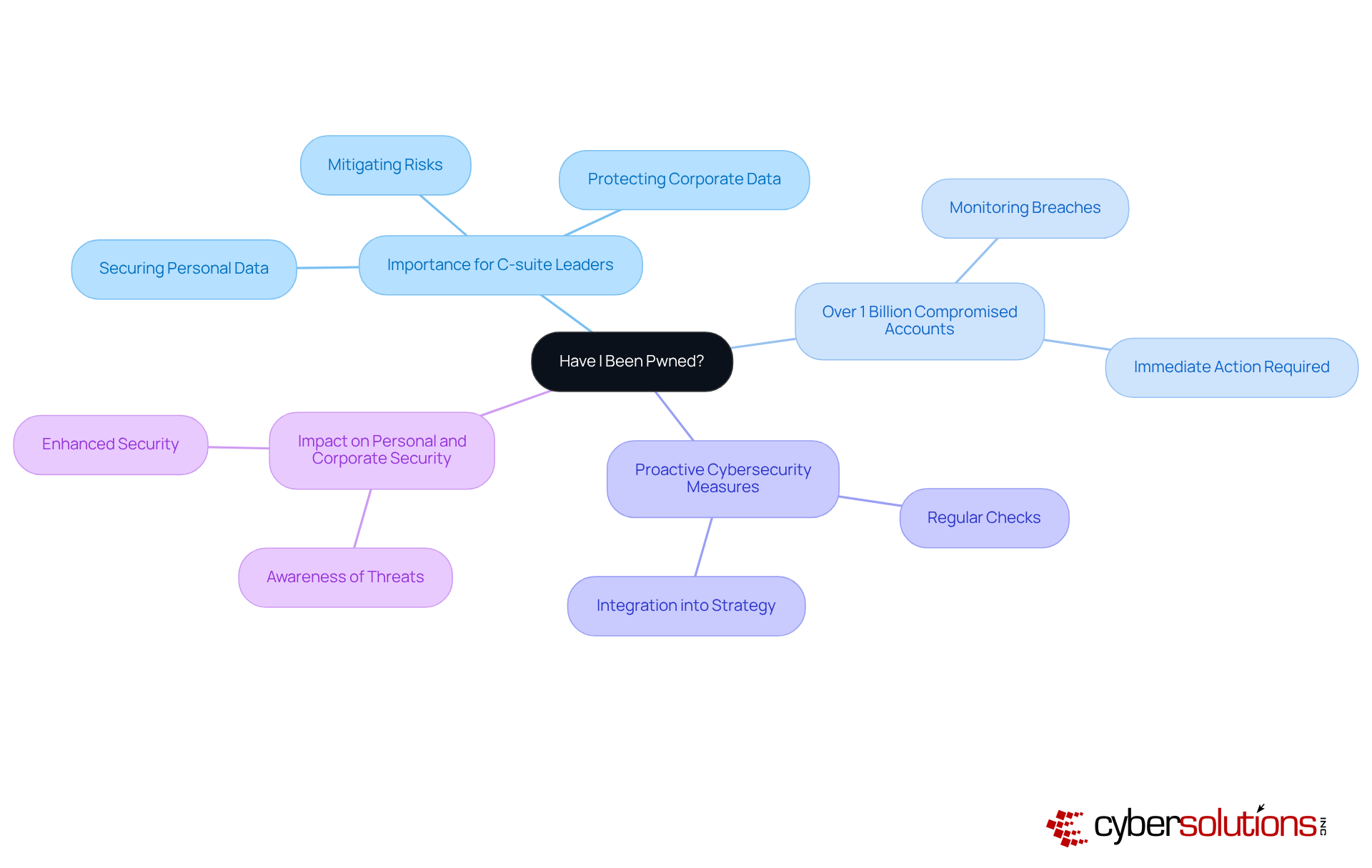
In today’s digital landscape, cybersecurity is not just a necessity; it’s a critical imperative for individuals that empowers users to respond in security breaches. By simply entering an email address, users can swiftly determine whether their information has been exposed, allowing them to take immediate action to protect their accounts.
This tool is particularly vital for organizations, who face the daunting task of maintaining security in an increasingly hostile environment. With its user-friendly interface, 'Have I Been Pwned?' stands out as a crucial resource for executives aiming to mitigate risks associated with data breaches. Cybersecurity experts stress the importance of proactive monitoring; regular checks can significantly lower the chances of falling victim to identity theft.
Consider the impact: individuals who have effectively utilized 'Have I Been Pwned?' have not only enhanced their personal security but also fortified their organizations against potential breaches. This showcases the tool's efficacy in protecting sensitive details and underscores the necessity of integrating such resources into a comprehensive cybersecurity strategy. Are you ready to take the necessary steps to safeguard your information?
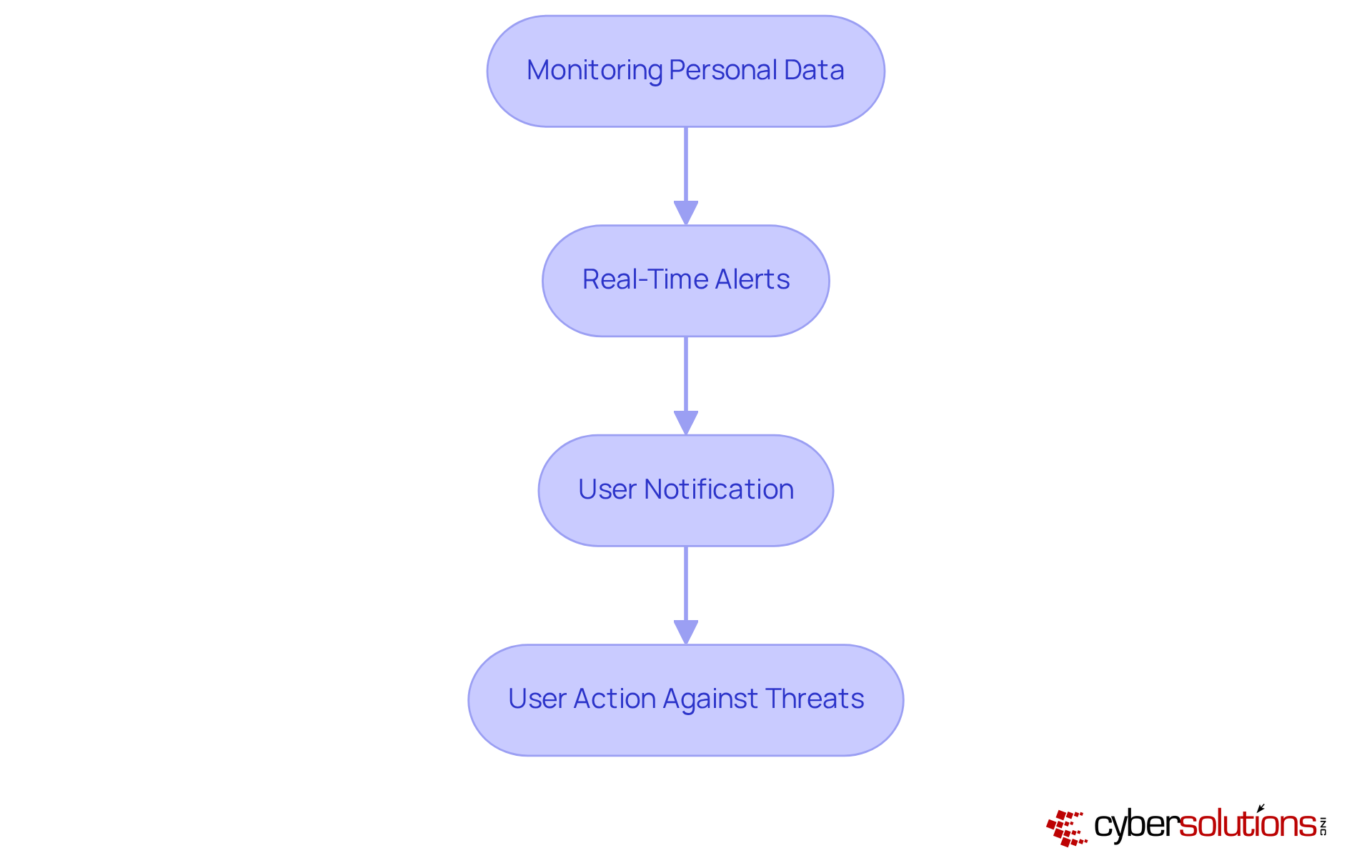
In today's digital landscape, the importance of cybersecurity cannot be overstated, especially for executives. Aura's scanner provides essential oversight of personal information, notifying users when sensitive details appear on the dark web. This capability is vital for protecting personal data from cybercriminals, who increasingly target high-profile individuals.
With advanced features and comprehensive monitoring, Aura empowers users to act swiftly against potential threats. This proactive approach underscores the critical role of cybersecurity in safeguarding identities. As the exposure of personal data continues to escalate, leaders must recognize that their identities are prime targets for cyberattacks.
Incorporating tools like Aura not only enhances personal security but also fortifies the overall security posture of organizations by utilizing dark web intelligence. By prioritizing cybersecurity measures, executives can protect themselves and their companies from the devastating impacts of data breaches.
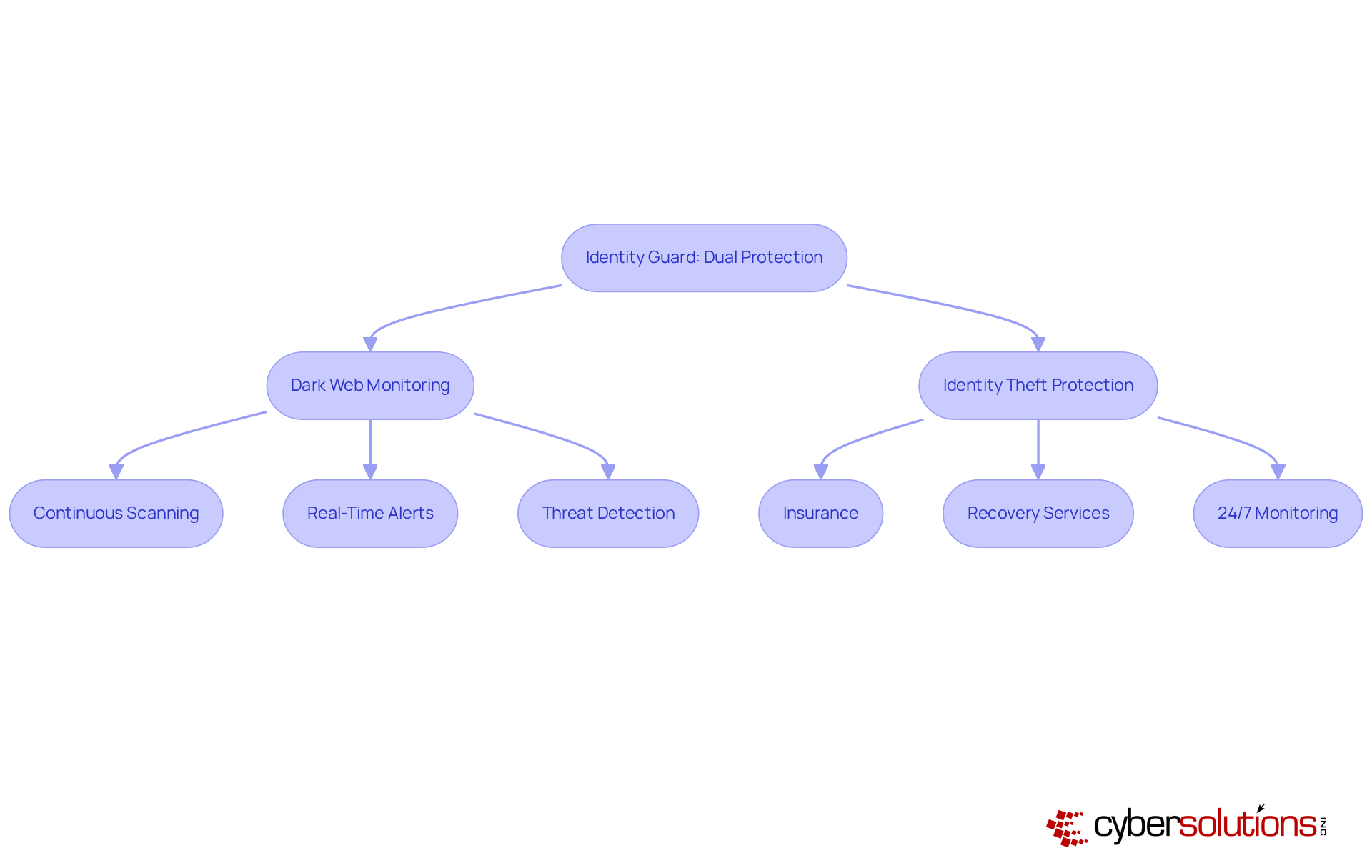
In today's digital landscape, the importance of cybersecurity cannot be overstated, especially for healthcare organizations. Identity Guard stands out with its robust dual protection strategy, merging deep web surveillance with dark web monitoring. This service uses advanced algorithms to continuously scan for compromised personal information, delivering real-time alerts to users. Not only does it monitor potential threats, but it also provides identity theft protection and recovery services, ensuring users are informed and shielded from financial repercussions.
For C-suite leaders, this comprehensive security approach is essential for safeguarding both personal and corporate information. As identity theft and data breaches rise, organizations must prioritize proactive measures to mitigate risks associated with identity fraud and information breaches. Cyber Solutions enhances this protective framework with a layered approach that includes threat detection, incident response, and user training, further bolstering security configurations and promoting staff cyber hygiene.
Their monitoring system is crucial, as it detects and halts suspicious activities before they escalate into serious threats, effectively safeguarding against ransomware and phishing attacks. This thorough strategy is vital, particularly as cyber threats are exacerbated by AI, extensive information exposure, and inconsistent protection standards. By adopting these measures, healthcare organizations can not only protect their assets but also foster trust and confidence among their stakeholders.
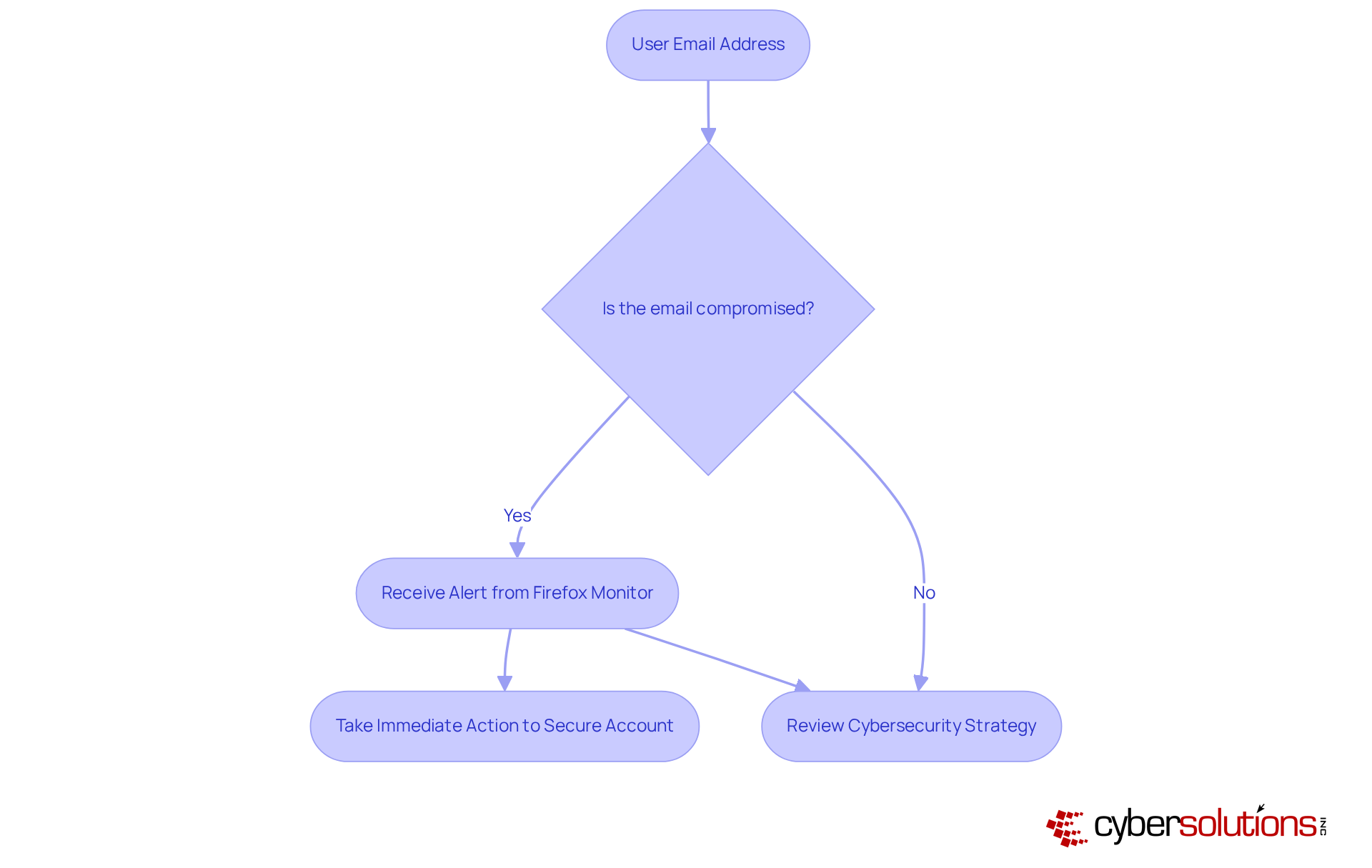
In today's digital landscape, cybersecurity is not just a technical concern; it's a critical priority for leaders, especially in healthcare. Firefox Monitor is a tool that alerts users if their email addresses have been compromised in recognized data breaches. By providing timely notifications, it empowers leaders to take immediate action to secure their accounts.
This tool is particularly vital for executives who frequently engage with web applications, as they face unique challenges in safeguarding their data from potential threats. With the increasing frequency of cyberattacks, how can leaders ensure their organizations remain secure? Firefox Monitor provides a proactive solution, allowing leaders to stay informed and act swiftly in the face of evolving risks.
By integrating such tools into their cybersecurity strategies, organizations can not only enhance their defenses but also uphold the integrity of their organizations. In a world where every click can lead to a security breach, taking advantage of resources like Firefox Monitor is not just advisable - it's imperative.
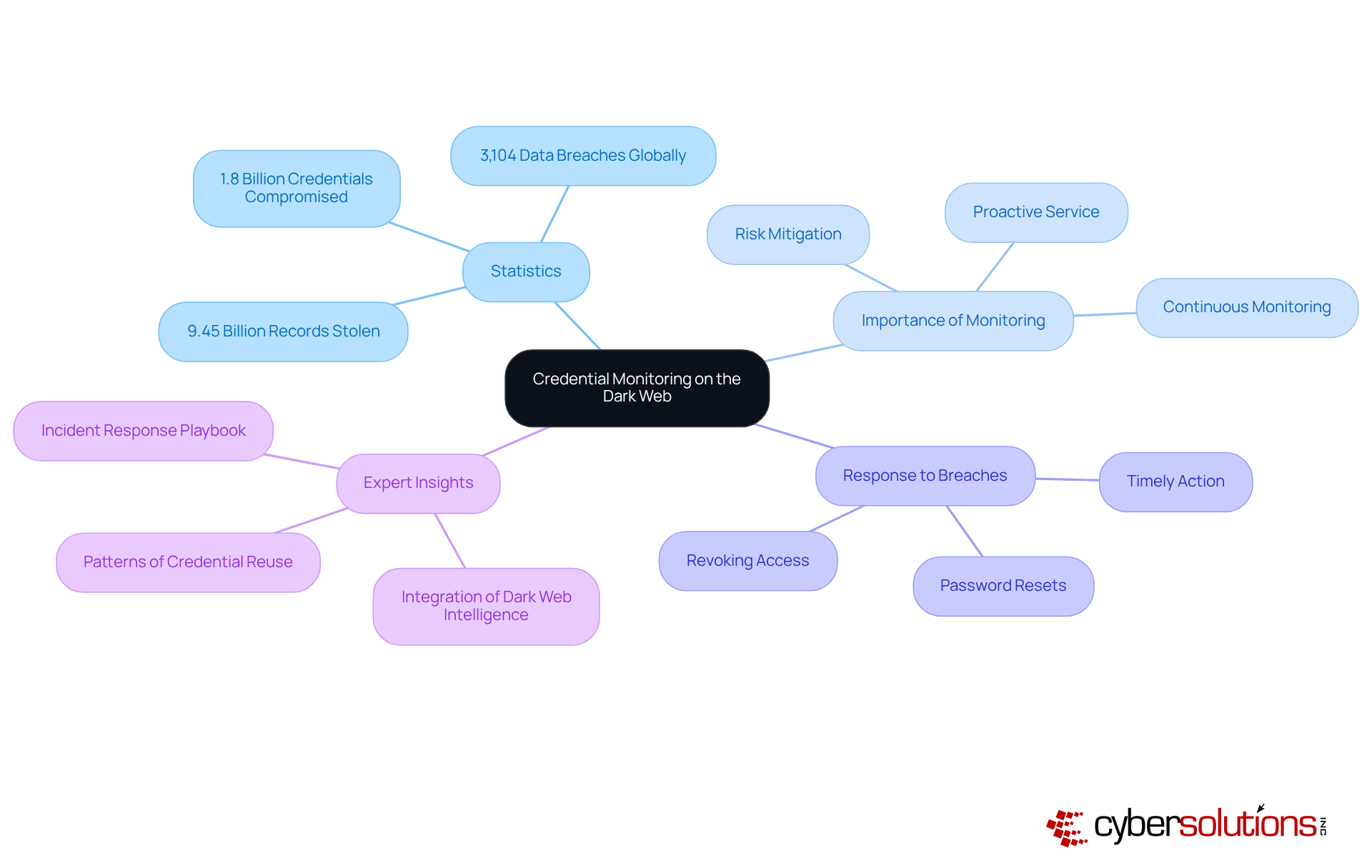
In today's digital landscape, the urgency of cybersecurity cannot be overstated. With over 1.8 billion data breaches in just the first half of 2025, organizations face a relentless tide of threats that demand immediate attention. Dehashed specializes in using advanced algorithms to track credentials, alerting users when their personal information, including email addresses and passwords, surfaces in security breaches. This proactive service is essential for organizations managing sensitive data, enabling them to swiftly mitigate risks and protect their assets.
For C-suite leaders, understanding the pervasive threats posed by cybercriminals is crucial for ensuring organizational security and compliance. Cyber Solutions emphasizes the importance of real-time monitoring and alerts to identify anomalies and potential vulnerabilities. This vigilance allows organizations to take prompt action against threats such as ransomware and phishing attacks. Experts stress that immediate action is vital; organizations must act immediately to revoke access and enforce password resets to minimize potential damage. Alarmingly, 50% of organizations take three days or longer to revoke access after employee departures, highlighting the critical need for timely responses.
As Ariel Parnes, COO of Mitiga, aptly states, "Companies must incorporate insights gained from dark web monitoring into their internal oversight." Tailored access controls and the adaptability of Cyber Solutions' services are indispensable for addressing evolving threats. As the landscape of cyber threats continues to shift, integrating deep web monitoring into cybersecurity strategies is no longer optional; it is essential for protecting valuable corporate information. Organizations must prioritize these measures to ensure their defenses are robust and responsive.
In today's digital landscape, cybersecurity is not just an option; it's a necessity. MyPwd emerges as a powerful tool, equipped with features that utilize artificial intelligence to monitor the deep and concealed web for any leaked passwords tied to user accounts. This proactive strategy ensures organizations receive timely alerts when breaches are detected, allowing for swift action to mitigate potential risks.
For C-suite leaders, employing a password manager like MyPwd, which features dark web scanning, is essential for security and maintaining a strong defense. Organizations that have adopted MyPwd report enhanced security practices, underscoring the tool's effectiveness in navigating the ever-evolving landscape of cyber threats; after all, a single compromised password can expose significant vulnerabilities.
By integrating advanced tools such as MyPwd, executives can fortify their organizations against potential attacks, ensuring resilience in the face of growing threats. The stakes are high, and the time to act is now.
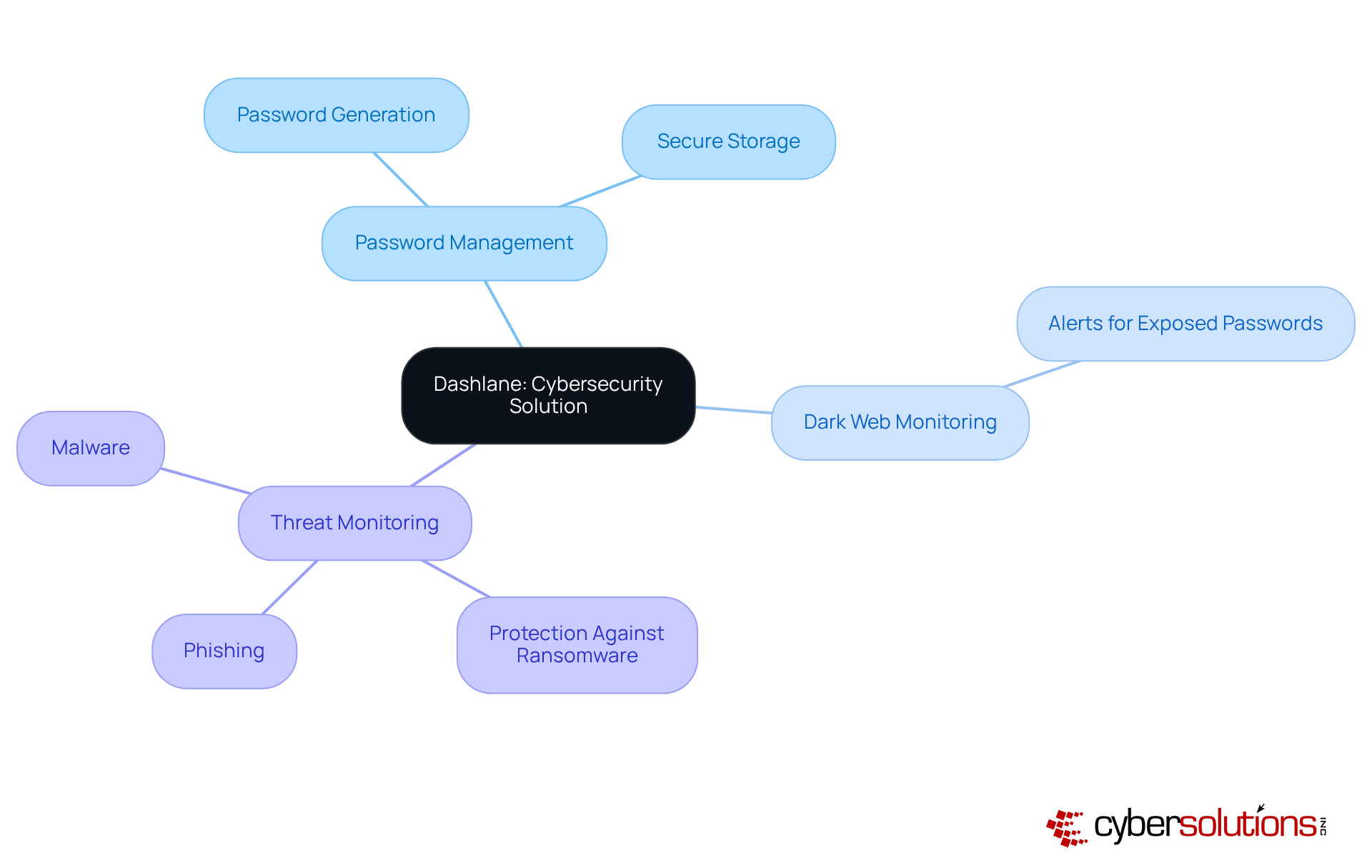
In today's digital landscape, the importance of robust cybersecurity cannot be overstated, especially for organizations handling sensitive information. Dashlane seamlessly integrates with existing systems, offering a powerful solution that alerts users when their passwords appear on the deep web. This proactive strategy not only fortifies security through features like password generation and secure storage but also keeps users informed of potential threats.
Organizations can significantly enhance their cybersecurity posture by leveraging Cyber Solutions' expertise. This comprehensive approach ensures that data is protected from unauthorized access. For C-suite leaders, Dashlane emerges as an indispensable tool in navigating the complexities of cybersecurity, empowering them to safeguard their organizations against evolving digital threats while maintaining compliance.
As the landscape of integrated solutions evolves, Dashlane stands out for its ability to tackle the pressing challenges executives face in protecting their organizations' critical information. Are you ready to take the necessary steps to secure your organization? With Dashlane, you can confidently manage your passwords, ensuring that your sensitive data remains protected.
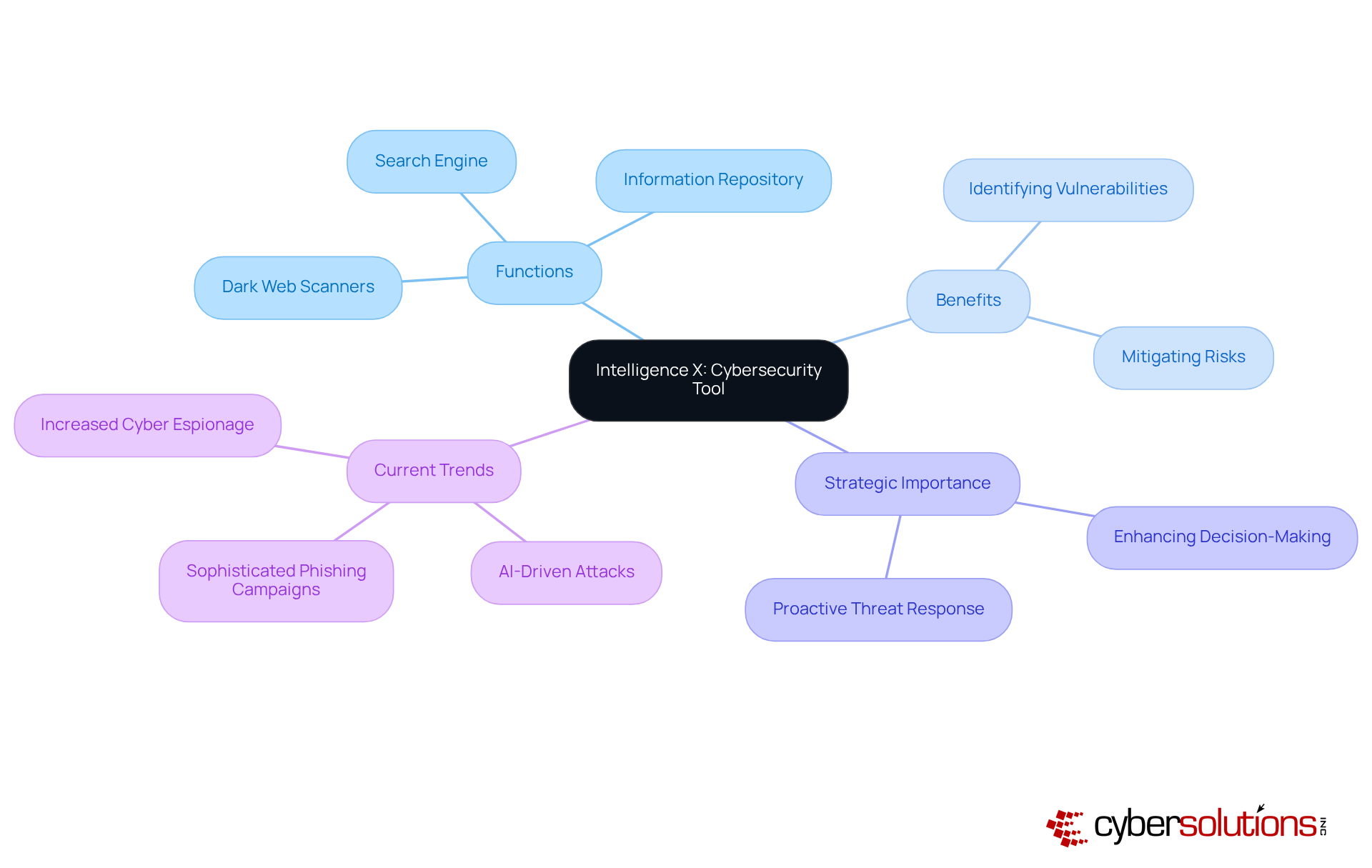
In today's digital landscape, the importance of cybersecurity cannot be overstated. Intelligence X serves as a powerful search engine and information repository, enabling organizations to scrutinize compromised information from diverse sources, including the dark web. By delivering comprehensive insights into leaks and breaches, it empowers organizations to grasp the extent of their exposure and make informed decisions. This tool not only deepens the analysis of threats but also plays a pivotal role in enhancing security measures.
Organizations leveraging Intelligence X have successfully pinpointed vulnerabilities associated with breaches, demonstrating its effectiveness in real-world applications. Cybersecurity specialists emphasize that proactive monitoring is vital for organizations aiming to bolster their defenses and respond proactively to emerging threats. Current trends reveal an increasing dependence on advanced scanning tools, which are essential for navigating the complexities of cybersecurity today.
By utilizing Intelligence X, leaders can stay ahead of potential threats, ensuring their organizations are well-prepared to confront the evolving challenges in cybersecurity. Are you ready to take the necessary steps to protect your organization?
In today’s digital landscape, the threat of information leaks is more pressing than ever. Hashcast stands out by focusing on the critical issue of data leaks as identified by cybersecurity professionals. This targeted approach allows organizations to quickly identify and mitigate potential threats, effectively protecting sensitive data. For C-suite leaders, leveraging Hashcast isn’t just a precaution; it’s a vital strategy for safeguarding information and ensuring compliance.
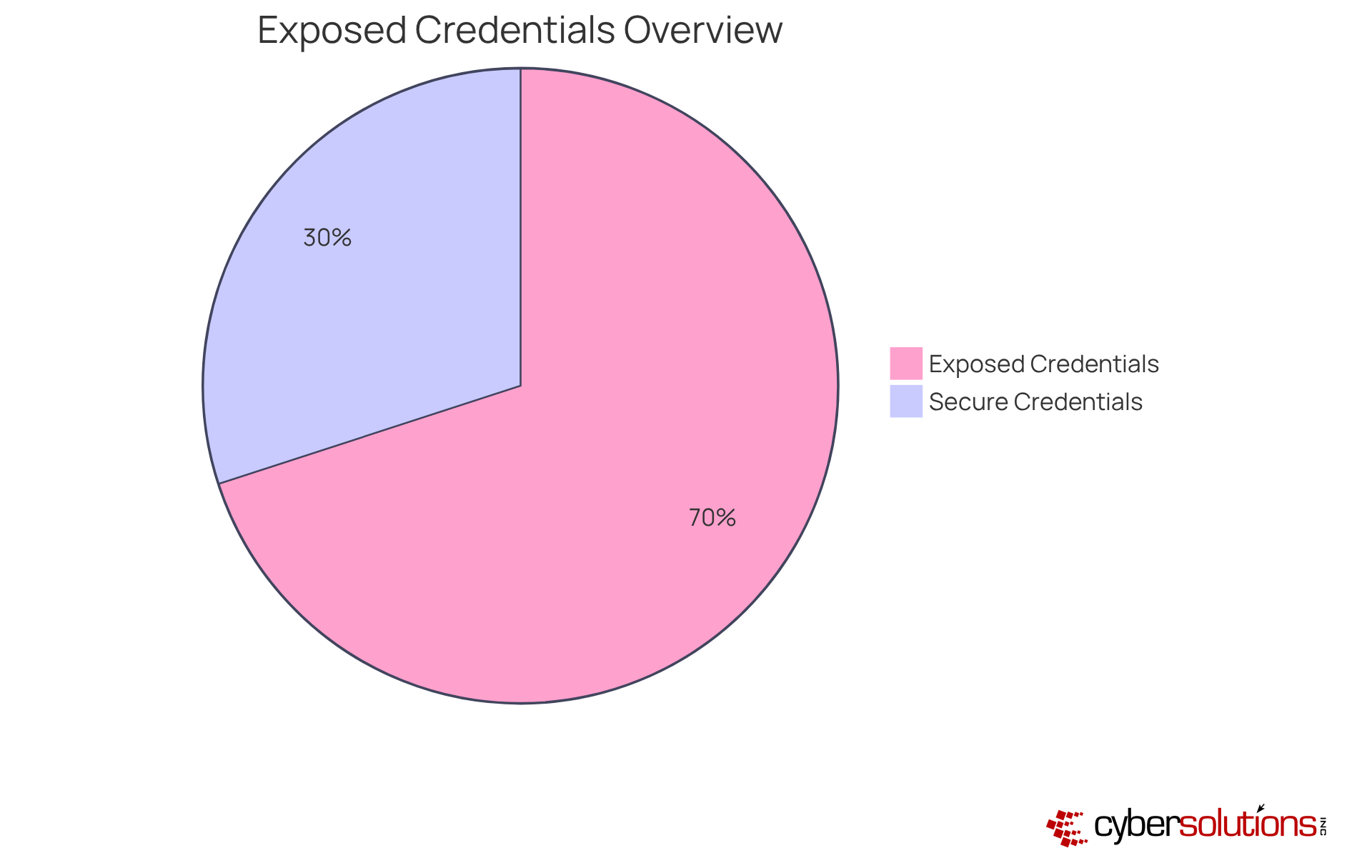
Cybersecurity experts stress the importance of investing in dark web monitoring, especially considering that over 70% of firms have executive credentials exposed to cybercriminals. This alarming statistic underscores the urgency for organizations to enhance their security measures. By adopting solutions like Hashcast, businesses can not only fortify their security posture but also stay ahead of emerging threats.
Ultimately, the question remains: can your organization afford to overlook such a critical aspect of cybersecurity? With Hashcast, you can take decisive action to protect your assets and maintain a robust security framework.
The importance of dark web scanners in protecting sensitive information is paramount for C-suite leaders today, especially as cyber threats grow more sophisticated. These tools are not just optional; they are essential components of a robust cybersecurity strategy, proactively identifying vulnerabilities and equipping organizations with the insights necessary to safeguard their assets effectively.
As we delve into ten essential dark web scanners, several key insights emerge. From Cyber Solutions' comprehensive protection and real-time alerts to the intuitive interface of 'Have I Been Pwned?', each tool presents unique features designed to enhance security. Moreover, the integration of password management solutions like MyPwd and Dashlane underscores the necessity of a multi-faceted approach in the fight against cyber threats. These resources empower executives to act swiftly against potential breaches, ensuring that both personal and corporate data remain secure.
In a landscape where cybercriminals are increasingly adept, the message is clear: organizations must prioritize the adoption of advanced monitoring tools and proactive cybersecurity measures. By leveraging these dark web scanners, leaders can not only strengthen their defenses but also foster a culture of vigilance within their organizations. The time to act is now-protecting sensitive information is not merely a necessity; it is imperative for maintaining trust and integrity in our interconnected world.
What is the purpose of Cyber Solutions' dark web scanner?
Cyber Solutions' dark web scanner monitors the concealed corners of the internet for compromised data associated with organizations, alerting them to potential breaches and providing actionable insights to mitigate risks.
How does the dark web scanner enhance cybersecurity for organizations?
The scanner employs sophisticated algorithms and expert human analysis to safeguard sensitive information, allowing organizations to focus on their core operations without the anxiety of cyber threats.
What additional services does Cyber Solutions offer alongside the dark web scanner?
Cyber Solutions provides 24/7 network oversight services that identify irregularities and weaknesses in real-time, ensuring that suspicious activities are recognized and addressed before they escalate into serious threats.
Why is deep web monitoring considered important by cybersecurity specialists?
Deep web monitoring helps organizations become aware of compromised credentials and sensitive information, enabling them to take proactive measures like changing passwords and strengthening security protocols, thus reducing the risk of data breaches.
What recent development has highlighted the need for reliable dark web scanners?
The discontinuation of Google's hidden web report tool has underscored the importance of dark web scanners that provide clear, actionable steps for organizations to remain vigilant against cyber threats.
What is 'Have I Been Pwned?' and how does it function?
'Have I Been Pwned?' is a complimentary service that allows users to check if their email addresses or passwords have been compromised in security breaches by simply entering their email address.
Who can benefit from using 'Have I Been Pwned?'?
C-suite leaders can particularly benefit from this tool as it helps secure both personal and corporate data against potential breaches.
How does using 'Have I Been Pwned?' enhance security for executives?
Regular checks with 'Have I Been Pwned?' can significantly lower the chances of falling victim to cyber threats, thereby enhancing personal security and fortifying organizations against breaches.
What is the role of Aura's dark web scanner?
Aura's dark web scanner provides oversight of personal information, notifying users when sensitive details appear on the dark web, which is crucial for safeguarding identities from cybercriminals.
Why is personal cybersecurity important for C-suite executives?
Personal cybersecurity is critical for C-suite executives as their identities are prime targets for cyberattacks, and protecting personal data also fortifies the overall cybersecurity posture of their organizations.