
In today's world, where cyber threats are more pervasive than ever, understanding threat intelligence in cybersecurity is essential for organizations, especially in sensitive sectors like healthcare. The stakes are high; a single breach can compromise patient data and undermine trust. This article explores the essence of threat intelligence, illustrating how it transforms raw data into actionable insights that can strengthen defenses against the relentless wave of cyber assaults.
As cybercriminals continuously evolve their tactics, healthcare organizations face unique challenges. How can they effectively harness threat intelligence not only to anticipate attacks but also to bolster their overall cybersecurity posture? By leveraging advanced threat intelligence solutions, organizations can stay one step ahead, ensuring that they are prepared to combat the ever-changing landscape of cyber threats.
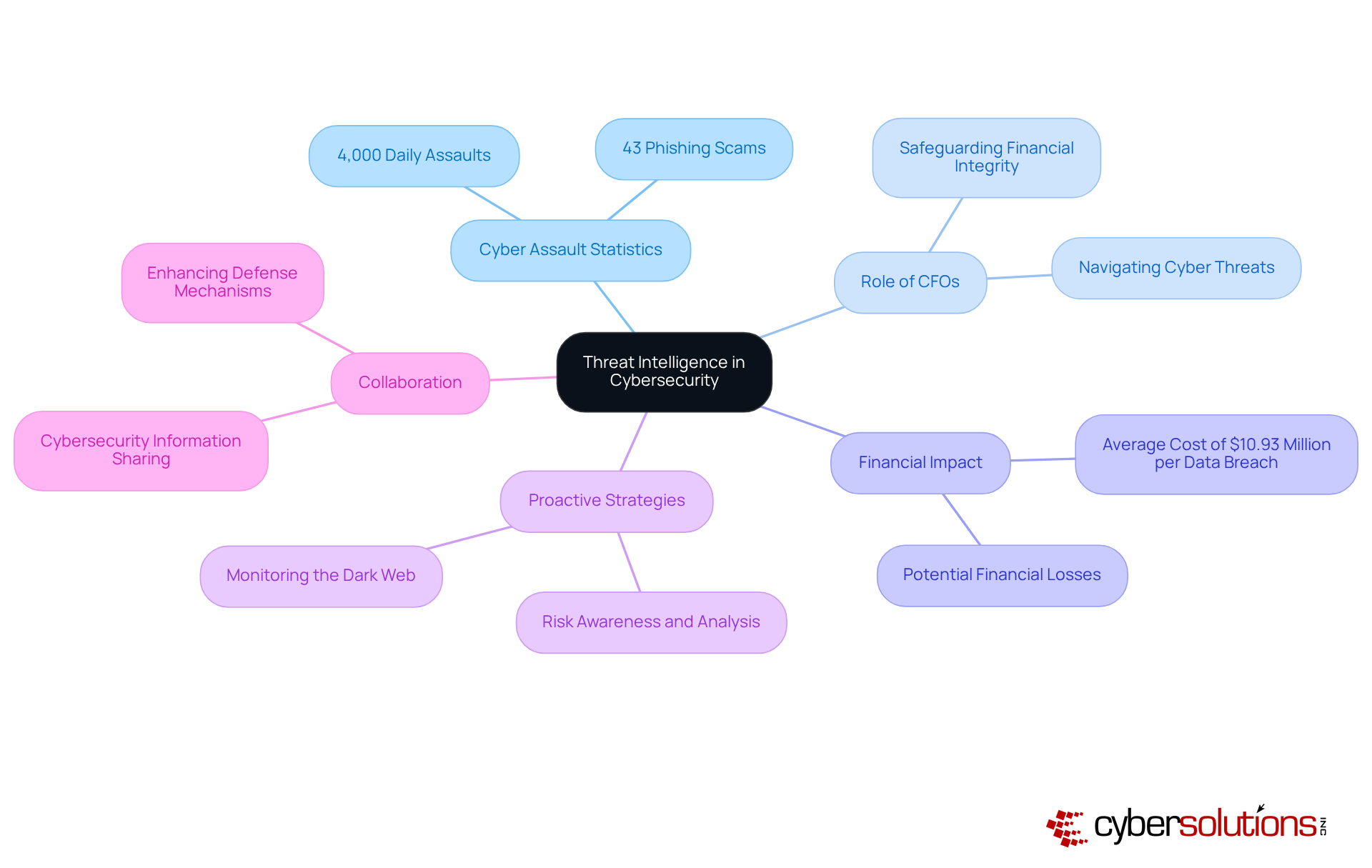
In today's digital landscape, the importance of threat intelligence in healthcare cannot be overstated. With approximately 4,000 cyberattacks occurring daily and phishing scams accounting for 43% of all attacks in 2023, healthcare organizations face unique challenges that demand immediate attention. CFOs, in particular, must navigate these threats while safeguarding their institutions' financial and operational integrity.
In this endeavor, organizations can better understand and transform raw data into actionable insights. This process not only enhances readiness and response strategies but also strengthens overall resilience against cyber risks. For instance, the healthcare sector, which faced an astonishing number of cyber incidents, stands to benefit significantly from threat intelligence. Understanding the tactics of advanced adversaries allows entities to establish robust protections and plans, ultimately minimizing the risk of operational disruptions and financial losses.
Real-world examples underscore the effectiveness of risk awareness in bolstering security measures. Organizations that actively seek to understand threat landscapes can identify potential vulnerabilities before they are exploited. Furthermore, the anticipated revival of information-sharing legislation is expected to enhance collaboration among healthcare entities, further fortifying their defenses against cyber threats. As the landscape of cyber risks evolves, the role of threat intelligence will be vital in helping organizations navigate these challenges effectively.
In conclusion, the integration of risk awareness into cybersecurity strategies is essential for healthcare organizations. By leveraging insights and fostering collaboration, CFOs can not only protect their institutions but also ensure a more secure future in an increasingly perilous digital environment.
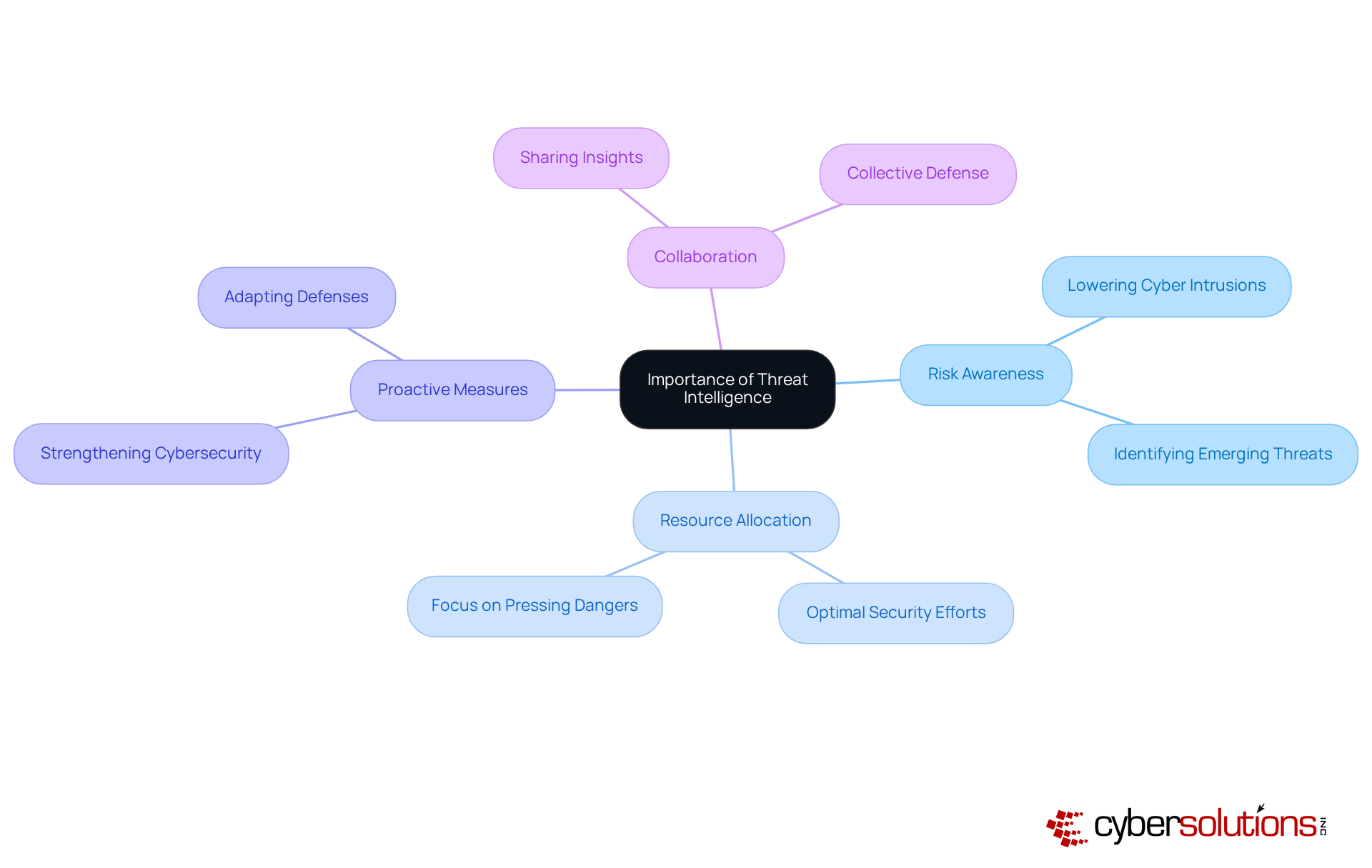
In the current cybersecurity landscape, threat intelligence is not just important; it’s essential. Organizations must anticipate and respond to threats before they escalate, significantly lowering the chances of successful cyber intrusions. By leveraging risk information, companies can focus their efforts on the most pressing dangers, ensuring optimal resource allocation and fortifying their defenses.
Consider this: organizations that harness risk insights can swiftly identify and adapt their defenses accordingly. This not only strengthens individual security measures but also fosters collaboration among organizations, enhancing the collective response and strategies to tackle common threats effectively.
Ultimately, threat intelligence cultivates a robust security posture. Are you ready to elevate your organization’s defenses?
Cybersecurity is not just a technical issue; it’s a critical component of organizational integrity, especially in healthcare. With approximately 4,000 cyber assaults occurring each day, the urgency for threat intelligence has never been clearer. Organizations must adopt a proactive approach to risk awareness, which encompasses:
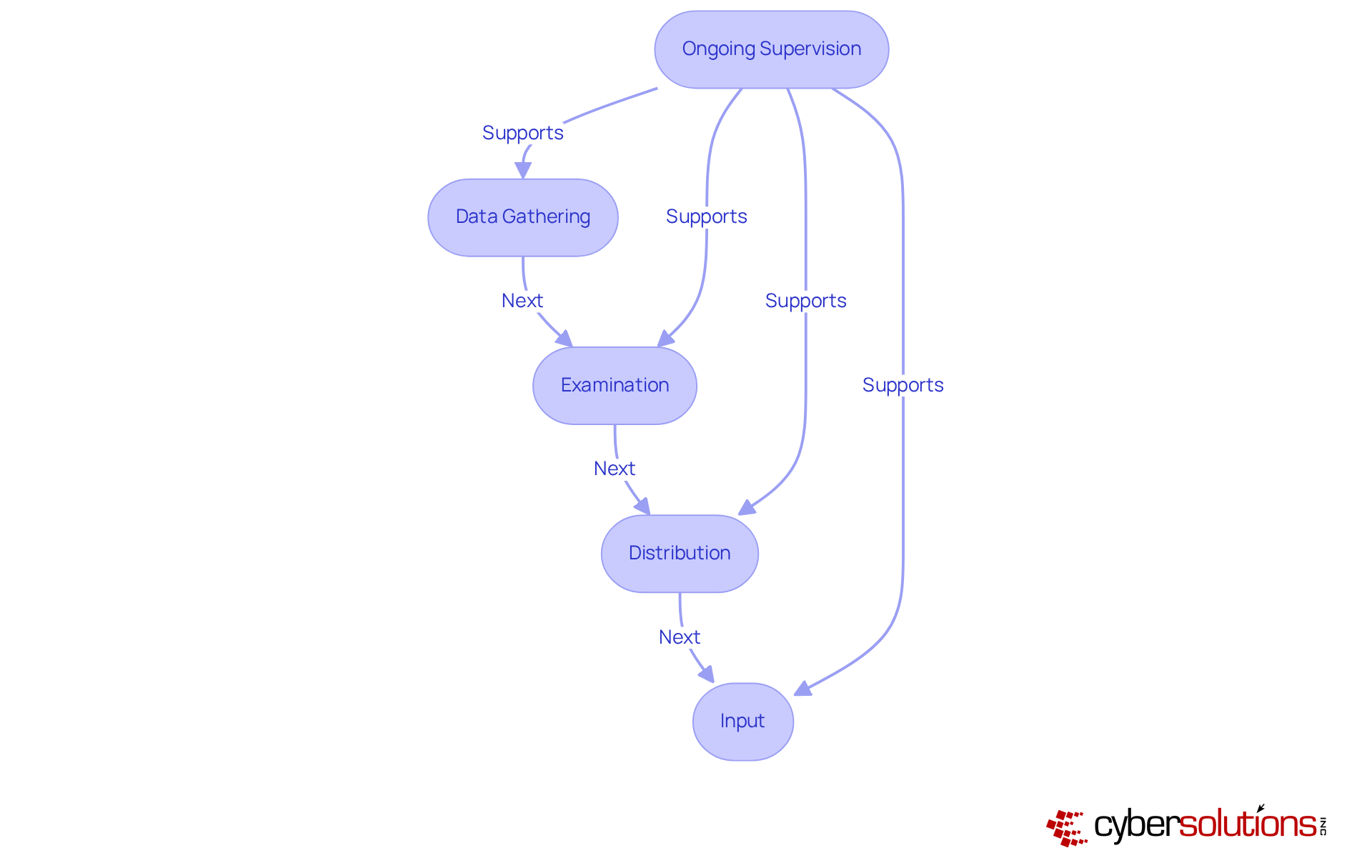
This cyclical process significantly enhances an organization’s security posture, ensuring that questionable actions are identified and halted before they escalate into serious threats.
Ongoing supervision is essential. It guarantees that potential risks, such as data breaches, are addressed swiftly. In 2025, organizations are increasingly leveraging intelligence from diverse sources, including:
For instance, intelligence platforms utilize machine learning to sift through vast amounts of data, enabling quicker identification of emerging threats.
Once data is collected, it undergoes rigorous analysis to uncover patterns and trends that may indicate vulnerabilities. This analytical phase is crucial; it transforms raw data into actionable insights. Effective analysis can reveal exploitable weaknesses, as evidenced by past incidents. Continuous monitoring and assessment are vital, and solutions like Cyber Solutions’ tools and advanced risk detection capabilities, including enterprise-grade firewalls and intrusion detection systems, empower organizations to stay ahead of these vulnerabilities.
The dissemination of pertinent information to stakeholders is equally important. Organizations should establish organized communication pathways to ensure that all relevant parties are informed of potential dangers and can respond appropriately. Threat intelligence platforms play a key role in monitoring evolving criminal tactics, helping entities stay ahead of developing threats.
Finally, feedback systems are essential for refining information processes based on the effectiveness of responses to threats. This iterative approach not only improves future risk assessments but also fortifies overall security strategies. By consistently evaluating the impact of their information initiatives, organizations can adapt to the ever-changing risk landscape, ensuring resilience against cyberattacks. Together, these components create a robust framework that exemplifies threat intelligence, empowering entities to proactively defend against cyber threats.
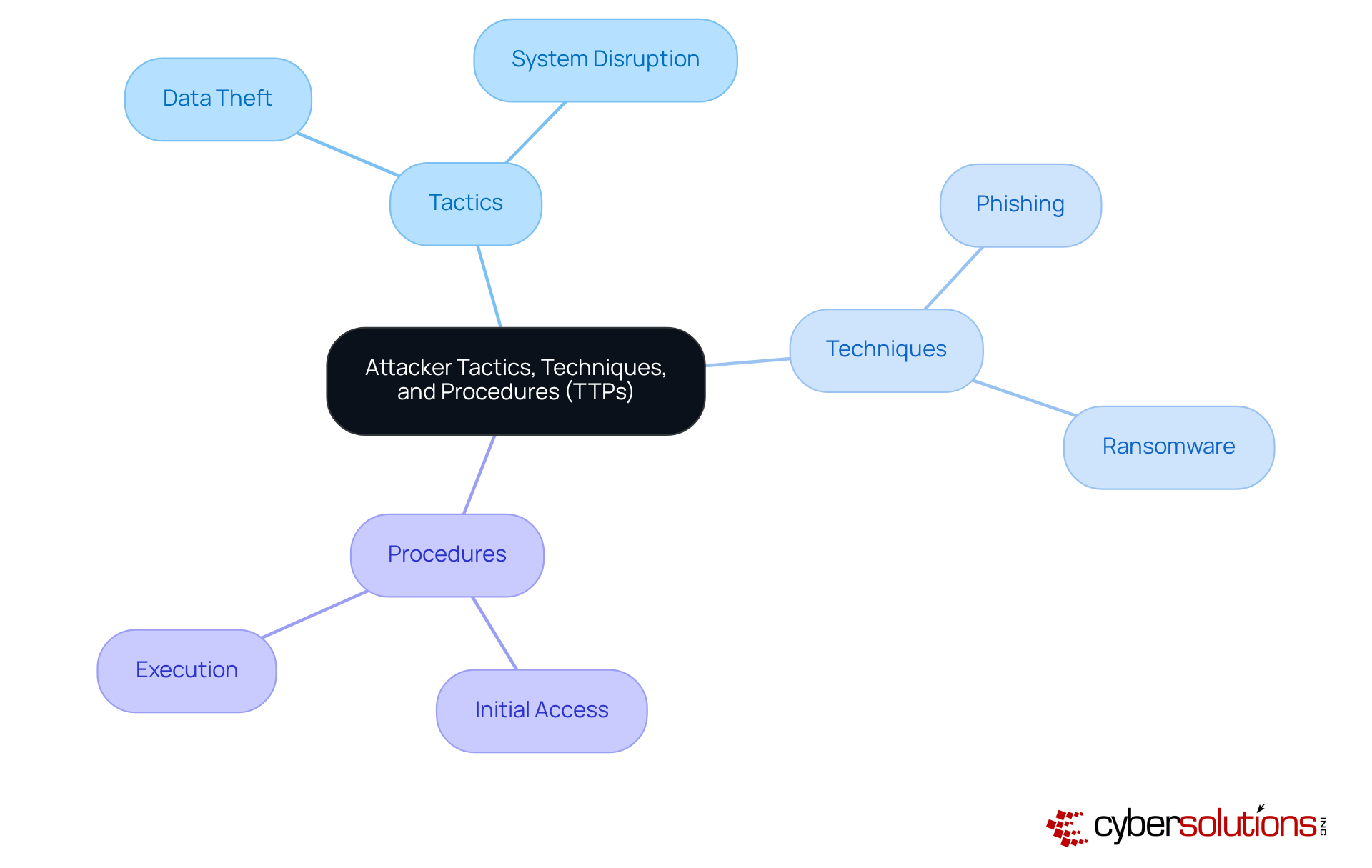
Analyze Attacker Tactics, Techniques, and Procedures (TTPs) is essential in the fight against cyber threats, especially in the healthcare sector. Cybercriminals are constantly evolving, and their methods can have devastating effects on organizations. Tactics encompass the overarching goals of an attack, such as data theft. Techniques detail the specific methods employed to achieve these goals, while procedures outline the exact steps taken during an attack. By analyzing these TTPs, healthcare entities can pinpoint vulnerabilities in their defenses and implement effective security measures.
For instance, if a particular technique is frequently used in ransomware attacks, organizations can prioritize their defenses against that method. This proactive approach minimizes risk exposure and enhances overall security posture. Understanding TTPs not only aids in threat detection but also significantly boosts incident response capabilities. Organizations can react swiftly and effectively to cyber incidents, ensuring that they are prepared for any eventuality.
In a landscape where cyber threats are increasing, the need for robust security measures cannot be overstated. Organizations can mitigate these threats by investing in technologies that address the unique challenges they face. By doing so, they not only protect sensitive patient data but also maintain trust and credibility in an industry where these factors are paramount.
Integrating threat intelligence into cybersecurity strategies is not just important; it’s essential for organizations, especially in the healthcare sector, where the stakes are incredibly high. With cyber threats evolving rapidly, understanding and implementing risk awareness can turn potential dangers into actionable insights. This proactive approach significantly enhances resilience against cyberattacks, ensuring that organizations are not just reacting but are prepared to defend themselves effectively.
Key components of threat intelligence - data gathering, analysis, dissemination, and feedback mechanisms - work together to form a robust framework. This synergy empowers organizations to defend against vulnerabilities and adapt to the ever-changing landscape of cyber threats. Real-world examples underscore the value of this approach, demonstrating how timely insights can lead to effective incident responses and strengthened defenses.
As cyber threats grow in sophistication and frequency, the necessity for a comprehensive threat intelligence strategy becomes increasingly critical. Organizations must embrace these insights and foster collaboration within the industry to build a collective defense mechanism. By prioritizing threat intelligence, entities can protect sensitive information and ensure operational integrity and trust in an increasingly digital world.
In conclusion, the time to act is now. Organizations that integrate threat intelligence into their cybersecurity strategies will not only safeguard their assets but also position themselves as leaders in the fight against cybercrime. Are you ready to take the next step in fortifying your defenses?
What is threat intelligence in cybersecurity?
Threat intelligence in cybersecurity refers to the systematic gathering and analyzing of information about potential threats, which helps organizations understand and respond to cyber risks effectively.
Why is cybersecurity important in healthcare?
Cybersecurity is crucial in healthcare due to the high volume of cyber assaults, with approximately 4,000 occurring daily, and the significant financial impact of data breaches, averaging $10.93 million per incident in 2023.
What challenges do CFOs in healthcare face regarding cybersecurity?
CFOs must navigate the complexities of cyber threats while safeguarding their institutions' financial and operational integrity, which requires proactive risk awareness and effective response strategies.
How does risk awareness enhance cybersecurity?
Risk awareness enhances cybersecurity by transforming raw data into actionable insights, improving readiness and response strategies, and strengthening overall resilience against cyber risks.
What role does monitoring the dark web play in threat intelligence?
Monitoring the dark web allows organizations to identify potential vulnerabilities before they can be exploited, thereby enhancing their security measures.
How is collaboration expected to improve cybersecurity in healthcare?
The anticipated revival of cybersecurity information-sharing legislation is expected to enhance collaboration among entities, fortifying their defenses against cyber threats.
What is the significance of risk analysis in cybersecurity?
Risk analysis is vital for helping organizations navigate evolving cyber risks and develop effective strategies to mitigate potential threats.
What can healthcare organizations do to protect themselves from cyber threats?
Healthcare organizations can protect themselves by integrating risk awareness into their cybersecurity strategies, leveraging insights, and fostering collaboration among stakeholders.