
In a time when cyber threats are more prevalent than ever, organizations face the daunting task of navigating the intricate world of IT service providers to protect their operations. Understanding the critical differences between Managed Service Providers (MSPs) and Managed Security Service Providers (MSSPs) is essential for leaders looking to strengthen their cybersecurity strategies. By grasping these distinctions, decision-makers can access tailored solutions that not only safeguard sensitive data but also improve operational efficiency. With the stakes so high, how can organizations identify which provider best meets their unique needs and regulatory requirements?
In today's digital landscape, the importance of cybersecurity in healthcare cannot be overstated. There is a significant difference, as both managed service providers (MSPs) and managed security service providers (MSSPs) play pivotal roles in safeguarding sensitive information. The key distinction is that while MSPs focus on network management, data backup, and help desk support to ensure seamless IT operations, MSSPs specialize in cybersecurity, offering critical services like threat detection, incident response, and compliance management. This distinction, or the difference in service models, is vital for leaders, enabling them to choose the right service that aligns with their organizational goals and safety needs.
Consider a healthcare organization facing escalating cyber threats. Such an entity would benefit significantly from the expertise of an MSSP, enhancing its protective measures and ensuring data security. On the other hand, a manufacturing firm might prioritize the operational efficiency that an MSP provides for effective IT infrastructure management. Understanding the differences empowers leaders to make informed decisions about their IT and security strategies.
Cyber Solutions exemplifies the proactive approach necessary in this environment. With advanced tools to detect anomalies and potential vulnerabilities, they provide instant alerts and real-time insights, enabling swift action to prevent downtime or breaches. This is crucial, especially when statistics reveal that 40% of alerts in contemporary settings go unexamined. The significance of timely responses in efficiently handling security alerts cannot be overlooked.
In conclusion, as leaders in the healthcare sector, healthcare organizations must prioritize their cybersecurity strategies. By leveraging the expertise of MSSPs like Cyber Solutions, they can not only protect sensitive data but also ensure compliance with regulatory standards, ultimately fostering trust and safety in their operations.

In today's rapidly evolving digital landscape, the importance of cybersecurity cannot be overstated, especially for organizations in the healthcare sector. As cyber threats become increasingly sophisticated, understanding the difference between MSPs and MSSPs is crucial for safeguarding sensitive information and ensuring data protection.
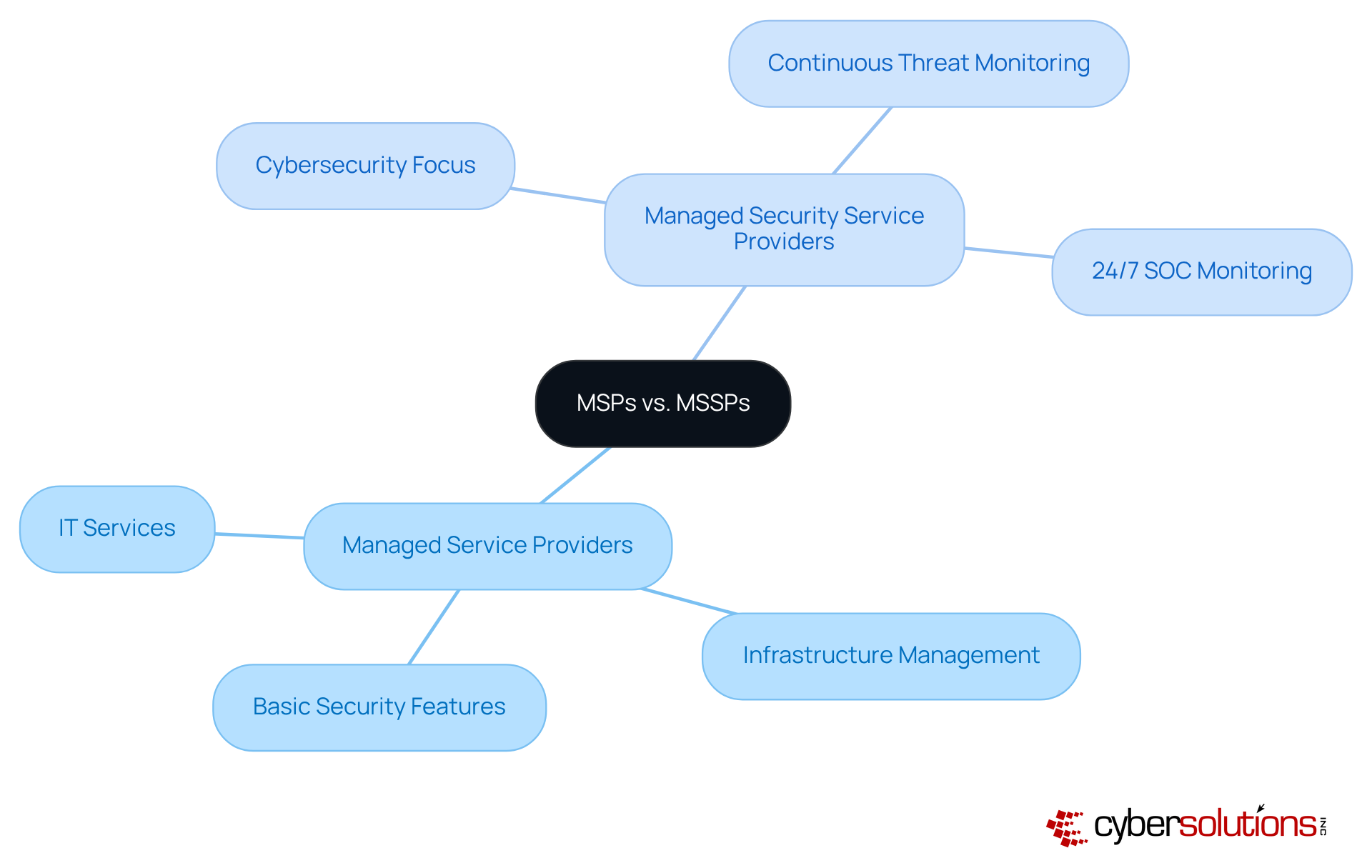
MSPs deliver a broad range of IT services, including infrastructure management, user support, and routine tasks like software updates and network monitoring. However, MSSPs focus specifically on cybersecurity, offering advanced protective measures such as continuous threat monitoring, incident response capabilities, and 24/7 security operations center (SOC) monitoring. The key difference is that while an MSP may provide basic security features, an MSSP delivers comprehensive solutions tailored to address specific vulnerabilities and regulatory compliance needs.
The distinction is particularly significant in today's landscape, where cyber threats are rampant. According to industry insights, 59.7% of organizations identify cybersecurity threats as their top concern, underscoring the necessity for robust security measures. Furthermore, MSSPs operate services that monitor networks around the clock, logging thousands of hours resolving potential cyber incidents - an unparalleled level of service that most conventional MSPs cannot match.
Real-world examples illustrate this distinction effectively. Organizations transitioning from MSP to MSSP models often restructure their services to provide full-scale cybersecurity offerings, ensuring they meet the evolving demands of their clients. For instance, a financial institution that previously relied on an MSP for basic IT support may shift to an MSSP like Cyber Solutions to enhance its security posture, benefiting from tailored solutions and continuous monitoring. This shift not only improves service delivery but also aligns with the growing need for robust cybersecurity measures across various industries, particularly in sectors like finance and healthcare that face stringent regulatory requirements.
Understanding the differences is essential for entities that seek to enhance their cybersecurity strategies. By recognizing the distinct capabilities of MSPs and MSSPs, leaders can make informed decisions that align with their business goals and bolster their overall resilience against cyber threats.
In today's digital landscape, the importance of cybersecurity cannot be overstated, especially for organizations in regulated sectors like healthcare and finance. When deciding the right service model, organizations must evaluate several key factors to ensure they choose the right partner for their unique needs.
By thoroughly assessing these factors, organizations can make informed decisions that align with their operational and safety objectives, ensuring they select the most appropriate provider for their unique needs.

Understanding the difference between MSP and MSSP is crucial for enhancing security and operational efficiency in any organization. In today’s landscape, where cyber threats are prevalent, understanding these options can significantly influence a company's resilience and productivity.
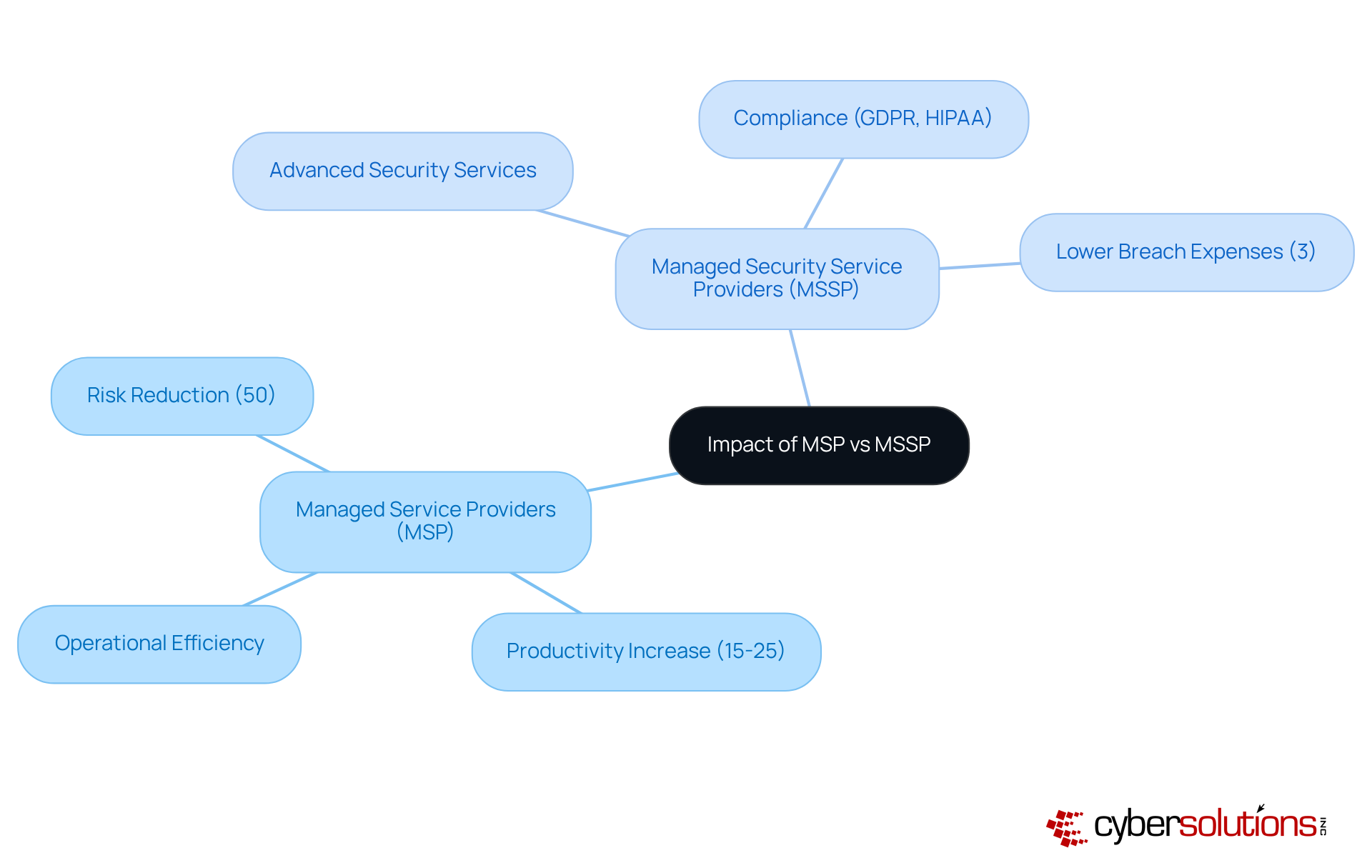
Managed service providers are essential for maintaining IT infrastructure. They maintain IT systems, which minimizes downtime and enhances productivity. Organizations leveraging MSPs can see productivity increases of 15-25% due to improved efficiency and reduced operational disruptions. Moreover, MSPs can cut the risk of cyberattacks by up to 50%, creating a secure and efficient operational environment.
However, if cybersecurity is your top priority, opting for an MSSP may offer greater advantages. These providers specialize in advanced security services that not only prevent breaches but also ensure rapid response. This proactive stance can lead to significant cost savings; entities using MSSPs report 3% lower breach expenses than the global average. Considering that the estimated cost of lost business due to a breach is projected to reach $1.38 million in 2025, the financial implications are substantial.
A key element of effective cybersecurity is the ability to respond swiftly to incidents. Cyber Solutions exemplifies this with its incident response team, crucial for minimizing damage during a security breach. With an expert available within a day, organizations can contain threats more effectively. This layered approach - comprising endpoint isolation, malware removal, and user training - facilitates a faster and more complete recovery, ensuring minimal operational disruption.
Leaders must carefully evaluate how their choice aligns with strategic objectives and the specific risks their organization faces. By understanding the differences between service models, as well as the distinct advantages of MSPs in operational efficiency and MSSPs in security, executives can make informed decisions that bolster both their security posture and overall business performance.
Understanding the distinction between Managed Service Providers (MSPs) and Managed Security Service Providers (MSSPs) is crucial for organizational leaders navigating the complexities of IT management and cybersecurity. In today’s landscape, where cyber threats are increasingly sophisticated, the choice between these two types of providers can significantly impact an organization’s security posture and operational efficiency.
While both MSPs and MSSPs offer valuable services, their core functions differ markedly. MSPs primarily focus on enhancing operational efficiency through comprehensive IT management. In contrast, MSSPs specialize in delivering targeted cybersecurity solutions designed to protect sensitive data and ensure compliance with regulatory standards. This distinction is vital for leaders who must align their provider choice with their specific organizational needs.
Key factors such as business focus, compliance requirements, budget constraints, scalability, and expertise play crucial roles in this decision-making process. For instance, organizations may find that transitioning from an MSP to an MSSP model not only strengthens their cybersecurity defenses but also helps them adapt to evolving threats. Real-world examples illustrate how this shift can lead to improved security outcomes and operational resilience.
Ultimately, the choice between an MSP and an MSSP carries significant implications for both security and operational efficiency. Leaders must carefully assess their unique requirements and the potential risks they face. By making informed decisions, organizations can bolster their defenses against cyber threats while enhancing overall productivity. Prioritizing the right service provider is not just a strategic move; it is a vital step toward fostering a secure and resilient operational environment in an increasingly digital world.
What is the difference between MSP and MSSP?
The difference between MSP (Managed Service Providers) and MSSP (Managed Security Service Providers) lies in their focus areas. MSPs concentrate on network management, data backup, and help desk support, ensuring seamless IT operations, while MSSPs specialize in cybersecurity, offering services like threat detection, incident response, and compliance management.
Why is understanding the difference between MSP and MSSP important for organizations?
Understanding the difference is vital for organizational leaders as it enables them to choose the right service that aligns with their specific goals and safety needs, particularly in the context of cybersecurity threats.
How can healthcare organizations benefit from MSSPs?
Healthcare organizations can significantly benefit from MSSPs by enhancing their protective measures against escalating cyber threats and ensuring compliance with regulations such as HIPAA.
What services do MSSPs provide?
MSSPs provide critical cybersecurity services including threat detection, incident response, compliance management, and 24/7 network monitoring to detect anomalies and potential vulnerabilities.
Why is 24/7 network monitoring important?
24/7 network monitoring is important because it allows for the detection of anomalies and potential vulnerabilities in real-time, enabling swift action to prevent downtime or breaches, especially as many alerts go unexamined in contemporary settings.
How does Cyber Solutions exemplify the role of MSSPs?
Cyber Solutions exemplifies the proactive approach of MSSPs by providing 24/7 network monitoring, instant alerts, and real-time insights to help organizations swiftly address potential security threats and maintain operational safety.
What impact do cyber threats have on healthcare organizations?
Cyber threats can jeopardize sensitive data and compliance with regulatory standards, making it essential for healthcare organizations to prioritize their cybersecurity strategies to foster trust and safety in their operations.