Introduction
The Cybersecurity Maturity Model Certification (CMMC) is fundamentally reshaping the landscape for defense contractors. This critical framework is designed to bolster cybersecurity across the Defense Industrial Base, addressing the urgent need for enhanced security measures. As organizations grapple with the complexities of compliance, they not only stand to gain improved security but also a competitive edge in an increasingly scrutinized arena.
However, the reality is stark: only a fraction of firms currently meet the stringent requirements set forth by the CMMC. This raises a pressing question for many: how can organizations effectively navigate these evolving standards? The answer lies in understanding the implications of these requirements and taking proactive steps to secure their future amid the challenges of compliance. By embracing the CMMC framework, organizations can position themselves not just to survive, but to thrive in a landscape where cybersecurity is paramount.
Understand DOD CMMC Requirements: Core Principles and Objectives
The Cybersecurity Maturity Model Certification (CMMC) serves as a crucial framework established by the Department of Defense (DoD) to strengthen the cybersecurity posture of organizations and meet the requirements within the Defense Industrial Base (DIB). Designed to protect Controlled Unclassified Information (CUI) and Federal Contract Information (FCI) from cyber threats, this framework adheres to best practices and encompasses five maturity levels, each delineating specific practices and processes necessary for certification. The core objectives of CMMC are critical for organizations navigating today's complex cybersecurity landscape:
- Enhancing Cybersecurity: By mandating specific security practices, the framework aims to significantly mitigate vulnerabilities within the supply chain. Alarmingly, 99% of the DIB is not fully prepared for the CMMC requirements, underscoring the urgency of this initiative.
- Ensuring Compliance: Ensuring compliance involves integrating established standards, such as NIST SP 800-171, into a comprehensive certification process that necessitates external evaluations. This guarantees that entities meet stringent security requirements, fostering a culture of accountability.
- Promoting Accountability: The certification process holds contractors responsible for their cybersecurity practices, ensuring adherence to required standards for CMMC compliance. Currently, only 431 entities have achieved final Level 2 certification, representing a mere 0.5% of the estimated 80,000 firms needing to fulfill the requirements at this level of compliance.
- Facilitating Trust: By instituting a standardized certification process, trust is established between the DoD and its contractors, ensuring that sensitive data is managed securely. This trust is vital as companies face increasing scrutiny regarding their security protocols.
Understanding these principles is essential for organizations as they navigate the compliance landscape and the associated financial implications. The recent updates to the compliance framework, effective from November 10, 2025, further emphasize the urgency for organizations to prepare for adherence to CMMC standards, ensuring contract eligibility and enhancing their security posture.

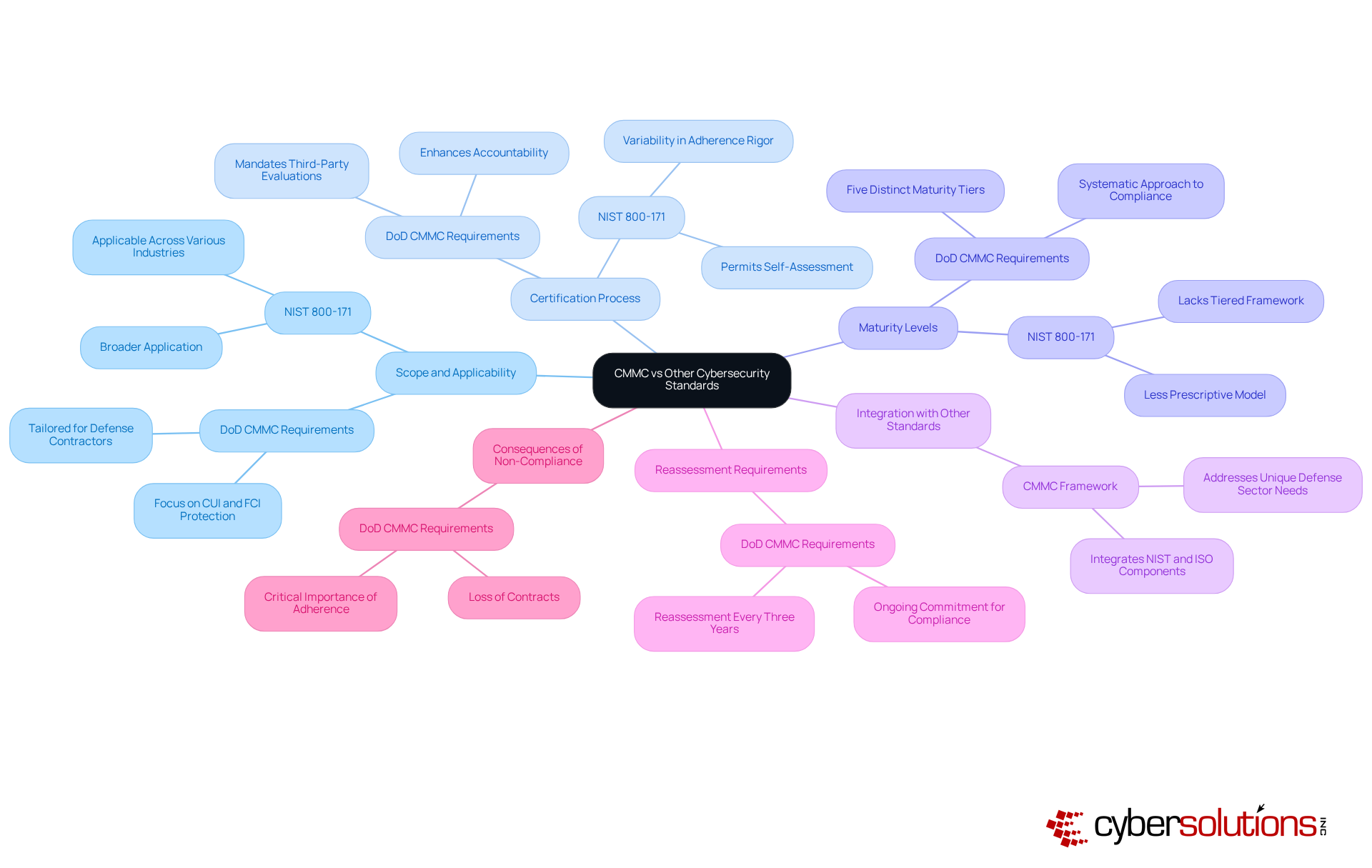
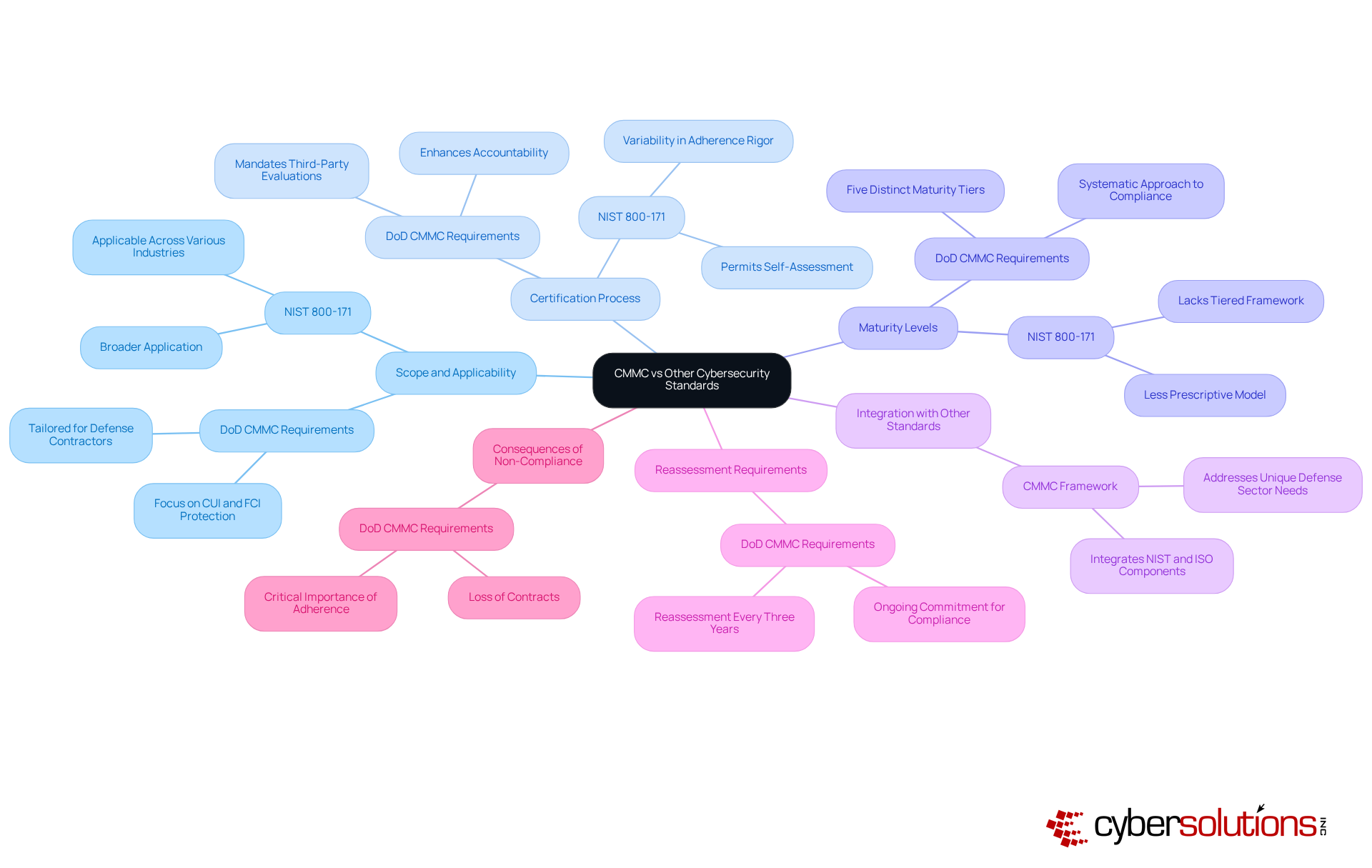
Compare CMMC with Other Cybersecurity Standards: Key Differences and Similarities
When it comes to cybersecurity, understanding the differences between the Cybersecurity Maturity Model Certification (CMMC) and other standards, particularly the NIST framework, is crucial for organizations, especially those in the defense sector.
- Scope and Applicability: The CMMC requirements are specifically tailored for defense contractors, focusing on the protection of Controlled Unclassified Information (CUI) and Federal Contract Information (FCI). In contrast, standards like ISO 27001 have a broader application across various industries, making them less specific to defense.
- The certification process presents a notable difference; the CMMC mandate third-party evaluations for elevated maturity levels, enhancing accountability. Conversely, other frameworks permit self-assessment, which can lead to variability in adherence rigor.
- Maturity Levels: The CMMC features five levels, each with escalating requirements, providing a systematic approach to compliance. Other standards, lacking this tiered framework, result in a less prescriptive model that may not adequately address the complexities faced by defense contractors.
- Integration with Other Standards: This framework effectively integrates components from established structures like NIST and ISO standards, creating a comprehensive regulatory model that specifically addresses the unique needs of the defense sector.
- Reassessment Requirements: Organizations must recognize that reassessment is necessary every three years for certifications at both Level 1 and Level 2, underscoring the ongoing commitment required for compliance.
- Consequences of Non-Compliance: Non-compliance with CMMC can lead to severe repercussions, including the loss of contracts, highlighting the critical importance of adhering to these requirements.
Understanding these distinctions is vital for companies as they evaluate their compliance strategies. Moreover, leveraging CMMC can provide small and medium-sized businesses (SMBs) with resources and ongoing compliance, including continuous monitoring and proactive risk assessments, ensuring alignment with regulatory standards in highly regulated sectors.
Evaluate the Impact of CMMC Compliance: Challenges and Strategic Benefits
is not just a regulatory hurdle; it represents a critical juncture for organizations navigating the complex landscape of cybersecurity to meet compliance requirements. As threats evolve, the need for robust security measures becomes paramount. However, achieving certification comes with its own set of challenges and strategic benefits that organizations must carefully consider.
Challenges:
- Financial Investment: Attaining certification can be a substantial financial endeavor, requiring investments in advanced technology, thorough training, and external evaluations. The Department of Defense estimates that reaching compliance may exceed $100,000, particularly for smaller contractors with limited budgets.
- Regulatory Complexity: The compliance process, specifically the documentation requirements, can be overwhelming, particularly for smaller entities that may lack the specialized governance, risk, and oversight (GRO) knowledge essential for effective execution. Many in the defense industrial sector feel unready for the new standards, with some firms taking no steps towards adherence, resulting in possible operational interruptions.
- Time Constraints: Organizations often face stringent deadlines to achieve compliance, particularly with the phased implementation schedule. The journey from initial gap assessment to final certification typically spans 12 to 24 months, which can strain resources and planning.
Strategic Benefits:
- Enhanced Security: Adherence to CMMC promotes better cybersecurity practices, significantly lowering the risk of data breaches and cyberattacks. Ongoing monitoring, a necessity under the framework, improves threat detection and response abilities, ultimately protecting sensitive information.
- Competitive Advantage: Organizations that obtain certification can differentiate themselves in the marketplace, gaining access to lucrative DoD contracts and enhancing their reputation as secure and trustworthy partners. As cybersecurity requirements become more prevalent in contracts by the end of 2025, organizations that are certified will be better positioned to win business.
- Cost Savings: Investing in cybersecurity measures now can yield substantial long-term savings by mitigating the higher costs associated with data breaches and non-compliance penalties. Firms that adhere to Level 2 certification can change meeting requirements from a cost center into a revenue generator, establishing themselves as low-risk allies to prime contractors.
By assessing these effects, organizations can make informed choices regarding their adherence strategies and investments, ultimately transforming compliance into a strategic benefit.

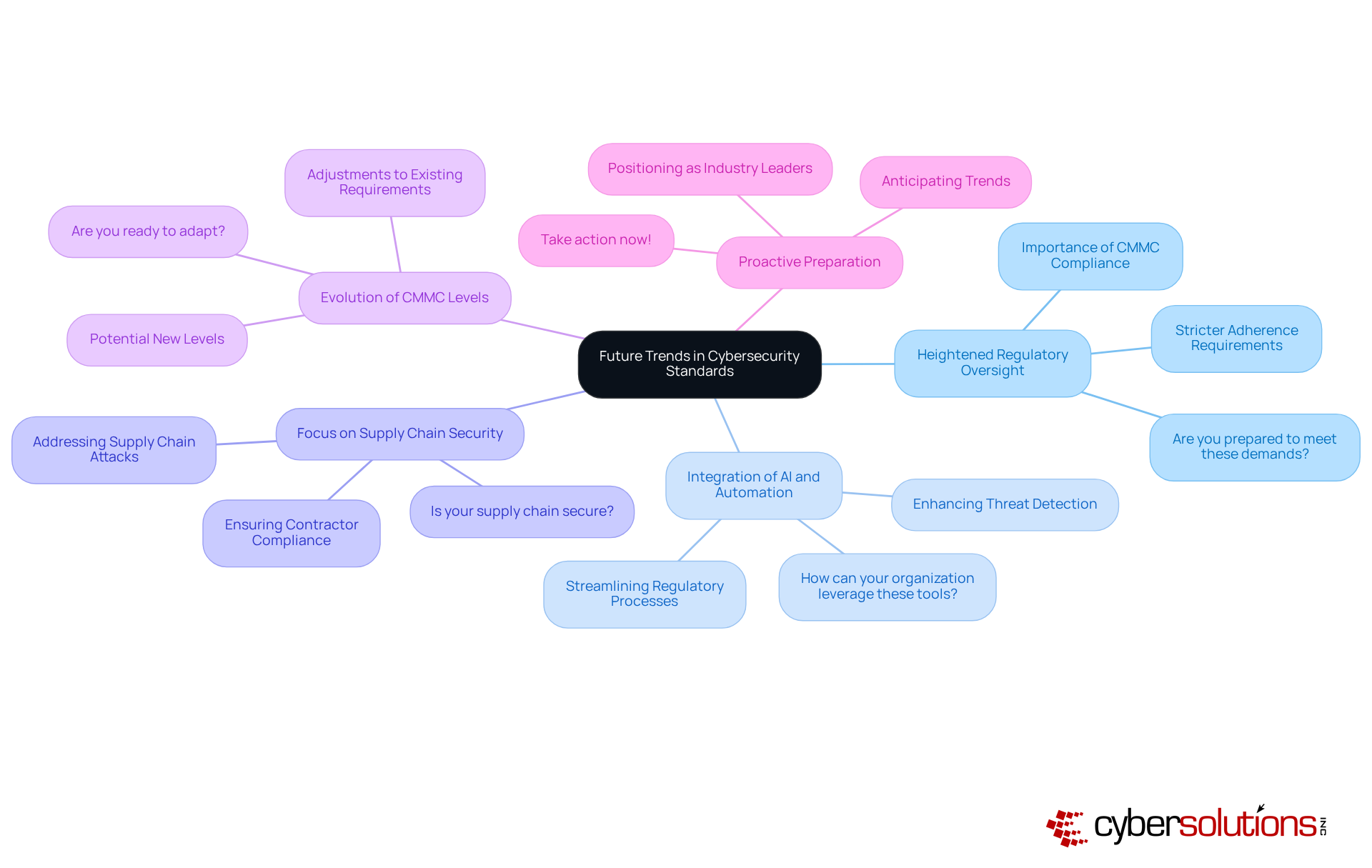
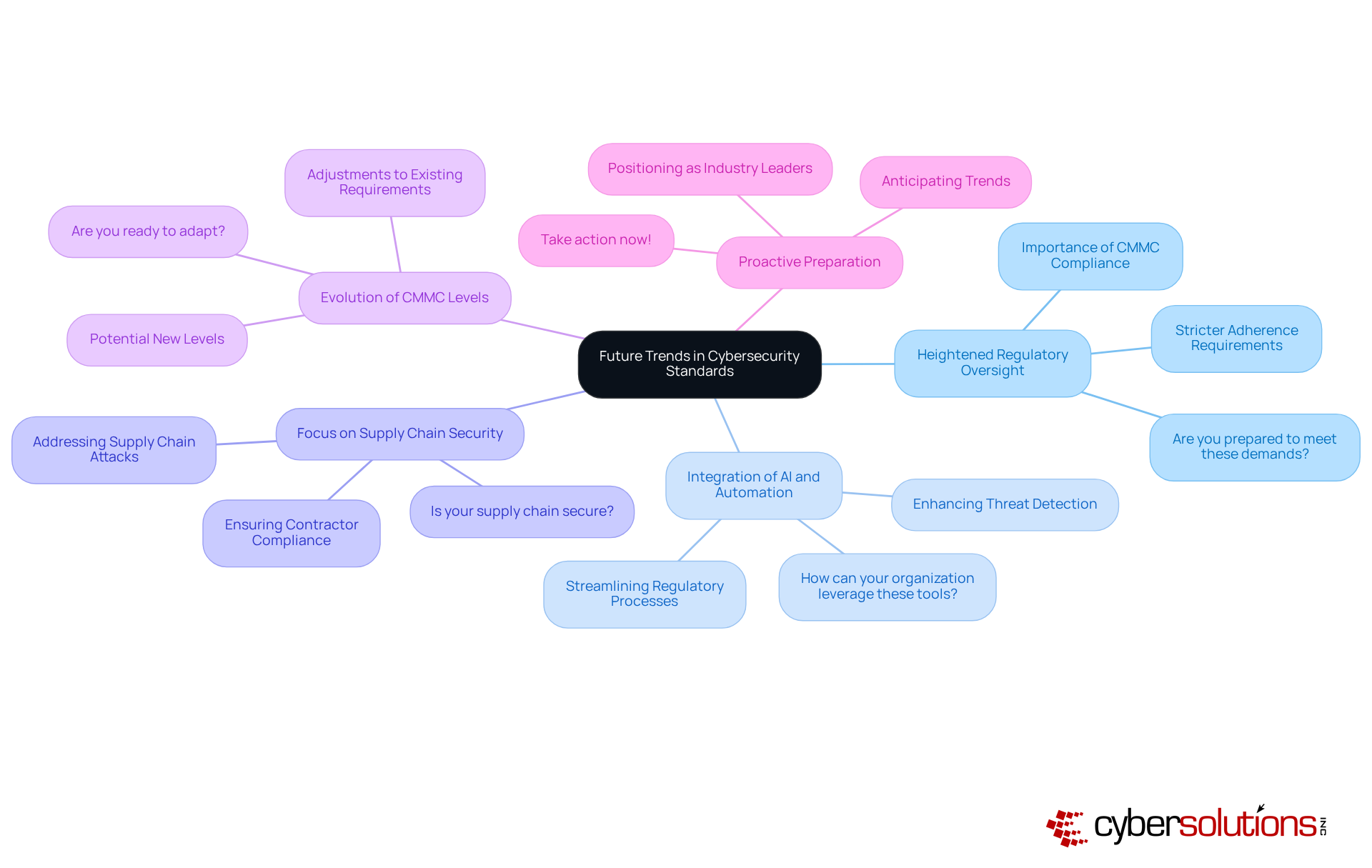
Anticipate Future Trends in Cybersecurity Standards: What Lies Ahead for CMMC and Beyond
As the cybersecurity landscape evolves, it’s crucial to recognize the trends that will shape the future of CMMC and related standards. The stakes are high, and organizations must adapt to stay ahead in this ever-changing environment.
Organizations: With cyber threats on the rise, regulatory agencies are expected to enforce stricter adherence requirements. This shift highlights the necessity for organizations to comply with regulations, which are becoming increasingly vital for maintaining eligibility in government contracts. Are you prepared to meet these demands?
Technologies: Organizations are turning to AI and automation technologies to streamline regulatory processes. These innovations not only enhance threat detection capabilities but also reduce the manual burdens of compliance, allowing teams to concentrate on strategic initiatives. How can your organization leverage these tools to improve efficiency?
Focus on Security: The rise of supply chain attacks has led to a stronger emphasis on ensuring that all contractors and subcontractors meet rigorous cybersecurity requirements. Future standards will likely reflect the need for comprehensive security across the entire supply chain, emphasizing the importance of collaboration. Is your supply chain secure?
Changes may occur as the CMMC framework potentially introduces new levels or adjusts existing standards in response to emerging threats and technological advancements. This flexibility will be essential for entities striving to remain at the forefront of the regulatory environment. Are you ready to adapt?
By proactively anticipating these trends, organizations can better prepare for the future of cybersecurity, positioning themselves as leaders in the arena. Don’t wait for change to happen - take action now to secure your organization’s future.
Conclusion
The Cybersecurity Maturity Model Certification (CMMC) stands as a crucial framework aimed at bolstering the cybersecurity posture of organizations within the Defense Industrial Base. In an era where cyber threats are constantly evolving, the CMMC framework mandates specific practices and accountability measures to safeguard sensitive information. For organizations striving for compliance, grasping the core principles and objectives of CMMC is not just beneficial; it’s essential for achieving certification and maintaining eligibility for defense contracts.
Key insights reveal the distinctive features of CMMC compared to other cybersecurity standards:
- Its specialized scope
- Tiered maturity levels
- The requirement for third-party evaluations
While compliance presents challenges - such as financial burdens and time constraints - these hurdles are outweighed by the strategic advantages of adherence, including enhanced security and a competitive edge in the marketplace. Moreover, organizations must stay ahead of emerging trends, such as increased regulatory oversight and the integration of advanced technologies to streamline compliance processes.
In light of these discussions, it’s imperative for organizations to proactively prepare for the shifting landscape of cybersecurity standards. By embracing the principles of CMMC and adapting to anticipated changes, businesses can position themselves as leaders in the defense sector while effectively safeguarding sensitive information. Taking decisive action now not only ensures compliance with DoD CMMC requirements but also cultivates a culture of resilience against future cyber threats.
Frequently Asked Questions
What is the Cybersecurity Maturity Model Certification (CMMC)?
The CMMC is a framework established by the Department of Defense (DoD) to enhance the cybersecurity posture of organizations within the Defense Industrial Base (DIB) and to protect Controlled Unclassified Information (CUI) and Federal Contract Information (FCI) from cyber threats.
What are the core objectives of the CMMC?
The core objectives of the CMMC include enhancing cybersecurity by mitigating vulnerabilities, ensuring compliance with established standards, promoting accountability among contractors, and facilitating trust between the DoD and its contractors.
How many maturity levels does the CMMC framework have?
The CMMC framework encompasses five maturity levels, each outlining specific practices and processes necessary for certification.
Why is the CMMC certification process important for organizations?
The CMMC certification process is important because it holds contractors accountable for their cybersecurity practices, ensures adherence to required standards, and fosters a culture of accountability to safeguard sensitive information.
What is the current state of compliance with DoD CMMC requirements?
Currently, only 431 entities have achieved final Level 2 certification, which is just 0.5% of the estimated 80,000 firms that need to fulfill the DoD CMMC requirements at this level.
When do the recent updates to the CMMC compliance framework take effect?
The recent updates to the compliance framework will take effect on November 10, 2025.
What is the significance of understanding CMMC principles for organizations?
Understanding CMMC principles is essential for organizations as it helps them navigate regulatory complexities and financial implications, ensuring contract eligibility and enhancing their overall security posture.
List of Sources
- Understand DOD CMMC Requirements: Core Principles and Objectives
- CMMC Deadline 2025: CMMC Phase 1 Is Now Live (https://secureframe.com/blog/cmmc-deadline-announcement)
- federalnewsnetwork.com (https://federalnewsnetwork.com/contracting/2025/11/new-cmmc-rules-take-effect-monday-with-contractors-facing-uncertainties)
- Pentagon begins enforcing CMMC compliance, but readiness gaps remain (https://defensescoop.com/2025/11/10/cmmc-compliance-dod-enforcement-defense-industry-readiness-gaps)
- CMMC 2.0 Details and Links to Key Resources (https://business.defense.gov/Programs/Cyber-Security-Resources/CMMC-20)
- 48 CFR Published: CMMC Enforceable on Nov 10, 2025 (https://preveil.com/blog/cmmc-final-rule-published)
- Compare CMMC with Other Cybersecurity Standards: Key Differences and Similarities
- CMMC Compliance 2025: What’s Changing and When? (https://compassmsp.com/resources/cmmc-compliance-2025-whats-changing-and-when)
- How CMMC News Is Changing The Rules For Government Contractors (https://cybersecinvestments.com/2025/09/cmmc-news-changing-rules-government-contractors)
- This Is Not a Drill: Cybersecurity Maturity Model Certification Goes into Effect on November 10, 2025 [Alert] (https://cozen.com/news-resources/publications/2025/this-is-not-a-drill-cmmc-will-go-into-effect-on-november-10-2025)
- D-Day: November 10, 2025; or Why CMMC is Already A Reality (https://idenhaus.com/d-day-november-10-2025-or-why-cmmc-is-already-a-reality)
- Evaluate the Impact of CMMC Compliance: Challenges and Strategic Benefits
- Pentagon begins enforcing CMMC compliance, but readiness gaps remain (https://defensescoop.com/2025/11/10/cmmc-compliance-dod-enforcement-defense-industry-readiness-gaps)
- CMMC Compliance in 2025: The Strategic Roadmap for Defense Contractors (https://compassmsp.com/resources/cmmc-compliance-in-2025-the-strategic-roadmap-for-defense-contractors)
- Cybersecurity Compliance: The Costs, Risks And Race To Certification (https://forbes.com/sites/heatherwishartsmith/2025/07/07/cybersecurity-compliance-the-costs-risks-and-race-to-certification)
- CMMC 2.0 Compliance: What Defense Contractors Need to Know in 2025 and 2026 - SecureStrux (https://securestrux.com/resources/insights/cmmc-2-0-compliance-what-defense-contractors-need-to-know-in-2025-and-2026)
- CMMC: New Era of Cybersecurity Compliance for Defense Contractors | Alston & Bird (https://alston.com/en/insights/publications/2025/11/cmmc-cybersecurity-compliance-defense)
- Anticipate Future Trends in Cybersecurity Standards: What Lies Ahead for CMMC and Beyond
- Pentagon begins enforcing CMMC compliance, but readiness gaps remain (https://defensescoop.com/2025/11/10/cmmc-compliance-dod-enforcement-defense-industry-readiness-gaps)
- Department of Defense Releases Long-Awaited DFARS Cybersecurity Final Rule for Government Contractors and Subcontractors - Law Offices of Snell & Wilmer (https://swlaw.com/publication/department-of-defense-releases-long-awaited-dfars-cybersecurity-final-rule-for-government-contractors-and-subcontractors)
- CMMC compliance checklist: Stay eligible for DoD contracts (https://wipfli.com/insights/articles/cmmc-compliance-checklist)
- CMMC Regulations: Key Questions and Answers for Defense Contractors | Insights | Holland & Knight (https://hklaw.com/en/insights/publications/2025/11/cmmc-regulations-key-questions-and-answers-for-defense-contractors)
- CMMC 2.0 Details and Links to Key Resources (https://business.defense.gov/Programs/Cyber-Security-Resources/CMMC-20)