
Achieving NIST 800 compliance is more than just ticking a box on a regulatory checklist; it stands as a crucial defense against the rising tide of cyber threats. In today’s landscape, organizations grapple with increasingly complex compliance requirements, making it essential for leaders to grasp the fundamental steps necessary to navigate this framework. What strategies can executives adopt to ensure their organizations not only meet these standards but also bolster their overall cybersecurity posture?
As the threat landscape evolves, the implications for organizations are profound. Cybersecurity is no longer a mere IT concern; it is a critical business imperative that demands attention from the highest levels of leadership. By understanding the unique challenges posed by compliance, executives can take proactive measures to safeguard their organizations.
To effectively address these challenges, consider implementing robust cybersecurity strategies that align with NIST 800 standards. This not only ensures compliance but also enhances your organization’s resilience against potential breaches. The time to act is now - prioritize cybersecurity and fortify your defenses.
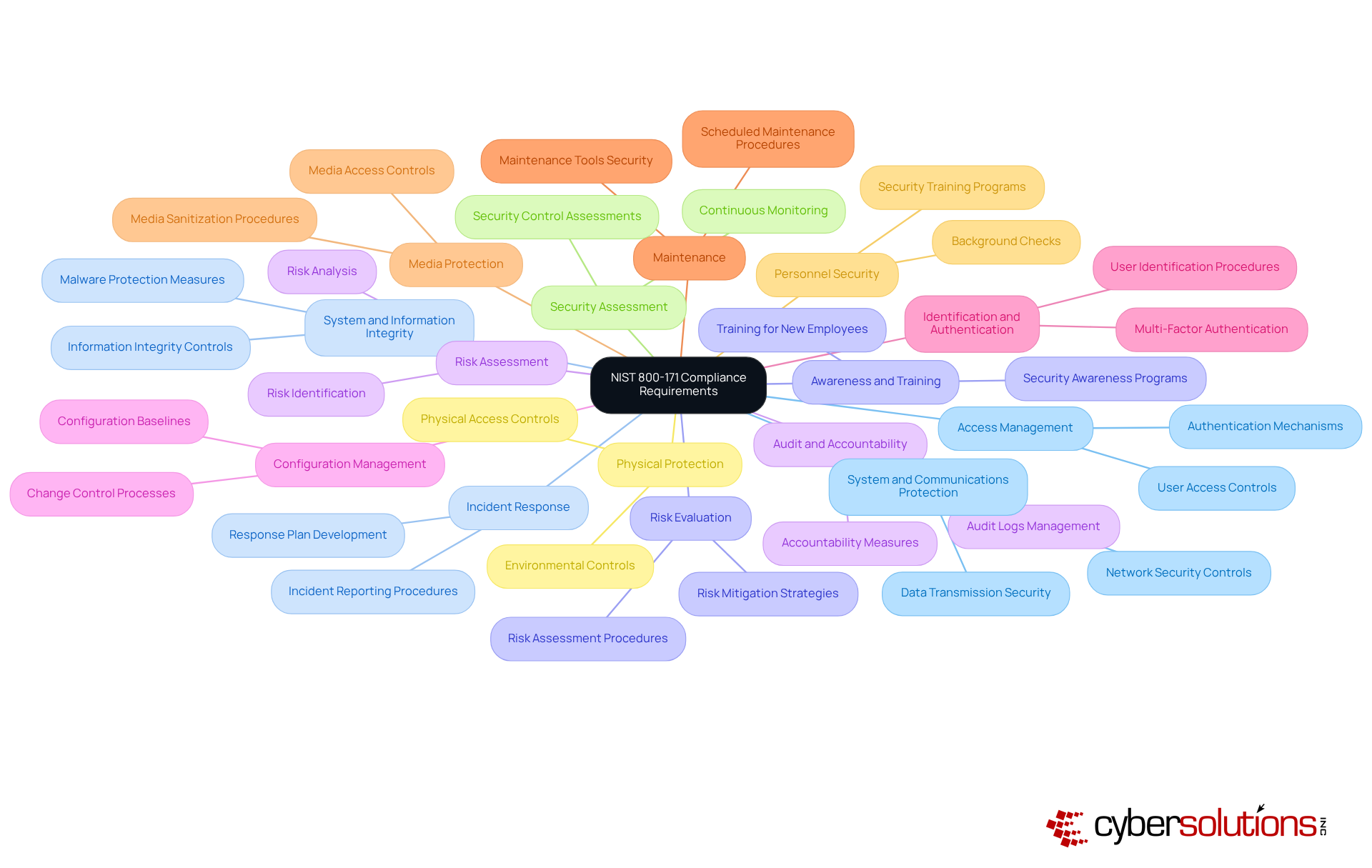
To achieve compliance, organizations must first familiarize themselves with the 14 categories of NIST 800-171. These categories encompass critical areas such as:
Each category contains specific measures vital for effectively protecting Controlled Unclassified Information (CUI). Recent updates to NIST 800-171, particularly the consolidation of requirements in Revision 3, underscore the necessity for organizations to adapt their security practices accordingly.
Leaders should conduct a thorough review of the compliance framework to fully grasp the requirements and pinpoint applicable controls for their operations. This foundational knowledge is crucial for devising a strategy that not only aligns with organizational objectives but also meets regulatory expectations. Notably, 55% of organizations report being extremely familiar with NIST 800-171 requirements, highlighting the significance of this knowledge in navigating the complexities of compliance.
Understanding these requirements is not merely a regulatory obligation; it is a strategic advantage that can significantly enhance an organization's defensive posture and resilience against cyber threats. Are you ready to take the necessary steps to safeguard your organization?
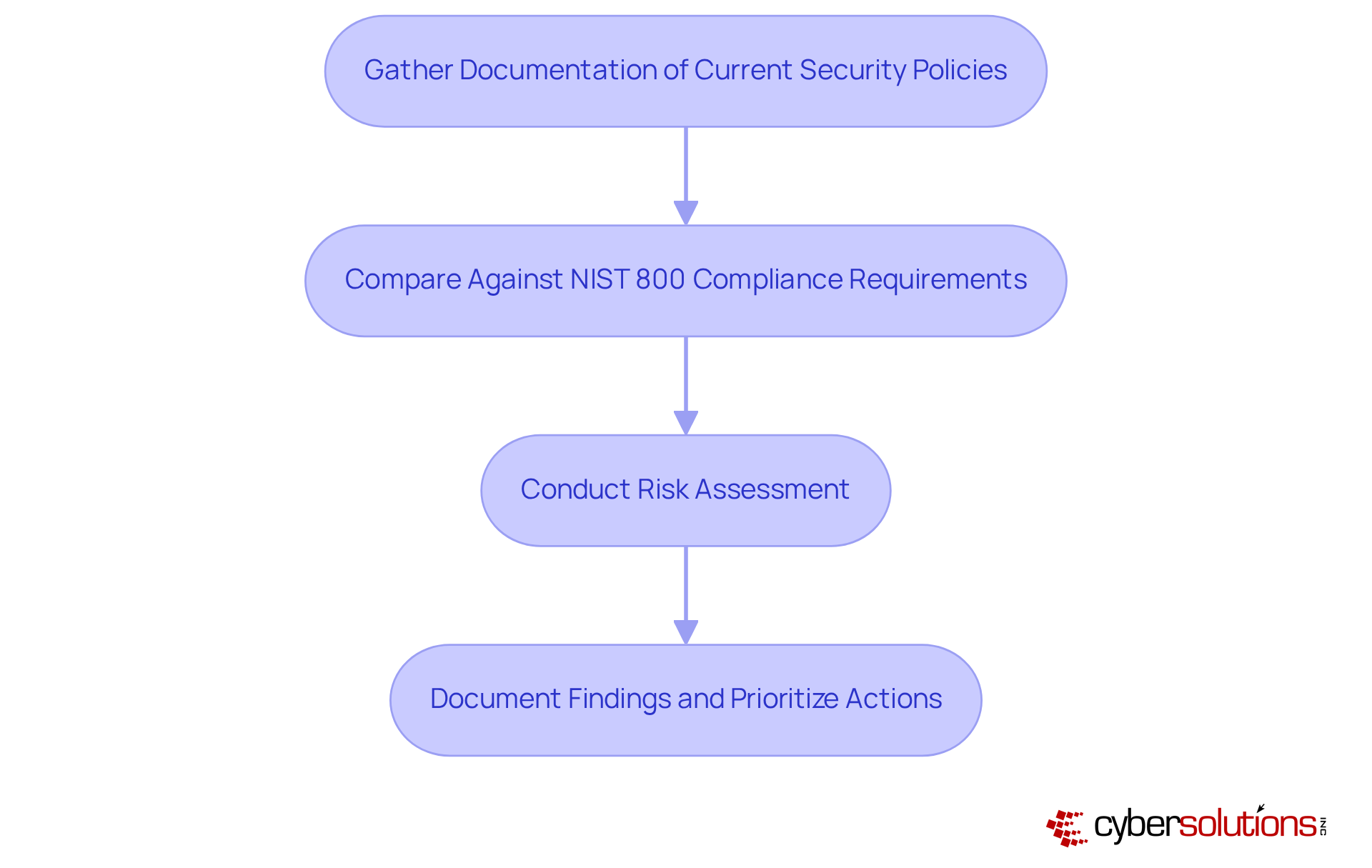
Begin by gathering documentation of your current security policies and procedures. This foundational step is crucial for establishing a baseline in your organization. Next, conduct a thorough comparison against the requirements to pinpoint any gaps. This involves a detailed evaluation of each control family to ascertain whether current measures align with established standards.
Following this gap analysis, perform a comprehensive assessment to identify potential threats and vulnerabilities. This assessment should include the identification of critical assets, an evaluation of the likelihood of various threats, and an analysis of the potential impact on your organization. Document your findings meticulously to create a clear overview of necessary improvements, prioritizing actions based on assessed risk levels.
For instance, entities that have adopted structured frameworks have reported notably reduced breach expenses, underscoring the importance of compliance. Furthermore, as regulatory practices evolve, incorporating automation tools can simplify the process, enhancing efficiency and precision in identifying regulatory gaps.
Cyber Solutions also offers expert guidance and support during the official certification process, ensuring your organization is fully prepared to secure certification. With the right strategies in place, you can effectively achieve compliance.
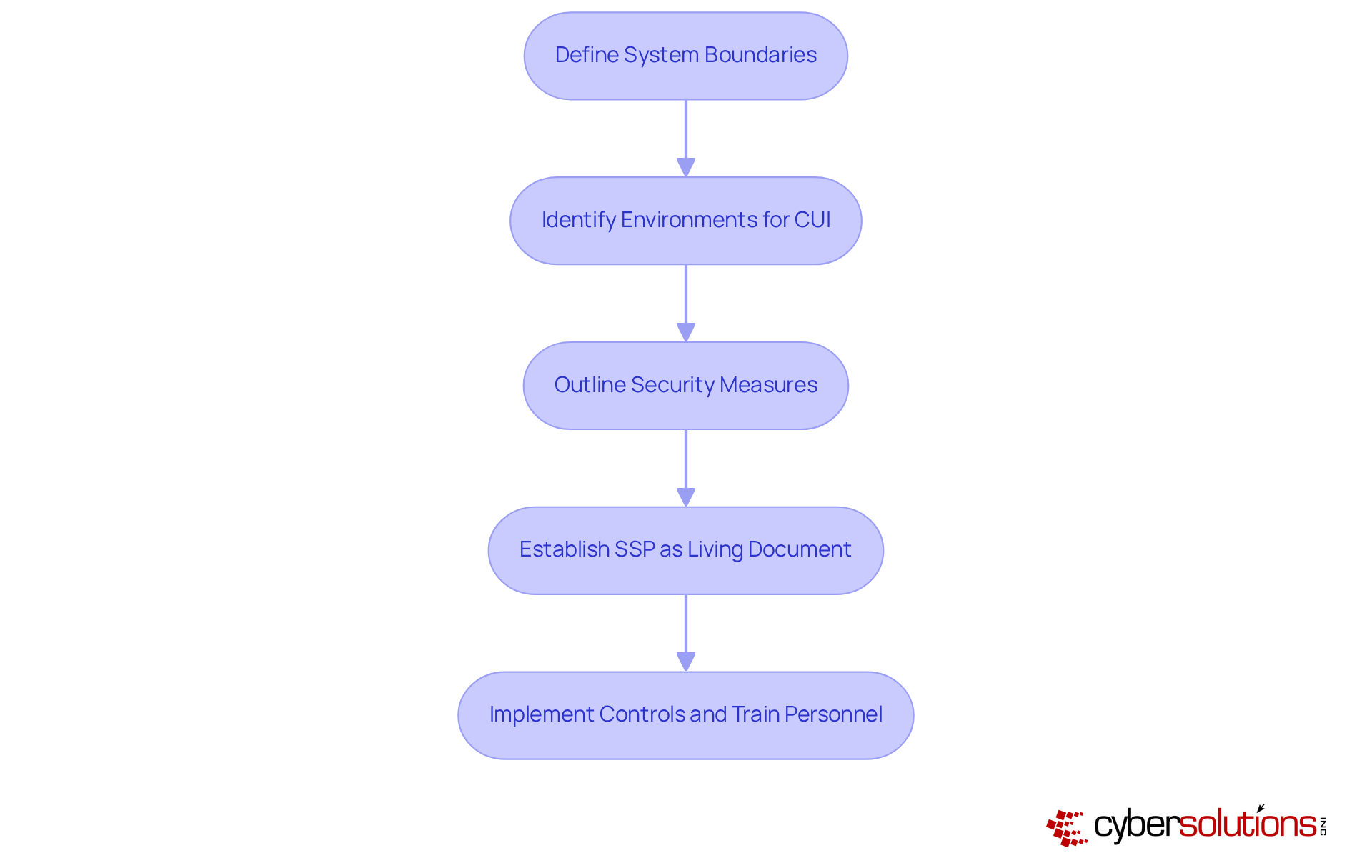
Creating a robust system security plan is not just a regulatory requirement; it’s a critical step in safeguarding sensitive information. Organizations must provide detailed descriptions of how each security measure will be implemented, clearly outlining the roles responsible for each task and the necessary resources. Start by defining the system boundaries and pinpointing the environments where data is processed, stored, and shared. What specific measures will you apply? Consider technical, administrative, and physical safeguards that are essential for a comprehensive approach.
The SSP should be viewed as a living document, requiring regular updates to reflect any changes in the organization’s structure or operational context. This adaptability ensures that the SSP remains relevant and effective against the ever-evolving landscape of cybersecurity threats. Once the SSP is established, it’s crucial to implement the specified controls and provide thorough training for all personnel regarding their roles and responsibilities in maintaining security. This proactive approach not only enhances the overall security posture of the organization but also ensures compliance with regulatory standards.
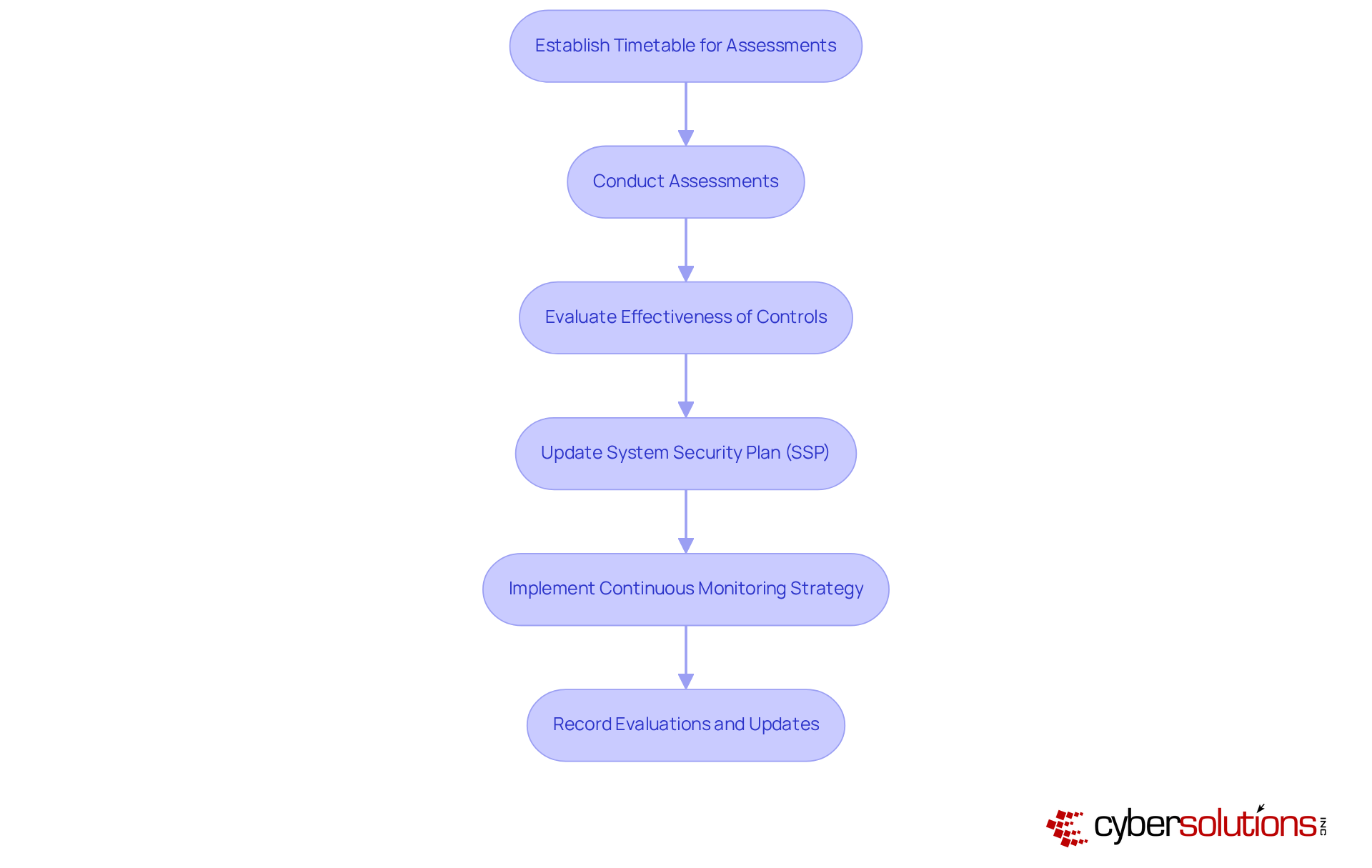
Establishing a timetable for assessments is not just important; it’s essential. Conducting these assessments quarterly or bi-annually allows organizations to effectively evaluate the effectiveness of implemented controls and update the security measures as needed. With 85% of executives acknowledging that regulations have grown more complex in recent years, staying informed about changes to the compliance requirements is critical. This complexity underscores the need for organizations to adapt their strategies accordingly.
Implementing a continuous monitoring strategy empowers organizations to swiftly detect and respond to threats, significantly enhancing their overall protective stance. Moreover, meticulously recording all evaluations and updates is vital for maintaining a clear regulatory record, which proves invaluable during audits and reviews. Regular assessments not only support sustained compliance but also bolster security by systematically identifying measures that effectively safeguard Controlled Unclassified Information (CUI).
In today’s rapidly evolving cybersecurity landscape, can your organization afford to overlook the importance of these evaluations? The time to act is now.
Achieving NIST 800 compliance is not just a regulatory checkbox; it’s a vital strategy for safeguarding sensitive information in today’s complex cybersecurity landscape. With cyber threats evolving rapidly, organizational leaders must adopt a proactive approach to enhance their cybersecurity posture. By thoroughly understanding the NIST 800-171 framework, conducting detailed gap analyses, and developing robust System Security Plans (SSPs), organizations can significantly bolster their defenses against potential threats.
Key steps in this journey include:
This diligence is essential as compliance complexities increase and the landscape of cyber threats continues to shift.
Ultimately, committing to NIST 800 compliance transcends mere regulatory adherence; it fosters a culture of security that protects sensitive information and builds trust with stakeholders. Organizations must take decisive action now, ensuring they are well-prepared to navigate the challenges of cybersecurity and compliance in the future. Are you ready to fortify your defenses and embrace a culture of security?
What is NIST 800-171 compliance?
NIST 800-171 compliance refers to the set of security requirements established by the National Institute of Standards and Technology to protect Controlled Unclassified Information (CUI) within organizations.
What are the main categories of security requirements in NIST 800-171?
The main categories of security requirements in NIST 800-171 include Access Management, Incident Response, and Risk Evaluation, among others, totaling 14 categories.
Why is it important for organizations to understand NIST 800-171 requirements?
Understanding NIST 800-171 requirements is crucial for organizations as it helps them devise compliance strategies that align with regulatory expectations and enhance their cybersecurity posture against threats.
What recent updates have been made to NIST 800-171?
Recent updates include the consolidation of requirements in Revision 3, which necessitates organizations to adapt their compliance strategies accordingly.
How familiar are organizations with NIST 800 compliance requirements?
According to reports, 55% of organizations state they are extremely familiar with NIST 800 compliance requirements, indicating its importance in the realm of cybersecurity and compliance.
What should leaders do to ensure compliance with NIST 800-171?
Leaders should conduct a thorough review of the NIST 800-171 document to understand the requirements and identify applicable controls for their operations.