
In today's world, where cyber threats are more prevalent than ever, understanding the complexities of vulnerability scanning is crucial for C-suite leaders. This automated process goes beyond being a mere technical task; it acts as a frontline defense, empowering organizations to pinpoint and address security weaknesses before they can be exploited. With the alarming rise in cybersecurity breaches, a pressing question arises: how can executives ensure their organizations are not just compliant, but truly resilient against evolving threats?
This guide explores the mechanics of vulnerability scanning, its vital role in risk management, and the best practices that can protect sensitive information while enhancing financial stability. By delving into these aspects, we aim to equip leaders with the knowledge needed to navigate the intricate landscape of cybersecurity effectively.
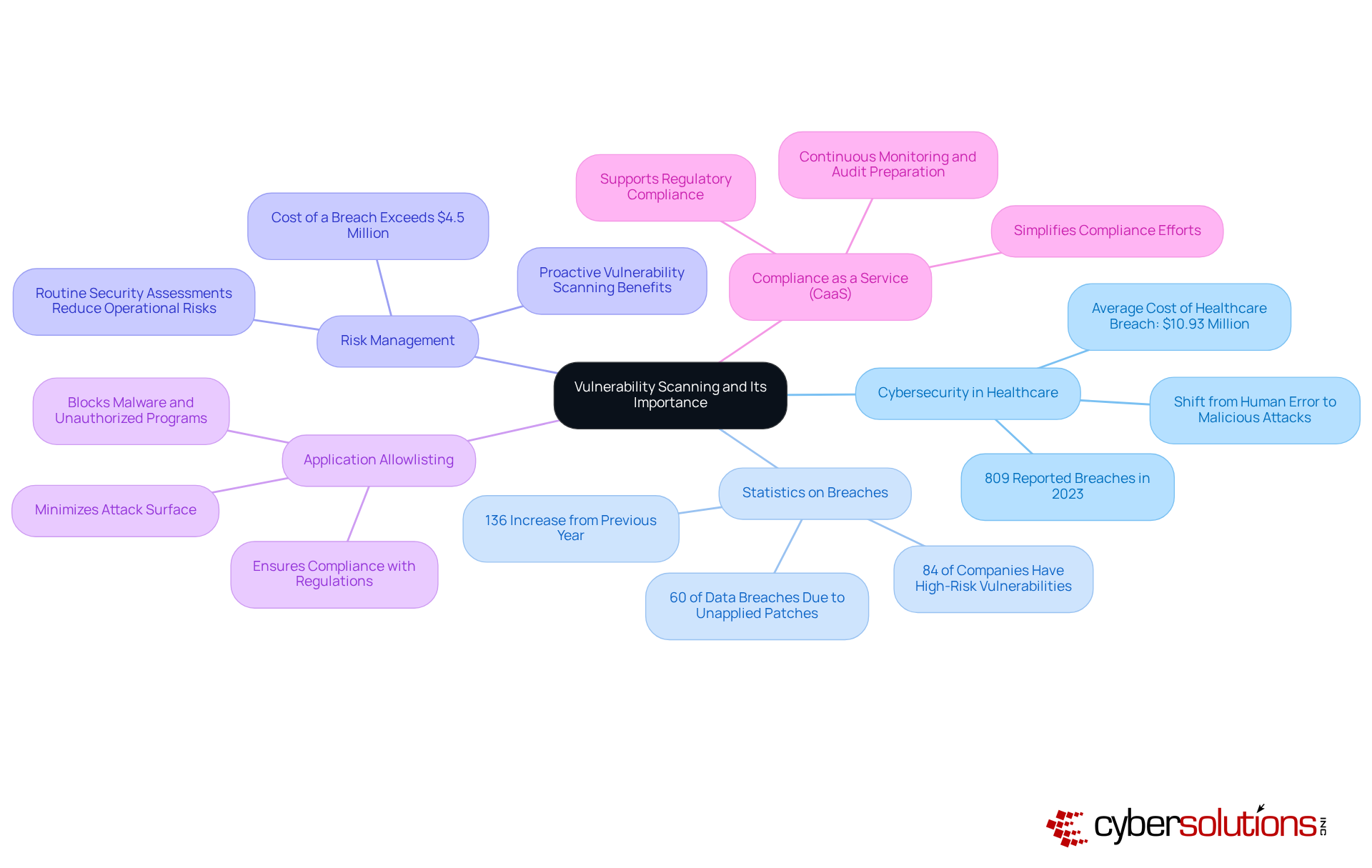
is not just a technical necessity; it’s a critical component of healthcare that can make or break an organization. With the staggering - 809 reported in 2023 alone, a 136% increase from the previous year - healthcare providers face unique challenges that demand immediate attention. To understand , it emerges as an essential automated process designed to pinpoint across software, systems, and networks. This proactive approach allows organizations to learn , enabling them to identify vulnerabilities before they can be exploited, safeguarding sensitive information and ensuring compliance with industry standards. After all, maintaining is paramount, and the cost of a breach can exceed $4.5 million, making risk management not just advisable but essential.
Statistics reveal that 84% of companies harbor , with half of these potentially addressable through straightforward software updates. This highlights the . By conducting routine , organizations can significantly reduce operational risks and bolster their financial stability, avoiding incidents that could lead to severe reputational damage.
In addition to vulnerability scanning, stands out as a gold standard in . This method actively blocks malware and unauthorized programs, effectively shrinking the attack surface and minimizing vulnerabilities. By permitting only authorized applications to run, organizations can thwart ransomware and other malicious software, ensuring compliance with stringent regulations like HIPAA, PCI-DSS, and GDPR.
For C-suite executives, understanding in conjunction with is crucial, as these elements directly impact the organization’s risk management and financial health. Furthermore, provides comprehensive solutions to meet regulatory requirements, offering continuous monitoring and audit preparation support - especially beneficial for highly regulated industries. This holistic approach to not only enhances protection but also simplifies compliance efforts, enabling organizations to navigate complex regulatory landscapes with greater ease.
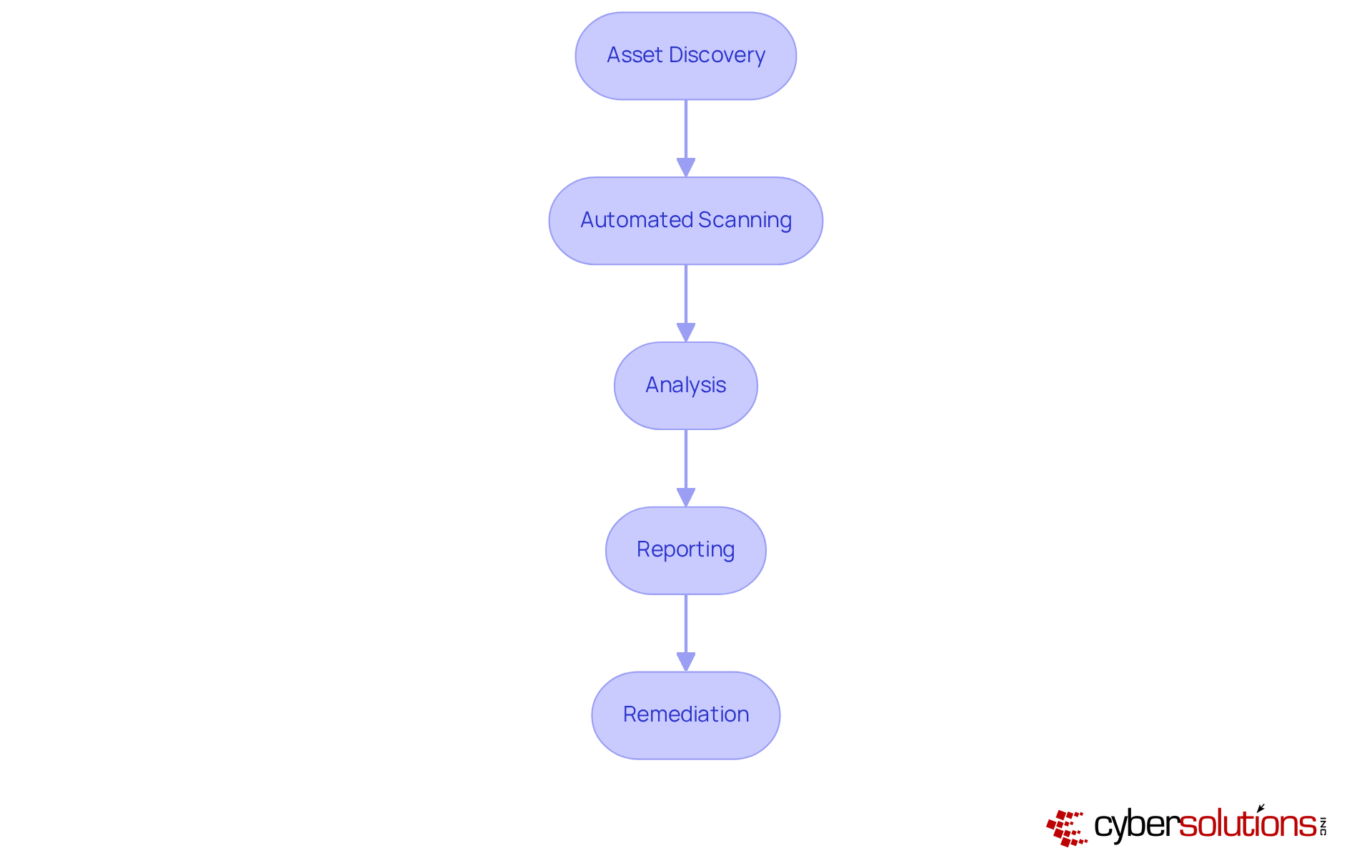
, and it encompasses several essential steps:
Integrating into risk assessment processes not only boosts the effectiveness of security measures but also aligns with best practices recommended by cybersecurity experts. Organizations that weave thorough [asset discovery](https://discovercybersolutions.com/blog-posts/10-benefits-of-managed-firewall-solutions-for-business-security) into their risk management strategies are better equipped to proactively identify and address potential threats. As Soros pointed out, when selecting new partners, highlighting the pressing need for efficient vulnerability management.
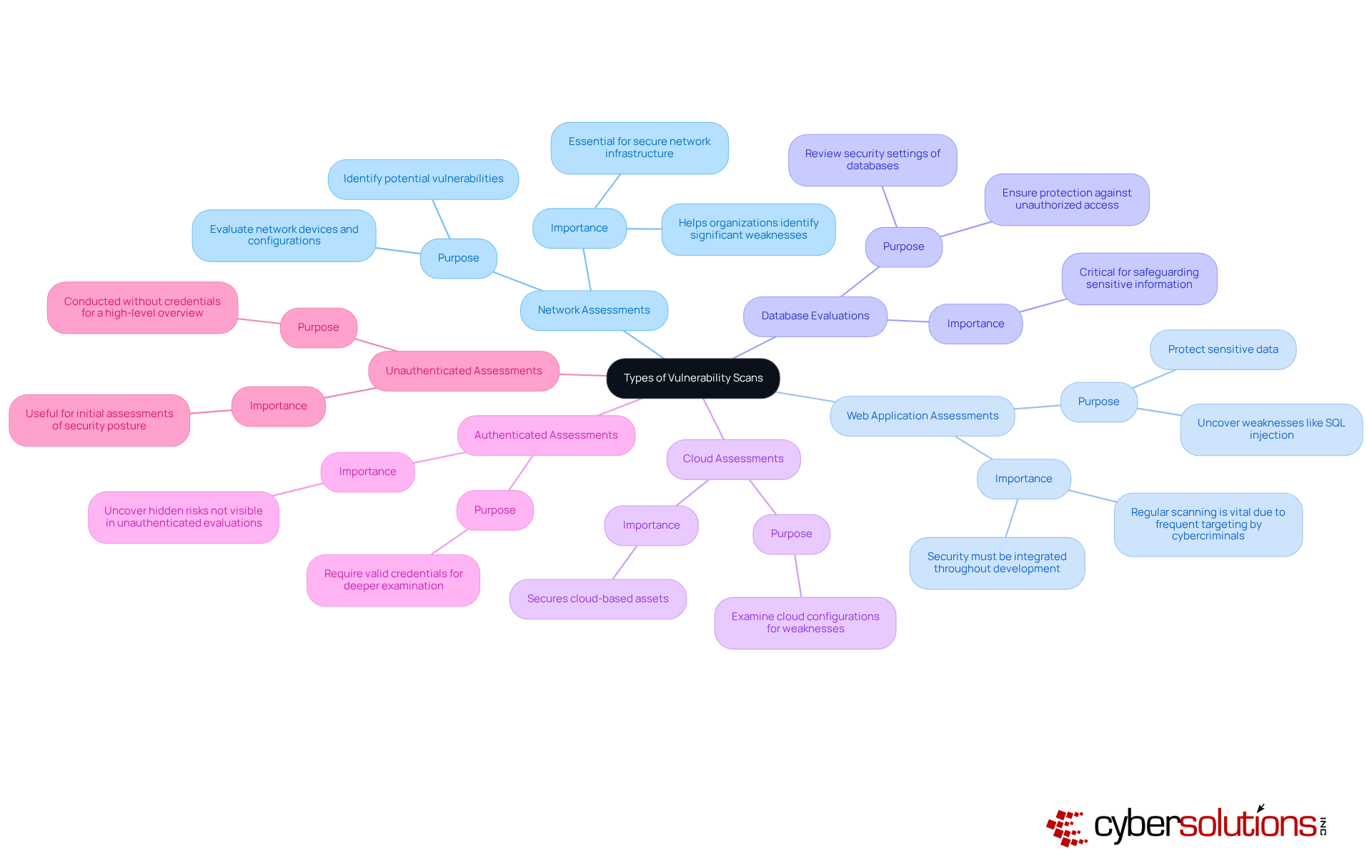
In today’s cybersecurity landscape, it is crucial for organizations to understand how does work to effectively protect their assets. These scans can be categorized into several types, each tailored to address specific security needs:
Looking ahead to 2025, a are expected to employ a combination of these scans to bolster their cybersecurity strategies, particularly in understanding how does work to identify and mitigate risks across various environments. Optimal methods for assessing network vulnerabilities include regular evaluations, prioritizing critical issues, and integrating results into the overall security management framework. A study highlights that the average cost of a financial breach is approximately $5.9 million, underscoring the importance of .
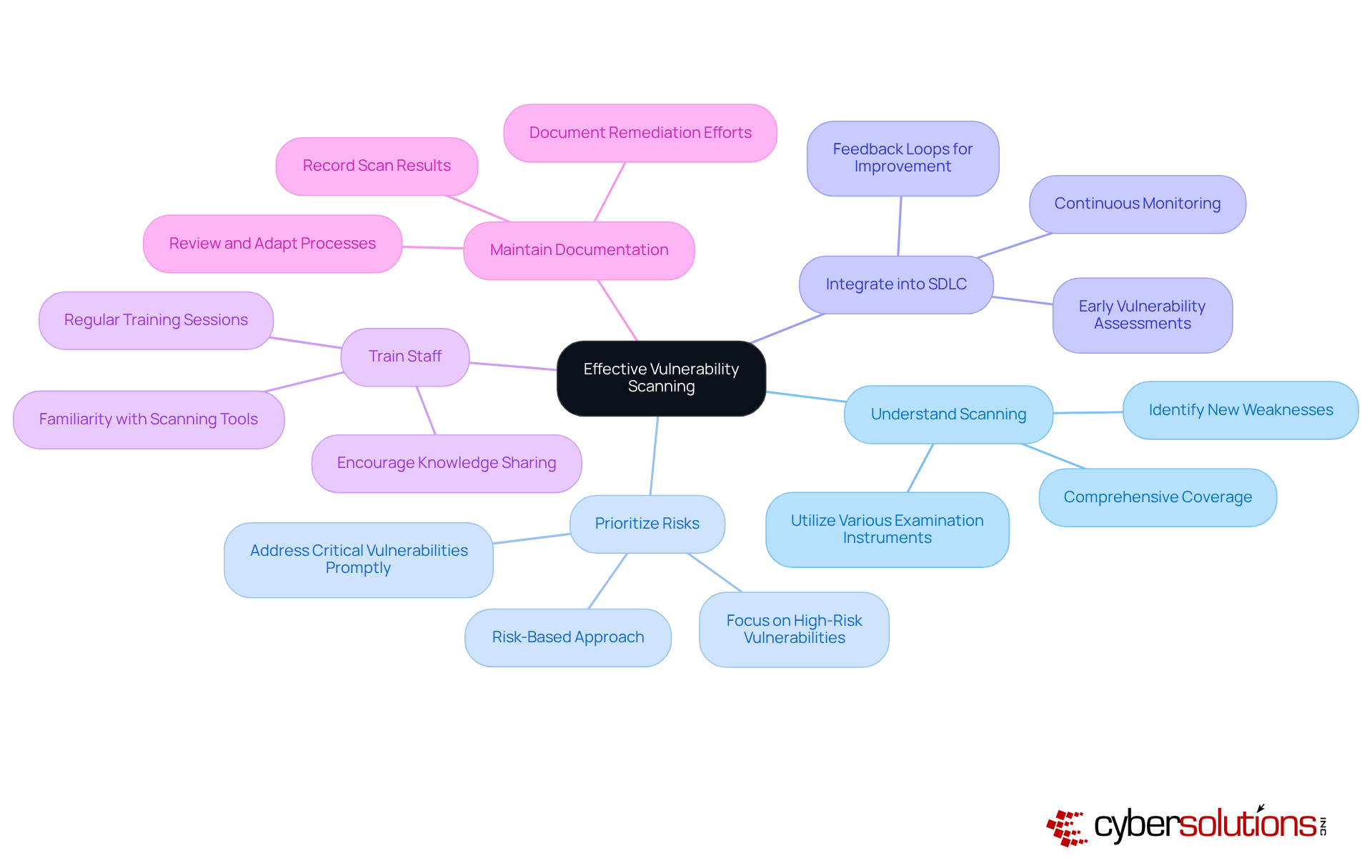
To ensure effective , organizations must understand and recognize the critical importance of cybersecurity in today’s landscape. Regular scanning is essential; knowing allows for the identification of new weaknesses as they arise. Next, it’s crucial to - adopting a risk-based approach helps organizations focus on vulnerabilities that could have the most significant impact.
Integrating analysis into the is another vital practice. By incorporating early in the development process, organizations can learn to catch vulnerabilities before they become problematic. Additionally, it’s important to understand how works; utilizing various examination instruments ensures and minimizes blind spots.
Moreover, organizations should effectively. Understanding [how vulnerability scanning works](https://breachpoint.com/the-importance-of-vulnerability-scanning-for-cybersecurity) is essential for ensuring that in the latest scanning tools and techniques, which maximizes the efforts. Finally, maintaining thorough documentation of scan results and remediation efforts is key. Regularly reviewing these processes allows organizations to adapt to evolving threats.
By following these best practices, organizations can significantly enhance their .
Understanding the mechanisms of vulnerability scanning is crucial for C-suite leaders who want to strengthen their organizations against cyber threats. In today’s landscape, where data breaches are alarmingly frequent, this automated process not only identifies security weaknesses but also plays a vital role in ensuring compliance and protecting sensitive information. Executives must prioritize cybersecurity measures, making vulnerability scanning an essential component of their organizational strategy.
This article explores the key processes involved in vulnerability scanning, such as:
It highlights the necessity of integrating these practices within the software development lifecycle and adopting a risk-based approach to prioritize vulnerabilities effectively. Furthermore, the discussion on various types of scans - ranging from network assessments to authenticated evaluations - underscores the need for a customized strategy that addresses specific security concerns within an organization.
Ultimately, the importance of vulnerability scanning goes beyond mere compliance; it represents a critical investment in an organization’s resilience against cyber threats. By embracing effective scanning strategies and fostering a culture of cybersecurity awareness, businesses can not only safeguard their assets but also improve their overall financial health. C-suite leaders are urged to champion these initiatives, ensuring their organizations are proactive rather than reactive in the face of evolving cybersecurity challenges.
What is vulnerability scanning?
Vulnerability scanning is an automated process designed to identify security weaknesses across software, systems, and networks. It helps organizations discover vulnerabilities before they can be exploited.
Why is vulnerability scanning important in healthcare?
Vulnerability scanning is crucial in healthcare due to the significant rise in data breaches, with 809 reported in 2023. It helps organizations safeguard sensitive information, ensure compliance with industry standards, and maintain stakeholder confidence.
What are the financial implications of neglecting risk management?
The cost of a data breach can exceed $4.5 million. Additionally, 84% of companies face significant risks, with many of these risks potentially addressable through simple software updates, highlighting the financial repercussions of neglecting risk management.
How can routine security assessments benefit organizations?
Conducting routine security assessments can significantly reduce operational risks and bolster financial stability, helping organizations avoid incidents that may lead to severe reputational damage.
What is application allowlisting, and how does it enhance cybersecurity?
Application allowlisting is a cybersecurity method that actively blocks malware and unauthorized programs by permitting only authorized applications to run. This approach minimizes vulnerabilities and shrinks the attack surface, helping to thwart ransomware and other malicious software.
Why should C-suite executives understand vulnerability scanning and application allowlisting?
C-suite executives should understand these concepts because they directly impact the organization’s risk management and financial health, influencing overall cybersecurity strategy and compliance efforts.
What is Compliance as a Service (CaaS)?
Compliance as a Service (CaaS) provides comprehensive solutions to meet regulatory requirements, offering continuous monitoring and audit preparation support, particularly beneficial for industries with strict regulations.
How does a holistic approach to cybersecurity benefit organizations?
A holistic approach to cybersecurity enhances protection and simplifies compliance efforts, enabling organizations to navigate complex regulatory landscapes more effectively.