Introduction
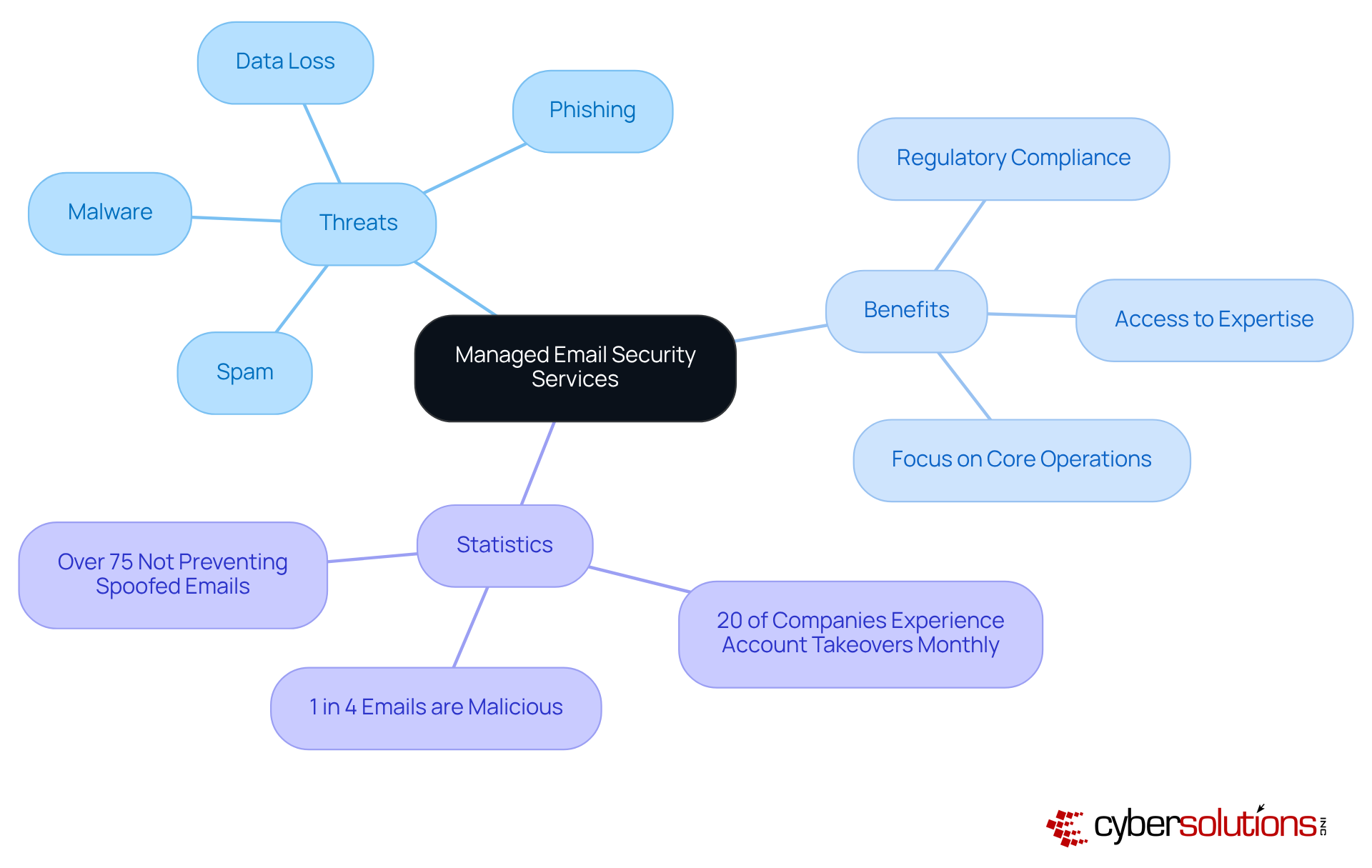
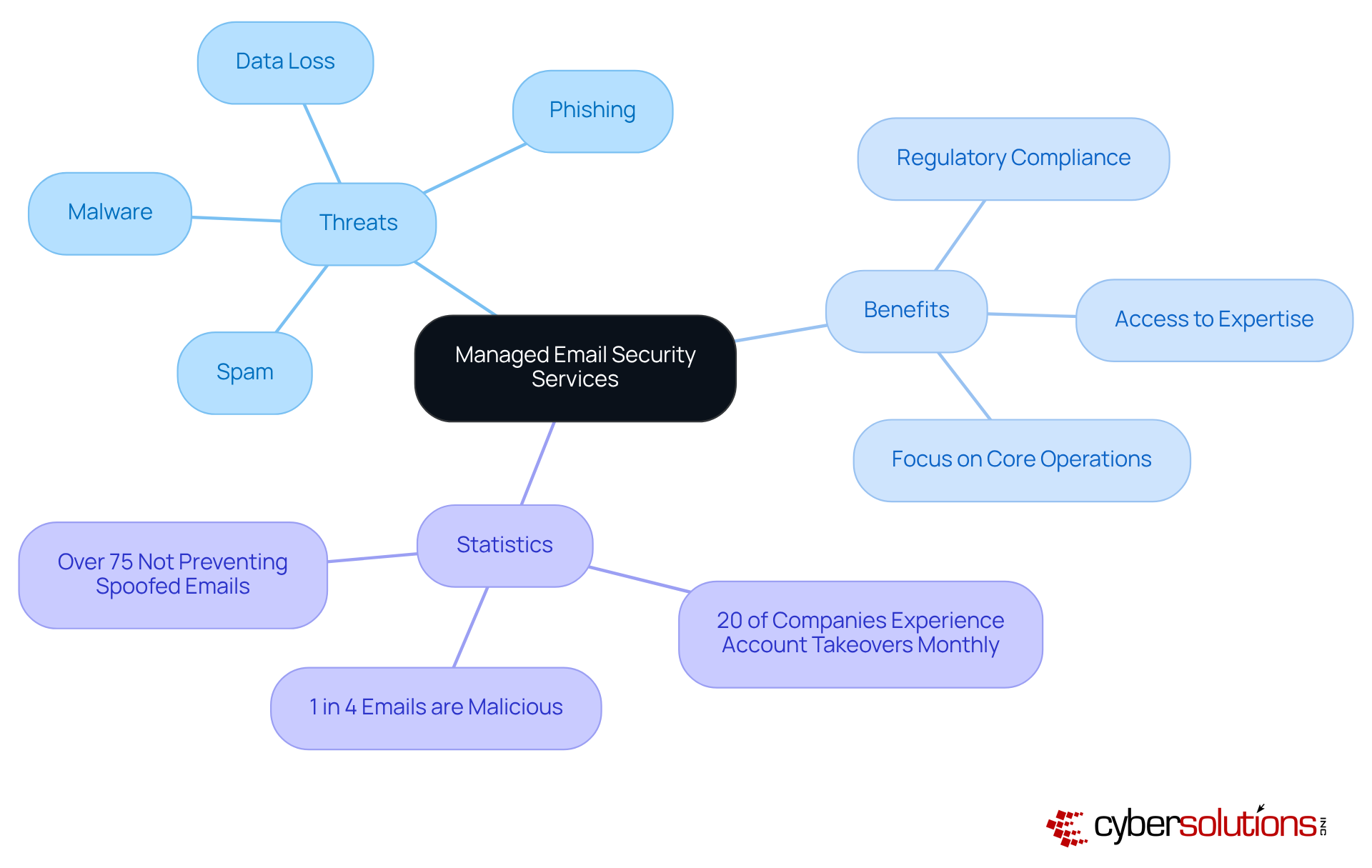
In today’s digital landscape, where communication drives organizational success, the security of email systems stands as a paramount concern. Managed email security services present a powerful solution, equipping businesses to effectively tackle threats such as:
- Phishing
- Malware
- Data breaches
All while adhering to stringent compliance regulations. Yet, as cyber threats continue to evolve, how can organizations ensure they are leveraging these services effectively? This article explores best practices that not only bolster email security but also empower organizations to adeptly navigate the complexities of modern communication risks.
Define Managed Email Security Services
In today's digital landscape, email security is not just important - it's essential. Managed email security services offer external solutions designed to shield organizations from a myriad of risks, including spam, malware, phishing, and data breaches. By outsourcing these critical protections, companies gain access to expert resources, significantly enhancing their defenses against ever-evolving communication threats.
This strategic approach not only improves security but also ensures compliance. For instance, starting in 2026, organizations that fail to implement DMARC policies risk having their messages relegated to spam folders. This underscores the necessity of proactive measures. Moreover, consider this: statistics reveal that 20% of companies experience at least one account takeover each month. This alarming figure highlights the urgent need for robust security protocols.
By leveraging managed email security services, organizations can mitigate risks while ensuring a strong defense posture. This ultimately fosters trust in their interactions, ensuring that they remain resilient in the face of potential threats.
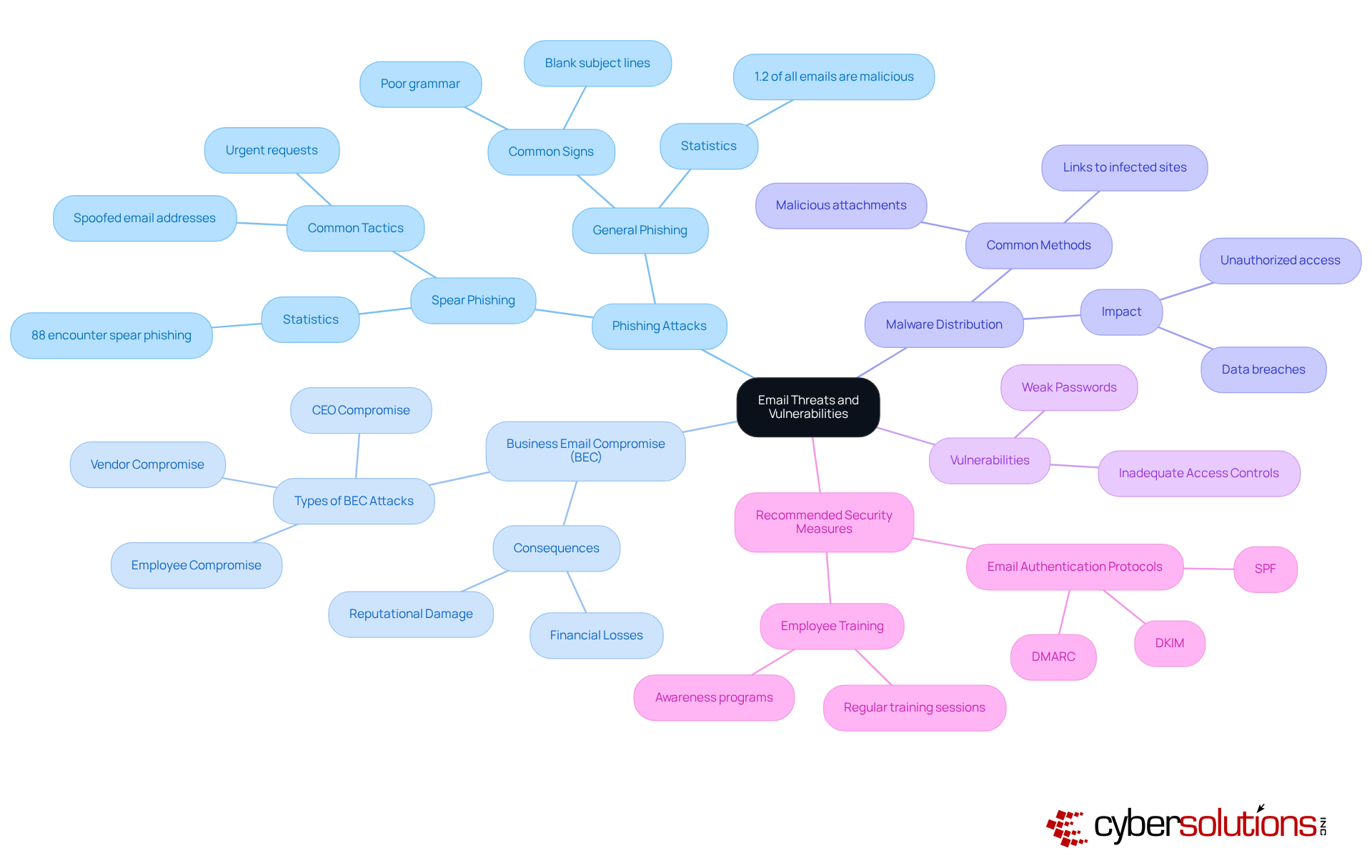
Identify Key Email Threats and Vulnerabilities
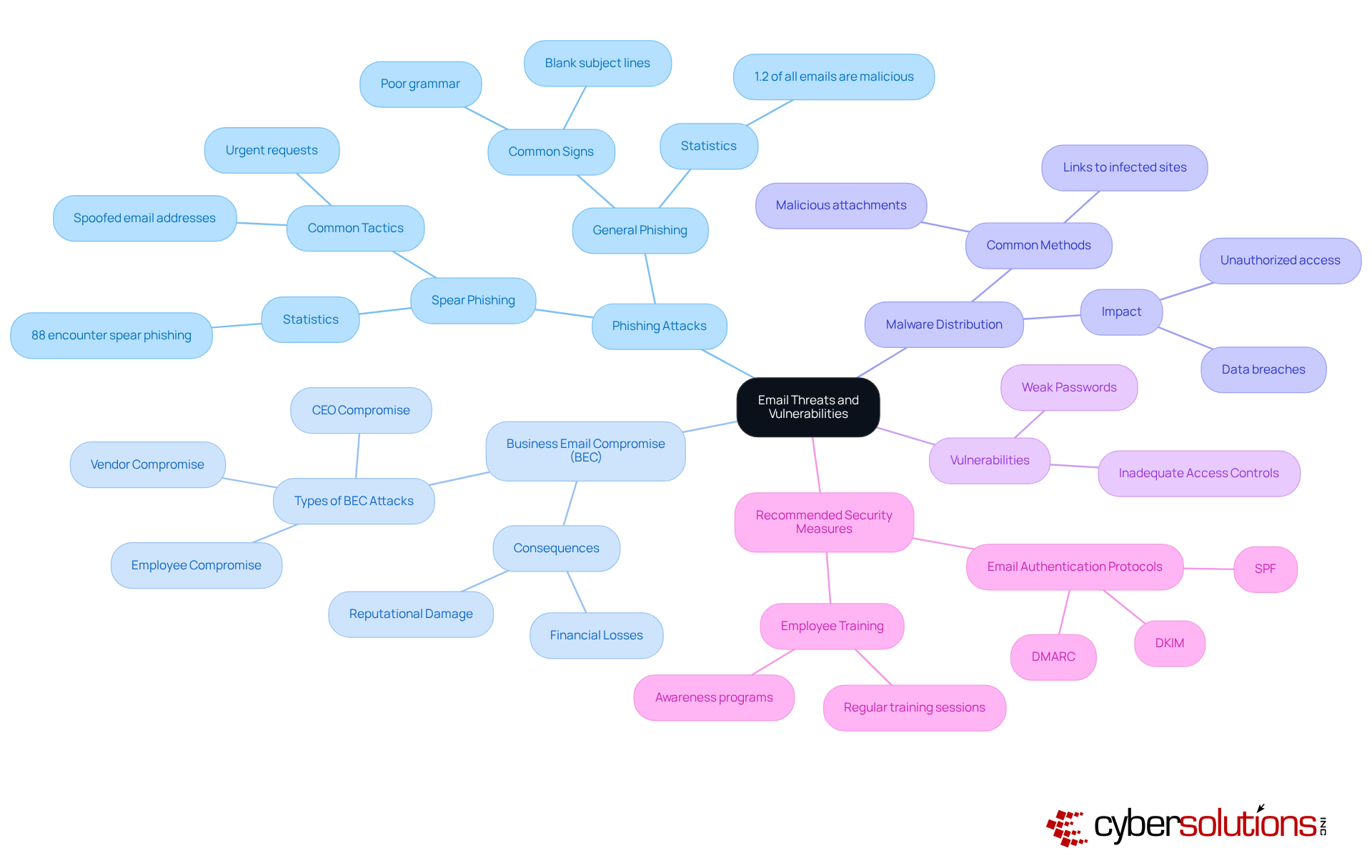
Organizations today face a myriad of threats that threaten their operational integrity and security. Phishing attacks are a significant concern, tricking users into revealing sensitive information through communications that appear legitimate. Another critical threat is business email compromise, where attackers impersonate trusted executives to authorize fraudulent transactions, resulting in substantial financial losses. In fact, BEC schemes have cost U.S. businesses billions of dollars in recent years, underscoring the urgent need for vigilance and proactive measures.
Moreover, the distribution of malware through malicious attachments or links complicates the landscape of communication protection, potentially leading to unauthorized access and data breaches. Vulnerabilities such as weak passwords and inadequate access controls exacerbate these risks, making organizations more susceptible to attacks. Alarmingly, statistics reveal that 88% of entities encounter spear phishing each year, highlighting the necessity for robust communication security strategies.
To effectively combat these risks, organizations must adopt security measures that include protocols like DMARC, SPF, and DKIM. These protocols help identify and block spoofing attempts. Additionally, cultivating a culture of awareness through regular training can significantly diminish susceptibility to attacks. As such, understanding the threats and the implications of BEC is essential for developing effective defenses, including employee education, to safeguard sensitive information.
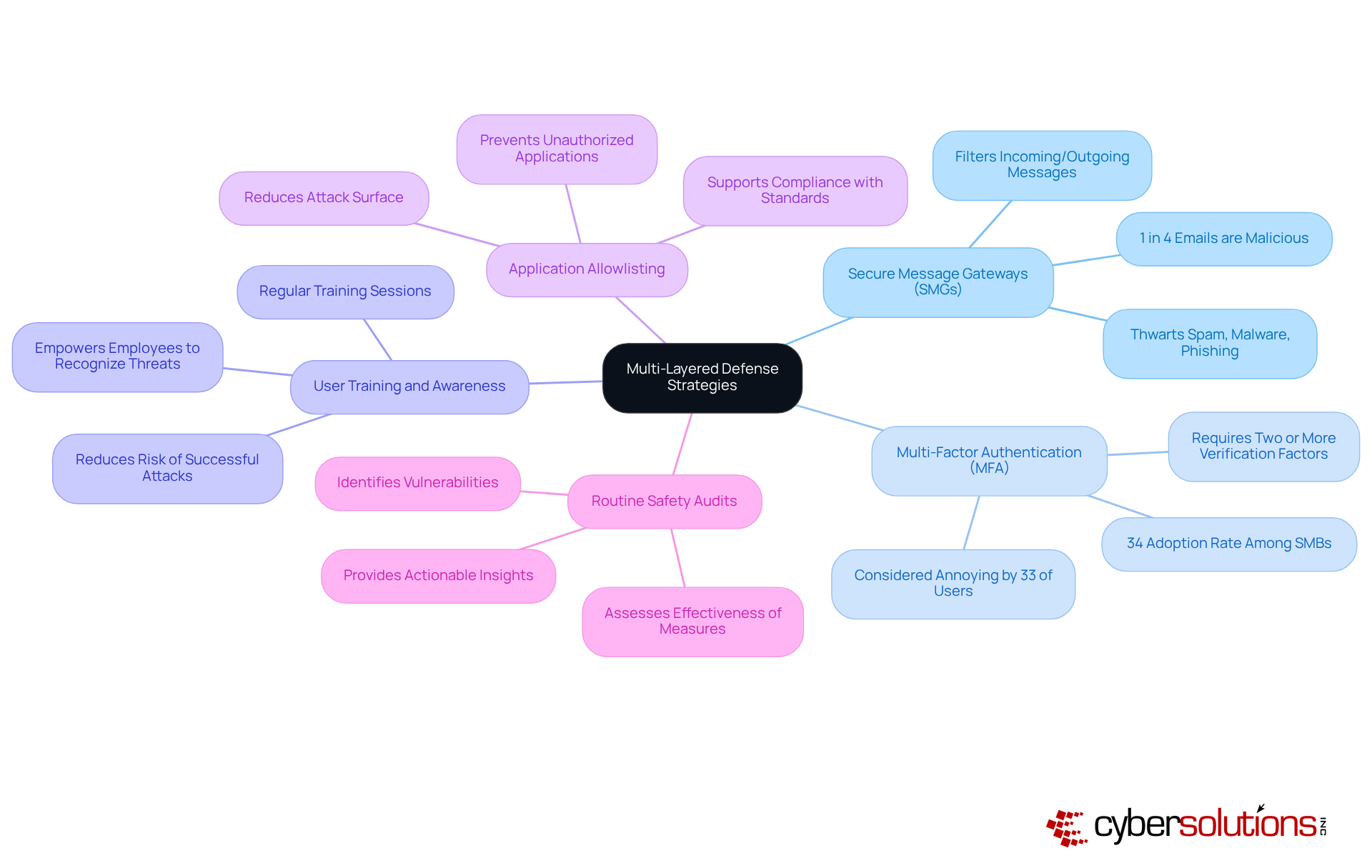
Implement Multi-Layered Defense Strategies
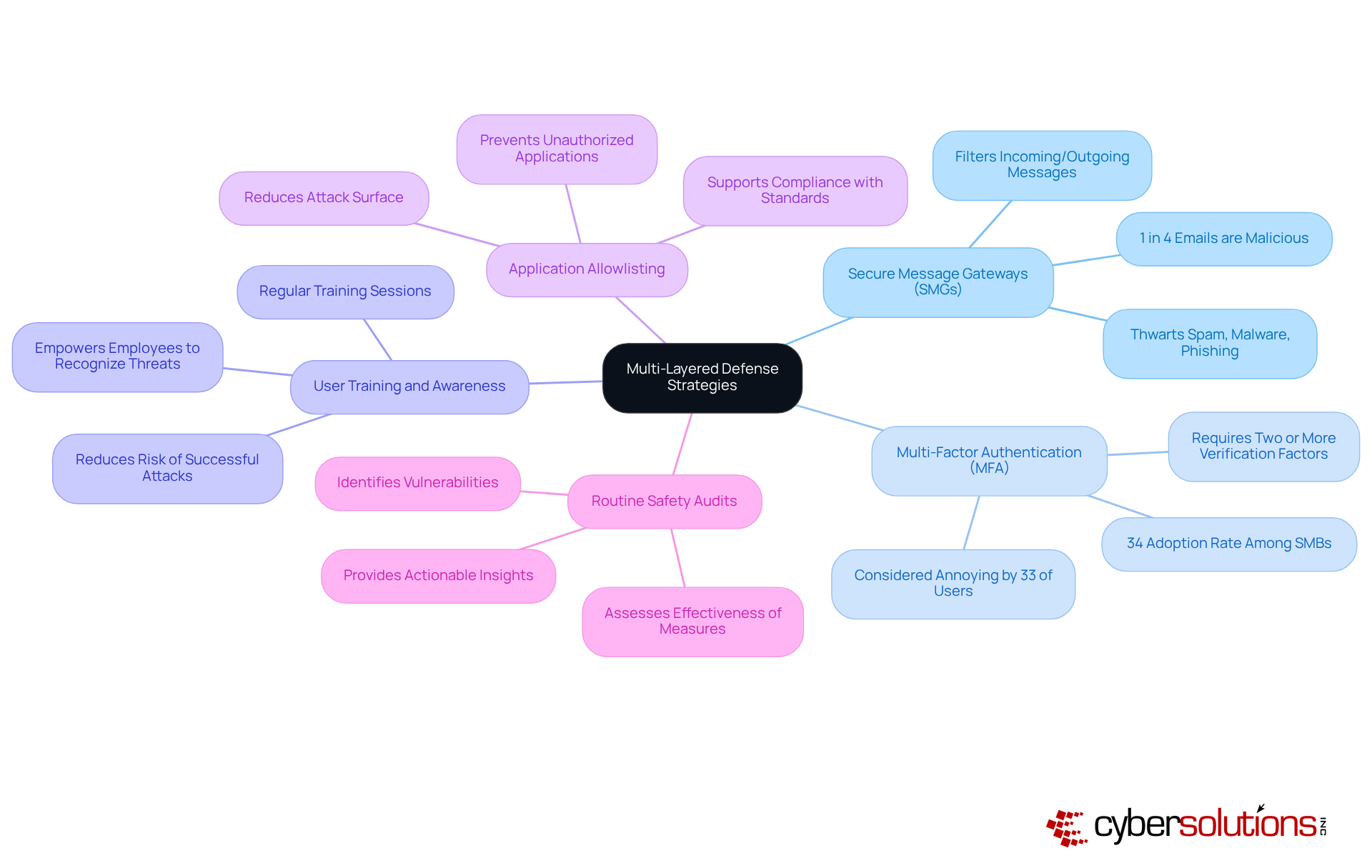
A robust defense strategy is vital for safeguarding communication systems against the ever-evolving landscape of cybersecurity threats. As organizations face increasing risks, understanding and implementing key components of this strategy is essential.
- Security Management Gateways serve as the first line of defense, filtering both incoming and outgoing messages to thwart spam, malware, and phishing attempts. With proper configuration, the deployment of SMGs is crucial for maintaining a secure email environment. Are you prepared to protect your organization from these threats?
- Multi-Factor Authentication significantly bolsters security by requiring users to provide two or more verification factors. Despite its proven effectiveness, only 34% of small to medium-sized businesses had implemented MFA as of 2026. This statistic underscores the urgent need for organizations to adopt measures to defend against unauthorized access.
- Employee training is another critical element. Regular training sessions empower employees to recognize phishing attempts and other email dangers, reducing the likelihood of successful attacks. Organizations that invest in awareness training can significantly reduce the risk of successful attacks by equipping their workforce with the knowledge to identify potential threats.
- Application whitelisting is a proactive measure that prevents unauthorized or malicious applications from executing on systems. By ensuring that only pre-approved and trusted software can run, organizations can greatly reduce their attack surface and minimize vulnerabilities. Continuous monitoring of application activity and centralized control of allowlists enhance protection, enabling swift identification and blocking of threats. Additionally, application whitelisting aids in meeting compliance requirements for standards such as GDPR, ensuring adherence to stringent data protection protocols.
- Security audits are essential for identifying vulnerabilities and assessing the effectiveness of existing measures. These audits provide actionable insights, allowing organizations to make timely adjustments to their security posture.
By integrating these strategies, organizations can establish a formidable framework for managing email security services, which significantly lowers the likelihood of successful attacks and ensures a secure operational environment. Furthermore, implementing email authentication is crucial for preventing message spoofing, thereby enhancing the overall protection strategy.
Choose the Right Managed Email Security Provider
Selecting the right managed email security provider is crucial for safeguarding your organization against emerging risks. In today’s landscape, where cyber threats are increasingly sophisticated, understanding the key factors in this selection process is essential.
- Detection Capabilities: First and foremost, assess the provider's expertise in recognizing and addressing various threats, especially phishing attacks. With email being the primary attack vector for cybercriminals, effective detection is paramount. Did you know that 90% of cyberattacks start with an email? This statistic underscores the urgent need for robust email security measures.
- Customization Options: Next, seek providers that offer tailored solutions to meet your organization's unique requirements, including integration with existing systems. Customization aligned with specific operational needs significantly enhances overall effectiveness.
- Reputation and Experience: Investigate the provider's history and client testimonials to gauge their reliability and effectiveness. A solid reputation often correlates with demonstrated success in managing email security. For instance, Mimecast safeguards over 40,000 entities globally, utilizing advanced threat intelligence. This showcases their capability to manage complex email environments.
- Support and Training: Ensure that the provider offers comprehensive support and training. This is vital for empowering your team to effectively utilize the security solutions. Consistent training and simulated phishing exercises can greatly enhance employees' ability to identify and report suspicious messages, thereby reinforcing the company's defensive posture.
- Current Reporting and Policy Modifications: Finally, regular reporting and policy modifications are essential for adapting to evolving threats. Regular assessments of DMARC reports and danger-detection logs enable organizations to adjust policies in line with the changing risk landscape, ultimately improving message protection efficiency.
By carefully evaluating these factors, organizations can select a provider that not only strengthens their security strategy but also adapts to the dynamic landscape of email threats.

Conclusion
Safeguarding communication systems through managed email security services is not just a choice; it’s a fundamental necessity for organizations aiming to protect sensitive information and uphold operational integrity. In today’s landscape, where cyber threats are constantly evolving, understanding the various vulnerabilities is crucial. By implementing effective strategies, organizations can significantly bolster their defenses against these threats.
Critical practices for achieving success in managed email security services include:
- Identifying key email threats such as phishing and Business Email Compromise
- Implementing multi-layered defense strategies
- Selecting the right provider
Each of these components is vital in establishing a robust security framework that not only mitigates risks but also fosters a culture of awareness and proactive defense among employees.
The significance of adopting managed email security services cannot be overstated. Organizations must prioritize these practices to safeguard their communications and sensitive data. By staying informed about current threats and continuously adapting their security measures, businesses can build resilience against cybercriminals and ensure a secure operational environment. Embracing these best practices is an investment in long-term security and trust, essential for thriving in today’s digital landscape.
Frequently Asked Questions
What are managed email security services?
Managed email security services are external solutions designed to protect organizations from risks such as spam, malware, phishing, and data loss by outsourcing email security protections.
Why is it important to use managed email security services?
It is essential to use managed email security services to enhance defenses against communication threats, comply with industry regulations, and protect against risks like account takeovers.
What risks do managed email security services help mitigate?
They help mitigate risks including spam, malware, phishing attacks, and data loss.
How do managed email security services benefit organizations?
By outsourcing email security, organizations gain access to specialized expertise and advanced technologies, allowing them to focus on their core operations while ensuring a strong defense posture.
What is the significance of DMARC policies in email security?
Starting in 2026, organizations that do not implement DMARC policies may have their messages sent to spam folders, highlighting the need for robust email authentication measures.
What statistics emphasize the need for email security?
Statistics show that 20% of companies experience at least one account takeover each month, underscoring the urgent need for effective email protection solutions.
List of Sources
- Define Managed Email Security Services
- Email Security in 2026: Stopping Phishing Before It Reaches Your Inbox (https://sunitsolutions.ca/email-security-in-2026-stopping-phishing-before-it-reaches-your-inbox)
- Email Security Trends in 2025 and Preparing for 2026 - Dynamic Business Solutions (https://dynamicbusiness.net/email-security-trends-in-2025-and-preparing-for-2026)
- Why Do We Need Email Security? - Guardian Digital (https://guardiandigital.com/resources/faq/why-do-we-need-email-security)
- Trends in Business Email Security for 2026 — 5 Practical Shifts (https://bigrock.in/blog/products/email/trends-in-business-email-security)
- Email Security Predictions 2026: What To Expect (https://powerdmarc.com/email-security-predictions-2026)
- Identify Key Email Threats and Vulnerabilities
- varonis.com (https://varonis.com/blog/2026-cybercrime-trends)
- Recognizing Business Email Compromise (BEC) scams (https://commercebank.com/business/trends-and-insights/2025/recognizing-business-email-compromise-scams)
- Business Email Compromise Persists as Actors Refine Tactics (https://bankinfosecurity.com/business-email-compromise-persists-as-actors-refine-tactics-a-30020)
- Understanding Business Email Compromise (BEC): A Growing Cybersecurity Threat - CatchMark Technologies (https://catchmarkit.com/understanding-business-email-compromise-bec-a-growing-cybersecurity-threat)
- getastra.com (https://getastra.com/blog/security-audit/phishing-attack-statistics)
- Implement Multi-Layered Defense Strategies
- Email Security Trends in 2025 and Preparing for 2026 - Dynamic Business Solutions (https://dynamicbusiness.net/email-security-trends-in-2025-and-preparing-for-2026)
- Email Security Predictions 2026: What To Expect (https://powerdmarc.com/email-security-predictions-2026)
- Top email phishing scams SMBs can expect in 2026, and what to do about them (https://integrisit.com/blog/email-phishing-scams-2026)
- Multi-Factor Authentication (MFA) Statistics You Need To Know In 2025 | Dental Technologies (https://njda.org/news-information/news-archive/2025/11/25/multi-factor-authentication-(mfa)-statistics-you-need-to-know-in-2025---dental-technologies)
- 105% Increase in Malicious Emails Bypassing SEGs | Cofense (https://cofense.com/blog/cofense-annual-report-indicates-105-increase-in-malicious-emails-bypassing-segs)
- Choose the Right Managed Email Security Provider
- 33 Phishing Statistics in 2025 Every MSP Should Know About | Guardz.com (https://guardz.com/blog/33-phishing-statistics-every-msp-should-know-about)
- 2025 Email Threats Report (https://barracuda.com/reports/2025-email-threats-report)
- Top 10 Enterprise Email Security Solutions For 2026 (https://powerdmarc.com/enterprise-email-security-solutions)
- Email Security Trends and Statistics in 2025 (https://titanhq.com/email-security-2025/state-email-security-report-2025)
- Top Email Security Solutions 2026: Best Email Security Compared (https://expertinsights.com/email-security/top-email-security-gateways)