
In today's world, where data breaches and natural disasters are ever-present threats to organizations, the importance of disaster recovery storage is paramount. This essential element of business continuity not only safeguards vital information but also ensures that it can be quickly restored, significantly reducing downtime and operational disruption.
But how can organizations effectively implement best practices to strengthen their disaster recovery strategies? By examining key techniques and compliance considerations, this article explores the strategies that empower businesses to protect their data and maintain resilience in the face of adversity.
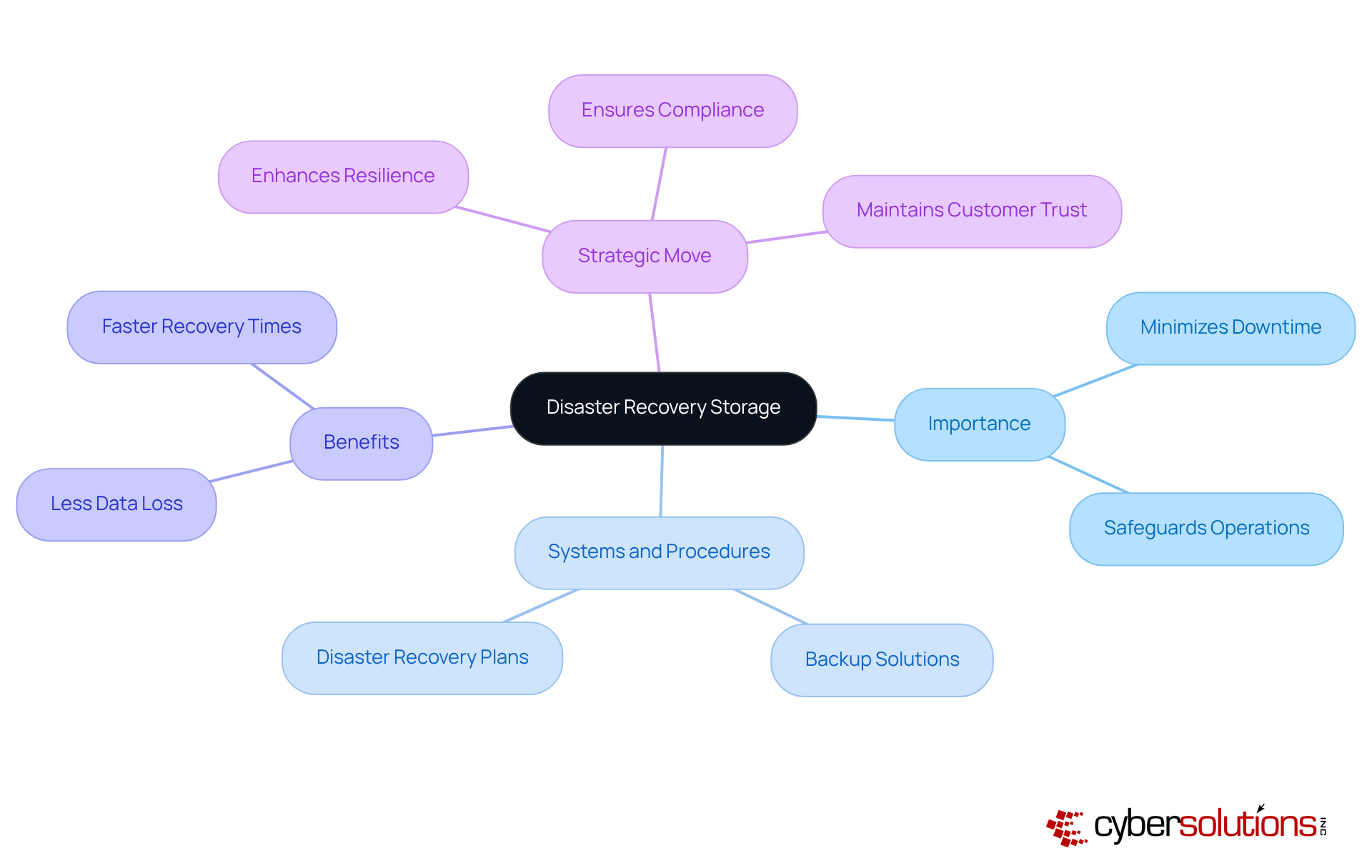
is crucial for any organization, especially in today's unpredictable landscape. It encompasses the systems and procedures used to back up and restore information during emergencies, such as floods, natural disasters, or hardware failures. The importance of this cannot be overstated; it ensures that vital information is preserved and can be swiftly restored, thereby minimizing downtime and operational disruption.
According to the 2025 State of Backup and Restoration Report, organizations with effective disaster recovery plans experience significantly less downtime. This not only safeguards their operations but also directly influences their profit margins. By investing in disaster recovery storage solutions, companies enhance their resilience against unforeseen events, ensuring business continuity and maintaining customer trust.
In a world where data breaches and disasters are increasingly common, the question arises: can your organization afford to overlook disaster recovery? Prioritizing this aspect of your operations is not just a safeguard; it's a critical measure against potential threats. Don't wait for a crisis to highlight the gaps in your strategy - take action now to secure your organization's future.
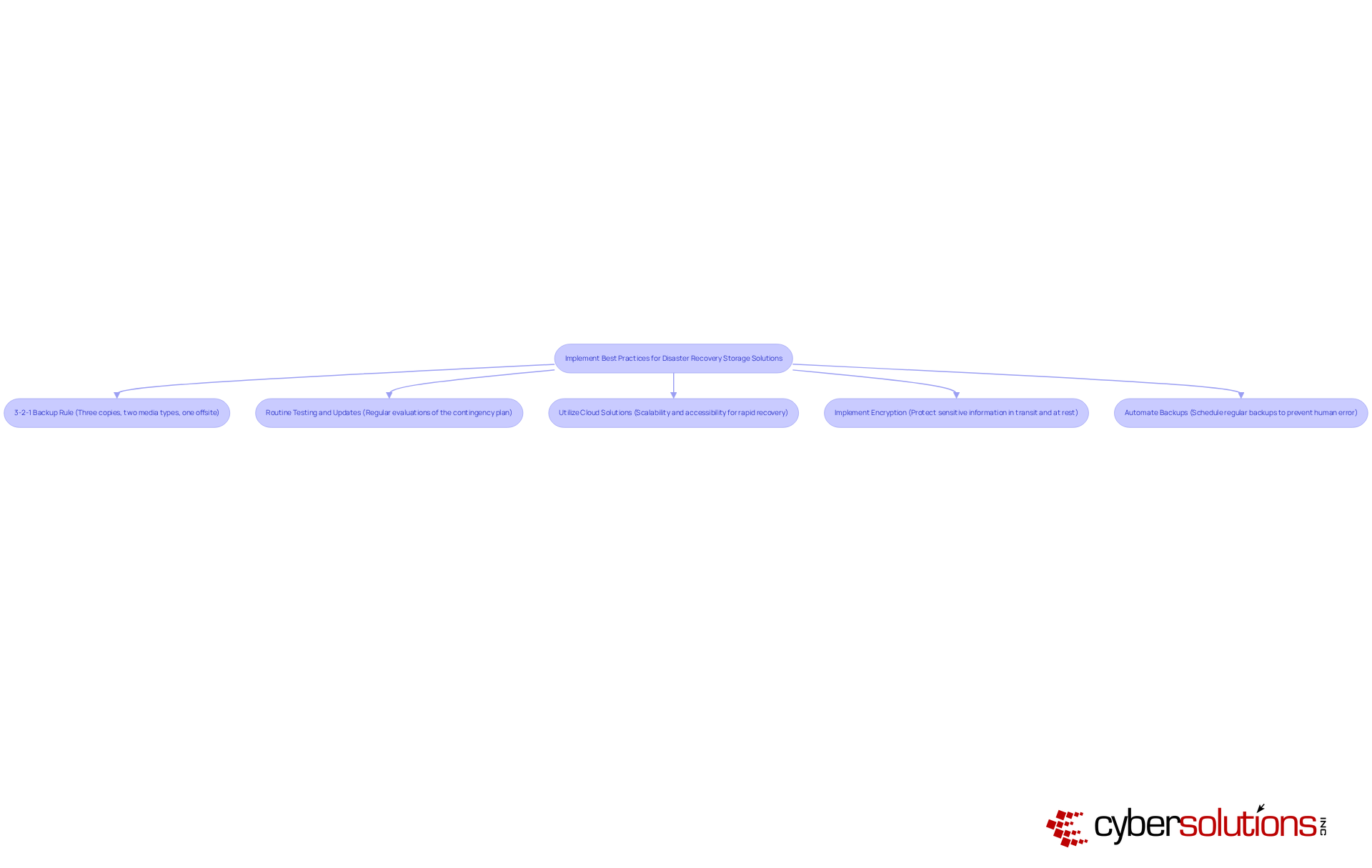
To implement effective disaster recovery storage solutions, organizations must prioritize strategies that safeguard their data and ensure business continuity.
By adhering to these best practices, companies can significantly enhance their disaster recovery strategies, equipping themselves to handle any contingency with confidence.
Ensuring adherence to regulatory standards is not just important - it's essential for organizations, particularly those in highly regulated sectors like healthcare and finance. The stakes are high, and understanding the landscape of compliance can make all the difference. Here are some critical considerations:
By prioritizing compliance, organizations not only protect their data but also enhance their reputation and trustworthiness among clients and stakeholders. Are you ready to take the necessary steps to safeguard your organization?

Disaster recovery storage stands as a cornerstone for organizations determined to protect their critical data from unforeseen threats. In today’s unpredictable landscape, prioritizing effective strategies in this domain is not just beneficial; it’s essential for ensuring operational resilience and continuity. By minimizing downtime and potential losses, businesses can safeguard their future. Recognizing the significance of robust disaster recovery storage solutions transcends mere operational necessity; it emerges as a strategic imperative that can define a company’s ability to thrive amidst challenges.
Key practices such as the following are vital in fortifying disaster recovery strategies:
Compliance with regulatory standards not only protects data but also maintains trust and credibility with stakeholders. Each of these elements contributes to a comprehensive approach that enhances organizational preparedness and responsiveness to crises.
Ultimately, organizations must grasp that effective disaster recovery storage is not merely about having a plan; it’s about actively engaging in continuous improvement and compliance. As the landscape of threats evolves, so too must the strategies employed to counter them. Are you ready to take proactive steps? Implementing and refining disaster recovery practices now will not only secure valuable data but also position organizations to navigate the complexities of the future with confidence.
What is disaster recovery storage?
Disaster recovery storage refers to the systems and procedures used to back up and restore information during emergencies, such as cyberattacks, natural disasters, or hardware failures.
Why is disaster recovery storage important for organizations?
Disaster recovery storage is important because it ensures that vital information is preserved and can be swiftly restored, minimizing downtime and operational disruption during emergencies.
How does effective disaster recovery storage impact data loss and recovery times?
Organizations with robust emergency response solutions experience significantly less data loss and faster recovery times, which safeguards operations and positively influences profit margins.
What are the benefits of investing in crisis management storage?
Investing in crisis management storage enhances an organization's resilience against unforeseen events, ensures compliance with industry regulations, and helps maintain customer trust.
What risks do organizations face if they overlook disaster recovery storage?
Organizations that overlook disaster recovery storage may face increased data loss, longer recovery times, and operational disruptions, which can jeopardize their business continuity and reputation.
What should organizations do to prepare for potential data breaches or disasters?
Organizations should prioritize disaster recovery storage as a strategic move to fortify their business against potential threats and take proactive measures to secure their data protection strategies.