
The rise of public charging stations has undeniably made it easier for individuals to power their devices on the go. However, this convenience comes with hidden dangers that cannot be overlooked. Juice jacking - a term that describes the malicious exploitation of public USB ports to steal data or install malware - poses a significant threat to both personal and organizational cybersecurity. As these attacks become more frequent, it raises an important question: how can businesses and individuals protect themselves from this insidious risk while navigating the ever-expanding digital landscape?
Understanding the current landscape of cybersecurity threats is crucial. Juice jacking is not just a theoretical concern; it has real implications for anyone who relies on public charging stations. The potential for data theft and malware installation can lead to devastating consequences, both personally and professionally.
To combat these challenges, it’s essential to adopt proactive measures. Cyber Solutions can provide the necessary tools and strategies to safeguard against such threats, ensuring that users can charge their devices without compromising their security. By staying informed and vigilant, individuals and organizations can navigate this digital landscape with confidence.
The section highlights a significant threat that arises when devices are charged through public outlets, which facilitate both power and data transfer. This dual functionality can be exploited by cybercriminals who set up charging stations, allowing them to either extract sensitive information from connected devices or install malware. The danger is particularly acute in high-traffic areas such as airports, cafes, and hotels, where users frequently depend on public charging options.
Recent warnings from the FBI and FCC underscore these risks, advising against the use of public power stations due to the increasing availability of attack tools. Alarmingly, statistics reveal that 28% of businesses have encountered attacks involving compromised or stolen devices, highlighting the urgency of cybersecurity measures, including the need for employee training. Moreover, a successful attack can occur in mere seconds, making even brief charging sessions risky.
Organizations must recognize that while public charging options are convenient, they also come with inherent vulnerabilities. This reality necessitates proactive measures to safeguard data and ensure device security. By understanding the dangers associated with charging devices at public locations, companies can better protect their operations against these evolving threats.

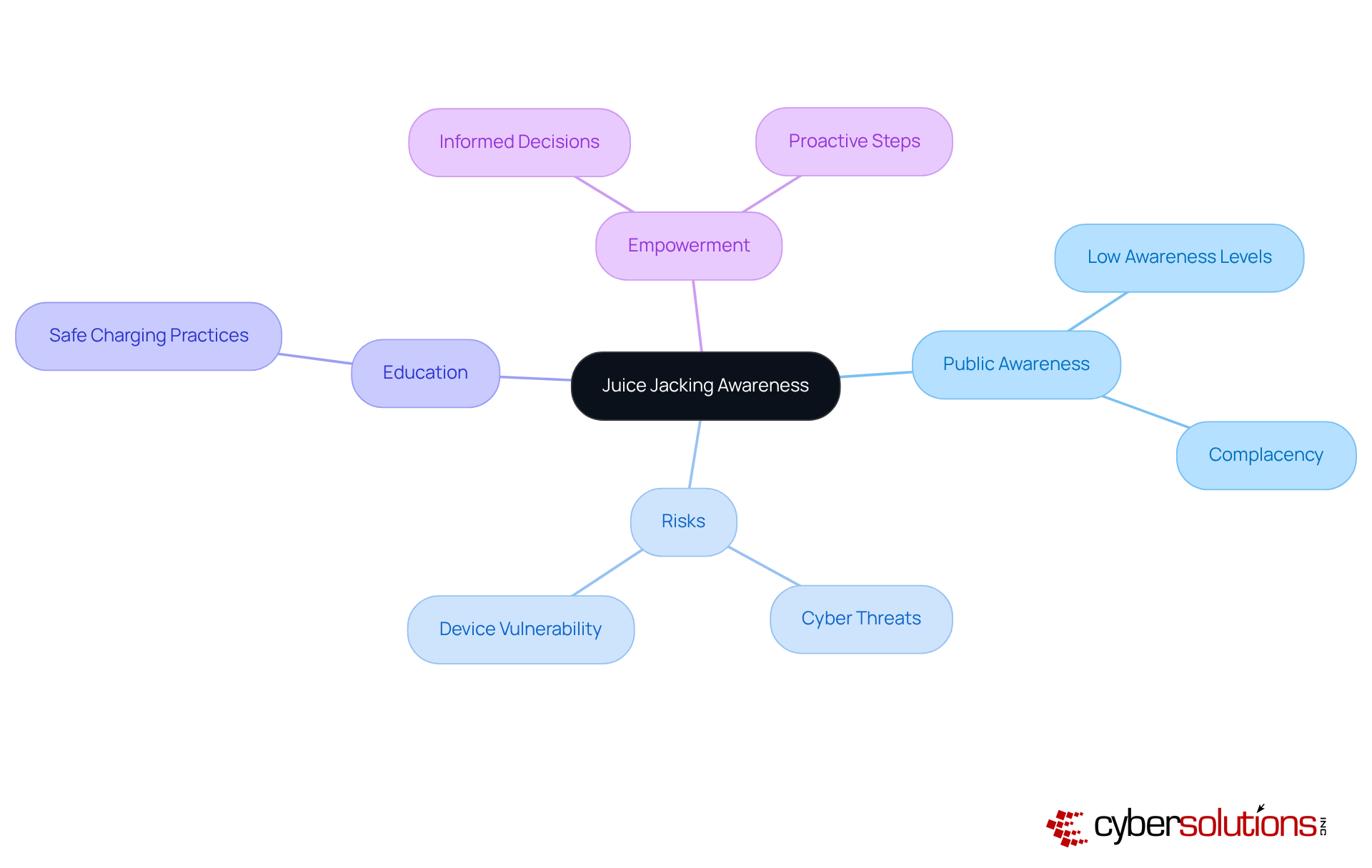
Public awareness of juice jacking is alarmingly low, despite its increasing prevalence. Many individuals remain unaware that charging their devices in public places can expose them to threats. This lack of awareness can foster complacency, leaving both individuals and organizations vulnerable to attacks. As society grows more dependent on mobile devices, the urgency for education on juice jacking cannot be overstated.
Campaigns designed to raise awareness about the risks can empower users to make informed decisions. By understanding the risks, individuals can take proactive steps to protect their data and personal information. Ultimately, fostering a culture that is vigilant is essential. Are you prepared to safeguard your devices against potential threats?
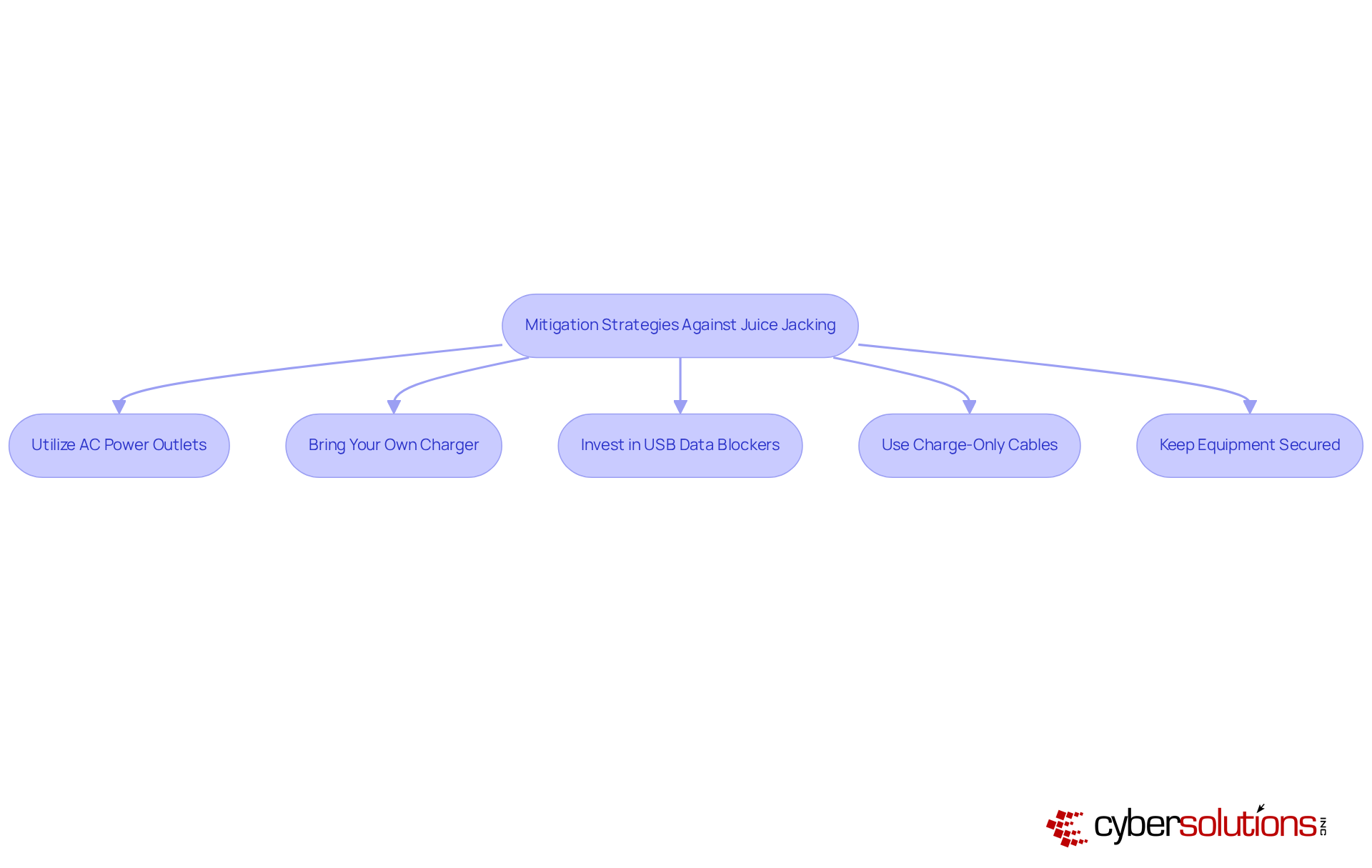
To effectively guard against juice jacking, it’s crucial to implement several essential strategies that can safeguard your devices and data.
The term juice jacking refers to the act of stealing data through compromised charging stations. Educate Employees: For organizations, training staff on the risks and the signs of juice jacking, as well as the importance of safe charging practices, is vital. Regular training sessions can enhance awareness and foster a culture of cybersecurity. As Sharkirah Foote, an Information Security Manager, emphasizes, "By developing good cyber safety habits and remaining vigilant, we can collectively keep both personal and university data better protected, no matter the threat."
By adopting these practices, businesses can significantly reduce the risks and protect against potential threats.
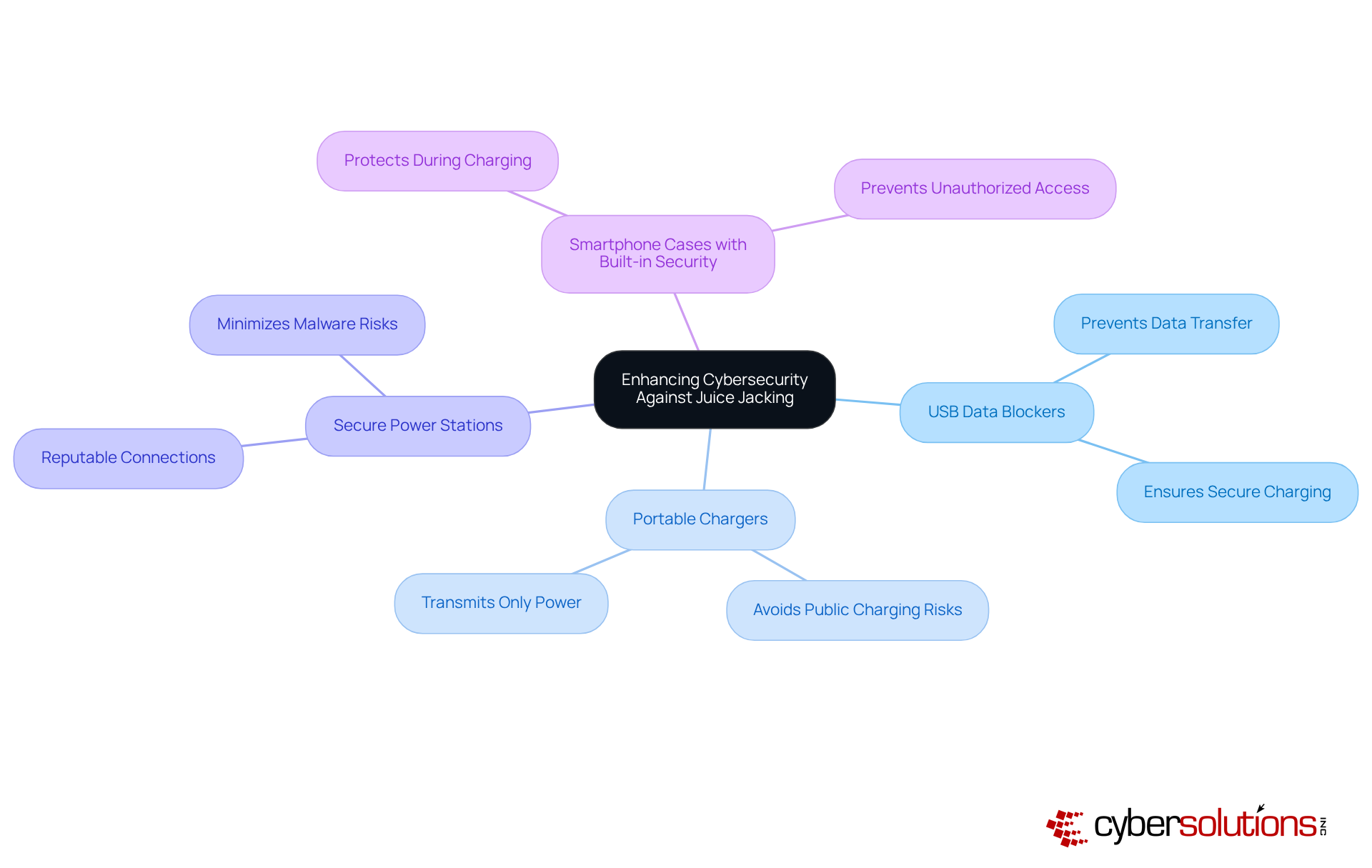
Enhancing Cybersecurity Against Juice Jacking
In today's digital landscape, safeguarding against threats like juice jacking is paramount for any organization. Hardware solutions play a crucial role in fortifying defenses. Consider these effective options:
Investing in these hardware solutions not only mitigates the risks associated with juice jacking but also strengthens your overall cybersecurity posture. By taking proactive measures, businesses can enhance their defenses and protect sensitive information.
Understanding the significance of juice jacking is crucial for anyone who frequently uses public charging stations. This cybersecurity threat, which entails unauthorized access and data theft through compromised USB ports, presents serious risks to both individuals and organizations. Recognizing the dual functionality of these ports is the first step in safeguarding sensitive information and maintaining data integrity.
The alarming rise in juice jacking incidents underscores the urgent need for public awareness. Did you know that many users remain unaware of the dangers lurking in seemingly innocuous charging stations? Strategies such as:
are essential in mitigating these risks. Moreover, fostering a culture of cybersecurity awareness within organizations through employee education can significantly enhance protective measures against juice jacking threats.
Ultimately, the importance of understanding and addressing juice jacking cannot be overstated. As our society increasingly embraces mobile technology, taking proactive steps to protect devices from potential threats is imperative. By implementing the recommended practices and encouraging awareness, individuals and businesses can significantly reduce their vulnerability to juice jacking, ensuring a safer digital environment for all.
What is juice jacking?
Juice jacking is a cybersecurity threat that occurs when devices are charged through public USB ports, which can facilitate both power and data transfer. Cybercriminals can exploit this by setting up compromised charging stations to extract sensitive information or install malware on connected devices.
Where are the risks of juice jacking most prevalent?
The risks of juice jacking are particularly acute in high-traffic areas such as airports, cafes, and hotels, where users often rely on public charging options.
What do recent warnings from authorities say about public charging stations?
Recent warnings from the FBI and FCC advise against using public power stations due to the increasing availability of attack tools that can be used for juice jacking.
How common are attacks related to juice jacking?
Statistics indicate that 28% of businesses have encountered attacks involving compromised or stolen devices, highlighting the importance of being vigilant against threats like juice jacking.
How quickly can a juice jacking attack occur?
A successful juice jacking attack can occur in mere seconds, making even brief charging sessions potentially risky.
What should organizations do to protect against juice jacking?
Organizations must recognize the vulnerabilities of public power sources and implement robust cybersecurity measures to safeguard sensitive data and ensure compliance. Understanding the dangers associated with charging devices at public USB ports is essential for better protection against these threats.