In today's world, where data breaches and cyber threats loom larger than ever, effective password management stands as a cornerstone of cybersecurity. The NIST guidelines for passwords, particularly those detailed in Special Publication 800-63B, offer vital insights into crafting secure yet user-friendly authentication practices. By emphasizing password length over complexity and promoting the use of passphrases, these guidelines not only challenge traditional security notions but also enhance the user experience.
How can organizations harness these evolving standards to safeguard sensitive information while streamlining their security processes? This question is crucial as the landscape of cybersecurity continues to evolve, presenting unique challenges that demand innovative solutions. By adopting these best practices, organizations can not only bolster their defenses but also foster a culture of security awareness among users.
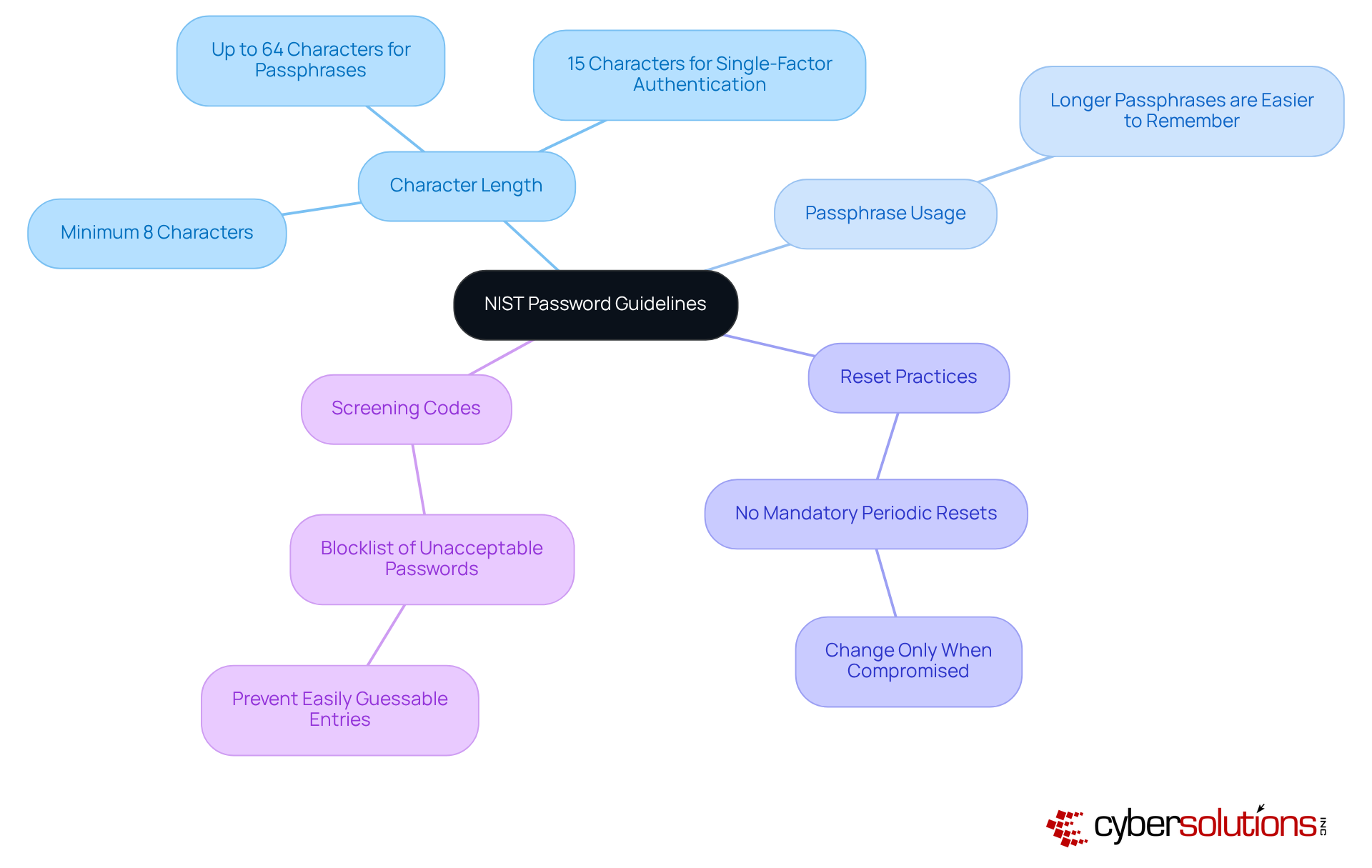
In today's digital age, the importance of password security cannot be overstated. The guidelines, outlined in Special Publication 800-63B, provide a strong framework for password management that enhances both security and user experience. These guidelines emphasize password key length over complexity, recommending:
This shift acknowledges that longer passphrases are not only more secure but also easier for individuals to remember.
Moreover, the guidelines advocate for the discontinuation of password rotation. Instead, changes should only be made when there is clear evidence of a compromise. This approach not only alleviates frustration for users but also encourages the adoption of more secure practices. Additionally, it recommends checking against a blocklist of unacceptable combinations, effectively preventing the use of easily guessable entries.
By prioritizing accessible strategies and emphasizing the importance of educating individuals on the best practices for password security, organizations can significantly enhance overall security. This proactive stance not only improves security but also fosters a safer digital environment. Are you ready to embrace these best practices and elevate your organization's security posture?
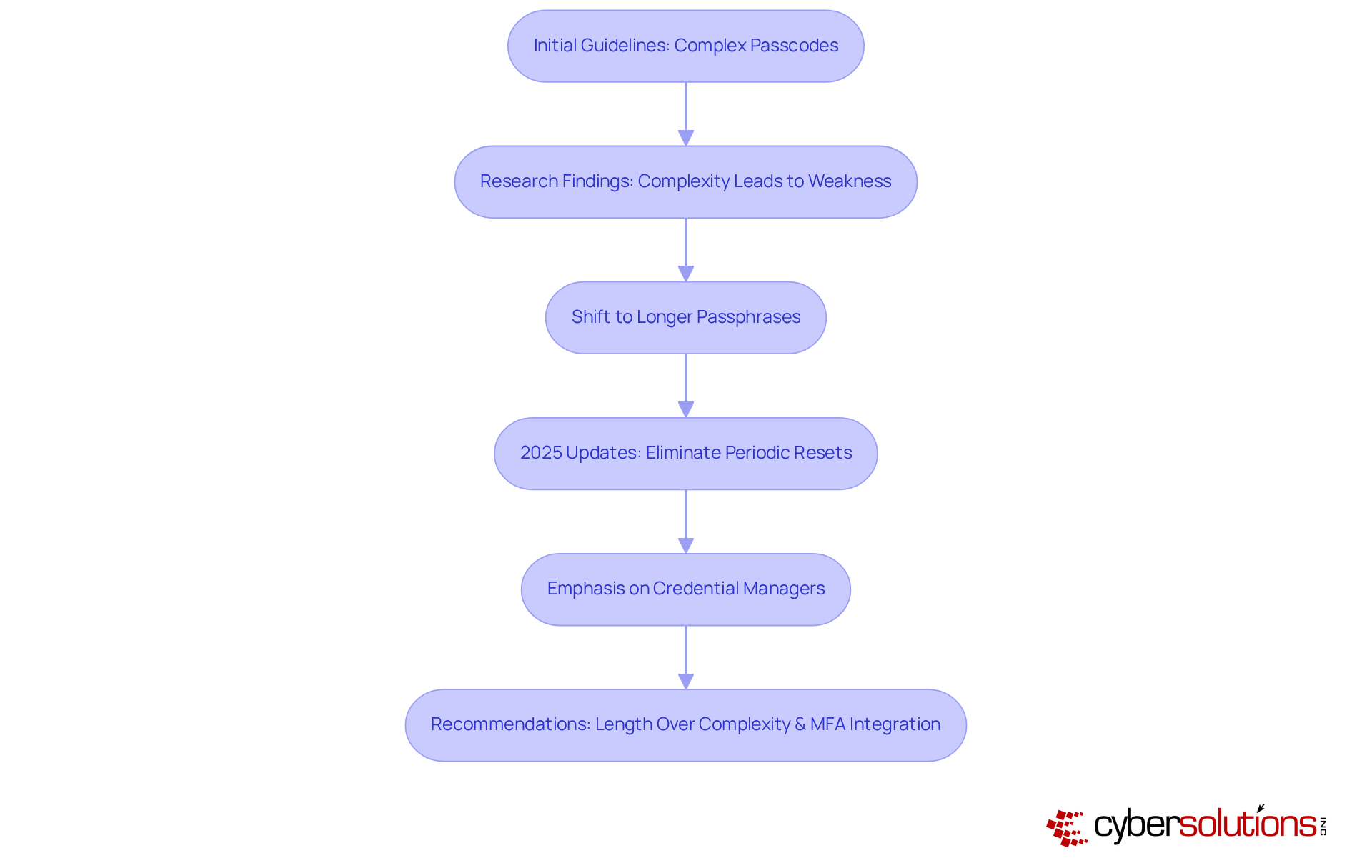
The evolution of the NIST guidelines has been significant to address the ever-changing landscape of cybersecurity and individual behaviors. Initially, these guidelines mandated complex passcodes, combining characters, numbers, and symbols. However, research revealed that such complexity often led to weaker security practices, as individuals resorted to predictable patterns or reused credentials. In response, NIST shifted its focus toward simplicity, in accordance with user preferences, which are not only easier to remember but also more resistant to attacks.
The 2025 updates further simplify these requirements by eliminating mandatory periodic resets and emphasizing the use of password managers. These tools are essential for securely storing and generating strong, unique combinations. This approach not only enhances safety but also aligns with individual behavior, reducing frustration. Organizations adopting these guidelines are witnessing improved compliance and a decrease in security incidents. Studies indicate that supporting Unicode characters results in 43% fewer resets.
By prioritizing length over complexity and recommending the maintenance of a blocklist to prevent weak credentials, the latest recommendations align with best practices, simplifying protection for users while effectively addressing evolving cyber threats. Moreover, the integration of multi-factor authentication is crucial for bolstering security alongside these new access code guidelines. Are you ready to enhance your organization's cybersecurity posture? Embrace these guidelines and fortify your defenses against emerging threats.
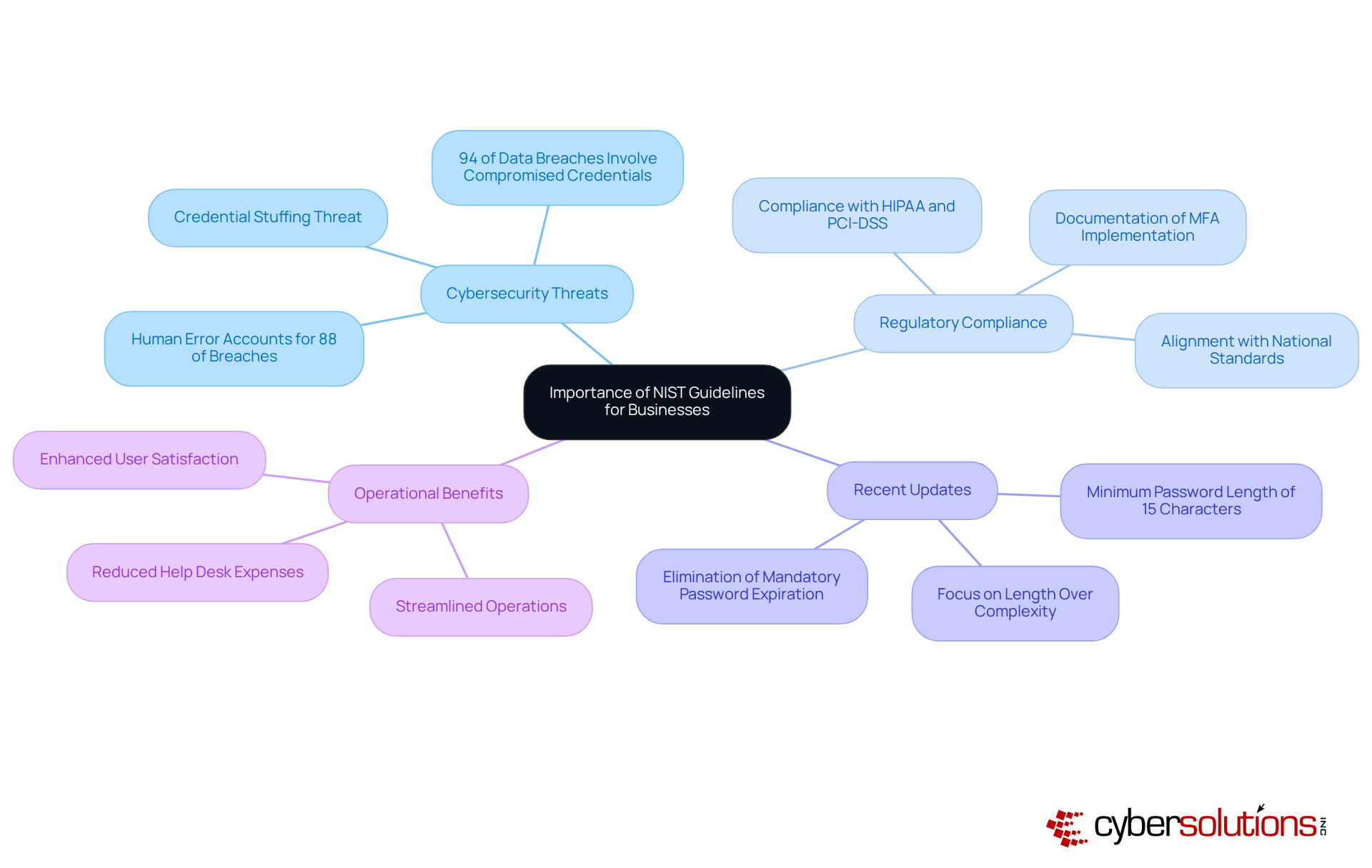
For businesses, adhering to NIST guidelines is not just important; it’s essential for safeguarding against the ever-evolving landscape of cybersecurity threats. Did you know that 94% of data breaches involve compromised credentials? This staggering statistic underscores the necessity of strong password policies. By adopting strong access controls, organizations can significantly mitigate the risk of data breaches and cyberattacks, which can lead to substantial financial losses and reputational damage.
Moreover, compliance with these guidelines is crucial for meeting various regulatory obligations, including GDPR and HIPAA, which mandate strong security measures. The recent updates call for a reduction in password complexity, recommending a minimum of 15 characters for single-factor codes. This shift not only enhances protection but also aligns organizations with national standards, fostering a culture of vigilance.
Organizations that align their security practices with these guidelines often experience enhanced user satisfaction and reduced help desk expenses related to password resets and account lockouts. As the institute aptly states, 'making the credential a component, not the focal point, of authentication' is vital for a secure environment. This alignment streamlines operations and contributes to a more resilient organizational framework, ultimately ensuring that sensitive information remains secure.
In today's digital landscape, cybersecurity is a critical imperative for healthcare organizations. With increasing threats looming over sensitive patient data, CFOs must navigate unique challenges that demand attention. The NIST guidelines offer essential recommendations to bolster security protocols:
By following NIST guidelines for passwords, healthcare organizations can significantly enhance their security posture while also improving user experience. The time to act is now-strengthening cybersecurity is not just about technology; it's about safeguarding the trust of patients and stakeholders alike.

Cybersecurity in healthcare is not just a necessity; it’s a critical imperative. The NIST guidelines for passwords mark a significant shift in how organizations approach this vital aspect of their operations. By prioritizing password length over complexity and promoting user-friendly practices, these guidelines aim to create a more secure and manageable authentication environment. This evolution not only enhances security but also cultivates a culture of compliance and awareness among users.
Key insights throughout the article underscore the importance of adopting robust password practices. Consider the following recommendations:
These strategies are designed to mitigate risks associated with data breaches, which are alarmingly prevalent in today’s digital landscape. Moreover, integrating multi-factor authentication alongside these guidelines adds an essential layer of security that organizations cannot afford to overlook.
Ultimately, embracing the NIST guidelines transcends mere compliance; it’s about safeguarding sensitive information and maintaining the trust of patients and stakeholders. Organizations must implement these best practices to strengthen their defenses against emerging threats, ensuring that cybersecurity remains a top priority in an ever-evolving digital world. Taking proactive steps today can significantly enhance security posture and contribute to a safer, more resilient future.
What are the NIST password guidelines?
The NIST password guidelines, outlined in Special Publication 800-63B, provide a framework for creating and managing passwords that enhances security and user experience.
What is the recommended minimum password length according to NIST?
The NIST guidelines recommend a minimum password length of 8 characters for general use and 15 characters for single-factor authentication.
How long can passphrases be under the NIST guidelines?
Passphrases can be up to 64 characters long according to the NIST guidelines.
Why does NIST emphasize longer passphrases?
NIST emphasizes longer passphrases because they are more secure and easier for individuals to remember.
What does NIST say about mandatory periodic password resets?
NIST recommends discontinuing mandatory periodic password resets, suggesting that changes should only occur when there is clear evidence of a compromise.
How do the NIST guidelines improve user experience?
By eliminating mandatory resets, users experience less frustration and are encouraged to adopt more secure authentication practices.
What is the purpose of screening access codes against a blocklist?
Screening access codes against a blocklist prevents the use of easily guessable entries, enhancing security.
How can organizations enhance overall security according to the NIST guidelines?
Organizations can enhance security by prioritizing accessible strategies and educating individuals on the NIST password guidelines, which reduces the administrative burden of credential management.