
In an age where cyber threats are escalating at an alarming rate, the significance of conducting thorough cybersecurity assessments is paramount. Organizations, especially in the healthcare sector, grapple with numerous vulnerabilities that can jeopardize sensitive information and operational integrity. This article presents a comprehensive, step-by-step guide to mastering cybersecurity assessments, empowering businesses to identify weaknesses, implement robust security measures, and ultimately safeguard their assets. But with so many complexities involved, how can organizations ensure they are not only compliant but also resilient against the ever-evolving landscape of cyber threats?
The current landscape of cybersecurity threats is daunting. Healthcare organizations face unique challenges that require immediate attention. From data breaches to ransomware attacks, the stakes are high, and the implications can be devastating. CFOs must navigate these turbulent waters, balancing compliance with the need for robust security measures.
Cyber Solutions can effectively address these challenges, providing the expertise and tools necessary to fortify defenses. By conducting thorough assessments, organizations can uncover vulnerabilities and take proactive steps to mitigate risks. This guide will walk you through the essential steps to ensure your organization is not just compliant but also resilient in the face of evolving cyber threats.
An assessment of cyber security is not merely a formality; it’s a critical evaluation of a company's information systems, policies, and procedures designed to uncover vulnerabilities and threats. In today’s landscape, where cyber threats are prevalent, an assessment of cyber security is essential for any organization, especially in healthcare. Breaches of information, malware attacks, and insider threats are just the tip of the iceberg. So, what can organizations do to safeguard their assets?
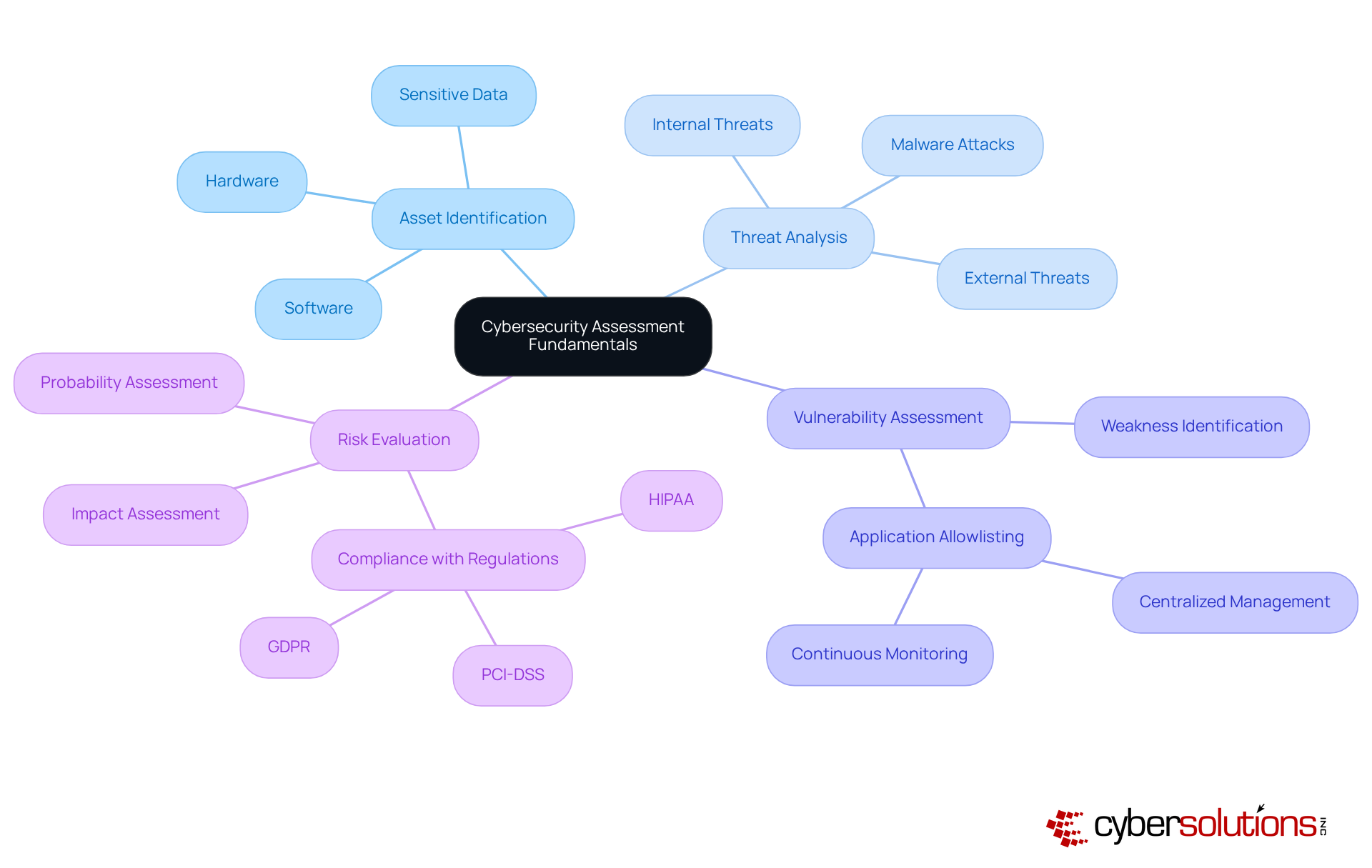
Key Components of a Robust Cybersecurity Assessment
Understanding these fundamentals is vital for organizations to allocate resources strategically and effectively manage risks. Statistics suggest that by 2025, information breaches and malware incidents will continue to rise, underscoring the necessity for assessment cyber security. A recent report highlighted that nearly 60% of companies faced a breach in the past year, with malware attacks increasing by 30% compared to the previous year.
Real-world examples illustrate the significance of vulnerability evaluations. For instance, a healthcare entity that conducted a thorough evaluation uncovered significant weaknesses in its patient data management system. This led to the adoption of improved security measures that greatly reduced the risk of data breaches. By prioritizing security assessments and implementing proactive strategies like employee training, organizations can better defend against the evolving landscape of cyber threats, ensuring they remain resilient and compliant in an increasingly regulated environment.
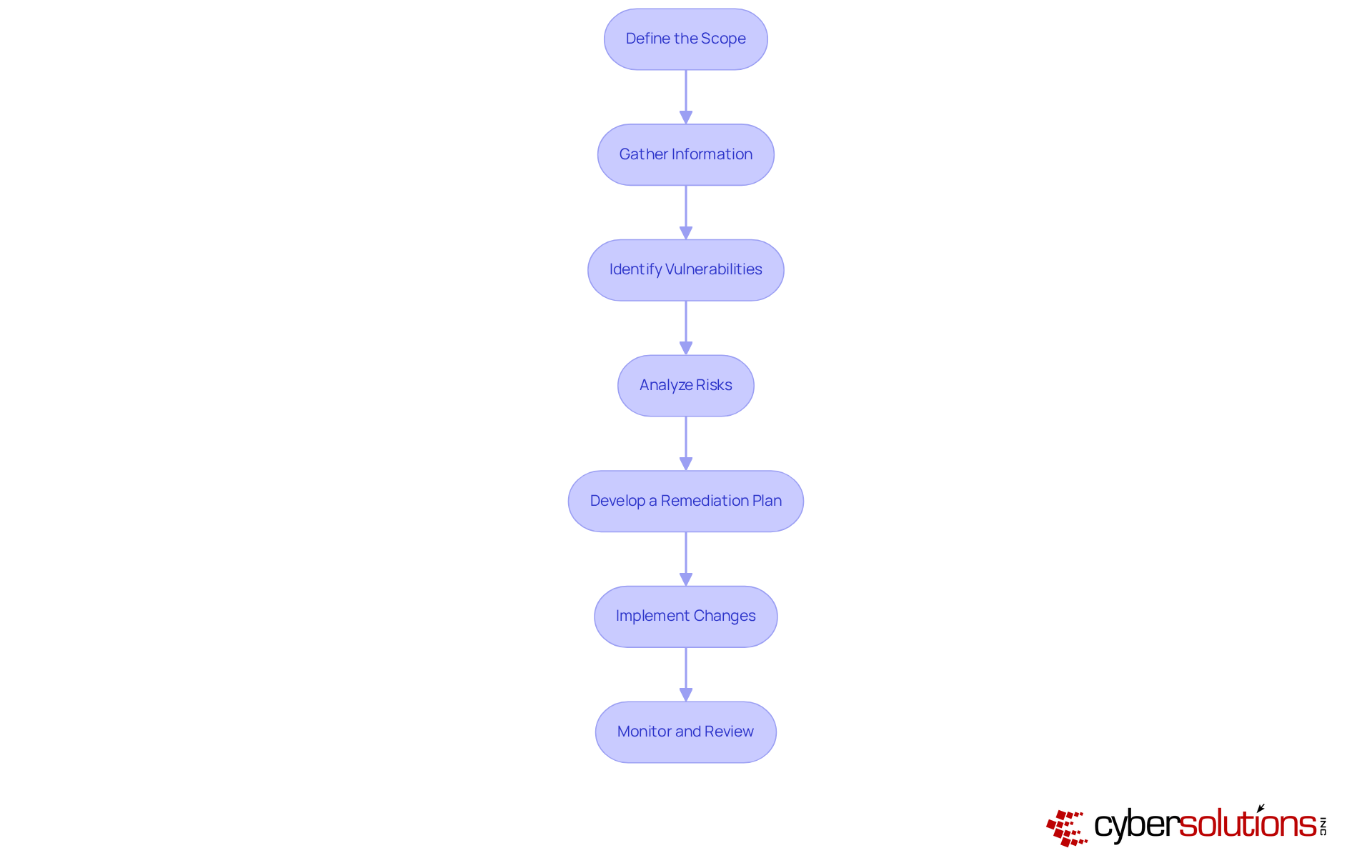
To conduct a comprehensive cybersecurity assessment, it’s crucial to follow these essential steps:
Define the Scope: Start by identifying which systems, processes, and assets will be included in the evaluation. This focus ensures that efforts are directed toward the most critical areas.
Gather Information: Collect data on existing security measures, policies, and procedures. This involves reviewing documentation and conducting interviews with key personnel.
Identify Vulnerabilities: Employ tools and techniques such as penetration testing and vulnerability scanning to uncover weaknesses in your systems.
Analyze Risks: Assess the likelihood and potential impact of identified vulnerabilities being exploited. This assessment helps in prioritizing which vulnerabilities to address first.
Develop a Remediation Plan: Formulate a plan to address identified vulnerabilities, detailing timelines and assigning responsibilities.
Implement Changes: Execute the remediation plan, making necessary adjustments to policies, procedures, and technical controls.
Monitor and Review: Continuously observe the effectiveness of implemented changes and regularly evaluate the assessment process to adapt to new threats.
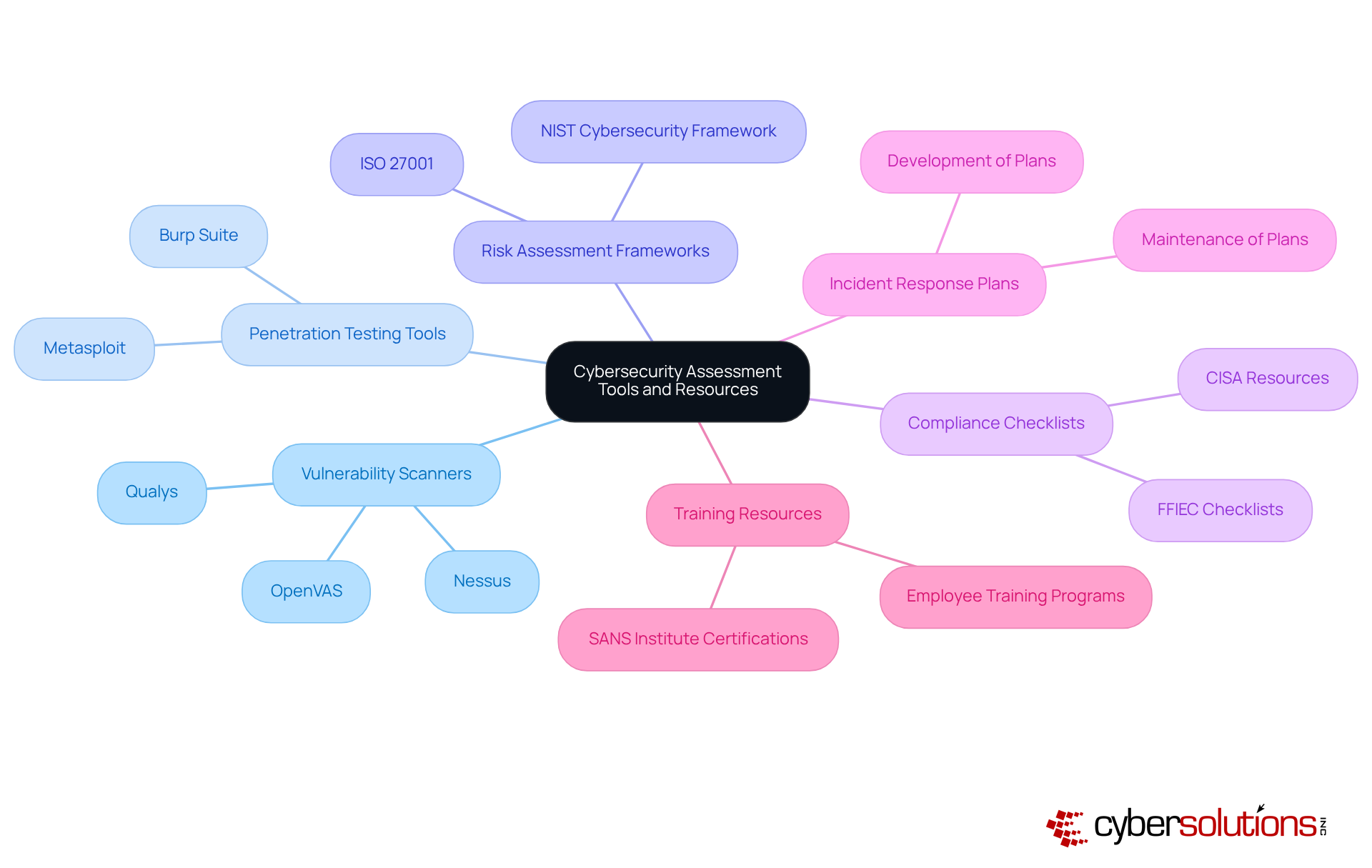
In today’s digital landscape, the importance of cybersecurity cannot be overstated, especially for healthcare organizations. With the rise in cyber threats, it’s crucial to adopt measures that not only comply with CMMC Level 3 standards but also improve your organization’s assessment of cyber security posture. Here are essential tools and resources to consider:
Recommended Resources:
By integrating these tools and resources, you can significantly enhance your assessment of cyber security measures, ensuring not only compliance but also the protection of vital information.
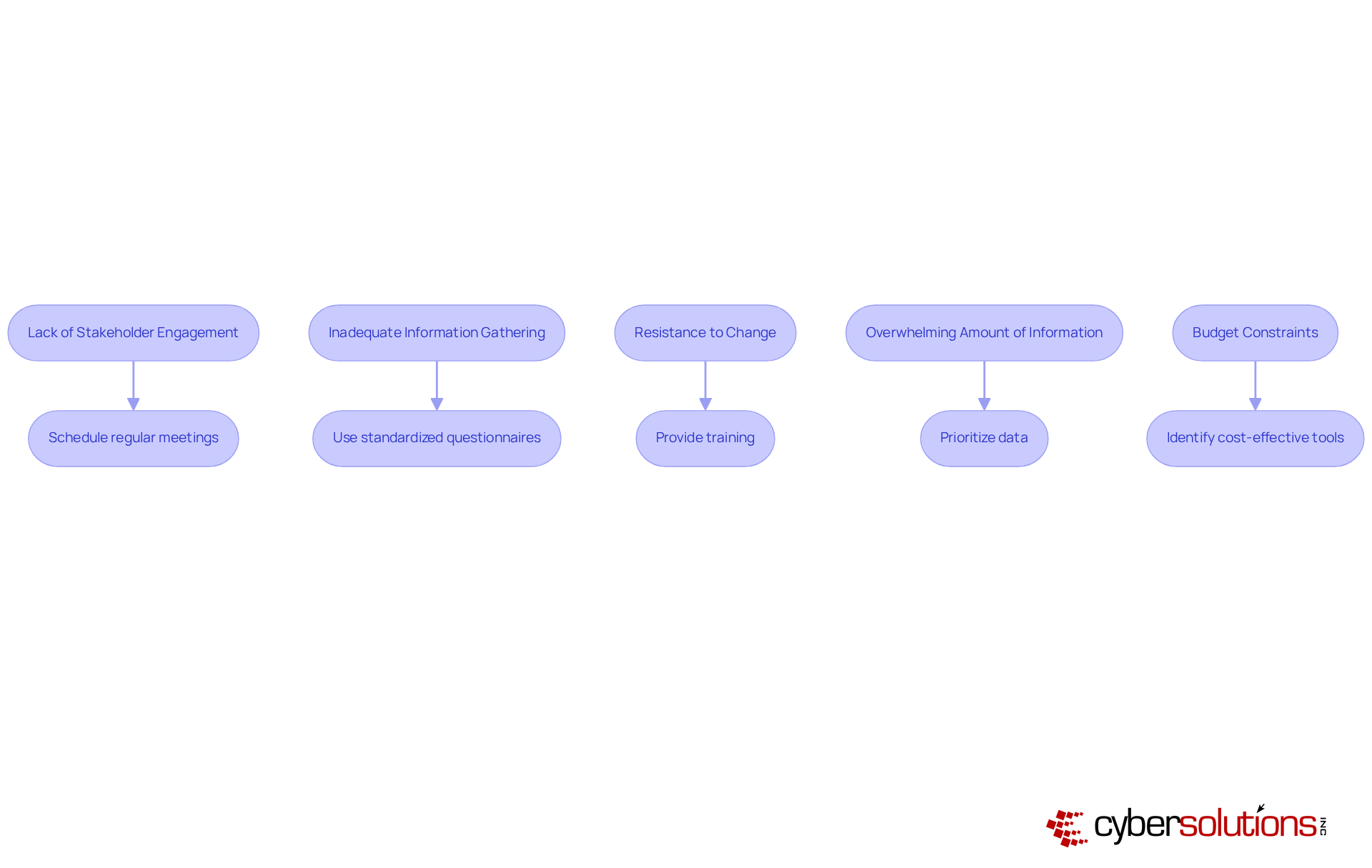
In today's digital landscape, cybersecurity is not just a technical concern; it's a critical priority for healthcare organizations. With the increasing frequency of cyber threats, CFOs face unique challenges that demand immediate attention and strategic action. Here’s how to troubleshoot common issues encountered during a cybersecurity assessment:
Lack of stakeholder engagement: When key stakeholders are not involved, assessments can become incomplete.
Inadequate information: Insufficient information can lead to flawed assessments.
Resistance to Change: Employees may resist new security measures or policies.
Overwhelming Amount of Information: Analyzing excessive information can lead to analysis paralysis.
Resource constraints: Limited resources can hinder the evaluation process.
By anticipating these issues and implementing targeted solutions, organizations can significantly enhance the effectiveness of their assessment of cyber security. Cyber Solutions stands ready to provide specialized expertise and rapid response capabilities, ensuring that your organization is well-equipped to tackle the evolving landscape of cyber threats.
A comprehensive cybersecurity assessment is not merely a regulatory obligation; it is a fundamental necessity for organizations striving to protect their critical assets against an ever-evolving threat landscape. In today’s digital age, where cyber threats are rampant, organizations must systematically identify vulnerabilities, analyze risks, and implement robust remediation plans. This proactive approach not only enhances their security posture but also ensures compliance with industry standards.
Key components of an effective cybersecurity assessment include:
Each of these elements plays a crucial role in uncovering potential weaknesses and prioritizing security measures. The integration of essential tools and resources, such as vulnerability scanners and risk assessment frameworks, empowers organizations to navigate the complexities of cybersecurity challenges effectively.
Ultimately, the importance of conducting thorough cybersecurity assessments cannot be overstated. As cyber threats continue to rise, it is imperative for organizations to adopt a proactive approach, ensuring they not only comply with regulations but also safeguard sensitive data. By fostering a culture of security awareness and utilizing best practices, organizations can position themselves to mitigate risks and protect their valuable information in an increasingly digital world. Are you ready to take the necessary steps to secure your organization?
What is the purpose of a cybersecurity assessment?
A cybersecurity assessment is a critical evaluation of a company's information systems, policies, and procedures designed to uncover vulnerabilities and threats to safeguard organizational assets.
Why is cybersecurity assessment especially important for healthcare organizations?
Cybersecurity assessments are essential for healthcare organizations due to the high risk of information breaches, malware attacks, and insider threats that can compromise sensitive patient data.
What are the key components of a robust cybersecurity assessment?
The key components include asset identification, threat analysis, vulnerability assessment, and risk evaluation.
What does asset identification involve?
Asset identification involves recognizing all critical assets, including hardware, software, and sensitive data, that are vital for an organization's operations.
How does threat analysis contribute to cybersecurity?
Threat analysis evaluates potential threats that could exploit identified vulnerabilities, considering both external and internal sources to enhance security measures.
What is a vulnerability assessment and why is it important?
A vulnerability assessment identifies weaknesses within systems that could be targeted by malicious actors, allowing for proactive remediation to strengthen security.
What role does application allowlisting play in cybersecurity?
Application allowlisting prevents unauthorized or malicious applications from executing, thereby reducing the attack surface and minimizing vulnerabilities within an organization.
How does risk evaluation help organizations prioritize their security efforts?
Risk evaluation assesses the potential impact and probability of identified threats, enabling organizations to prioritize their security measures effectively.
What are some statistics regarding cybersecurity threats?
Statistics suggest that by 2025, information breaches and malware incidents will continue to rise, with nearly 60% of companies facing a breach in the past year and malware attacks increasing by 30% compared to the previous year.
Can you provide an example of the importance of vulnerability evaluations?
A healthcare entity that conducted a thorough vulnerability evaluation uncovered significant weaknesses in its patient data management system, leading to improved security measures that greatly reduced the risk of data breaches.