
In today's world, where cyber threats are more prevalent than ever, the healthcare sector is grappling with a significant challenge: maintaining operational continuity while protecting sensitive patient information. A well-crafted software disaster recovery plan isn't just a regulatory checkbox; it’s a crucial strategy that can determine whether an organization thrives or faces catastrophic failure. What happens when healthcare organizations overlook their business disruption tolerance or fail to pinpoint critical functions? The stakes are incredibly high, and the repercussions can be severe.
This article explores essential best practices for developing a robust disaster recovery plan that not only meets compliance standards but also strengthens organizations against the constantly evolving landscape of cyber risks. By understanding the unique challenges faced by healthcare CFOs and implementing effective strategies, organizations can safeguard their operations and ensure they are prepared for any eventuality.
In today's healthcare landscape, the importance of cybersecurity cannot be overstated. As organizations face an increasing number of cyber threats, understanding business disruption tolerance becomes essential. To effectively evaluate this tolerance, entities must conduct a thorough analysis of their operations. This process involves identifying the maximum acceptable downtime (MAD) for each critical function and grasping the impact of potential disruptions.
Utilizing tools like business impact analysis allows companies to quantify the effects of downtime on revenue, customer satisfaction, and regulatory compliance. For instance, in the healthcare sector, a BIA might reveal that downtime exceeding 30 minutes could jeopardize patient safety and lead to substantial financial penalties. With the average cost reaching $10.1 million, the stakes are incredibly high.
Establishing clear metrics for recovery enables entities to prioritize their recovery efforts effectively. This ensures they can maintain and protect their reputation in an increasingly regulated environment. As industry leaders emphasize, understanding the limits of acceptable downtime is crucial for minimizing the impact of business disruptions on revenue and customer satisfaction.
Moreover, incorporating thorough and robust disaster recovery plans is vital for healthcare entities. Proactive risk management and audit assistance are essential to safeguard patient health information (PHI) and prevent costly penalties. By leveraging expert consulting services, entities can ensure continuous monitoring and expert guidance, significantly enhancing their capability to respond to potential disruptions.

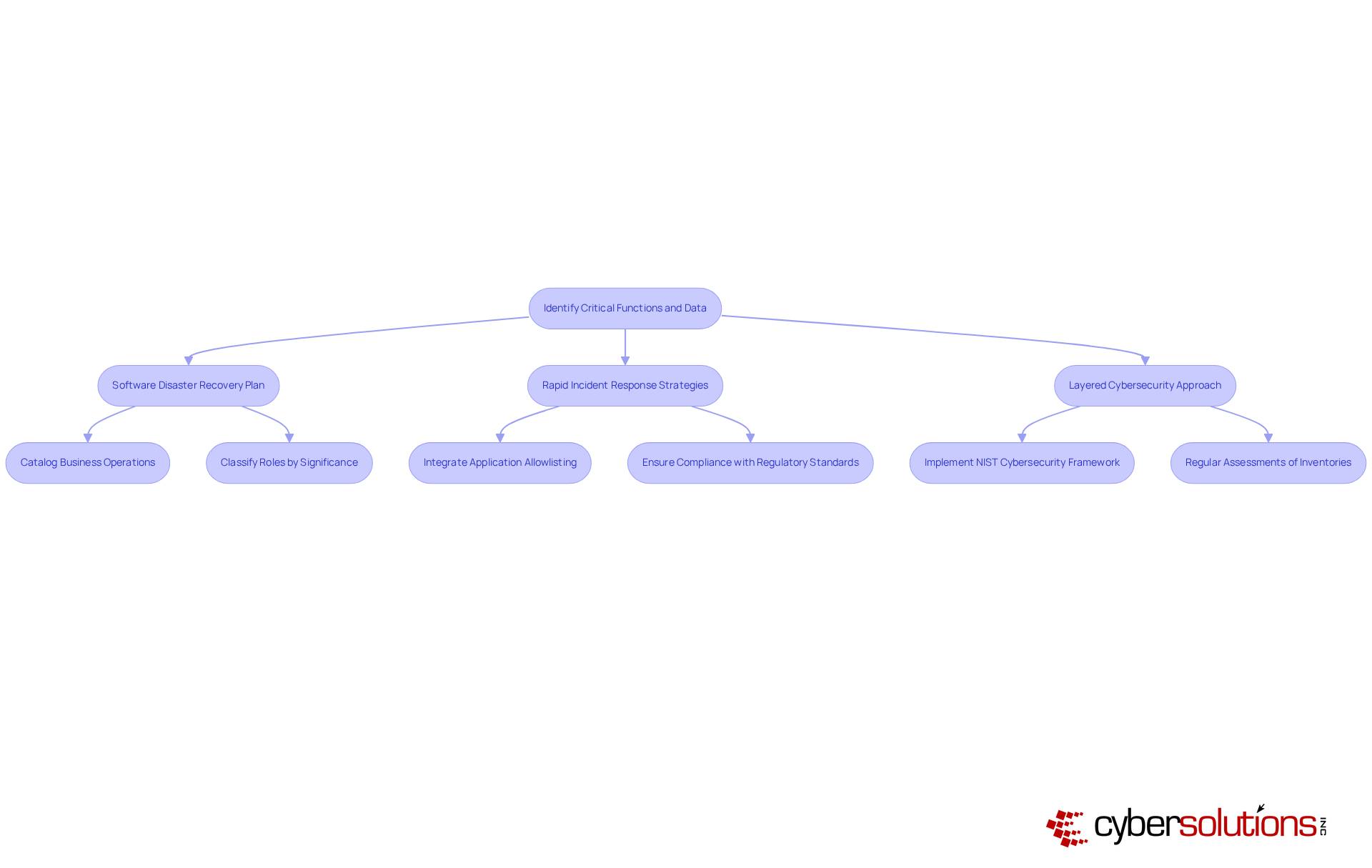
In today’s digital landscape, the importance of cybersecurity cannot be overstated. Organizations must proactively prepare for potential interruptions by developing a comprehensive plan that includes a catalog of all critical functions and their related information. This inventory should classify roles based on their significance to operations and compliance obligations. For instance, in financial institutions, activities like transaction processing and customer data management are typically deemed essential.
Implementing frameworks such as the cybersecurity framework is vital for identifying dependencies and weaknesses within these operations. Regular assessments of these inventories are crucial to adapt to evolving threats and vulnerabilities, ensuring that the identified functions remain relevant and effective in mitigating risks.
Cyber Solutions underscores the necessity of a robust cybersecurity strategy, which includes:
to prepare organizations for potential disasters. By integrating cybersecurity measures into a disaster recovery plan, organizations can bolster their defenses against malware and ensure compliance with regulatory standards. This proactive stance is essential in safeguarding data and maintaining operational integrity.
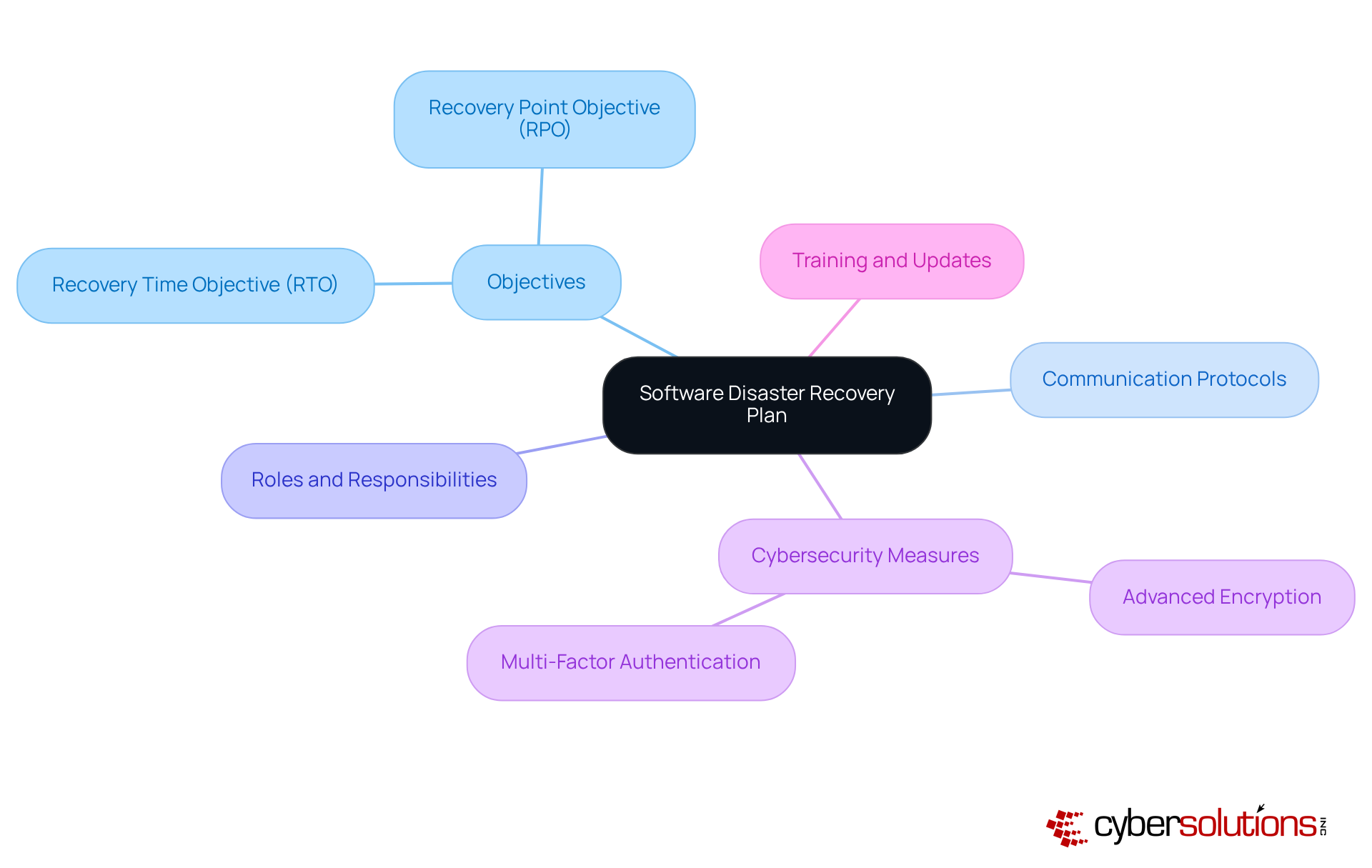
In today's healthcare landscape, the importance of a robust disaster recovery plan cannot be overstated. With increasing threats to patient data, healthcare organizations must prioritize the development of a thorough recovery plan that complies with regulations. This should clearly outline the specific measures necessary to reinstate critical functions, including timelines for each function.
To effectively safeguard PHI during the restoration process, the recovery plan must detail risk assessments, resource distribution, and the roles and responsibilities of team members. For example, a healthcare organization might implement procedures for restoring electronic health records within a specified timeframe to ensure compliance with legal requirements. Furthermore, implementing a security framework with best practices, such as advanced encryption and multi-factor authentication, is crucial to protect PHI throughout the restoration.
Regular updates and training sessions are essential to ensure that all team members are familiar with the plan and can execute it effectively when needed. Collaborating with a Chief Information Security Officer (CISO) can provide strategic oversight, enhance compliance initiatives, and ensure continuous adherence to HIPAA standards. This collaboration not only boosts the overall efficiency of the restoration plan but also reinforces the organization's commitment to safeguarding patient information.
In conclusion, a well-structured disaster recovery plan is essential for healthcare organizations to navigate the complexities of cybersecurity threats while maintaining compliance and protecting patient data.
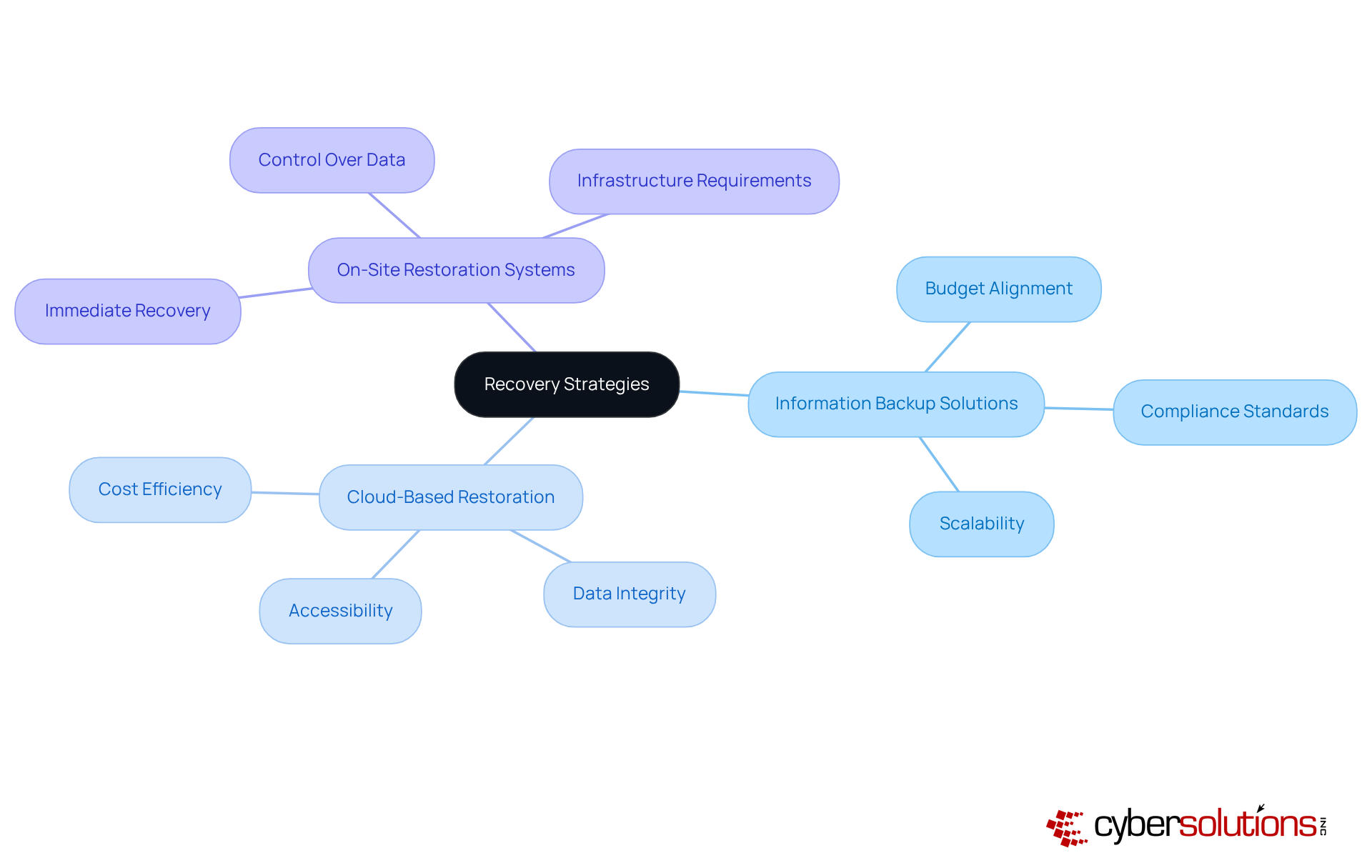
Organizations must rigorously assess various restoration strategies, including cloud backups, off-site storage, and on-site restoration systems. This evaluation is crucial for aligning with the entity's goals and budget, particularly considering the foreseeable monthly expenses outlined by Cyber Solutions. For example, a company facing data loss might opt for a hybrid solution that combines on-site backups with cloud replication. This approach not only guarantees data availability but also benefits from flat-rate pricing that simplifies budgeting.
Moreover, organizations should critically evaluate the scalability of these strategies to accommodate future growth or changes in operational requirements. The effectiveness of these strategies is essential to adapt to the ever-evolving landscape of cybersecurity threats and technological advancements. By proactively addressing these challenges, organizations can ensure robust protection and business continuity.
To ensure the effectiveness of the software recovery plan, organizations must establish a strategy that includes both tabletop exercises and full-scale simulations. These tests are essential for evaluating and assessing the team's ability to fulfill their roles during a crisis.
Consider this: financial institutions often conduct quarterly drills simulating disaster scenarios. This practice allows them to measure response times and the effectiveness of their teams. Following each exercise, a debriefing should be conducted to pinpoint areas for improvement. This ensures that the recovery plan is continuously updated to address evolving threats and vulnerabilities.
This iterative process not only enhances preparedness but also reinforces the organization's resilience against potential disruptions. By committing to regular testing and reviews, organizations can stay ahead of challenges and ensure a robust response to any crisis.

Understanding the complexities of a software disaster recovery plan is crucial for organizations, especially in high-stakes sectors like healthcare and finance. A robust recovery plan not only protects sensitive data but also guarantees operational continuity amid potential disruptions. By prioritizing business disruption tolerance, identifying critical functions, and developing comprehensive recovery strategies, organizations can significantly enhance their resilience against cyber threats.
The article underscores several essential practices:
These steps ensure that organizations are well-prepared to respond effectively to incidents, minimizing impacts on revenue and customer satisfaction. Moreover, integrating strong cybersecurity measures - such as multi-factor authentication and encryption - is vital for safeguarding sensitive information throughout the recovery process.
Ultimately, the importance of a proactive approach to disaster recovery cannot be overstated. Organizations must embrace these best practices, continuously refine their strategies, and commit to regular testing. By doing so, they not only strengthen their defenses against cyber threats but also demonstrate their commitment to compliance and the protection of vital data. Taking these steps empowers organizations to navigate the complexities of today's digital landscape with confidence and resilience.
Why is understanding business disruption tolerance important in healthcare?
Understanding business disruption tolerance is essential in healthcare due to the increasing number of cyber threats. It helps organizations identify the maximum acceptable downtime (MAD) for critical functions and understand the financial implications of potential disruptions.
What tools can be used to evaluate business disruption tolerance?
Tools like Business Impact Analysis (BIA) can be utilized to quantify the effects of downtime on revenue, customer satisfaction, and regulatory compliance.
What are the consequences of exceeding acceptable downtime in healthcare?
Exceeding acceptable downtime can jeopardize patient safety and lead to substantial financial penalties, with the average cost of a data breach in healthcare reaching $10.1 million.
How can organizations prioritize their recovery strategies?
By establishing clear metrics for disruption tolerance, organizations can effectively prioritize their recovery strategies to maintain operational resilience and protect their reputation.
What role does HIPAA compliance play in cybersecurity for healthcare entities?
Incorporating thorough HIPAA compliance solutions and robust cybersecurity measures is vital for healthcare entities to safeguard patient health information (PHI) and prevent costly penalties.
What is Compliance as a Service (CaaS)?
Compliance as a Service (CaaS) is a solution that provides continuous monitoring and expert guidance to enhance an organization's capability to respond to potential disruptions.
How should organizations identify critical functions and data?
Organizations should develop a comprehensive software disaster recovery plan that includes a catalog of all business operations and their related information, classifying roles based on their significance to operations and compliance obligations.
What frameworks can help in identifying dependencies and weaknesses in operations?
Implementing frameworks like the NIST Cybersecurity Framework is vital for identifying dependencies and weaknesses within business operations.
Why is regular assessment of inventories important?
Regular assessments are crucial to adapt to evolving business operations and regulatory requirements, ensuring that identified critical functions remain relevant and effective in mitigating risks.
What components should a structured process for disaster recovery include?
A structured process should include a software disaster recovery plan, rapid incident response strategies, and a layered cybersecurity approach to prepare organizations for potential disasters.