
As organizations face the mounting pressures of cybersecurity and regulatory compliance, the significance of understanding IT spending as a percentage of revenue by industry has reached a critical juncture. In particular, the healthcare sector grapples with unique challenges that demand tailored strategies to optimize budget allocations and bolster operational resilience. With the stakes soaring, how can CFOs effectively navigate these complexities while ensuring a robust return on investment?
The current landscape of cybersecurity threats is daunting, especially for healthcare organizations that handle sensitive patient data. The implications of these threats extend beyond financial loss; they can jeopardize patient trust and regulatory standing. Therefore, it is imperative for organizations to adopt a proactive approach to cybersecurity, integrating comprehensive solutions that address these vulnerabilities head-on.
Cyber Solutions can play a pivotal role in this endeavor. By leveraging data-driven insights and industry-specific strategies, organizations can not only enhance their security posture but also streamline their IT expenditures. This dual focus on security and efficiency is essential for maximizing value in an increasingly complex environment.
In conclusion, as the demand for cybersecurity intensifies, organizations must prioritize their IT investments wisely. By understanding the nuances of their industry and implementing tailored strategies, they can navigate the challenges ahead and secure a competitive edge.
In today's digital landscape, IT spending is a critical component of operational integrity, especially in healthcare. With increasing threats targeting healthcare organizations, CFOs and IT leaders alike face significant challenges.
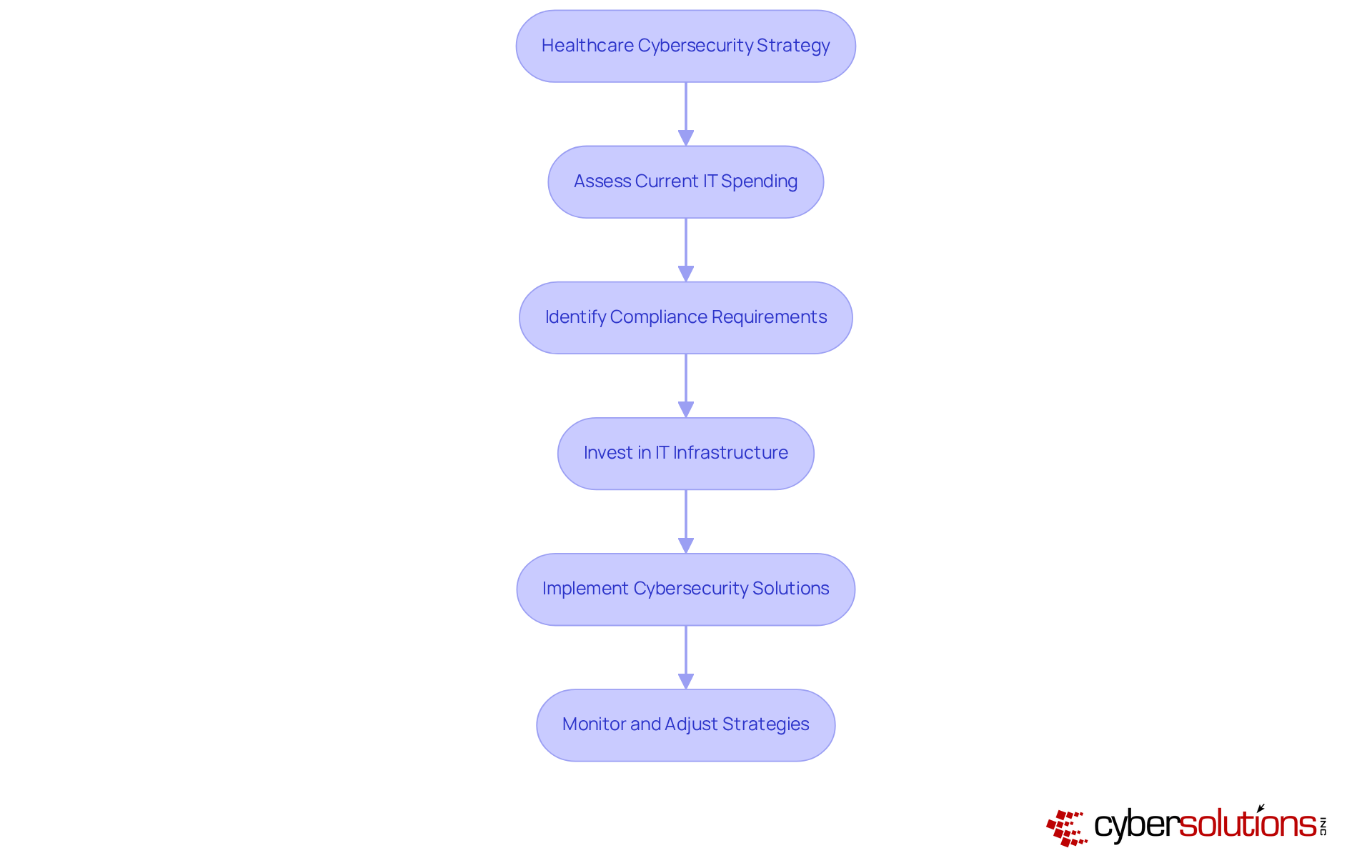
Healthcare institutions must navigate a complex environment while ensuring data security. For instance, the stakes are high when it comes to compliance and other regulatory frameworks. Failure to adhere to these standards can lead to severe penalties and loss of trust. How can organizations effectively allocate their IT budgets while considering best practices to address these pressing concerns?
Cyber Solutions Inc. offers a tailored approach to IT spending, recognizing that different sectors have distinct needs. Our customized IT services are designed to meet the specific security and regulatory requirements of healthcare, financial services, manufacturing, and government. By analyzing industry-specific benchmarks, we empower clients to allocate their IT budgets effectively, ensuring that investments align with both operational goals and regulatory mandates, particularly by evaluating performance metrics.
To combat unauthorized software and enhance cybersecurity, we implement proactive strategies such as:
These measures not only mitigate risks but also bolster overall business performance, providing a strategic advantage for our clients across various sectors.
In conclusion, as cybersecurity threats continue to evolve, Cyber Solutions Inc. can help healthcare organizations navigate these challenges effectively. Are you ready to enhance your cybersecurity posture and ensure compliance? Let's discuss how we can support your organization's unique needs.
In today's healthcare landscape, the stakes for cybersecurity have never been higher. Organizations face challenges, especially with IT spending often surpassing 5% due to stringent regulatory demands such as HIPAA, PCI-DSS, CMMC, and SOX. The costs are rising, highlighting the urgency for action.
Healthcare providers must invest in cybersecurity measures to ensure compliance and safeguard patient information. Cyber Solutions stands ready to assist these organizations in navigating the complexities of cybersecurity through tailored offerings like managed services and continuous risk assessments. This proactive approach not only helps mitigate risks but also builds patient trust and enhances operational efficiency.
Consider this: organizations that prioritize cybersecurity investments often see a direct correlation with increased patient confidence. For healthcare leaders, allocating resources effectively in this evolving landscape is not just advisable; it's imperative. In a recent incident, Cyber Solutions demonstrated its commitment by assembling a specialized team within 24 hours, successfully containing the threat and restoring systems to ensure continuity of care.
Such rapid response capabilities underscore the critical need for robust cybersecurity strategies. Investing in these measures is not merely a choice; it’s a necessity to protect and maintain the trust of patients.
In the finance sector, the significance of cybersecurity cannot be overstated. Financial institutions are prioritizing cybersecurity more than ever, with spending typically ranging from 4.4% to 11.4%. As cyber threats escalate, these organizations are increasingly investing in cybersecurity technologies and solutions. For example, healthcare organizations have raised their budgets in response to ransomware attacks, a trend that is now mirrored in finance as firms recognize the urgent need for protection.
Cyber Solutions stands at the forefront of this critical landscape, offering tailored risk evaluations, assessments, and proactive strategies like application allowlisting. This approach not only prevents unauthorized software from running but also aids in maintaining system integrity. By aligning IT investments with risk management, financial institutions can protect their assets while enhancing regulatory compliance, ensuring their organization effectively navigates the complexities of an evolving digital landscape.
Moreover, as financial firms invest in reusable data pipelines and governance frameworks, they position themselves to manage costs while pursuing innovative IT solutions. This strategic focus ultimately enhances operational efficiency. Are you ready to take your cybersecurity measures to the next level? With Cyber Solutions, you can ensure that your organization is not just compliant but also competitive in the digital realm.

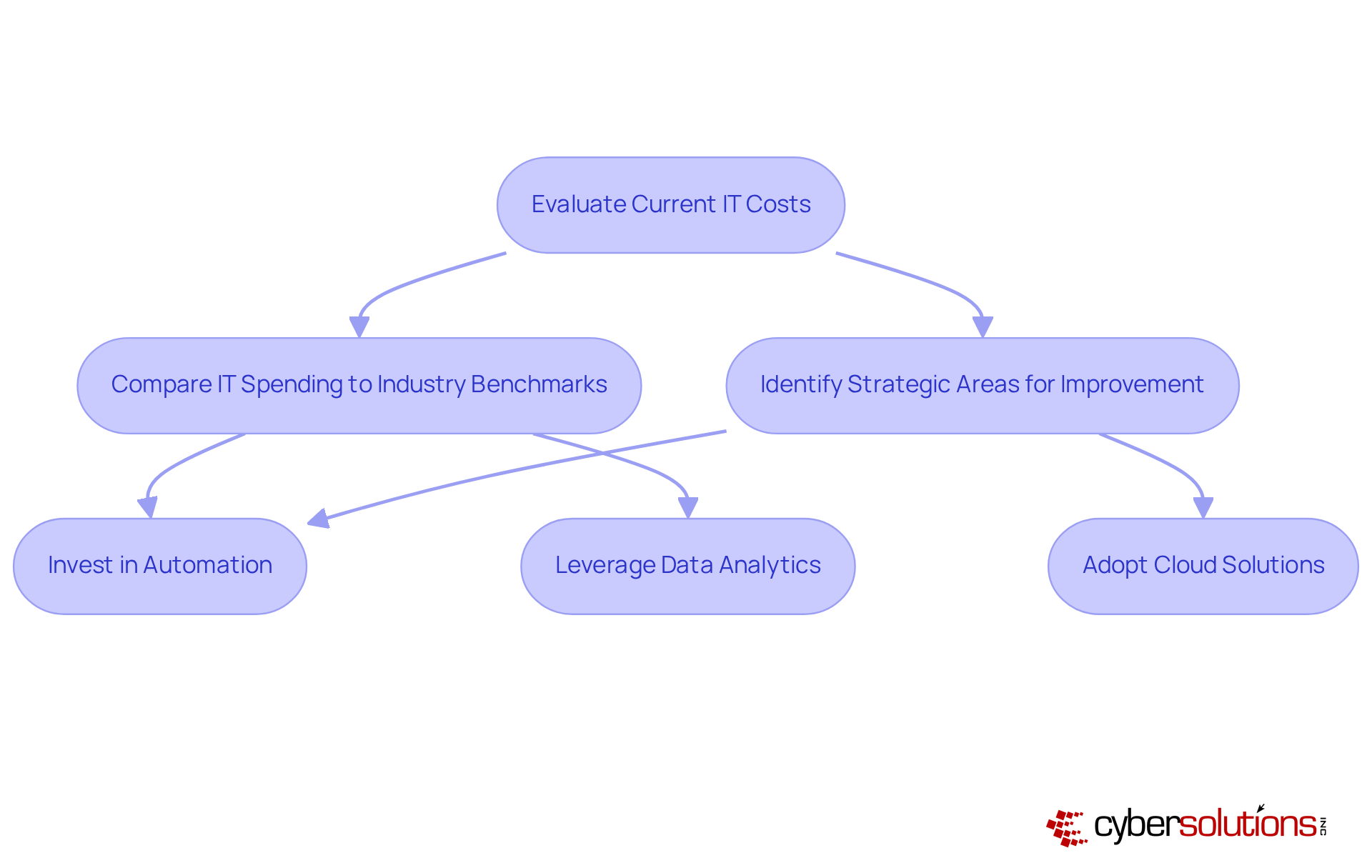
Manufacturing companies face a pressing challenge: managing to keep IT spending below 5% while maximizing efficiency. As we look toward 2025, investing in automation, data analytics, and IT infrastructure is not just beneficial; it’s essential for growth and maintaining competitiveness. Industry leaders assert that technological advancements are pivotal for success, with a striking 86% of executives believing these technologies will offer a significant edge over the next five years.
Cyber Solutions Inc. stands at the forefront, helping manufacturers identify strategies that align with their operational goals. This alignment ensures that every dollar spent translates into measurable efficiency gains. By leveraging technology, manufacturers can significantly reduce downtime and streamline processes, ultimately boosting their productivity. As Wes aptly noted, "Automation empowers workers while boosting output," underscoring the vital role of automation in driving productivity.
To fully capitalize on IT expenditures, manufacturers must benchmark against industry benchmarks, specifically looking at performance metrics, and explore strategic areas for improvement. Are you ready to take the next step in enhancing your operations? The time to act is now.
Government agencies are increasingly confronted with the pressing challenges of limited budgets and the need for effective technology solutions. Did you know that IT spending in the public sector typically accounts for 3% to 7% of total budgets? This figure varies based on the agency's size and mission. As we look ahead to 2025, investments are not just beneficial; they are essential for maintaining operations and complying with evolving regulations.
Cyber Solutions Inc. stands at the forefront, guiding government entities in prioritizing these vital investments. By harnessing advanced technologies and robust cybersecurity measures, agencies can optimize their IT spending while simultaneously mitigating operational risks and strengthening public trust. This approach resonates with industry leaders who stress the importance of strategic investments and planning to navigate the complexities of today’s IT landscape.
In a world where cybersecurity threats are ever-present, the implications for government organizations are profound. Agencies must not only invest in technology but also ensure that their IT frameworks are resilient and adaptable. Cyber Solutions Inc. offers the expertise needed to tackle these challenges head-on, ensuring that agencies can focus on their core missions without compromising security.
As cyber threats become increasingly sophisticated, organizations across various sectors are significantly increasing their investments to bolster cybersecurity measures. In 2025, global IT spending on cybersecurity is projected to reach $200 billion, representing a 15% increase from the previous year. This surge underscores the urgent need for robust defenses against evolving threats, with a staggering rise in cyberattacks.
Cyber Solutions recognizes the critical importance of cybersecurity investment. By enabling clients to allocate their IT budgets effectively, we empower them to invest in advanced cybersecurity solutions such as firewalls, intrusion detection systems, and employee training programs.
These investments are essential for protecting sensitive data and maintaining customer trust.
This tiered recovery strategy not only enhances security but also optimizes ROI, particularly for small to medium enterprises striving to comply with regulations and safeguard their federal data. Are you prepared to face the challenges posed by cyber threats? With the right strategies in place, organizations can not only protect their assets but also ensure business continuity.

Compliance as a Service is not just a trend; it’s a necessity for organizations grappling with the intricate web of regulations. As businesses increasingly outsource regulatory management, they can optimize their approach to compliance while ensuring compliance with critical regulations like GDPR. This strategic move streamlines regulatory processes, reduces costs, and mitigates risks associated with non-compliance.
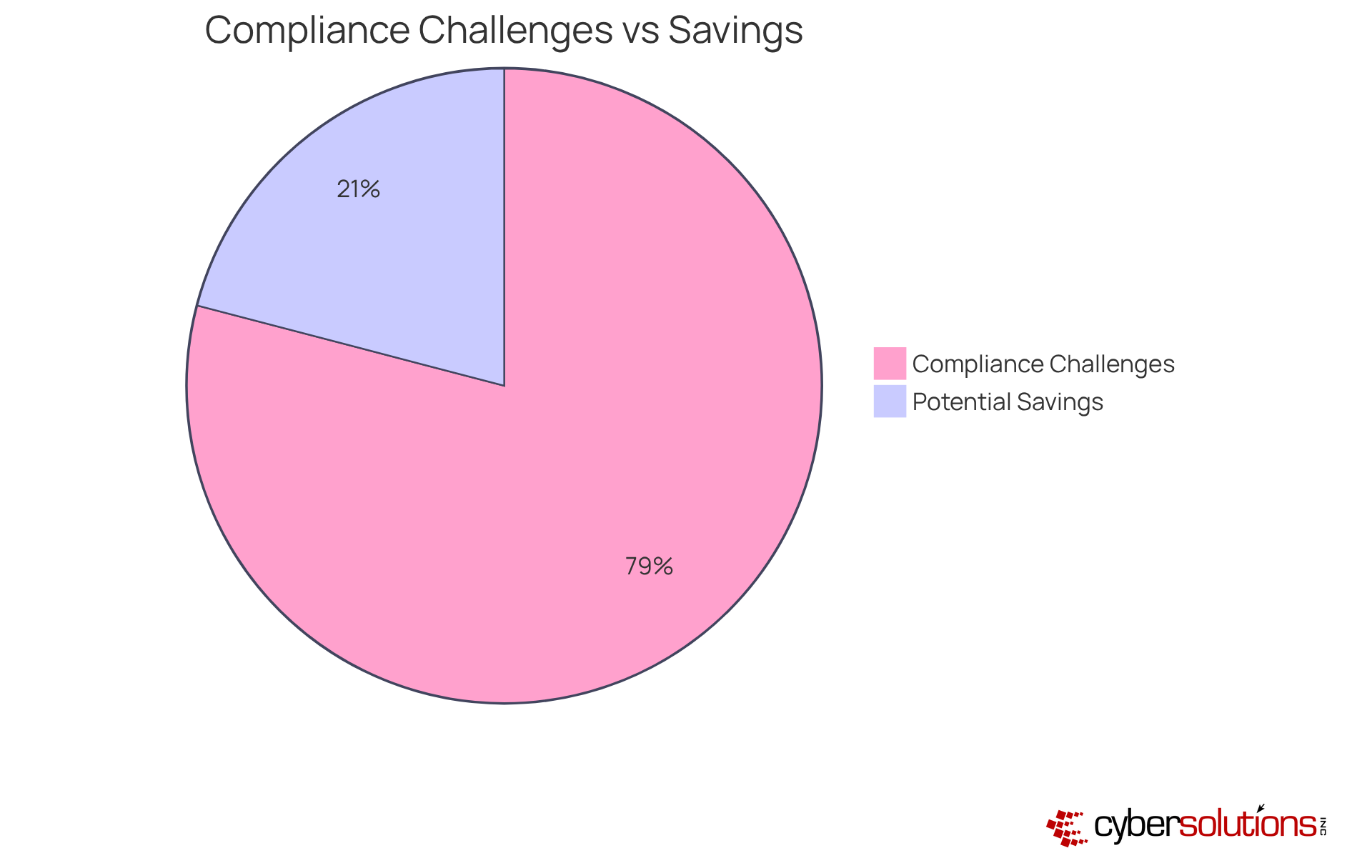
Consider this: 85% of organizations have reported challenges over the past three years. With such pressures mounting, compliance as a Service emerges as a proactive strategy to maintain adherence while optimizing budgets. Cyber Solutions Inc. stands at the forefront, offering tailored solutions that enhance compliance efforts and provide a clear return on investment, particularly in the context of budgeting for compliance-related IT expenditures.
Experts assert that adopting technology-driven compliance solutions can lead to savings of 15% to 30% on operational costs. This reinforces the value of compliance solutions in today’s dynamic regulatory environment. Are you ready to transform your compliance strategy and navigate these complexities with confidence?
Managed IT services are not just a trend; they are a strategic investment crucial for enhancing organizational security and operational efficiency. In today’s landscape, where cyber threats loom large, managed IT services allow businesses to significantly improve security while accessing cutting-edge security technologies and specialized expertise.
Cyber Solutions Inc. stands out by offering a comprehensive suite of services, including:
These services collectively bolster a company's security posture, ensuring that organizations are not only reactive but proactive.
This proactive approach not only mitigates risks associated with cyber threats but also allows companies to better manage their resources. By aligning expenditures with overarching strategic objectives, businesses can invest with confidence.
As we look toward 2025 and beyond, the advantages of managed IT services become increasingly evident. Are you ready to position your organization for sustained growth and resilience? With Cyber Solutions, you can enhance security and secure your future.

Assessing the importance of IT expenditures is not just important; it’s essential for organizations aiming to validate their budgets and enhance future investments. In today’s landscape, where challenges loom large, effective ROI measurement becomes a critical tool. It involves analyzing the benefits of IT spending, improved productivity, and cost savings.
Cyber Solutions Inc. stands ready to assist clients in establishing metrics that assess the financial impact of their IT investment choices. By concentrating on measurable results, organizations can make decisions that align with their strategic goals. This proactive approach not only enhances efficiency but also positions entities to thrive in an increasingly complex digital environment.
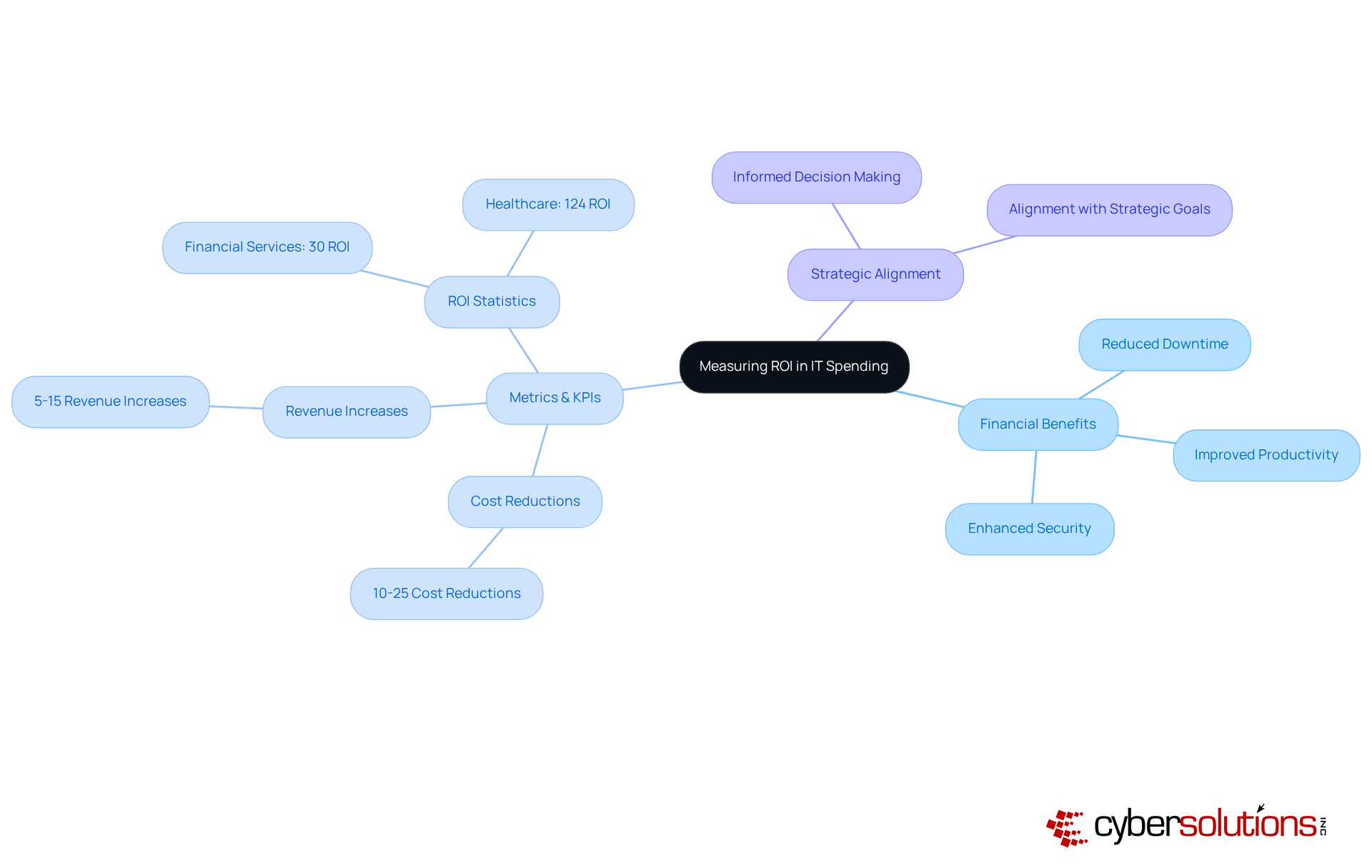
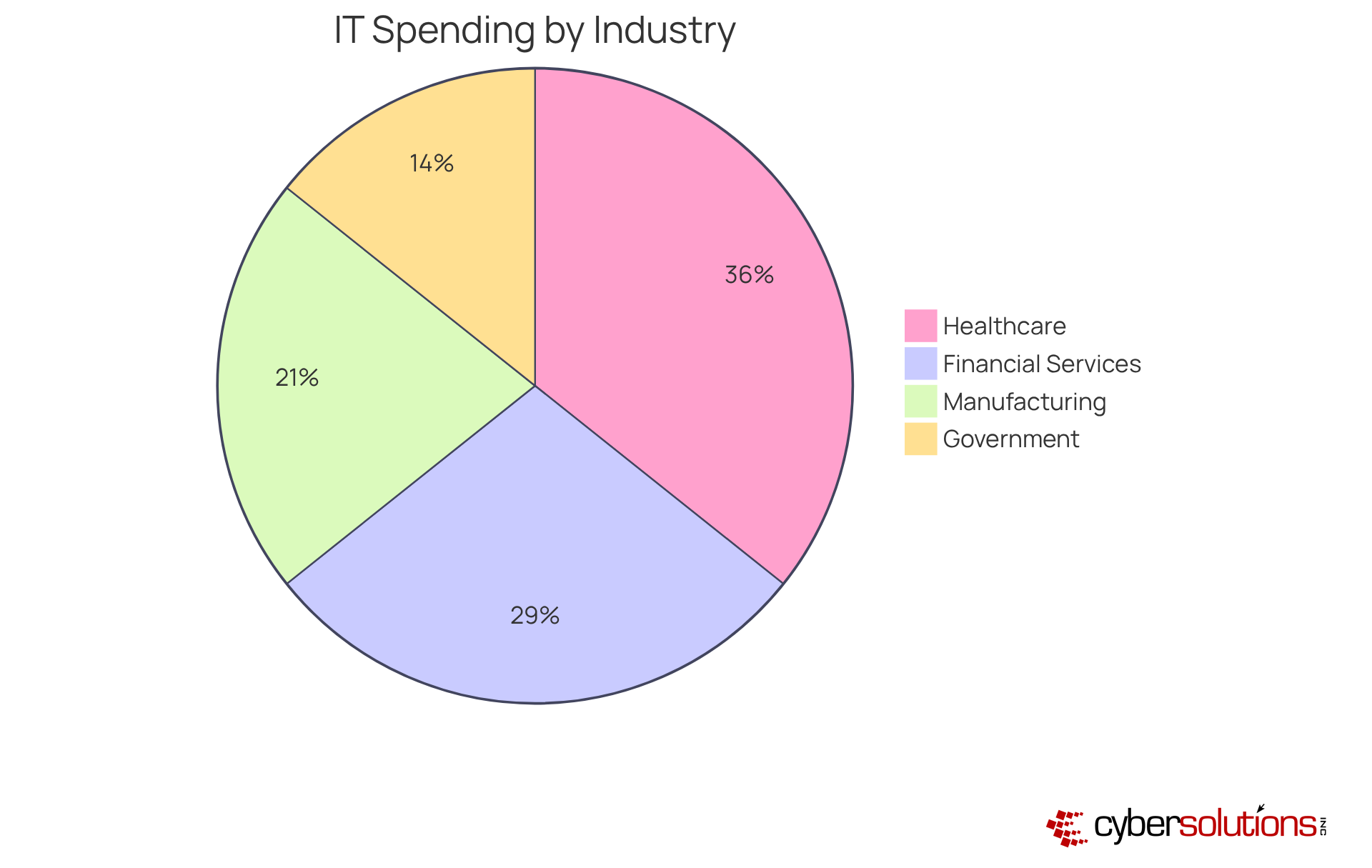
It is crucial for organizations to understand IT spending trends, as it varies significantly due to their industry needs. For example, the healthcare sector typically allocates between 4.4% and 11.4% of revenue to IT, while the finance sector often invests more than 5%. In contrast, the manufacturing industry strives to keep IT expenses below 5% to enhance operational efficiency.
By analyzing these trends, organizations can benchmark against the established industry standards. This not only ensures that their investments are aligned with best practices but also supports their overall business objectives. Are you ready to evaluate your IT spending and ensure it meets the demands of your industry?
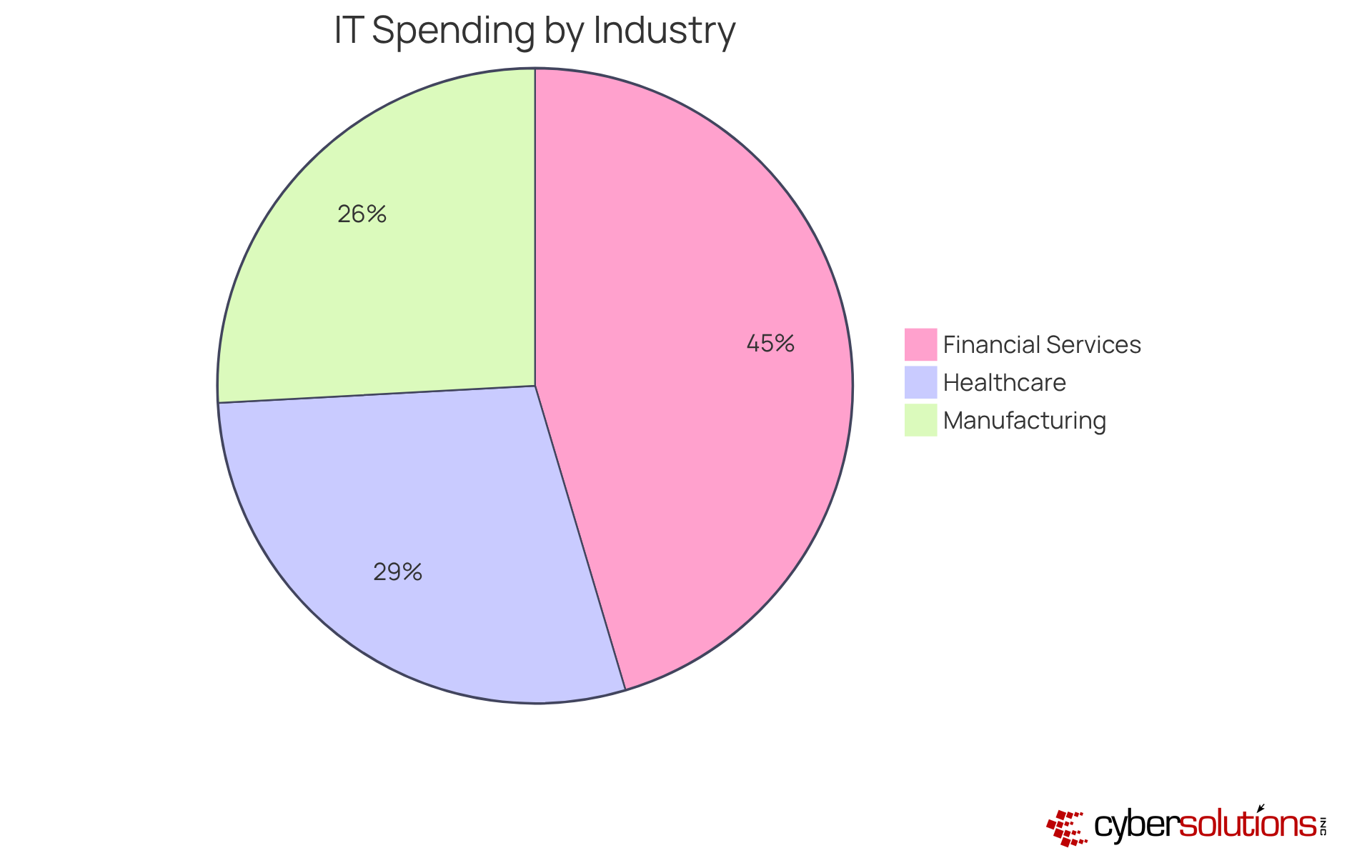
In today’s intricate business environment, grasping IT spending as a percentage of revenue by industry is crucial for organizations striving to boost operational efficiency and security. Tailored IT strategies that address the distinct needs of sectors like healthcare, finance, manufacturing, and government are vital for overcoming challenges related to regulatory compliance and cybersecurity threats.
The significant disparities in IT expenditure across industries are striking. For instance, healthcare often surpasses 5% due to rigorous compliance demands, while manufacturing aims to keep costs below that threshold to enhance efficiency. Proactive investments in cybersecurity, managed IT services, and compliance solutions not only mitigate risks but also drive operational improvements and build trust among stakeholders.
As organizations gear up for 2025 and beyond, the necessity to align IT spending with industry benchmarks becomes increasingly evident. By adopting strategic budgeting and investment approaches, businesses can safeguard their assets against evolving threats and position themselves for sustainable growth. Embracing tailored IT spending strategies is not merely a choice-it’s an essential step for thriving in an ever-evolving digital landscape.
Why is cybersecurity critical for healthcare organizations?
Cybersecurity is essential for healthcare organizations due to increasing threats targeting sensitive patient data and the need to comply with regulations like HIPAA. Failure to adhere to these standards can result in severe penalties and loss of trust.
How does Cyber Solutions Inc. approach IT spending for different industries?
Cyber Solutions Inc. offers a tailored approach to IT spending, recognizing that different sectors, such as healthcare, financial services, manufacturing, and government, have distinct needs. They analyze industry-specific benchmarks to help clients allocate their IT budgets effectively.
What are some proactive strategies implemented by Cyber Solutions to enhance cybersecurity?
Cyber Solutions implements strategies such as application allowlisting, endpoint protection, and advanced threat detection to combat unauthorized software and improve overall business performance.
What are the financial implications of inadequate cybersecurity in healthcare?
The average cost of a healthcare data breach reached approximately $10.22 million in 2025, highlighting the significant financial risks associated with insufficient cybersecurity measures.
How does Cyber Solutions assist healthcare organizations in managing compliance costs?
Cyber Solutions provides tailored offerings like Compliance as a Service (CaaS) and continuous risk assessments, helping organizations navigate regulatory complexities and manage compliance expenses effectively.
What is the typical range of IT spending as a percentage of revenue in the finance sector?
In the finance sector, IT spending as a percentage of revenue typically ranges from 4.4% to 11.4%.
How are financial institutions responding to increasing cyber threats?
Financial institutions are raising their cybersecurity budgets by 15-20% annually in response to escalating cyber threats, particularly ransomware attacks, to enhance their defenses.
What role does Cyber Solutions play in risk management for financial institutions?
Cyber Solutions offers tailored risk evaluations, incident response plans, and proactive strategies that help financial institutions align their IT investments with risk management and regulatory compliance.
Why is investing in cybersecurity measures imperative for healthcare providers?
Investing in cybersecurity is crucial for healthcare providers to protect operations, maintain patient trust, and ensure continuity of care in the face of evolving cyber threats.