
Disaster recovery tiers form a crucial framework for organizations aiming to protect their data and ensure business continuity in an unpredictable landscape. With alarming statistics indicating that over half of organizations lack formal disaster management plans, the pressing question arises: how prepared are companies to respond effectively to crises? This framework categorizes restoration capabilities, ranging from basic manual techniques to advanced automated solutions, providing a structured approach for businesses to evaluate their readiness for emergencies.
As organizations navigate the complexities of disaster recovery, they must confront unique challenges that can hinder their response efforts. The implications of inadequate preparedness can be severe, impacting not only operational efficiency but also stakeholder trust. Therefore, it is essential for companies to take proactive steps to enhance their disaster recovery strategies. By investing in robust solutions and developing comprehensive plans, organizations can significantly improve their resilience against potential crises.
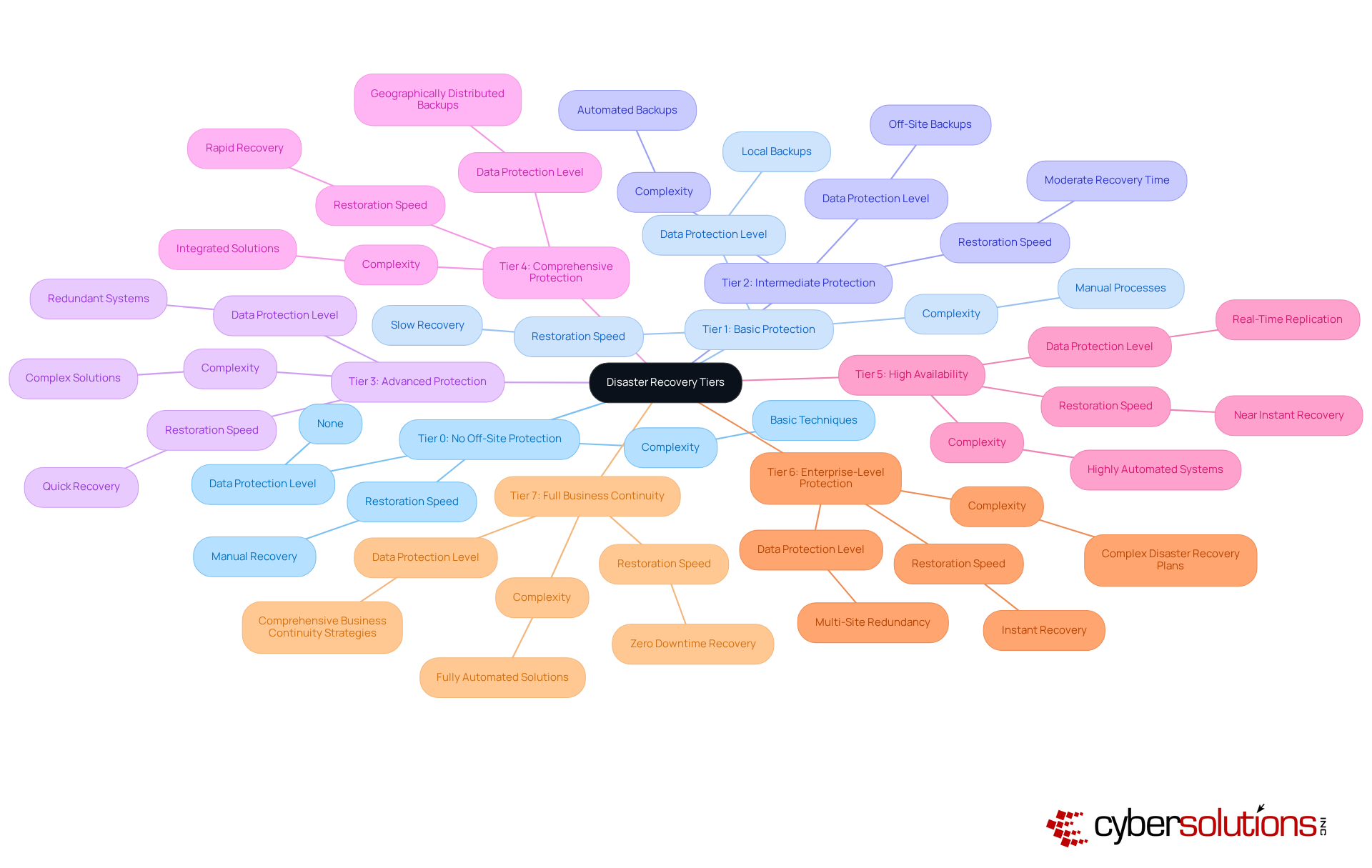
serve as a crucial framework that categorizes the various restoration capabilities an organization can implement. Understanding these tiers is not just beneficial; it’s essential for effective planning and ensuring business continuity. Each level within the tiers signifies a distinct degree of risk, restoration speed, and complexity, ranging from basic manual techniques to advanced automated solutions.
These levels, known as disaster recovery tiers, are typically labeled from 0 to 7. Level 0 indicates no off-site recovery, while Level 7 embodies extensive measures that are part of a comprehensive strategy to ensure minimal disruption during emergencies. This structured approach allows organizations to assess their current capabilities and identify areas for improvement within their disaster recovery plans.
By comprehending the tiers, entities can efficiently devise their strategies and allocate resources appropriately. Are you prepared to evaluate your organization’s recovery plan? The time to act is now.
are essential for enhancing business operations, particularly as organizations encounter an increasing range of cyber threats and natural disasters. In today’s landscape, where nearly 54% of businesses lack a disaster recovery plan, it’s crucial to adopt a structured approach. By classifying restoration strategies into tiers, companies can prioritize essential functions and allocate resources effectively. For instance, in the healthcare sector, patient data recovery is categorized within disaster recovery as Tier 1 due to its urgency and regulatory compliance requirements, such as HIPAA. This structured methodology not only safeguards critical operations but also boosts stakeholder confidence, showcasing the entity's commitment to resilience.
Real-world examples illustrate that organizations with clearly defined disaster recovery tiers experience shorter restoration times and improved operational continuity. This ultimately protects their reputation and ensures stability in an unpredictable environment. Consider this: how prepared is your organization to respond swiftly to incidents? Cyber Solutions emphasizes the importance of having a disaster recovery plan, such as having an available on-site team within 24 hours. This is essential for minimizing damage and enhancing restoration efforts.
Additionally, our monitoring and alert services provide proactive cybersecurity and threat prevention. This ensures that suspicious activities are detected and addressed before they escalate. By integrating compliance solutions into our offerings, we empower businesses to navigate regulatory requirements effectively, further solidifying their resilience against potential penalties and operational disruptions. In a world where the stakes are high, can you afford to be unprepared?
The evolution of disaster recovery tiers is crucial in today’s fast-paced technological landscape. Since the late 1980s, organizations have transitioned from basic backup solutions, often relying on physical storage media, to more sophisticated restoration strategies. This shift became necessary as technology advanced, prompting the SHARE Technical Steering Committee to introduce a framework of disaster recovery tiers that classifies restoration capabilities. This framework allows entities to systematically evaluate their readiness for emergencies by assessing their disaster recovery plans.
As we look at the current landscape, the rise of cloud computing and virtualization has transformed disaster recovery. Organizations now have access to adaptable and scalable solutions tailored to their specific operational needs and risk profiles. This evolution reflects a deeper understanding of crisis management, highlighting the importance of robust strategies and technologies in safeguarding assets.
However, the statistics are alarming: only 30% of organizations have a documented disaster recovery plan. This highlights an ongoing need for strong disaster recovery strategies. Moreover, a staggering 60% of companies experience downtime after a significant disaster. These figures emphasize the critical necessity of having a solid plan in place.
As cloud adoption continues to rise, with 88% of companies indicating that the public cloud will play a role in their future backup strategies, the landscape of disaster recovery in crisis management is evolving. This shift not only enhances restoration capabilities but also aligns with the growing recognition of the essential role that technology plays in maintaining business continuity.
Furthermore, the disaster recovery market is reaching $23.3 billion by 2027. This growth underscores the increasing significance and investment in disaster recovery solutions, making it imperative for organizations to prioritize their disaster restoration strategies.

Understanding the essential features of disaster recovery tiers is crucial for any organization aiming to safeguard its operations. Key elements such as recovery time objectives and recovery point objectives play a significant role in determining how quickly an organization can bounce back after a disaster. Each tier is characterized by its ability to minimize downtime and the amount of data that can be lost without causing substantial harm.
For example:
This distinction is vital for organizations to consider, as the recovery capabilities can vary significantly. Higher tiers typically require greater investments in technology and infrastructure, making it essential for decision-makers to carefully evaluate their options.
By grasping these elements, organizations can enhance their disaster recovery strategies, ensuring they are prepared for potential disruptions. This proactive approach not only enhances resilience but also aligns with the organization's overall risk management framework.
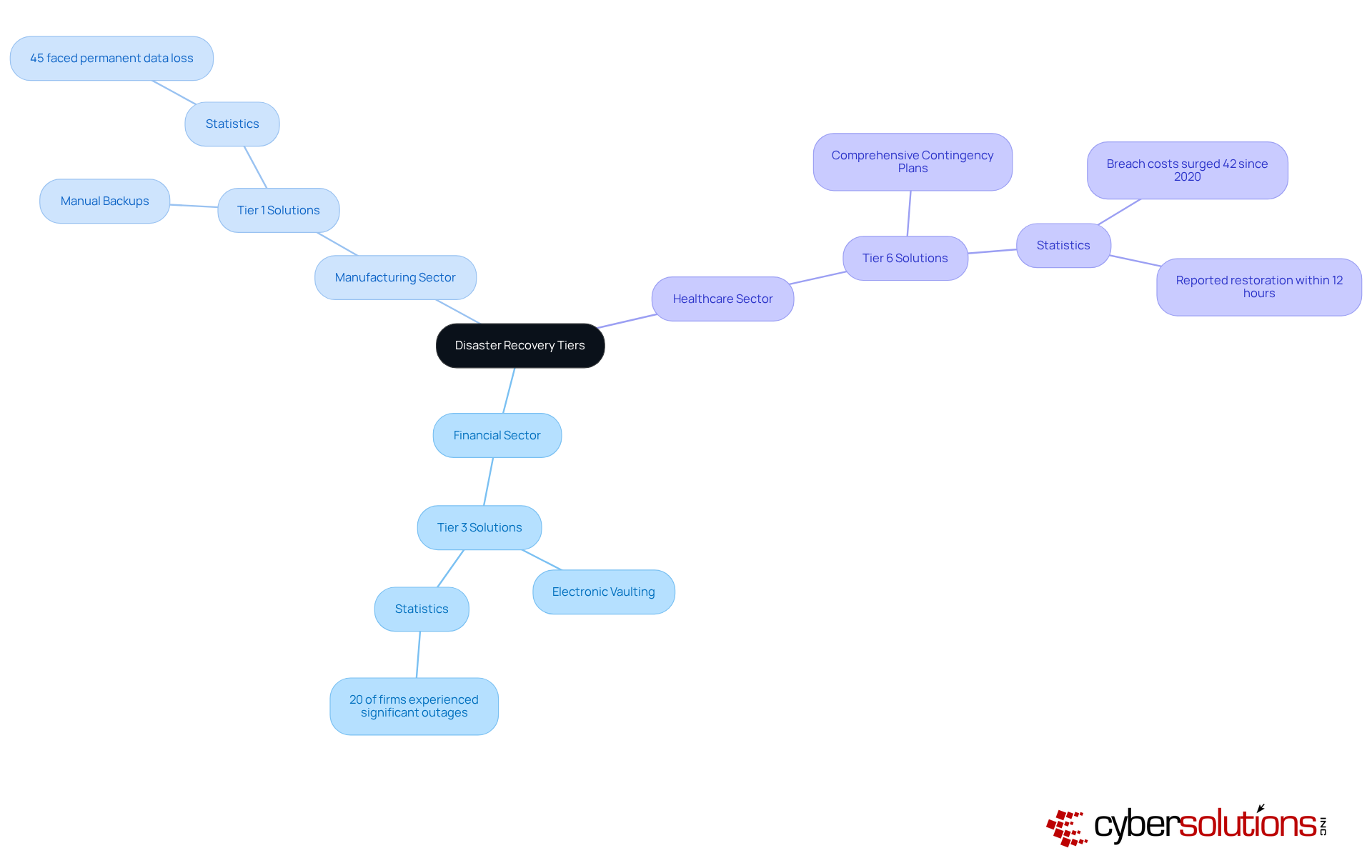
tiers are essential for organizations across diverse sectors, as each tailors solutions to meet specific operational needs and regulatory standards. In the financial sector, for instance, many companies adopt Tier 3 solutions, leveraging electronic vaulting to ensure the rapid retrieval of essential transaction data. This approach is vital, especially considering that 20% of firms reported experiencing a disruption in the past three years, underscoring the necessity for disaster recovery plans.
Conversely, smaller manufacturing firms often resort to Tier 1 solutions, relying on manual backups due to budget limitations. However, this choice carries risks; 45% of organizations have faced permanent data loss during incidents. The healthcare sector typically prioritizes higher tiers, such as Tier 6, to comply with stringent regulations and safeguard sensitive patient information. With soaring costs increasing by 42% since 2020, implementing robust recovery strategies is imperative.
Real-world case studies further illuminate these applications. For example, a healthcare provider that adopted Tier 6 solutions reported a remarkable reduction in restoration time, enabling them to restore critical systems within 12 hours after a severe incident. Similarly, a financial institution employing Tier 3 solutions showcased enhanced resilience, swiftly recovering vital transaction data during a cyber incident.
These examples underscore the adaptability and significance of disaster recovery tiers, empowering organizations to select solutions that align with their operational requirements and risk management strategies. By effectively implementing these tiers, businesses can bolster their resilience and ensure continuity amid disruptions.
Understanding disaster recovery tiers is crucial for organizations that want to protect their operations and ensure business continuity. These tiers provide a structured framework that categorizes restoration capabilities, enabling businesses to assess their preparedness and bolster resilience against various threats, from cyberattacks to natural disasters. By recognizing the significance of these tiers, organizations can prioritize critical functions and allocate resources effectively, ultimately safeguarding their reputation and financial stability.
The evolution of disaster recovery tiers has transformed from basic backup solutions to sophisticated, cloud-based strategies. Recovery time objectives (RTO) and recovery point objectives (RPO) are essential metrics that highlight how different tiers cater to varying operational needs. Consider the healthcare and finance sectors, where real-world applications illustrate the necessity of adopting appropriate tiers to comply with regulations and maintain operational integrity. How prepared is your organization to face these challenges?
In conclusion, the landscape of disaster recovery is rapidly evolving, making it essential for organizations to remain proactive in their planning. As the global market for disaster recovery solutions continues to grow, embracing these tiers not only enhances resilience but also aligns with comprehensive risk management strategies. Organizations are encouraged to evaluate their disaster recovery capabilities and invest in robust solutions that ensure they are well-prepared to face unexpected disruptions.
What are disaster recovery tiers?
Disaster recovery tiers are a framework that categorizes the various restoration capabilities an organization can implement, indicating different levels of data protection, restoration speed, and complexity.
How are disaster recovery tiers labeled?
Disaster recovery tiers are typically labeled from 0 to 7, where Level 0 indicates no off-site data protection and Level 7 represents extensive business continuity strategies.
Why are disaster recovery tiers important for organizations?
They are essential for effective data safeguarding and ensuring business continuity, helping organizations assess their current capabilities and identify areas for improvement.
How do disaster recovery tiers enhance business resilience?
They allow organizations to prioritize essential functions, allocate resources effectively, and respond to an increasing range of cyber threats and natural disasters.
Can you provide an example of how disaster recovery tiers are applied in specific sectors?
In the healthcare sector, patient data restoration is categorized as Tier 1 due to its urgency and regulatory compliance requirements, such as HIPAA.
What benefits do organizations with defined disaster recovery tiers experience?
They typically experience shorter restoration times, improved operational continuity, and enhanced reputation and financial stability in unpredictable environments.
What is the significance of having an incident response team?
An incident response team available on-site within 24 hours is essential for minimizing damage and enhancing restoration efforts during incidents.
How does Cyber Solutions support businesses in disaster recovery?
Cyber Solutions provides 24/7 network monitoring and alert services for proactive cybersecurity and threat prevention, as well as Compliance as a Service (CaaS) to help navigate regulatory requirements.