
In today’s interconnected world, the urgency of robust cybersecurity measures is paramount, especially in the healthcare sector where cyber threats are ever-present. Internal vulnerability scanning stands out as a crucial practice that not only uncovers weaknesses within an organization’s network but also strengthens defenses against potential breaches. Yet, many executives find themselves questioning how to implement these scans effectively and ensure ongoing protection.
What best practices can organizations adopt to elevate vulnerability scanning from a mere compliance task into a strategic advantage that enhances their overall security posture? By understanding the current landscape of cybersecurity threats, healthcare organizations can better navigate the complexities they face.
Consider this: healthcare data breaches can lead to significant financial losses and damage to reputation. With the stakes so high, it’s essential for CFOs and executives to recognize that vulnerability scanning is not just about meeting regulatory requirements; it’s about safeguarding sensitive information and maintaining trust with patients.
To address these challenges effectively, Cyber Solutions can provide tailored strategies that transform vulnerability scanning into a proactive measure. By leveraging data and case studies, organizations can see the tangible benefits of a robust cybersecurity framework.
In conclusion, the time to act is now. Embracing best practices in vulnerability scanning can not only protect healthcare organizations from cyber threats but also position them as leaders in security and compliance.
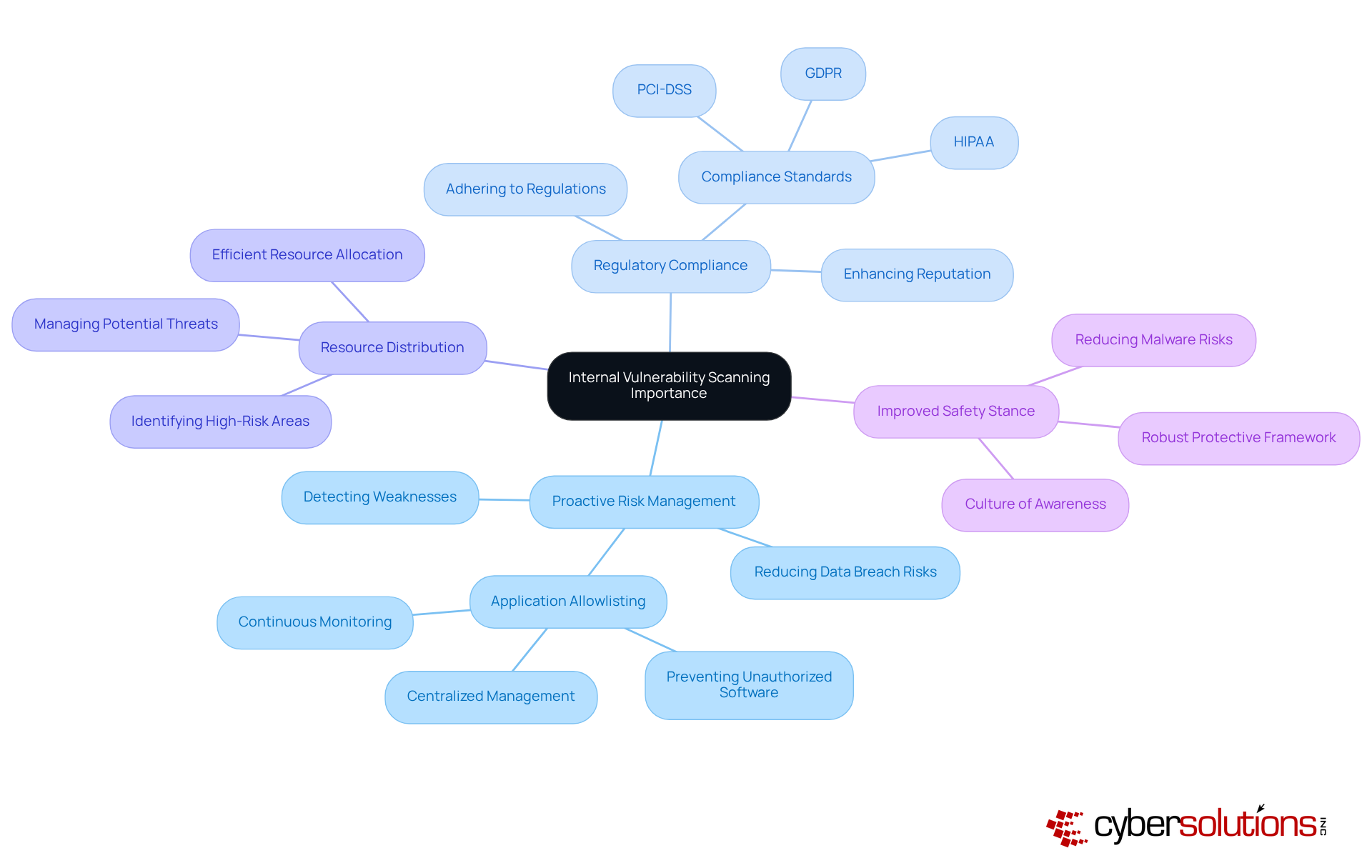
In today's digital landscape, the importance of cybersecurity cannot be overstated, especially for healthcare organizations. Internal vulnerability scanning is a systematic procedure that detects, evaluates, and ranks vulnerabilities within a company's internal network. This practice is essential for several reasons:
In summary, internal vulnerability scanning is a vital component of a comprehensive cybersecurity strategy. It empowers organizations to protect their assets and maintain operational integrity while ensuring compliance and proactive defense against emerging threats. Are you ready to strengthen your cybersecurity posture?
In today's digital landscape, the importance of cybersecurity cannot be overstated, especially for healthcare organizations. With the rise of cyber threats, CFOs face unique challenges that demand immediate attention and action. To effectively conduct internal vulnerability scans, organizations should adhere to the following best practices:
By applying these optimal strategies, companies can enhance their threat management procedures through proactive measures and significantly reduce their risk exposure, effectively addressing the critical issues posed by evolving cyber threats.

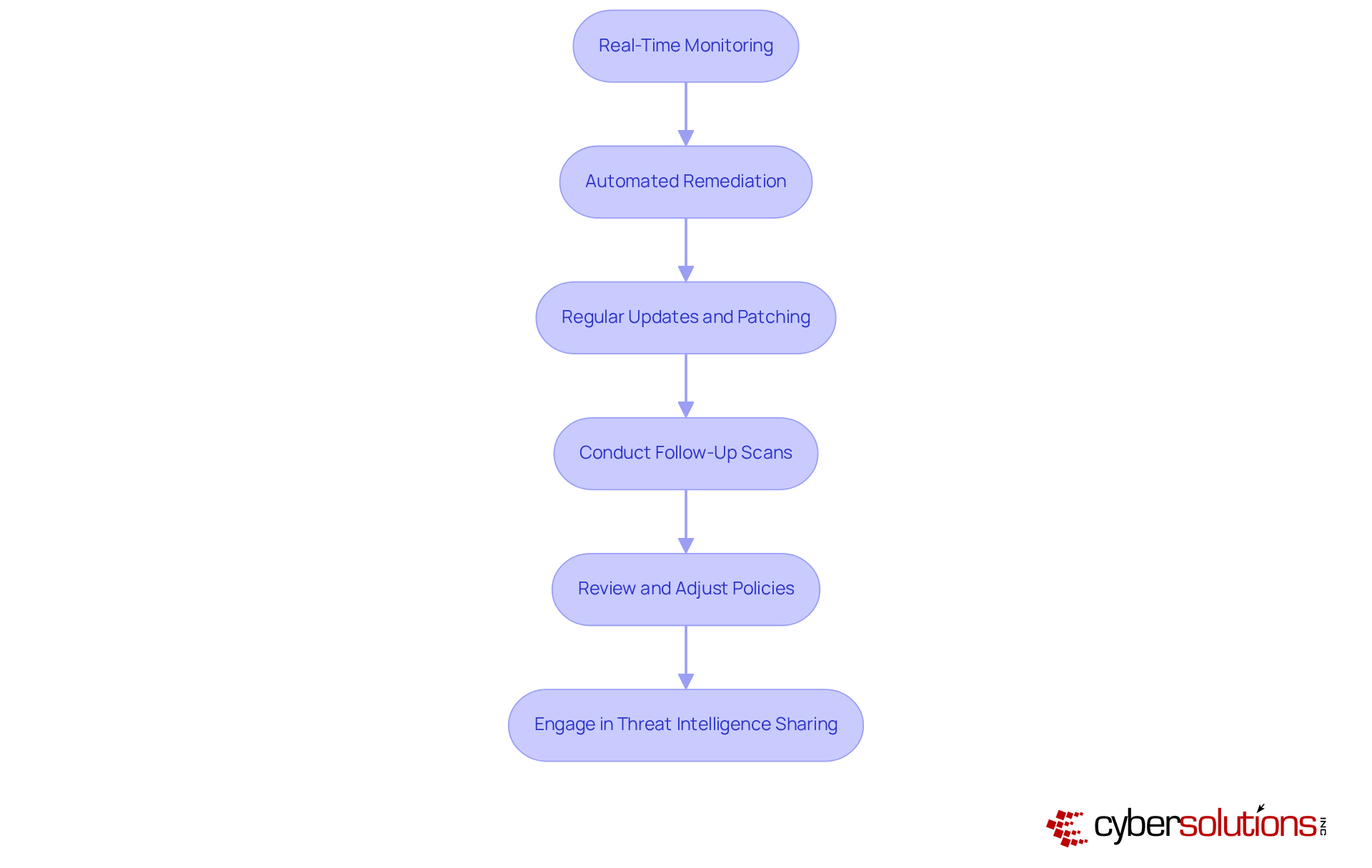
In today's rapidly evolving digital landscape, the importance of cybersecurity cannot be overstated, especially in the healthcare sector. Organizations must not only identify vulnerabilities but also implement robust security measures along with remediation strategies to fortify their security posture. Here’s how:
By committing to continuous monitoring and proactive remediation, organizations can significantly bolster their cybersecurity resilience, safeguarding critical assets against evolving threats. Are you ready to take the necessary steps to protect your organization?
Internal vulnerability scanning stands as a cornerstone of cybersecurity, especially for organizations in the healthcare sector. In a landscape where cyber threats are ever-evolving, it’s crucial for these organizations to protect their internal networks from potential dangers. By systematically identifying and addressing vulnerabilities, companies not only safeguard sensitive data but also bolster their overall security posture and ensure compliance with regulatory standards.
Consider the implications: proactive risk management is essential. Vulnerability scanning not only facilitates this but also underscores the importance of adhering to regulatory requirements. Efficient resource allocation becomes paramount, as organizations must navigate the complexities of their security needs. Best practices for conducting effective scans include:
These practices are vital for cultivating a culture of security awareness and preparedness within organizations.
The significance of internal vulnerability scanning cannot be overstated. As cyber threats continue to evolve, organizations must prioritize these strategies to protect their assets and maintain operational integrity. Are you ready to take action? Implementing robust scanning and remediation practices now will not only mitigate risks but also position organizations for long-term success in an increasingly complex digital landscape. The time to act is now.
What is internal vulnerability scanning?
Internal vulnerability scanning is a systematic procedure that detects, evaluates, and ranks vulnerabilities within a company's internal network.
Why is internal vulnerability scanning important for organizations?
It is important because it allows organizations to proactively manage risks, comply with regulations, allocate resources efficiently, and improve their overall safety stance.
How does internal vulnerability scanning contribute to proactive risk management?
By recognizing weaknesses before they can be exploited, organizations can effectively reduce risks, significantly lowering the chances of data breaches and related financial losses.
What role does application allowlisting play in internal vulnerability scanning?
Application allowlisting prevents unauthorized software from executing, minimizing the attack surface and enhancing security through features like centralized management and continuous monitoring.
How does internal vulnerability scanning help with regulatory compliance?
Many industries have regulations that require regular vulnerability assessments. Adhering to these regulations helps prevent penalties and enhances the organization's reputation.
In what way does understanding vulnerabilities assist in resource distribution?
By identifying where vulnerabilities exist, organizations can allocate resources more efficiently, focusing on high-risk areas that need immediate attention.
What is the impact of routine assessments on an organization's safety stance?
Routine assessments contribute to a robust protective framework and foster a culture of awareness and continuous improvement, significantly reducing the risk of malware.
What is the overall benefit of internal vulnerability scanning in cybersecurity?
It empowers organizations to protect their assets, maintain operational integrity, ensure compliance, and proactively defend against emerging threats.