
In a world where cyber threats are not just a possibility but a reality, organizations must elevate their cybersecurity strategies to protect sensitive information. The role of external vulnerability scanners is crucial in this proactive defense, allowing businesses to pinpoint and address weaknesses before they can be exploited by malicious actors. Yet, the path to effectively implementing these scanners is riddled with challenges and complexities, leaving many organizations exposed.
How can companies navigate this intricate landscape to ensure robust protection against the ever-evolving threat of cyberattacks? The stakes are high, and the consequences of inaction can be devastating. By understanding the unique challenges they face, organizations can take decisive steps toward fortifying their defenses and safeguarding their assets.
In today’s digital age, cybersecurity is not just an option; it’s a necessity, especially in healthcare. An external vulnerability scanner serves as a crucial proactive safeguard, allowing organizations to identify flaws in their systems, networks, and applications before attackers can exploit them. With hackers launching attacks approximately every three seconds and increasing sophistication of threats, the urgency for robust security measures has never been greater. These assessments are vital for organizations to effectively gauge their protective measures against escalating threats.
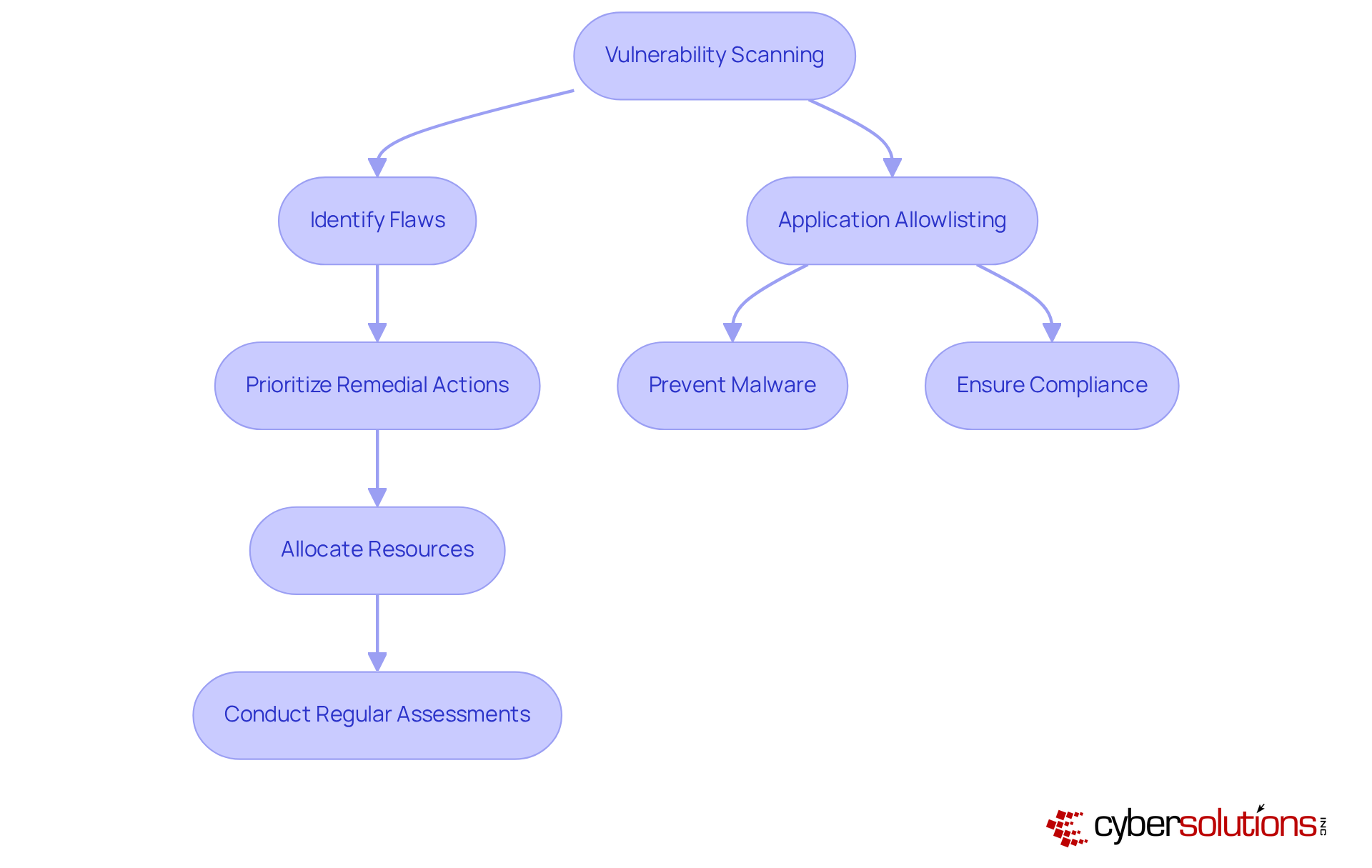
By conducting vulnerability assessments, companies can pinpoint specific weaknesses within their infrastructure. This allows them to prioritize remedial actions and allocate resources more effectively. Such a proactive approach not only helps maintain security but also plays a critical role in risk management. For instance, organizations that have embraced vulnerability scanning have seen significant improvements, reducing the likelihood of data breaches and enhancing overall operational efficiency.
In addition to threat scanning, application allowlisting is essential. By ensuring that only approved applications can operate on a network, it actively prevents malware, ransomware, and unauthorized software from executing. This dual strategy not only mitigates vulnerabilities but also aids organizations in meeting stringent compliance standards, particularly those required for federal contracts. Experts advocate for regular security scans with an external vulnerability scanner, recommending they be conducted monthly or quarterly, as these evaluations provide a roadmap for identifying and addressing potential risks. This practice not only protects a company’s reputation but also contributes to its financial stability by minimizing the risks associated with cyber incidents.
As the cybersecurity landscape continues to evolve, integrating risk assessment and application allowlisting into an organization’s security strategy is not merely beneficial; it’s essential for long-term success. Are you prepared to take the necessary steps to fortify your organization against these ever-present threats?
In today’s digital landscape, the importance of cybersecurity cannot be overstated, especially for organizations navigating the complexities of using an external vulnerability scanner. However, implementing an external vulnerability scanner presents several challenges that must be effectively addressed to ensure security.
By strategically addressing these challenges and managing resources efficiently, organizations can significantly enhance their threat assessment processes and bolster their overall cybersecurity stance.

To effectively implement an external vulnerability scanner, it’s crucial to consider the appropriate tools and resources that can enhance your security posture.
Here are some popular options:
Documentation and Guides: Leverage vendor documentation and online resources to gain insights into the features and best practices for each tool. Websites like OWASP and various cybersecurity blogs offer information that can enhance your understanding of risk management.
Community Engagement: Engage with cybersecurity communities on platforms such as Reddit or Spiceworks. These forums present opportunities to share experiences, seek advice, and learn from the challenges faced by peers in the industry.
Training and Certification: Investing in training programs or certifications for your IT staff can significantly enhance their skills in vulnerability scanning and assessment techniques. This investment not only boosts team capability but also fosters a culture of safety awareness within the organization.
Regulatory Compliance: Utilize relevant standards to your industry to ensure that your scanning processes align with regulatory requirements. This proactive approach helps mitigate risks associated with non-compliance and strengthens your overall security posture.

Implementing an external vulnerability scanner is not just a step; it’s a vital leap for organizations striving to bolster their cybersecurity defenses. In a landscape where cyber threats are not only sophisticated but also alarmingly frequent, proactively identifying and addressing potential weaknesses is essential. This approach not only safeguards sensitive information but also ensures compliance with industry regulations, which is paramount in today’s digital age.
This guide outlines key steps for effective implementation, including:
Each step is crucial in maximizing the effectiveness of vulnerability scanning. Moreover, tackling challenges such as false positives and resource allocation is necessary to enhance the overall impact of these efforts. By utilizing the right tools and engaging with community resources, organizations can significantly strengthen their cybersecurity posture.
Ultimately, integrating an external vulnerability scanner into an organization’s security strategy transcends mere compliance; it’s about establishing a robust defense against the ever-evolving cyber threats. Organizations must prioritize vulnerability scanning as a foundational element of their cybersecurity framework. This commitment fosters a culture of continuous improvement and vigilance, ensuring that digital assets remain secure in an unpredictable environment.
What is vulnerability scanning and why is it important?
Vulnerability scanning is a proactive cybersecurity measure that helps organizations identify flaws in their systems, networks, and applications before they can be exploited by attackers. It is crucial for maintaining security, especially in the healthcare sector, where the risk of cyberattacks is high.
How frequently should organizations conduct vulnerability scans?
Experts recommend conducting vulnerability scans with an external scanner monthly or quarterly to effectively identify and address potential risks.
What are the benefits of conducting regular security assessments?
Regular security assessments help organizations pinpoint specific weaknesses, prioritize remedial actions, maintain compliance with regulations (like HIPAA and PCI-DSS), and significantly improve their security posture, thereby reducing the likelihood of data breaches.
What role does application allowlisting play in cybersecurity?
Application allowlisting ensures that only approved applications can run on a network, preventing malware, ransomware, and unauthorized software from executing. This strategy helps mitigate vulnerabilities and aids in meeting compliance standards.
How does vulnerability scanning contribute to an organization's financial stability?
By minimizing the risks associated with cyber incidents through regular threat assessments, vulnerability scanning helps protect a company’s reputation and reduces potential financial losses from data breaches and other cyber threats.
Why is it necessary for organizations to integrate risk assessment and application allowlisting into their security strategy?
Integrating these measures is essential for long-term success in cybersecurity, as they provide a robust defense against evolving threats and help organizations maintain compliance with industry standards.