
Custom software has emerged as a pivotal element for organizations striving to maintain a competitive edge in a rapidly evolving digital landscape. These tailored solutions not only address specific operational challenges but also enhance efficiency and adaptability, allowing businesses to respond swiftly to market changes. As the demand for personalized applications grows, leaders must grapple with the complexities of implementation and the potential pitfalls of off-the-shelf alternatives.
What are the critical considerations for leveraging custom software to drive innovation and secure long-term success?
Business custom software represents tailored solutions meticulously crafted to address the distinct needs and requirements of a company. Unlike ready-made applications that cater to a broad audience, these solutions are developed from the ground up to resolve specific challenges, enhance efficiency, and integrate seamlessly with existing systems. This bespoke methodology empowers businesses to optimize their processes and achieve strategic objectives more effectively by utilizing business custom software.
The demand for business custom software is on the rise, with approximately 56% of organizations opting for tailored applications over standard offerings. This transition is fueled by the need for flexibility, security, and the capacity to adapt to changing business needs with business custom software. For example, in the healthcare sector, personalized applications can incorporate patient management features, while in finance, tailored solutions can bolster risk assessment capabilities.
Incorporating security measures, such as encryption, is critical in the development of custom applications. This approach proactively prevents unauthorized programs from executing, significantly mitigating the risk of malware and ransomware attacks. Key features include:
This proactive approach not only safeguards sensitive information but also aids organizations in meeting stringent compliance standards, including HIPAA and PCI-DSS, which are vital for maintaining government contract eligibility and protecting federal data.
Expert opinions underscore the importance of business custom software in fostering innovation and growth. As companies increasingly aim to leverage advanced technologies like AI and machine learning, the development of custom solutions becomes essential. Furthermore, embedding security throughout the application development lifecycle is crucial to addressing the evolving challenges that businesses face. By investing in business custom software development, organizations can streamline their operations and gain a competitive advantage in their respective industries.
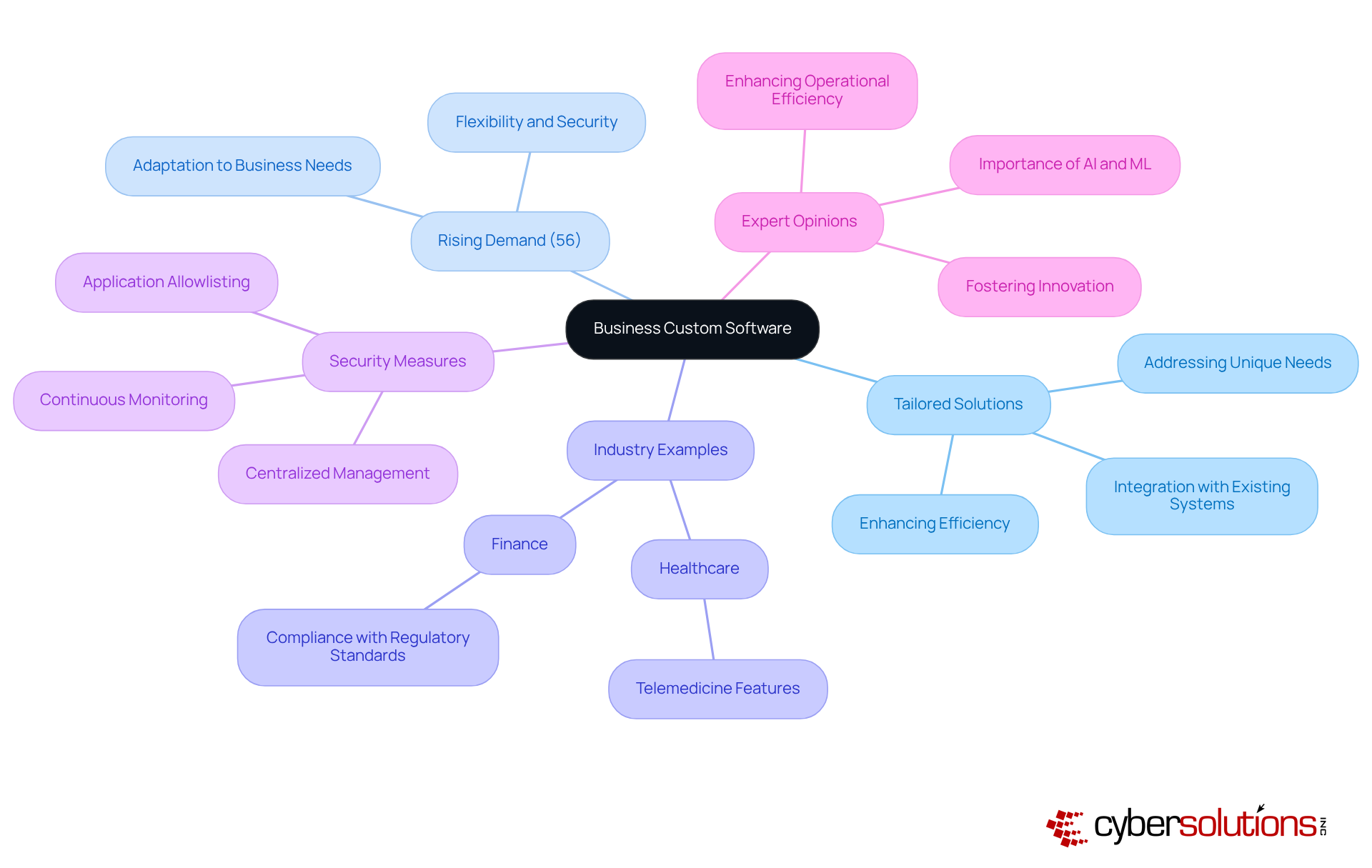
Business custom software is crucial for organizations aiming to secure a competitive advantage by aligning technology with specific business objectives. In an era where digital transformation is imperative, solutions that empower businesses to enhance operations, elevate customer experiences, and swiftly adapt to market dynamics. Consider healthcare, for example; they can utilize tailored applications to streamline patient data management, ensuring efficiency while improving service delivery.
Tailored IT services from Cyber Solutions specifically address the needs of industries such as healthcare and finance, safeguarding operations with essential tools like:
This adaptability is vital in today’s fast-paced business landscape, as off-the-shelf solutions frequently fall short of meeting the requirements addressed by business custom software. With investments projected to reach 2.8 trillion U.S. dollars by 2027, organizations investing in business custom software are better positioned to leverage technology for sustained growth and efficiency.
Moreover, the creation of scalable solutions, enabling companies to modify and incorporate features as they grow, ensuring the application remains beneficial and cost-effective over time.

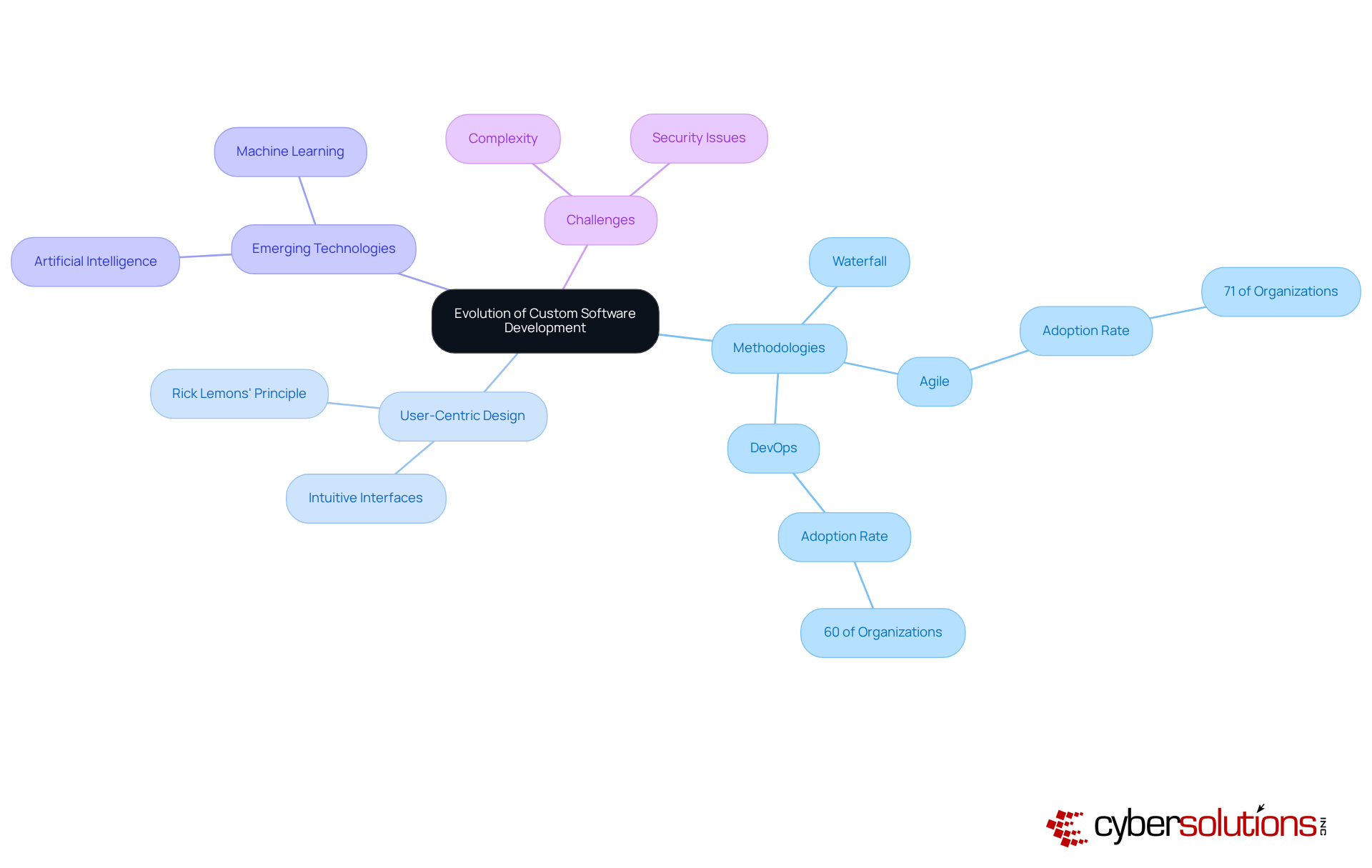
Custom application development has undergone a transformative shift over the past few decades, moving from traditional waterfall methodologies to embrace agile and DevOps practices. Once considered a luxury reserved for large corporations with extensive budgets, custom software solutions have become increasingly accessible, thanks to technological advancements and the proliferation of cloud computing. This democratization empowers small and medium-sized enterprises to invest in business custom software that meets their specific needs.
The transition towards agile methodologies is noteworthy, with a significant 71% of organizations adopting agile practices in some capacity, underscoring a growing recognition of its advantages in fostering flexibility and responsiveness. Agile emphasizes rapid production cycles and iterative progress, enabling teams to swiftly adapt to changing requirements and user feedback. As Kent Beck aptly states, "The only way to go fast is to go well," encapsulating the essence of agile methodology. Similarly, DevOps practices, which integrate software development and operations, have gained momentum, with 60% of organizations reporting improved collaboration and efficiency as a result.
Expert insights highlight the critical role of these methodologies. Industry leaders assert that agile and DevOps not only enhance the development process but also cultivate a culture of innovation. This is particularly evident in organizations that prioritize user-focused design, ensuring solutions are not only functional but also intuitive and engaging. Rick Lemons emphasizes that systems should not require users to input information that is already known, reinforcing the importance of user-centric design in application development.
Current trends reveal a strong emphasis on incorporating artificial intelligence and machine learning into custom applications. This integration significantly enhances application capabilities, enabling businesses to harness data-driven insights for improved decision-making and operational efficiency. Richard Stallman explores the relationship between creativity and the freedom to utilize program outcomes, suggesting that promoting freedom in program usage can stimulate creativity and innovation in development.
As organizations transition from waterfall to agile methodologies, they are beginning to recognize the advantages of adaptability and speed in application development. This evolution not only enhances the quality of the final product but also aligns development efforts more closely with business objectives, ultimately delivering greater value across various sectors. However, as Ray Ozzie warns, complexity can impede productivity and introduce security challenges, emphasizing the need for diligent oversight of development processes.
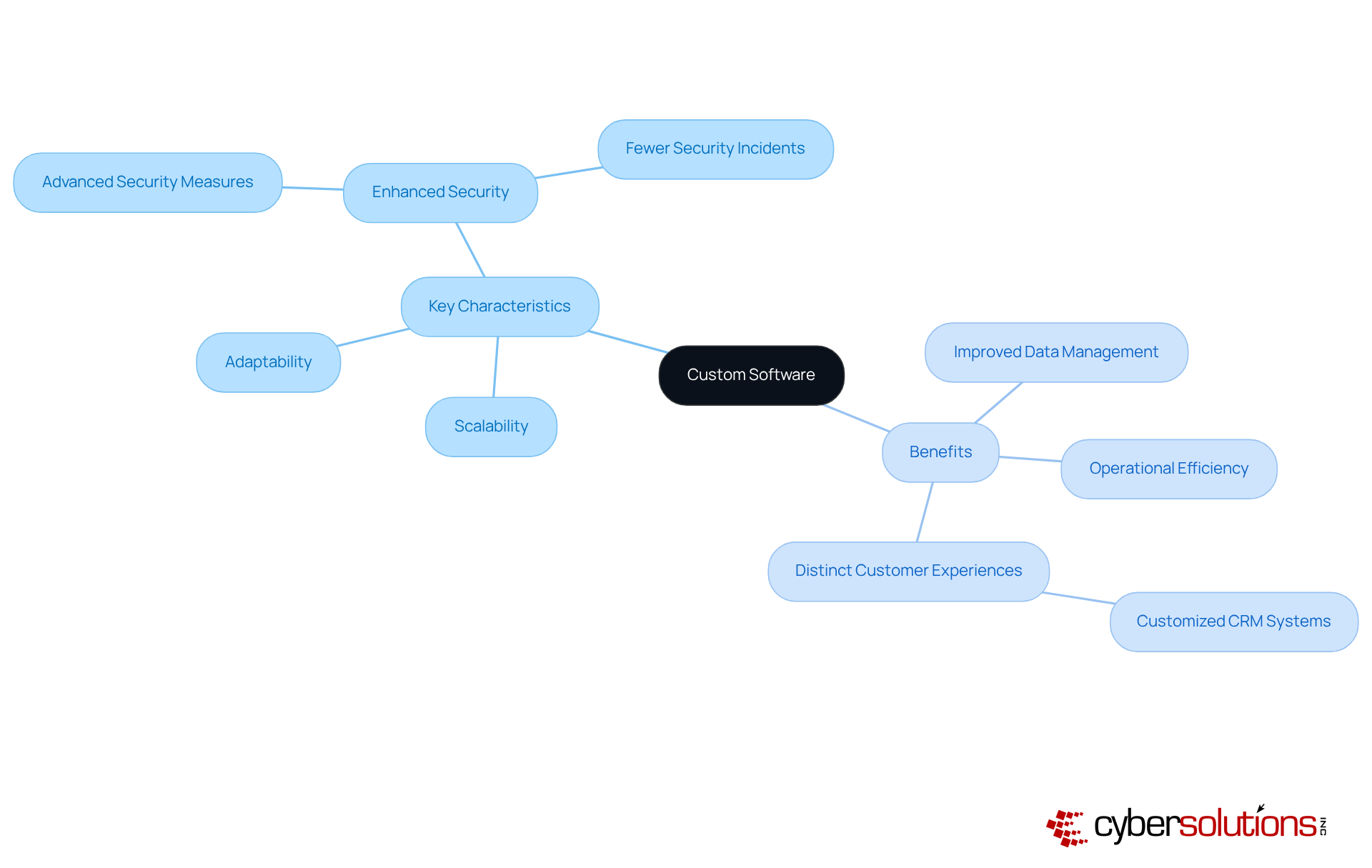
is characterized by its scalability, adaptability, and functionality, positioning it as a superior alternative to off-the-shelf solutions. Designed to evolve alongside a company, custom software can seamlessly adjust to shifting requirements and user expectations, ensuring that enterprises remain agile in a competitive landscape. In sectors such as healthcare and finance, where security is paramount, bespoke applications incorporate features specifically tailored to address vulnerabilities, thereby significantly reducing the likelihood of breaches. Notably, research indicates that organizations utilizing custom software experience fewer security incidents compared to those relying on standard applications, which often lack critical protections against emerging cyber threats.
The advantages of adopting tailored applications extend well beyond security concerns. Businesses frequently report enhanced efficiency, improved data management, and the capacity to deliver distinctive customer experiences thanks to customization. A prime example is the implementation of a customized analytics tool, which can provide insights specifically tailored to a business's customer interactions. This degree of personalization not only fosters more effective marketing strategies but also propels increased sales, with companies witnessing growth following the adoption of custom solutions. By investing in custom software, businesses strategically position themselves to optimize operations and maintain a competitive edge.
When implementing custom software, organizations must assess several critical factors, including budget, timeline, and stakeholder involvement. A thorough needs assessment is essential to ensure that the application aligns with business objectives. Engaging stakeholders throughout the development process not only facilitates smoother adoption but also enhances integration into existing systems. Furthermore, organizations must prepare for ongoing maintenance and updates, as technology and business needs are continually evolving. By addressing these considerations, businesses can maximize the benefits of their custom software solutions and secure long-term success.

In today's competitive landscape, custom software is indispensable, offering tailored solutions that meet the unique needs of organizations. Unlike generic applications, custom software is meticulously crafted to enhance operational efficiency, bolster security, and ensure seamless integration with existing systems. This bespoke approach empowers businesses to streamline processes and achieve their strategic goals with greater effectiveness.
The rising demand for custom software is driven by the need for flexibility and adaptability in a rapidly evolving environment. The critical importance of robust cybersecurity measures is underscored, alongside the evolution of development methodologies, particularly the shift towards agile practices that promote innovation and responsiveness. The myriad benefits of custom software—including enhanced operational efficiency, improved customer experiences, and scalability—underscore its vital role in driving business success.
Organizations are urged to recognize the long-term advantages of investing in custom software solutions. As digital transformation reshapes industries, businesses that prioritize tailored applications will be better positioned to navigate challenges, leverage emerging technologies, and maintain a competitive edge. Embracing custom software is not merely a strategic choice; it is a crucial step toward achieving sustained growth and operational excellence in an increasingly complex business landscape.
What is business custom software?
Business custom software refers to tailored solutions specifically designed to meet the unique needs and requirements of a company, developed from the ground up to address specific operational challenges and enhance efficiency.
Why is there a growing demand for business custom software?
The demand for business custom software is increasing because approximately 56% of organizations prefer tailored applications for their flexibility, security, and ability to adapt to changing business needs.
How does business custom software benefit different industries?
In industries like healthcare, custom software can include telemedicine features, while in finance, it can help ensure compliance with regulatory standards, thereby enhancing operational efficiency and service delivery.
What cybersecurity measures are important in custom software development?
Robust cybersecurity measures, such as application allowlisting, are critical. This approach helps prevent unauthorized programs from executing, thereby reducing the risk of malware and ransomware attacks.
What are the key features of application allowlisting?
Key features of application allowlisting include continuous monitoring of application activity and centralized management of allowlists to identify and block threats immediately.
How does business custom software contribute to compliance standards?
Custom software development incorporates strong security measures that help organizations meet stringent compliance standards, such as HIPAA and PCI-DSS, which are essential for protecting sensitive information and maintaining eligibility for government contracts.
What role does business custom software play in innovation?
Business custom software fosters innovation by allowing companies to leverage advanced technologies like AI and machine learning, thus enhancing operational efficiency and providing a competitive advantage.
How does custom software align with digital transformation?
Custom software aligns with digital transformation by providing tailored technological solutions that enhance operations, improve customer experiences, and allow businesses to quickly adapt to market changes.
What are the advantages of creating tailored applications?
Tailored applications offer scalability and adaptability, enabling companies to modify and incorporate new features as they grow, ensuring the software remains beneficial and cost-effective over time.
What is the projected investment in digital transformation by 2027?
Digital transformation expenditures are projected to reach 2.8 trillion U.S. dollars by 2027, indicating a significant investment trend in technology that supports sustained growth and efficiency for organizations.