
Understanding the motivations behind hacking is crucial in the current landscape of cybersecurity threats. A complex interplay of factors drives individuals to breach digital defenses, ranging from:
These motivations not only shape the actions of hackers but also carry profound implications for individuals and organizations alike. As cybercrime escalates, organizations must confront a pressing question: how can they effectively anticipate and counteract these diverse motivations? By safeguarding their assets and ensuring robust cybersecurity, they can protect themselves against the evolving threats posed by malicious actors.
The question of why hackers hack can be understood through a complex array of motivations, broadly categorized into:
Financially driven individuals, often referred to as cybercriminals, exploit vulnerabilities for monetary gain through methods such as ransomware, data theft, and fraud. The staggering losses from cybercrime alone have surpassed billions in 2025, underscoring the financial stakes involved.
Hacktivists, known as hacktivists, utilize their skills to advocate for political agendas or social causes, targeting entities they deem unethical. Recent attacks on major retailers like Marks and Spencer and The Co-op illustrate the disruptive impact of ideological hacking on business operations.
Furthermore, some hackers are motivated by the thrill of hacking, viewing hacking as a game. This thrill-seeking behavior can lead to significant breaches, exemplified by the resurgence of teenage hacking gangs in English-speaking countries.
Understanding motivations is essential for organizations to effectively combat hacking, enabling them to anticipate potential threats and allocate resources appropriately. A proactive approach, such as implementing robust security measures, is critical in this context. By preventing unauthorized applications from executing, organizations can significantly reduce their attack surface and minimize vulnerabilities, making it increasingly difficult for attackers to exploit systems.
As Stéphane Nappo, a Global Chief Information Security Officer, aptly stated, 'Cybersecurity is much more than a matter of IT—it’s a business imperative.' Understanding motivations enables us to recognize the varied motivations of cybercriminals, which not only informs defensive strategies but also fosters a proactive approach to cybersecurity.

Hackers can be categorized into distinct groups based on their intentions and methods, underscoring the critical importance of cybersecurity. White-hat specialists, also known as ethical hackers, play a vital role in enhancing protection systems by proactively identifying weaknesses before they can be exploited by malicious actors. Their contributions are increasingly recognized, with organizations reporting a significant reduction in breaches when ethical hackers are involved. For instance, Delaware has engaged ethical firms for cybersecurity assessments, resulting in fortified defenses and the closure of vulnerabilities before cybercriminals can capitalize on them. Elayne Starkey, Delaware’s chief security officer, stated, "The results of these tests allow us to tighten up our defenses and close gaps before the real bad guys find them."
Conversely, black-hat hackers engage in illegal activities for personal gain, often inflicting substantial harm on individuals and organizations. The repercussions of their actions can be severe; for example, a series of cyberattacks on UK retailers in 2023 caused operational disruptions and financial losses, highlighting the urgent need for robust cybersecurity measures. In this context, antivirus software is essential, as it actively prevents malware and unauthorized software from executing, thereby significantly reducing the attack surface and minimizing vulnerabilities that malicious actors seek to exploit.
Gray-hat hackers occupy a morally ambiguous space, occasionally breaching laws or ethical norms without harmful intent. Understanding these distinctions is crucial for organizations aiming to develop targeted cybersecurity strategies that effectively address threats, as well as the specific methods and objectives of each type of attacker. With cybercrime projected to increase by 2025, the importance of a comprehensive cybersecurity framework, supported by ethical programmers and proactive strategies like penetration testing, cannot be overstated. This approach not only mitigates risks but also fosters a culture of continuous improvement in security practices, ensuring compliance with regulations such as GDPR. In summary, cybersecurity serves as a fundamental protective measure against the diverse risks posed by various types of hackers, highlighting the necessity for comprehensive security strategies.

The significance of cybersecurity cannot be overstated, particularly when pondering why hackers hack, as the consequences of hacking extend far beyond immediate financial losses, profoundly affecting both individuals and organizations. For individuals, data breaches lead to identity theft, substantial financial loss, and emotional distress, leaving a lasting mark on their lives. Organizations face a multifaceted array of repercussions, including operational disruptions, legal liabilities, and significant reputational damage. In the healthcare sector, the stakes are particularly high; breaches not only compromise sensitive patient data but also violate privacy regulations, resulting in hefty fines.
Recent incidents underscore this alarming trend:
The financial implications are staggering, with the average cost of a data breach reaching millions. Moreover, 93% of healthcare institutions reported experiencing at least one cyberattack in the previous year, raising concerns about why hackers hack and emphasizing the urgent need for improved cybersecurity measures.
The cumulative effect of these outcomes underscores the necessity for businesses to prioritize digital security. It is imperative that they adopt robust measures to mitigate risks and protect their assets effectively. As the landscape of cyber threats continues to evolve, healthcare organizations must remain vigilant and proactive in safeguarding their critical information.

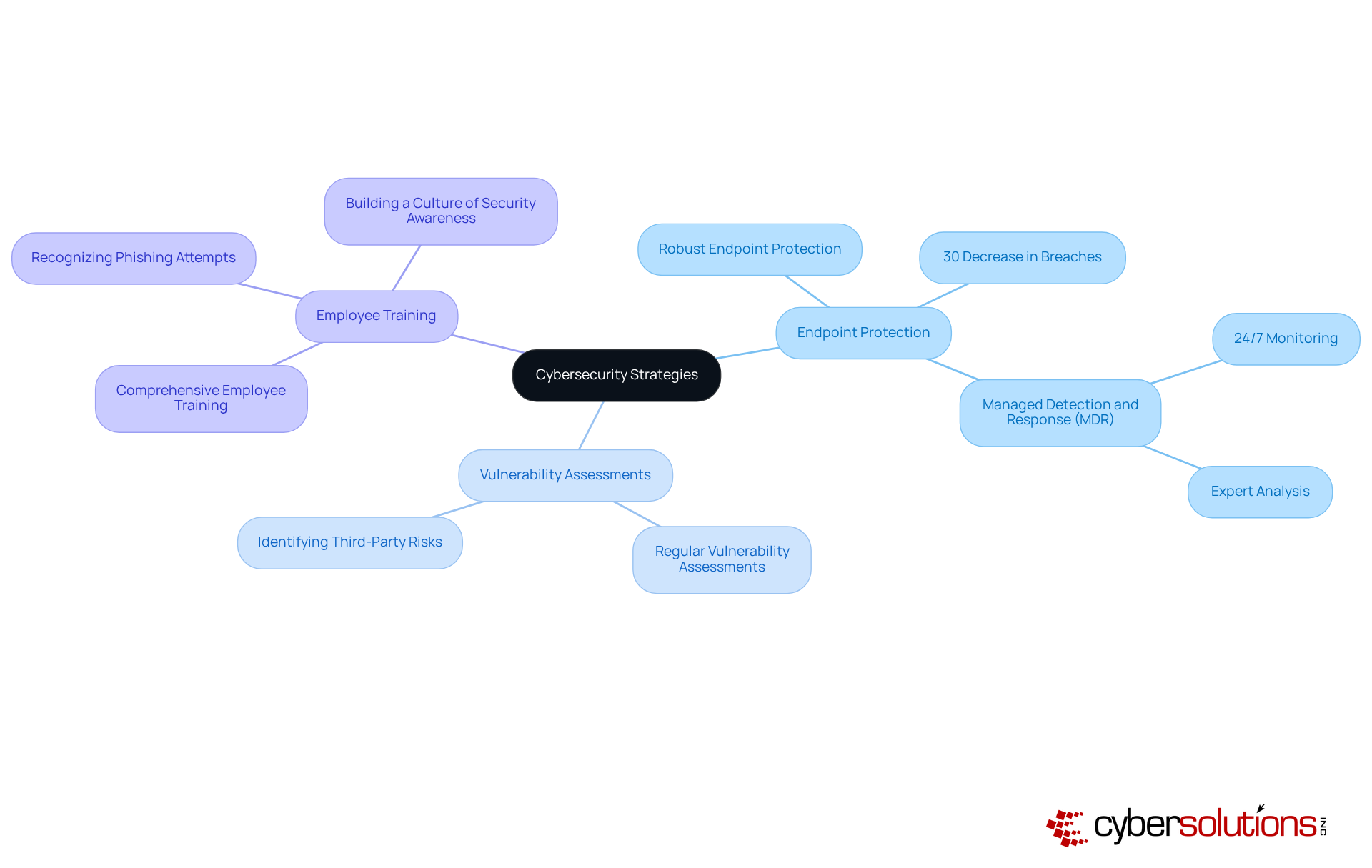
To effectively combat hacking, organizations must adopt a multi-layered cybersecurity approach that encompasses:
Cybersecurity is particularly critical, serving as the first line of defense against cyber threats. In 2025, statistics reveal that organizations with endpoint detection and response solutions experience a 30% decrease in successful breaches compared to those relying solely on conventional protective measures.
Employing managed protective services significantly enhances threat identification and response capabilities, enabling organizations to swiftly address potential breaches. For instance, companies that implement these services benefit from 24/7 monitoring and expert analysis, markedly improving their security posture. Additionally, adopting compliance frameworks aids organizations in navigating complex regulatory frameworks, ensuring compliance while minimizing risks associated with data breaches.
By investing in these strategies, organizations not only improve their security but also demonstrate a commitment to safeguarding sensitive information. This proactive approach not only enhances their reputation but also fosters trustworthiness in the market, making them more resilient against evolving threats.
In today's digital age, the importance of cybersecurity in healthcare cannot be overstated. Understanding the motivations behind hacking reveals a multifaceted landscape driven by various factors, including financial gain, ideological beliefs, personal challenges, and revenge. Each motivation significantly shapes hackers' actions, whether they seek profit, advocate for social causes, or simply test their skills. Recognizing these motivations is crucial for organizations aiming to bolster their cybersecurity measures and effectively protect against potential threats.
The article explored the different types of hackers, highlighting the roles of white-hat, black-hat, and gray-hat hackers. Ethical hackers contribute positively by identifying vulnerabilities, while malicious hackers inflict harm for personal gain. The consequences of hacking are profound, affecting individuals through identity theft and emotional distress, and organizations through financial losses and reputational damage. As demonstrated by recent high-profile breaches, the stakes are particularly high in sectors like healthcare, where the implications of hacking can be devastating.
To combat these evolving threats, it is imperative for organizations to adopt comprehensive cybersecurity strategies. Implementing robust endpoint protection, conducting regular vulnerability assessments, and providing employee training are essential steps in creating a resilient security posture. By prioritizing these measures, organizations not only safeguard their assets but also foster trust and credibility in an increasingly digital landscape. As the motivations for hacking continue to diversify, a proactive and informed approach to cybersecurity is essential for mitigating risks and ensuring safety in the face of potential cyber threats.
What are the core motivations behind hacking?
The core motivations behind hacking can be broadly categorized into four areas: financial gain, ideological beliefs, personal challenge, and revenge.
How do financially motivated hackers operate?
Financially driven hackers, often referred to as cybercriminals, exploit vulnerabilities for monetary gain through methods such as ransomware, data theft, and fraud.
What is the impact of Business Email Compromise?
Business Email Compromise has resulted in staggering losses, surpassing billions in 2025, highlighting the significant financial stakes involved in hacking.
Who are hacktivists and what motivates them?
Hacktivists are ideologically motivated individuals who use their hacking skills to advocate for political agendas or social causes, targeting entities they consider unethical.
Can you provide examples of ideological hacking?
Recent attacks on major retailers like Marks and Spencer and The Co-op illustrate the disruptive impact of ideological hacking on business operations.
What drives hackers who seek personal challenges?
Some hackers are motivated by the thrill of overcoming security measures, viewing hacking as a personal challenge, which can lead to significant breaches.
What recent trend has been observed in hacking?
There has been a resurgence of teenage hacking gangs in English-speaking countries, indicating a trend of young individuals engaging in hacking for thrill-seeking purposes.
Why is it important for organizations to understand hacker motivations?
Understanding why hackers hack is essential for organizations to tailor their security strategies effectively, allowing them to anticipate potential threats and allocate resources appropriately.
What proactive measures can organizations take to enhance cybersecurity?
A proactive approach, such as application allowlisting, can significantly reduce the attack surface and minimize vulnerabilities by preventing unauthorized applications from executing.
How does cybersecurity relate to business?
Cybersecurity is more than just an IT issue; it is a business imperative, as stated by Stéphane Nappo, a Global Chief Information Security Officer. Understanding hacker motivations informs defensive strategies and fosters a proactive approach to cybersecurity.