
As cyber threats become increasingly sophisticated, organizations face mounting pressure to safeguard their digital assets. This reality underscores the critical importance of robust cybersecurity measures.
Network Security as a Service (NSaaS) emerges as a pivotal solution, offering a cloud-based framework that alleviates the complexities of traditional security measures while enhancing protection.
This article delves into the essential components and implementation strategies of NSaaS, posing a critical question: how can businesses effectively transition to this model to fortify their defenses against an evolving threat landscape?
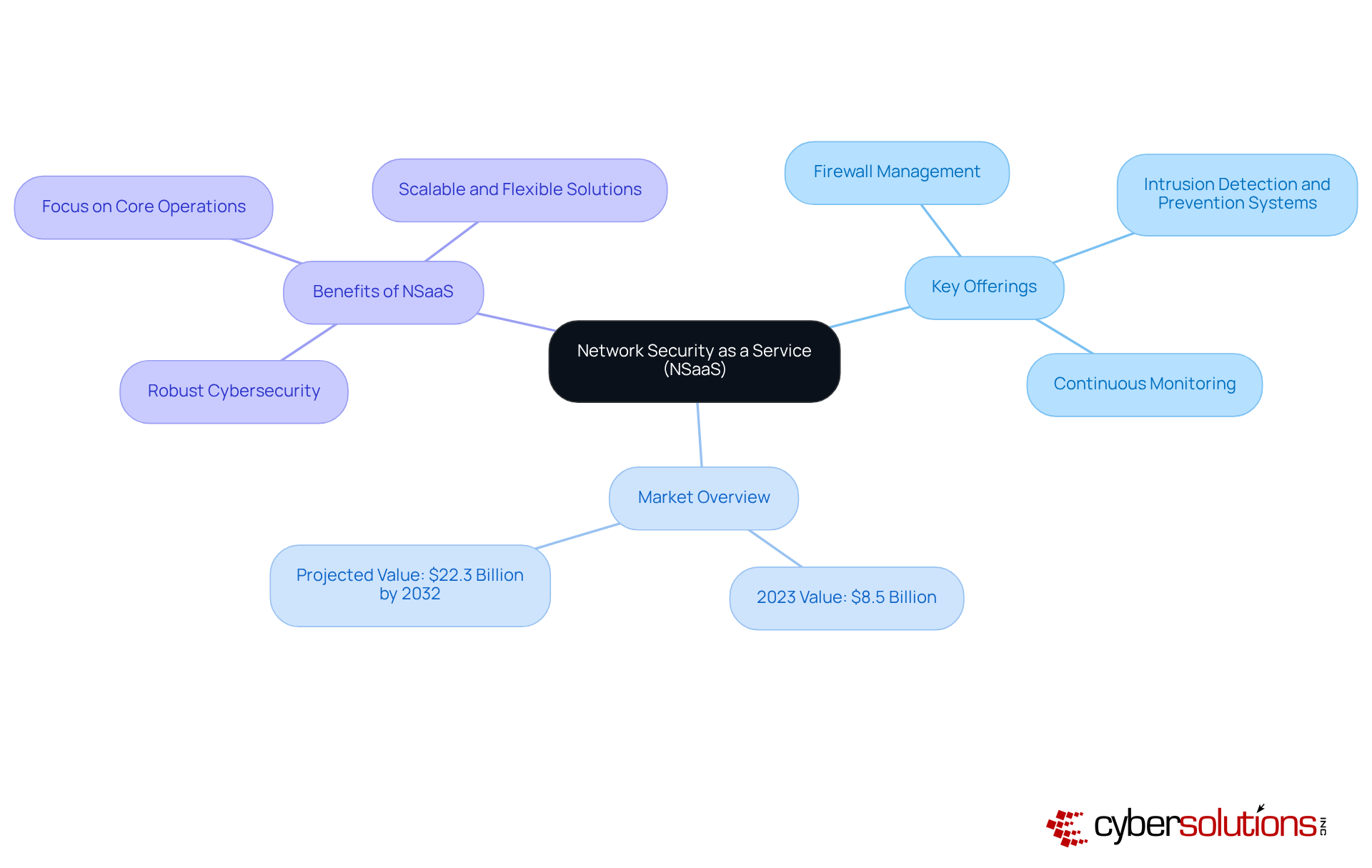
In today's digital landscape, Network Security as a Service stands as a critical solution for organizations seeking robust protection. This offers extensive network safeguarding, effectively eliminating the burdens associated with on-site hardware management. Key offerings include:
All delivered through a flexible subscription model. This framework empowers institutions to enhance their defenses in response to evolving threats, leveraging advanced technologies and expert knowledge in cybersecurity.
By outsourcing these essential functions, businesses can focus on their core operations, secure in the knowledge that they are fortified against increasingly sophisticated attacks. The global market for network services as software, valued at approximately $8.5 billion in 2023, is projected to reach $22.3 billion by 2032, reflecting a compound annual growth rate (CAGR) of 11.2%. This remarkable growth underscores the importance of NSaaS as organizations strive to bolster their protection measures and operational effectiveness.
In an era where cybersecurity is paramount, embracing NSaaS is not just a strategic move; it is an imperative for organizations committed to safeguarding their assets and ensuring resilience against the ever-present threat landscape.
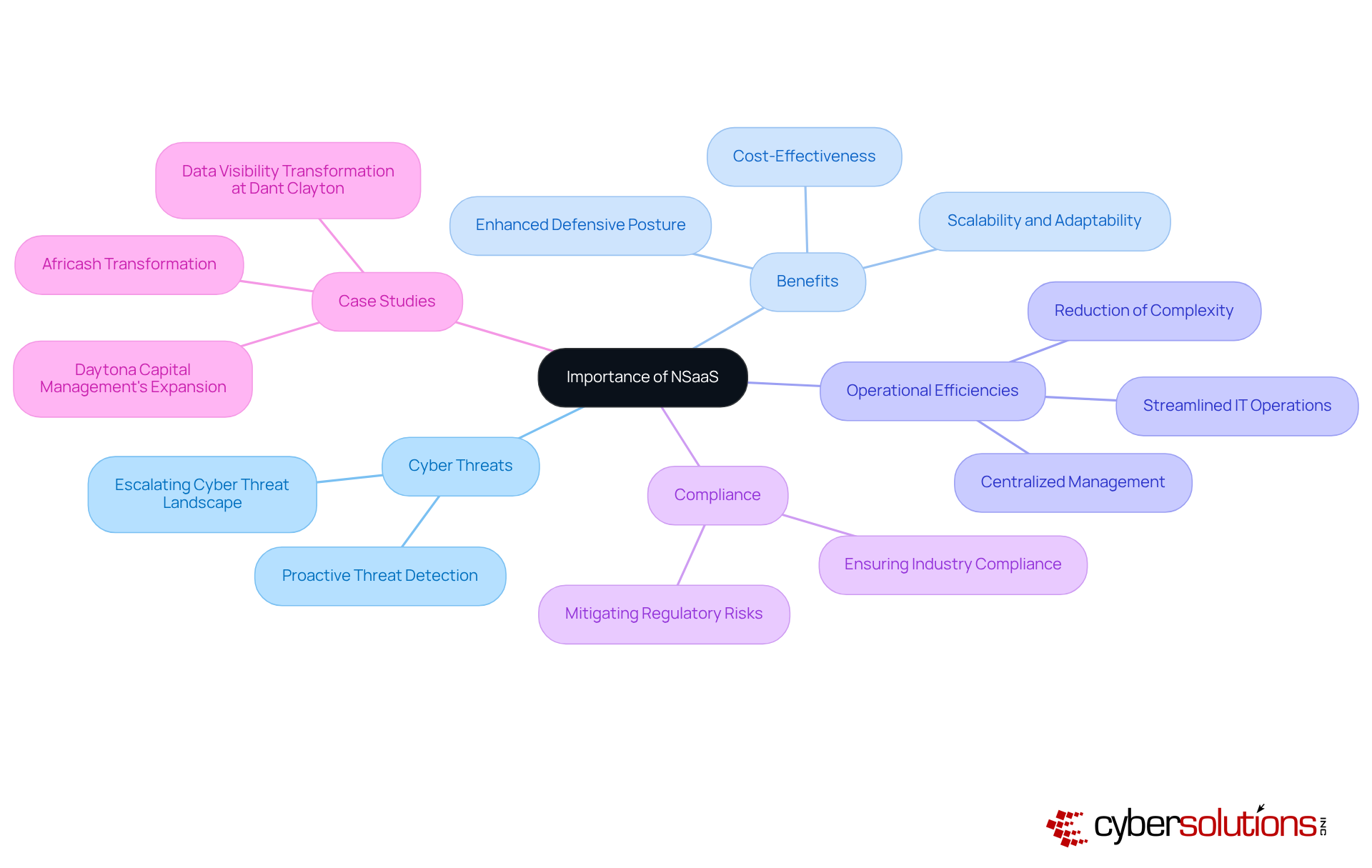
In the current landscape of escalating cyber threats, NSaaS emerges as an indispensable solution for modern enterprises. Its significance lies in delivering scalable, adaptable, and secure solutions that evolve alongside the shifting threat environment. By adopting NSaaS, organizations can significantly enhance their security posture while reducing the complexities related to managing complex infrastructures. Furthermore, this service is vital for ensuring data protection, thereby safeguarding sensitive information. As businesses increasingly depend on digital operations, the demand for NSaaS intensifies, positioning this service as a fundamental element of any comprehensive cybersecurity strategy.
Cyber Solutions provides continuous monitoring of your systems to detect anomalies and potential vulnerabilities, ensuring that suspicious activities are intercepted before they escalate into threats. This proactive approach, paired with a layered strategy that encompasses endpoint isolation and user training, significantly enhances recovery from incidents such as ransomware attacks. This effectiveness is exemplified by our successful restoration of 4,500 endpoints for a healthcare provider. According to the GTT Editorial Team, "By transitioning network and security services to the cloud, this approach eliminates the need for extensive on-site infrastructure and multiple truck rolls while centralizing management and streamlining IT operations." This statement underscores the importance of efficiency through Network Software as a Service.
Moreover, case studies such as the transformation of Africash, which evolved into a leading financial service offering following the adoption of the service model, illustrate the benefits of NSaaS. As the cybersecurity landscape continues to evolve, investing in NSaaS is not merely a strategic advantage; it is an essential necessity for contemporary businesses.
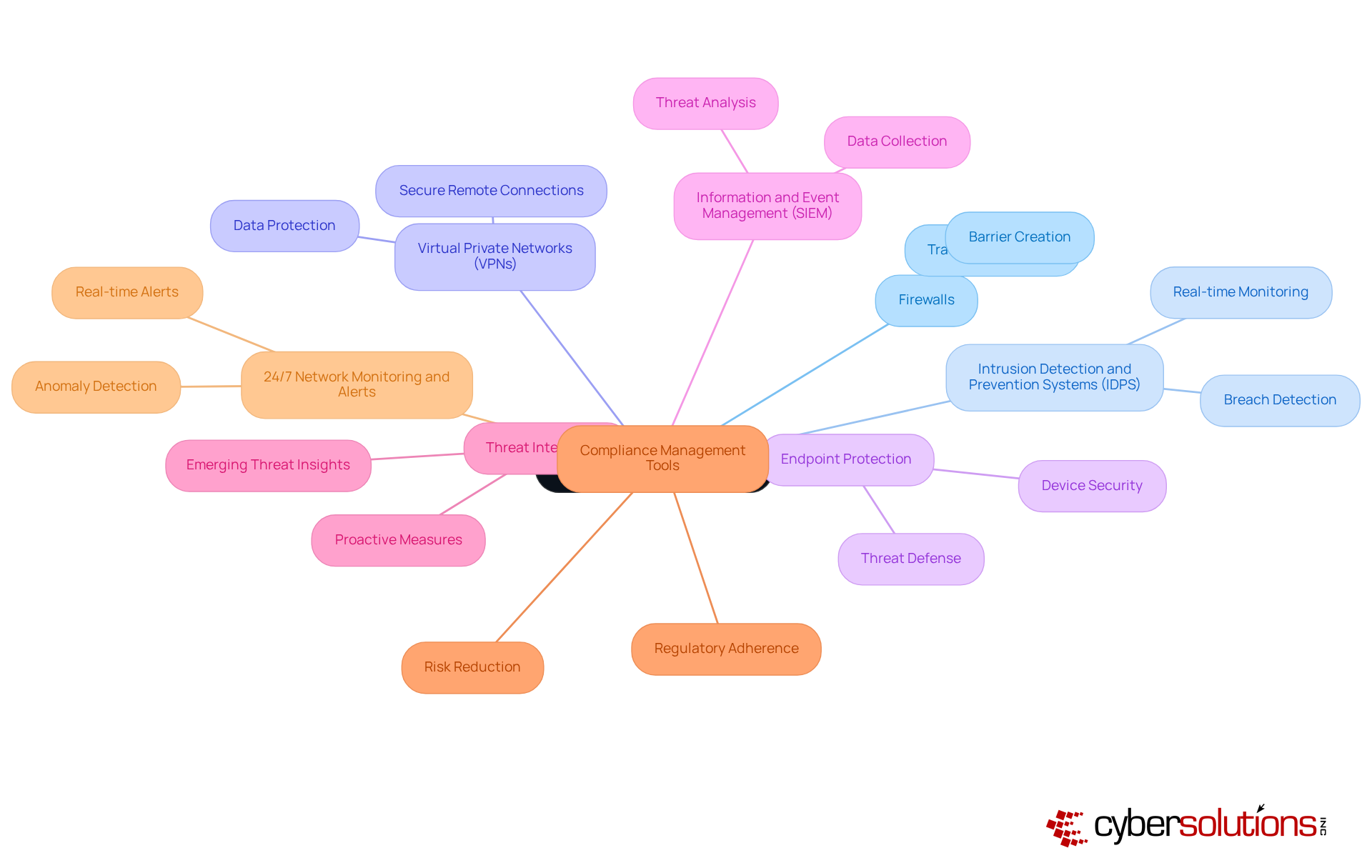
In today's digital landscape, the significance of cannot be overstated. As organizations face increasing cybersecurity threats, understanding the key components of is crucial for safeguarding sensitive information and maintaining operational integrity.
Incorporating these technologies into not only strengthens an organization's protective structure but also enhances operational effectiveness. This enables businesses to concentrate on their primary goals while ensuring a robust defense against advancing cyber threats.
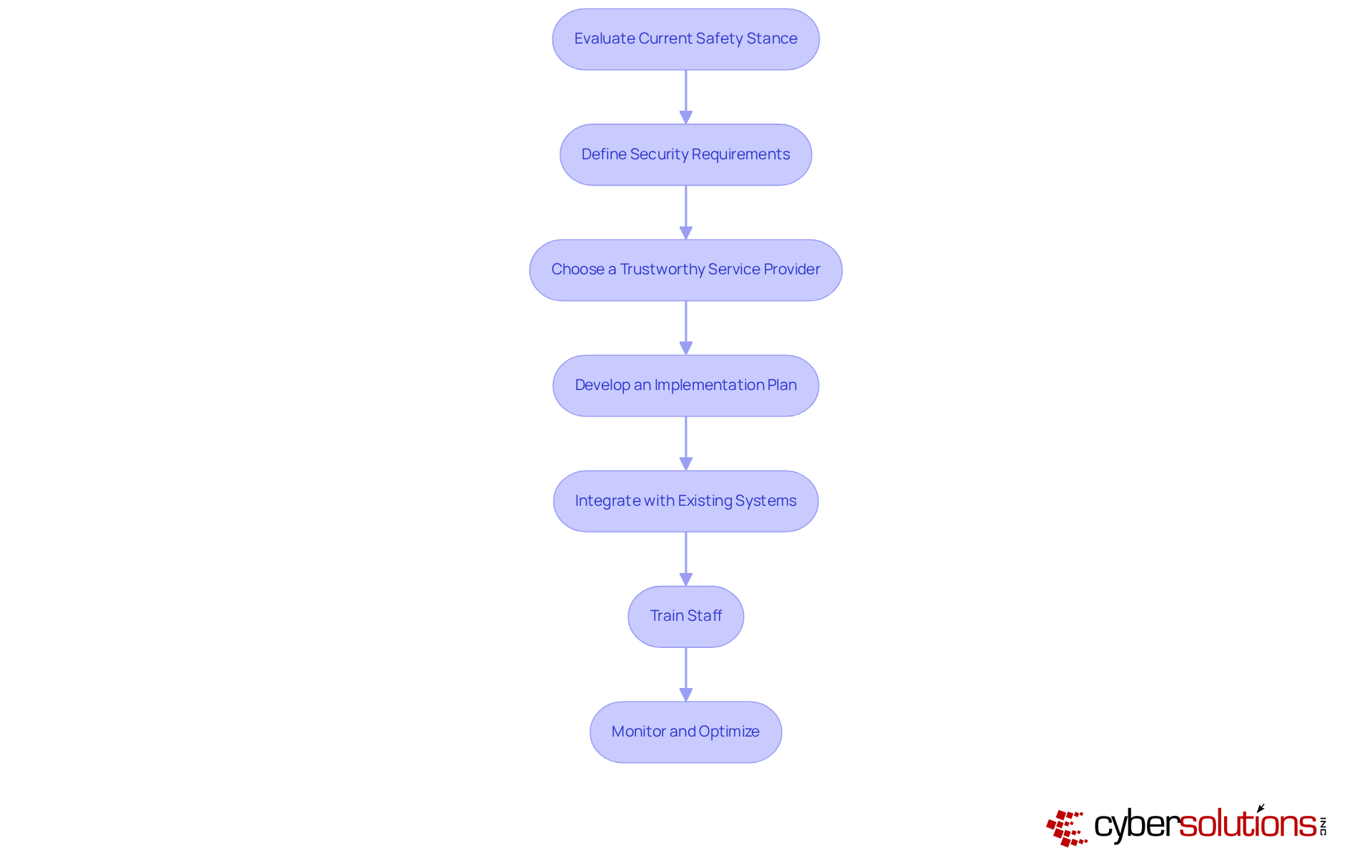
Implementing NSaaS is crucial for organizations aiming to bolster their cyber security. The following essential steps will guide you through a successful transition:
Embracing Network Security as a Service (NSaaS) is not merely beneficial; it is essential for organizations striving to navigate today’s intricate cybersecurity landscape. This innovative approach alleviates the burden of managing on-site hardware while equipping businesses with advanced protection against ever-evolving threats. By leveraging NSaaS, companies can concentrate on their core operations, ensuring their digital assets remain secure.
The article highlights several key aspects of NSaaS, including:
From firewalls and intrusion detection systems to compliance management tools, these components collaborate to create a robust defense strategy. Furthermore, the guide underscores the necessity of evaluating current security measures, defining specific requirements, and selecting a reliable service provider to facilitate a seamless transition.
As cyber threats escalate, organizations must prioritize their cybersecurity strategies. Investing in NSaaS not only fortifies defensive measures but also enhances operational efficiency and compliance. By adopting this model, businesses position themselves to thrive in a digital-first world, ensuring they are well-prepared to confront the challenges of tomorrow. The time to act is now—fortify defenses and embrace the future of network security.
What is Network Security as a Service (NSaaS)?
Network Security as a Service (NSaaS) is a cloud-based model that provides organizations with extensive network protection, including firewall management, intrusion detection and prevention systems, and continuous monitoring, all delivered through a flexible subscription model.
What are the key offerings of NSaaS?
The key offerings of NSaaS include firewall management, intrusion detection and prevention systems, and continuous monitoring.
How does NSaaS benefit organizations?
NSaaS allows organizations to outsource essential cybersecurity functions, enabling them to focus on their core operations while ensuring robust protection against sophisticated cyber threats.
What is the current market value of NSaaS?
The global market for network services as software is valued at approximately $8.5 billion in 2023.
What is the projected growth of the NSaaS market?
The NSaaS market is projected to reach $22.3 billion by 2032, reflecting a compound annual growth rate (CAGR) of 11.2%.
Why is NSaaS considered imperative for organizations?
NSaaS is considered imperative because it helps organizations safeguard their assets and ensure resilience against the ever-present threat landscape in today's digital world.