
Choosing the right managed IT consultant can be a game-changer for organizations in today’s landscape, where cybersecurity threats loom larger than ever. These consultants not only provide essential expertise in navigating complex IT landscapes but also play a crucial role in enhancing operational efficiency and ensuring compliance with industry regulations. However, with a myriad of options available, how can organizations effectively identify the best-fit consultant who aligns with their unique needs? This article explores four best practices that will empower businesses to make informed decisions in selecting a managed IT consultant, ensuring they are well-equipped to tackle the challenges of today’s digital environment.
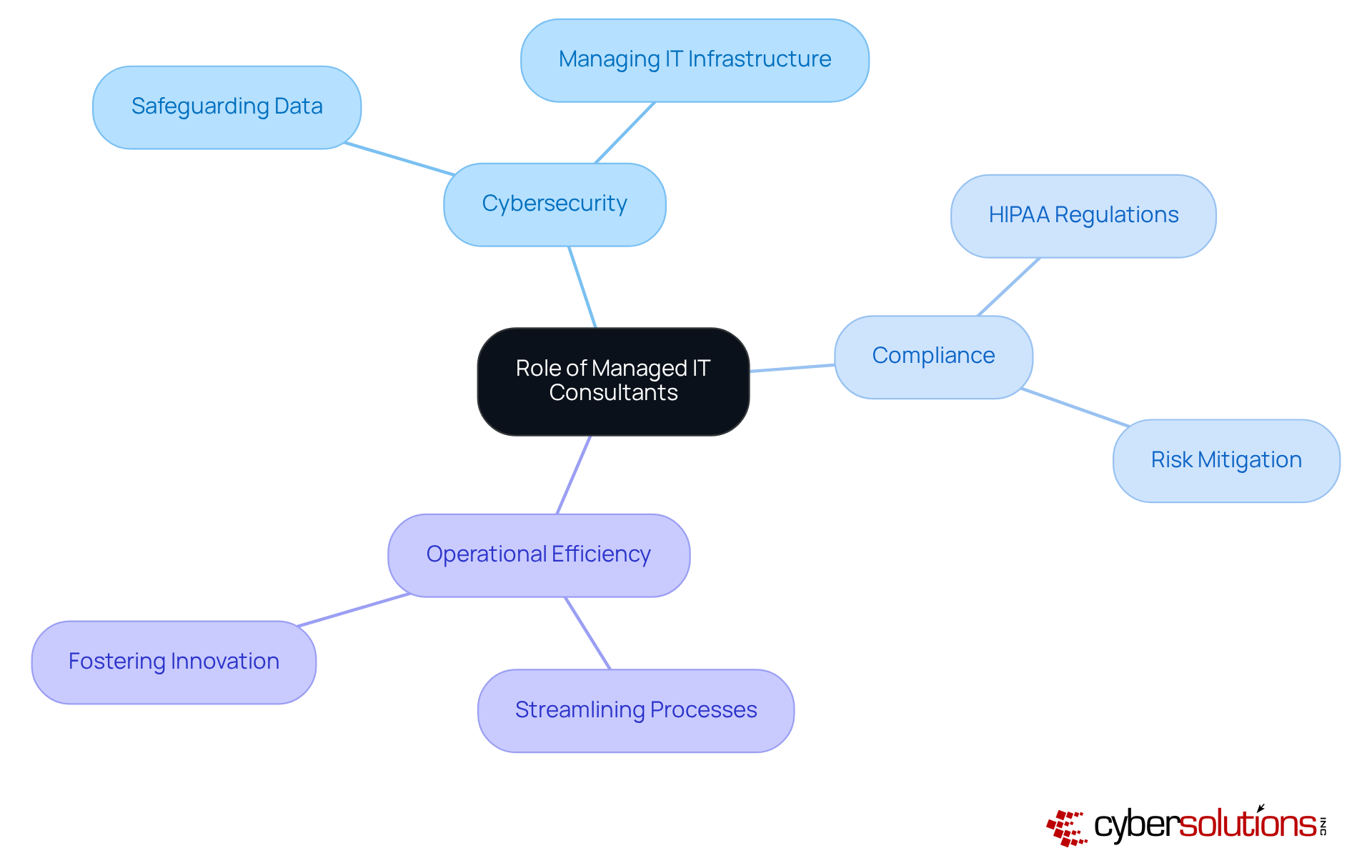
s are indispensable strategic allies for organizations, particularly in navigating the complexities of cybersecurity in healthcare. With the rise of sophisticated threats, a consultant provides specialized expertise in managing risks, vulnerabilities, and ensuring compliance. Their role is pivotal in helping businesses develop strategies that address specific operational requirements, ultimately enhancing security and efficiency.
Consider a healthcare organization that works with a consultant to ensure adherence to regulations while simultaneously strengthening measures to protect sensitive patient information. This dual approach not only mitigates risks associated with breaches but also aligns with the organization's goals by averting potentially costly incidents.
The impact of organized IT advisors extends beyond mere compliance; they significantly enhance performance. By streamlining IT processes and automating routine tasks, these professionals enable enterprises to focus on their core business objectives, fostering growth and innovation. Industry leaders emphasize that outsourcing IT management to a consultant allows organizations to concentrate on strategic initiatives, knowing that their infrastructure, security, and compliance are expertly managed. This proactive strategy is vital in today’s rapidly changing digital landscape, where the complexity of technology is ever-increasing.
When selecting a consultant, organizations must prioritize several key criteria to effectively navigate the complex landscape of cybersecurity.
By meticulously assessing these criteria, companies can select a consultant who not only meets their technical needs but also aligns with their financial goals, ultimately enhancing operational efficiency and security.

To foster communication and collaboration with a consultant, organizations must take decisive steps:
By establishing these efficient communication pathways, organizations can ensure that their consultant is well-prepared to tackle specific challenges and add substantial value to their success. For instance, the integration of communication tools has been shown to improve project outcomes, as demonstrated in various case studies.

Organizations must implement strategies to ensure security.
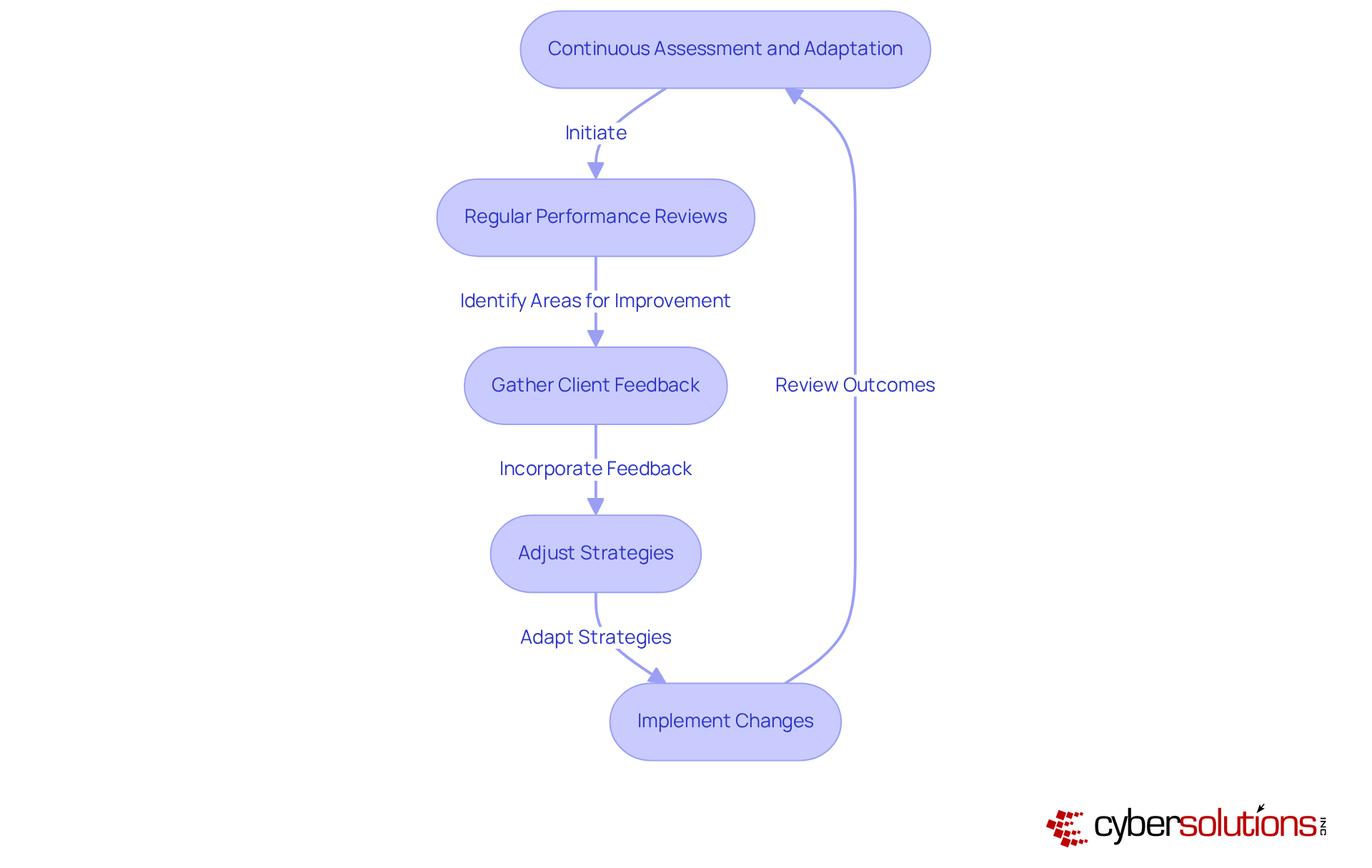
Regular performance reviews involve assessments against established key performance indicators (KPIs), which is essential. This review process not only identifies areas for improvement but also ensures accountability. Regular evaluations assist companies in remaining aligned with their strategic objectives, particularly given that the average response time is 258 days. This statistic emphasizes the necessity for proactive management and ongoing monitoring to effectively adjust security measures. Case studies exemplify this approach, ensuring that suspicious activities are detected and addressed before they escalate into significant threats.
Staying updated on industry trends is equally vital. Awareness of emerging threats is crucial in a landscape where ransomware accounts for 59% of all cyberattacks and 88% of cyber incidents are attributed to human errors. Organizations must proactively adapt their strategies to maintain a robust security posture. Understanding trends, such as the projected growth to $368.19 billion by 2033, can guide strategic choices. Cyber Solutions highlights the significance of a layered strategy for digital security, which encompasses endpoint isolation and user education, to improve recovery and protect against future risks.
Regularly gathering feedback from internal stakeholders regarding the consultant's performance and the effectiveness of implemented solutions is vital. Organizations that involve employees in feedback processes see a 12% increase in productivity, while those utilizing regular feedback systems achieve 39% higher effectiveness in talent attraction. This underscores the importance of creating channels for open communication. A robust feedback loop can also strengthen partnerships, as demonstrated by Cyber Solutions’ collaborative efforts with clients to enhance their security measures.
Flexibility is key to navigating the dynamic landscape of IT and cybersecurity. Organizations must be willing to pivot and adapt strategies based on performance reviews and feedback. The swift development of cyber threats necessitates continuous improvement in methods to mitigate risks effectively. Best practices, which include specialized expertise and a structured response plan, illustrate the importance of being prepared to act quickly in the face of threats. Moreover, relying solely on yearly evaluations may result in outdated conclusions, exposing entities to new risks introduced by modifications made after their previous assessment.
By committing to continuous assessment and adaptation, organizations can ensure that their collaboration with a managed IT consultant remains productive and aligned with their evolving needs. As noted, "99% of companies find 360-degree surveys effective for strategic decision-making," underscoring the importance of soliciting feedback.
Choosing the right managed IT consultant is not just a decision; it is a pivotal choice that can significantly influence an organization's cybersecurity and operational efficiency. Understanding the crucial role these consultants play enables organizations to adeptly navigate the complexities of IT management, ensuring they select a partner who aligns seamlessly with their specific needs and goals.
This article outlines essential best practices for selecting a managed IT consultant, such as:
Equally important is the establishment of effective communication and collaboration, which fosters a productive partnership capable of adapting to the ever-evolving landscape of cybersecurity threats. Continuous assessment and adaptation strategies further enhance this relationship, ensuring that the consultant's performance remains aligned with the organization's objectives.
In an era where cyber threats are increasingly sophisticated, organizations must prioritize these best practices in their search for a managed IT consultant. By doing so, they not only bolster their security posture but also empower their teams to concentrate on strategic initiatives that drive growth and innovation. Embracing these strategies guarantees that businesses remain resilient and competitive in an ever-changing digital environment.
What is the role of managed IT consultants in organizations?
Managed IT consultants serve as strategic allies for organizations, providing specialized expertise in managing IT infrastructure, safeguarding data, and ensuring compliance, particularly in complex areas like cybersecurity in healthcare.
How do managed IT consultants help with cybersecurity in healthcare?
They help healthcare organizations adhere to regulations such as HIPAA while strengthening cybersecurity measures to protect sensitive patient information, which mitigates risks associated with data breaches.
What are the benefits of working with a managed IT consultant?
Benefits include enhanced security, operational efficiency, and the ability for organizations to focus on core business objectives while knowing their IT infrastructure, security, and compliance are expertly managed.
How do managed IT consultants improve operational efficiency?
They streamline IT processes and automate routine tasks, allowing enterprises to concentrate on growth and innovation rather than being bogged down by IT management.
Why is outsourcing IT management to a managed IT consultant considered a proactive strategy?
It enables organizations to focus on strategic initiatives while ensuring that their infrastructure, security, and compliance are expertly managed, which is crucial in a rapidly changing digital landscape with increasing cyber threats.