
In an increasingly interconnected world, the role of Managed Service Providers (MSPs) has evolved from a mere support function to a strategic asset for businesses. By outsourcing IT operations, organizations can enhance their efficiency while navigating the complexities of cybersecurity and compliance with greater ease.
However, as businesses contemplate this shift, they must grapple with the potential challenges of relinquishing control over their IT landscape.
What critical factors should business leaders consider when exploring the true meaning of MSP technology and its implications for their operations?
In today's complex digital landscape, understanding the role of Managed Service Providers has never been more crucial for the role of businesses. These third-party companies proactively oversee a customer's IT infrastructure and end-user systems, allowing organizations to outsource their IT operations. This strategic model enables businesses to focus on their core functions while ensuring that their IT needs are met effectively.
MSPs offer a diverse range of solutions tailored to the specific requirements of their clients, including:
At Cyber Solutions, we pride ourselves on delivering comprehensive reporting and support, ensuring audit readiness through detailed compliance and risk assessments. Our flat-rate pricing simplifies budgeting, covering everything from email licenses to advanced cybersecurity measures that not only protect businesses but also enhance operational efficiency.
Moreover, our offerings include:
The increasing complexity of IT environments and the rising demand for specialized knowledge have driven the growth of Managed Service Providers, illustrating the importance of their services. Our monitoring and alert systems proactively defend against threats such as ransomware and phishing attacks, ensuring that suspicious activities are detected and addressed before they escalate.
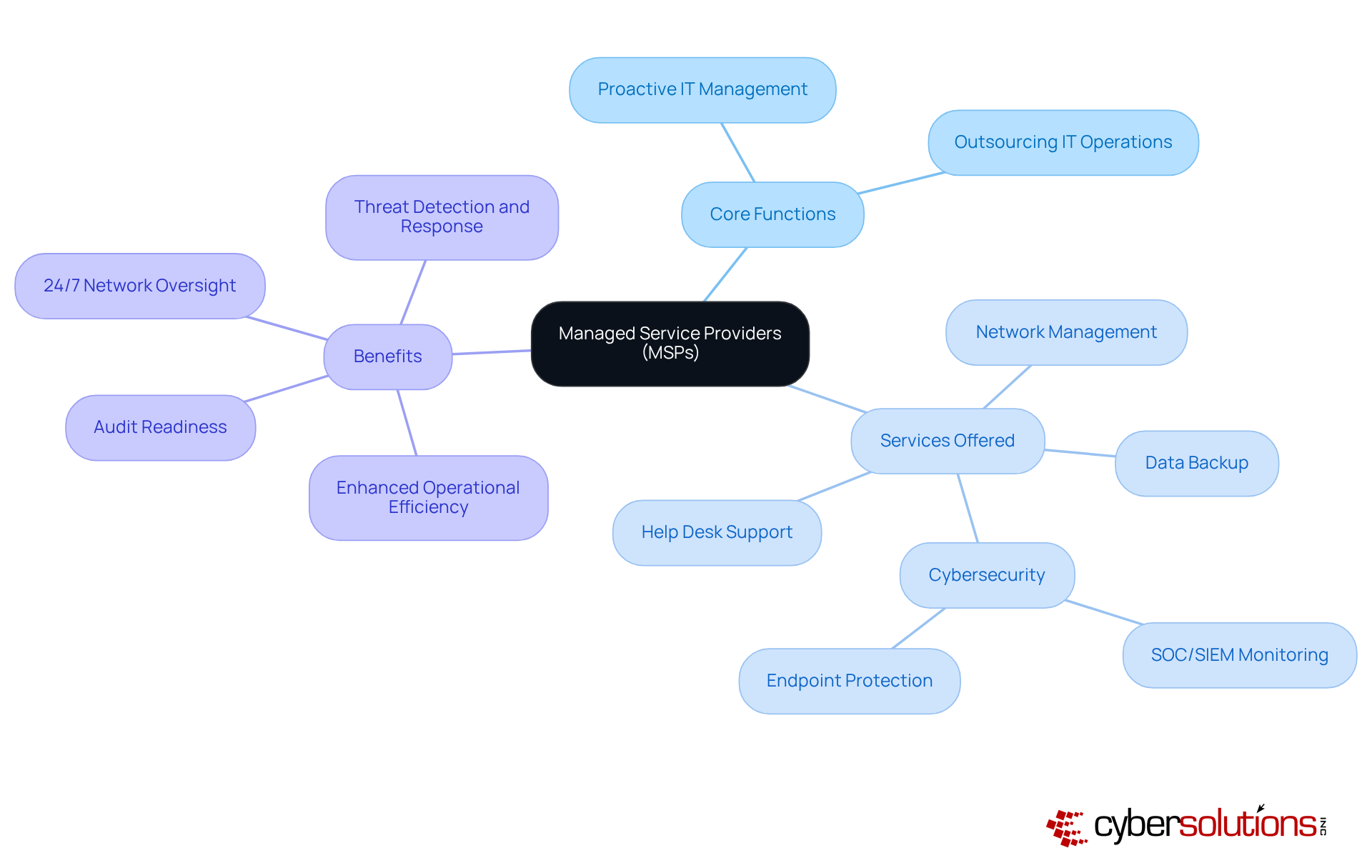
Managed Service Providers (MSPs) operate primarily on a subscription model, allowing clients to manage their IT expenses with predictable monthly costs. The core services they provide include:
By leveraging advanced technologies and a team of skilled professionals, MSPs can proactively identify and mitigate potential issues before they escalate into significant challenges.
Consider Cyber Solutions Inc., which offers IT management and cybersecurity services that not only protect businesses but also ensure adherence to industry regulations. This not only enhances efficiency but also grants organizations the flexibility to adapt in response to evolving needs. In fact, businesses that engage MSPs can achieve average cost savings of up to 30% in their IT expenditures.
In an era where cyber threats are increasingly sophisticated, the role of MSPs like Cyber Solutions becomes paramount. Their expertise allows organizations to navigate these challenges effectively, ensuring that they remain compliant while safeguarding their critical data. The partnership is not just a cost but a strategic move towards securing a resilient IT infrastructure.

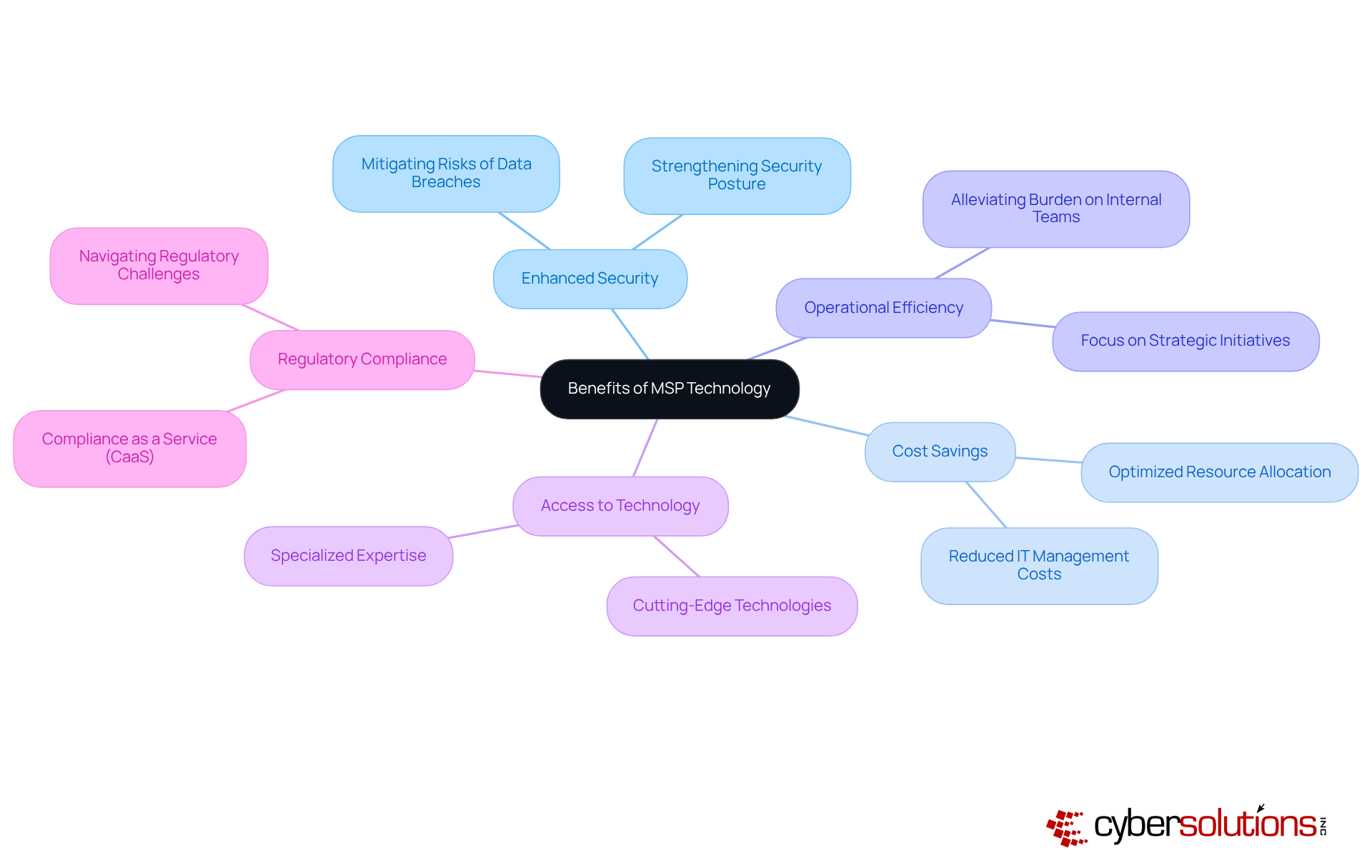
Organizations that collaborate with managed service providers (MSPs) can leverage technology to gain significant advantages, including enhanced security, cost savings, and improved operational efficiency. In today’s landscape of increasing cybersecurity threats, outsourcing IT management allows businesses to alleviate the burden on internal teams, enabling them to concentrate on strategic initiatives that drive growth.
Moreover, MSPs provide access to cutting-edge technologies and specialized expertise, which can be particularly beneficial for small to medium-sized businesses that may lack the resources for a comprehensive in-house IT department. This access not only helps in optimizing operations but also positions firms to effectively tackle the unique challenges posed by the evolving regulatory environment.
Furthermore, MSPs play a crucial role in ensuring compliance with regulatory obligations, thereby mitigating risks associated with data breaches and penalties for non-compliance. For instance, Cyber Solutions Inc. exemplifies this by offering compliance as a service (CaaS), which addresses the complexities of regulations such as HIPAA and GDPR. This service is indispensable for industries like healthcare and finance, where compliance is paramount.
In summary, partnering with a managed service provider not only enhances operational capabilities but also fortifies an organization’s security posture and compliance efforts, making it a strategic move for businesses aiming to thrive in a competitive landscape.
While collaborating with MSPs presents numerous advantages, understanding the challenges is essential for entities to navigate potential challenges and ensure effective partnerships. A primary concern is the perceived loss of control over IT operations, which can lead to misalignment between the MSP and the entity's unique requirements. Notably, nearly 60% of businesses express concerns about losing control when outsourcing IT functions. This statistic underscores the necessity for vigilance in these partnerships.
To mitigate this risk, companies should prioritize selecting an MSP with a proven track record in service delivery. Any misalignment can lead to operational disruptions, including financial losses and regulatory penalties. Establishing robust communication strategies is essential; organizations must set clear expectations and maintain open lines of dialogue with their MSPs to ensure alignment on goals and objectives.
Moreover, evaluating the MSP's pricing model is crucial. Organizations should ensure that it aligns with their budget while providing transparency regarding the services included. By proactively addressing these challenges, businesses can enhance their control over IT operations and service quality, ultimately leading to improved efficiency and security.

Understanding the role of Managed Service Providers (MSPs) is crucial for business leaders intent on optimizing their IT operations. By outsourcing IT management to these specialized firms, organizations can concentrate on their core business activities while ensuring their technology needs are met effectively. This strategic partnership not only enhances operational capabilities but also strengthens security and compliance efforts, positioning MSPs as invaluable assets in today’s intricate digital landscape.
This article explores the multifaceted benefits of MSP technology, highlighting essential services such as:
Engaging with MSPs can lead to substantial cost savings and operational efficiencies, particularly for small to medium-sized businesses. Furthermore, the discussion on potential challenges—such as the perceived loss of control and the necessity of clear communication—underscores the importance of selecting the right MSP that aligns with specific organizational needs.
In conclusion, partnering with a managed service provider transcends mere tactical decision-making; it is a strategic move that can profoundly influence an organization's success. By leveraging the expertise and resources of MSPs, businesses can adeptly navigate the complexities of IT management while bolstering their security posture and compliance efforts. As the digital landscape continues to evolve, embracing MSP technology will be vital for organizations striving to thrive and maintain a competitive edge.
What are Managed Service Providers (MSPs)?
Managed Service Providers (MSPs) are third-party companies that proactively oversee a customer's IT infrastructure and end-user systems, allowing organizations to outsource their IT operations.
What services do MSPs typically offer?
MSPs offer a range of solutions including network management, data backup, cybersecurity, and help desk support.
How do MSPs benefit businesses?
MSPs enable businesses to focus on their core functions while ensuring that their technology needs are met effectively, enhancing operational efficiency and security.
What is included in the flat-rate pricing offered by MSPs?
The flat-rate pricing typically covers various services including email licenses and advanced cybersecurity measures.
What specific security services do MSPs provide?
MSPs provide services such as SOC/SIEM for security monitoring and endpoint protection to safeguard devices.
Why has the demand for MSPs increased?
The increasing complexity of IT environments and the rising demand for specialized knowledge have driven the growth of managed service providers.
How do MSPs handle cybersecurity threats?
MSPs offer 24/7 network oversight and alert systems to proactively defend against threats like ransomware and phishing attacks, ensuring suspicious activities are detected and addressed promptly.