
In an age where digital interactions are integral to business operations, the concept of secure browsing has emerged as a cornerstone of online safety. This practice not only protects users from threats like identity theft and data breaches but also ensures that organizations comply with stringent regulations, safeguarding their integrity and reputation.
However, as cyber threats evolve, how can businesses effectively implement robust secure browsing strategies that keep pace with these challenges?
Exploring this question reveals the critical importance of proactive measures and best practices in creating a safer online environment.
What is secure browsing is a critical aspect of online safety, as it encompasses a range of techniques and tools that protect users' online activities and personal information. This practice employs protected connections (HTTPS), trusted browsers, and various protective measures to illustrate what is secure browsing by mitigating risks such as malware, phishing, and identity theft. As the landscape of the internet continues to evolve, so too do the threats, necessitating increasingly robust security protocols to safeguard sensitive information and uphold user privacy.
In 2025, the imperative for secure browsing extends beyond personal safety; it is vital for organizational integrity. Ensuring adherence to regulations while safeguarding data is non-negotiable. Notably, a significant proportion of organizations have adopted HTTPS, reflecting a growing commitment to safe online practices. Practical examples abound, showcasing how leading firms implement security measures, underscoring the importance of these actions in maintaining trust and protection in digital exchanges.
We emphasize that as online dangers evolve, organizations must adopt best practices. These strategies should integrate technical safeguards with comprehensive user training to effectively address emerging risks. Are your organizations keeping pace with the threats? The time to act is now.

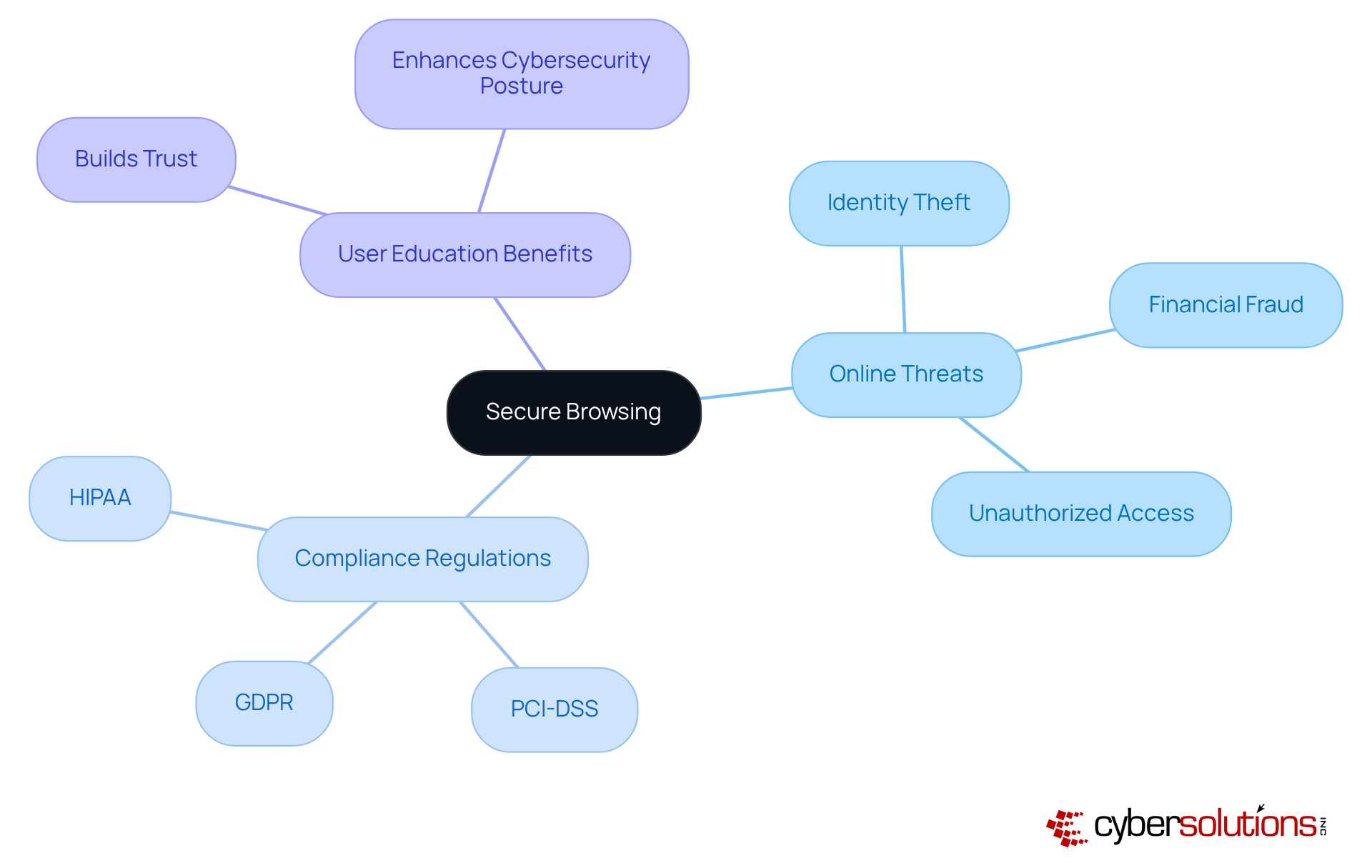
In today's environment, where cyber threats are on the rise, knowing what is secure browsing is crucial for ensuring online safety. It serves as a frontline defense, illustrating what is secure browsing by protecting individuals from threats such as:
For organizations, understanding what is secure browsing is not merely a precaution; it is crucial for compliance with regulations like GDPR and CCPA. These frameworks mandate the protection of personal and financial data, with non-compliance potentially resulting in significant penalties.
Moreover, secure browsing instills confidence among customers and stakeholders, showcasing an organization's commitment to security. In a competitive landscape, companies that prioritize safe internet practices not only enhance their cybersecurity posture but also distinguish themselves by demonstrating a proactive approach. This proactive strategy is essential in maintaining trust and ensuring resilience against the ever-evolving cyber threats that organizations face today.
Essential features of safe online activity involve the use of HTTPS for protected connections, regular updates of web browsers and extensions, and the adoption of robust password protocols. These practices include:
By implementing these practices, organizations can enhance their approach to secure browsing for their users and safeguard sensitive information from possible dangers. As emphasized by cybersecurity experts, implementing a comprehensive security strategy is vital for maintaining robust defenses against the ever-evolving landscape of cyber threats.
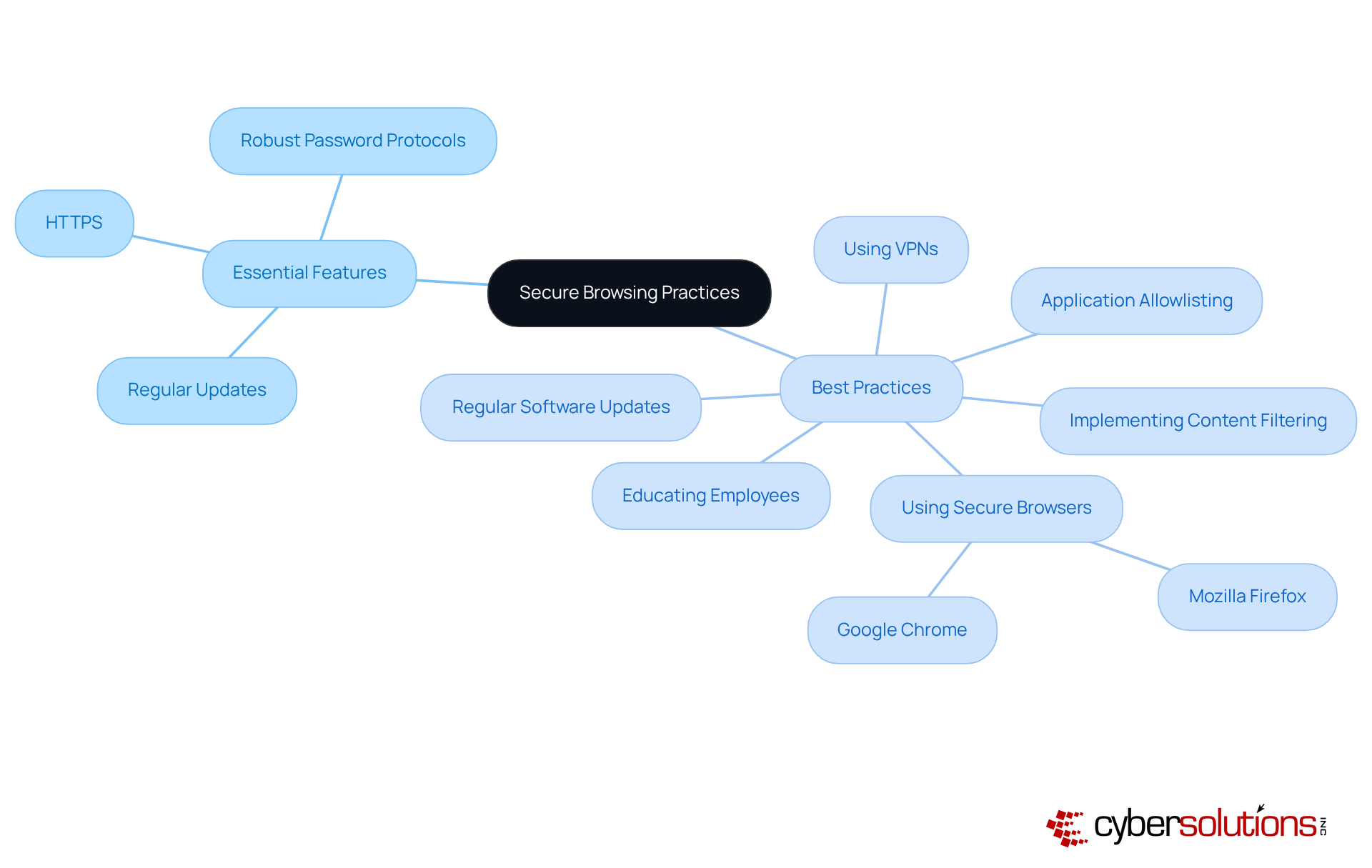
Understanding secure browsing is essential for both individuals and organizations; it serves as a crucial line of defense against the myriad of cyber threats that permeate the online landscape. By employing techniques such as HTTPS, utilizing trusted browsers, and implementing comprehensive security measures, users can significantly mitigate risks to their personal information and corporate data. This commitment to secure browsing is not merely a technical necessity; it is a fundamental aspect of maintaining trust and integrity in digital interactions.
Key insights into secure browsing include:
These proactive measures are vital for fostering a culture of security that enhances overall resilience against evolving cyber threats.
In a world where cybercrime is projected to inflict trillions in damages, the significance of secure browsing extends beyond mere compliance; it is a strategic imperative for any organization aiming to safeguard its assets and maintain stakeholder confidence. By prioritizing secure browsing practices, businesses can not only protect their sensitive information but also position themselves as leaders in the commitment to online safety. The call to action is clear: investing in secure browsing is investing in the future of organizational integrity and user trust.
What is secure browsing?
Secure browsing is a critical aspect of online safety that involves techniques and tools designed to protect users' online activities and personal information. It includes using protected connections (HTTPS), trusted browsers, and various protective measures to mitigate risks such as malware, phishing, and data breaches.
Why is secure browsing important for organizations?
Secure browsing is vital for organizational integrity as it ensures adherence to regulations while safeguarding corporate data. It helps maintain trust and protection in digital exchanges, which is essential for both personal and organizational safety.
How are organizations implementing secure browsing practices?
Many organizations have adopted HTTPS as part of their commitment to safe online practices. They implement secure online strategies that reflect a growing awareness of the importance of protecting sensitive information.
What do cybersecurity specialists recommend for addressing online threats?
Cybersecurity specialists recommend that organizations adopt layered security approaches that integrate technical safeguards with comprehensive user training to effectively address emerging online risks.
What are some common threats that secure browsing aims to mitigate?
Secure browsing aims to mitigate various online threats, including malware, phishing attacks, and data breaches, which can compromise users' personal information and online safety.
How does the landscape of online threats affect secure browsing practices?
As the landscape of the internet evolves, so do the threats, necessitating increasingly robust security protocols to safeguard sensitive information and uphold user privacy.