
In an era where technology dictates the pace of business, recognizing the pivotal role of business IT services companies is essential for any organization striving to excel. These firms not only deliver vital IT solutions but also empower businesses to adeptly navigate the complexities of the digital landscape, ensuring both efficiency and security. As the demand for advanced cybersecurity and operational support escalates, organizations must confront significant challenges in selecting the right IT services partner. How can making the right choice enhance their operational capabilities and drive strategic growth?
In today's digital landscape, the significance of cannot be overstated. A business IT services company is dedicated to providing a comprehensive array of technology-related services that enhance the operational capabilities of enterprises. These services encompass:
The primary goal of these companies is to empower clients to operate efficiently and securely, navigating the complexities of technology without the distractions of IT challenges.
Take Cyber Solutions, for instance. They offer extensive designed not only to protect enterprises but also to enhance and reduce costly downtime. Their cybersecurity solutions include:
These solutions are specifically tailored for small to medium enterprises. As the demand for corporate IT solutions continues to rise, projected to experience significant growth by 2025, are essential in helping organizations remain competitive and compliant in a rapidly evolving environment.
It is crucial for companies to thoroughly evaluate managed IT providers, considering factors such as customer support history and compatibility with existing infrastructure. Successful IT services firms, like Cyber Solutions, exemplify the effectiveness of these services in bolstering and security. Case studies reveal that prompt incident management can lead to a remarkable 30% reduction in downtime, significantly improving operational continuity. Moreover, neglecting cybersecurity can create substantial liabilities as organizations expand, underscoring the necessity of prioritizing robust IT support and a layered cybersecurity approach.

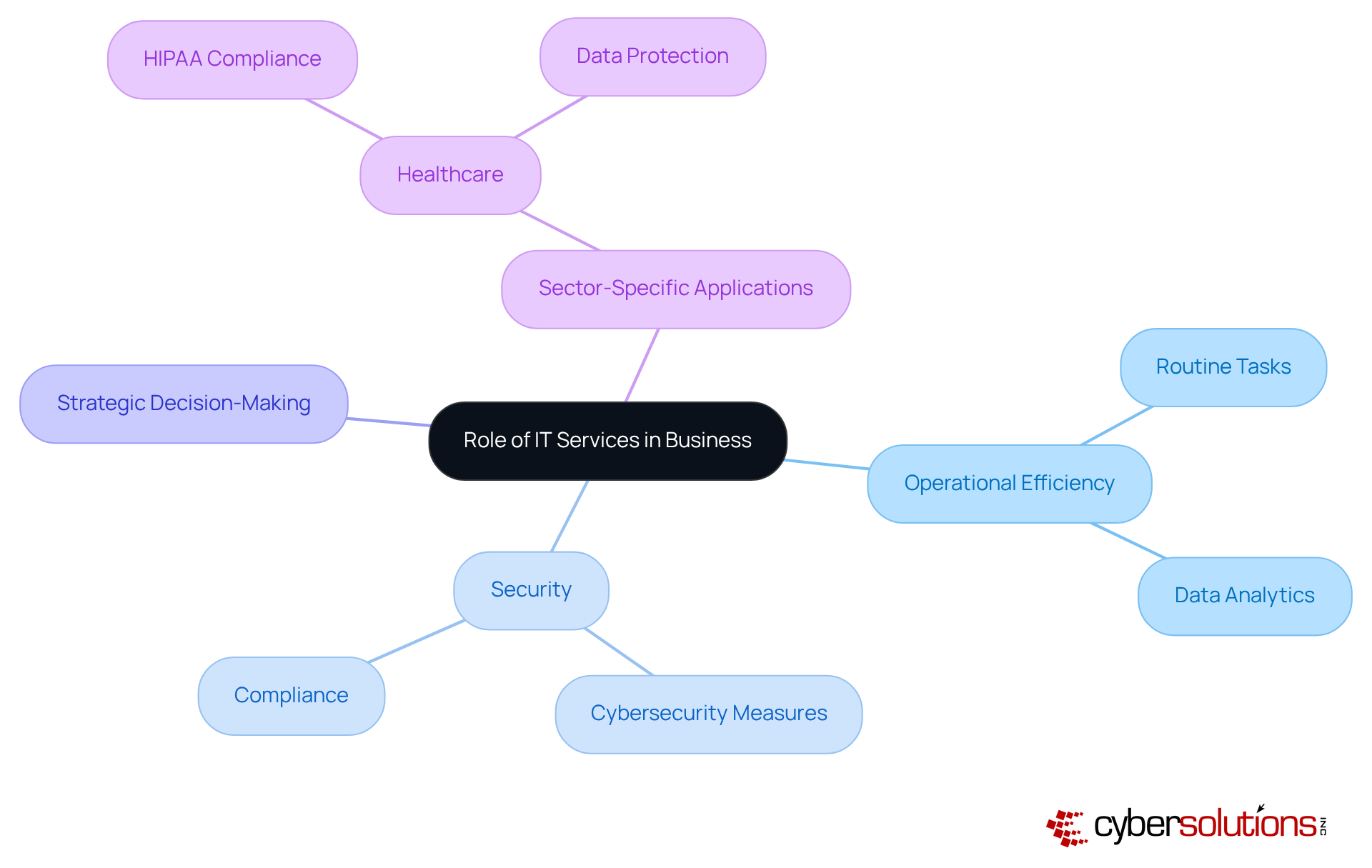
In today's fast-paced business landscape, a business IT services company is indispensable for providing technology solutions and security. As companies increasingly rely on technology for their daily operations, the demand for support from a reliable IT services provider has surged. These solutions not only facilitate routine tasks but also enhance strategic decision-making through data analytics and robust infrastructure.
In sectors such as healthcare, where data protection is paramount, IT services play a critical role while safeguarding sensitive patient information. Therefore, IT offerings are not merely ancillary support functions; they are essential services that drive growth and foster innovation.
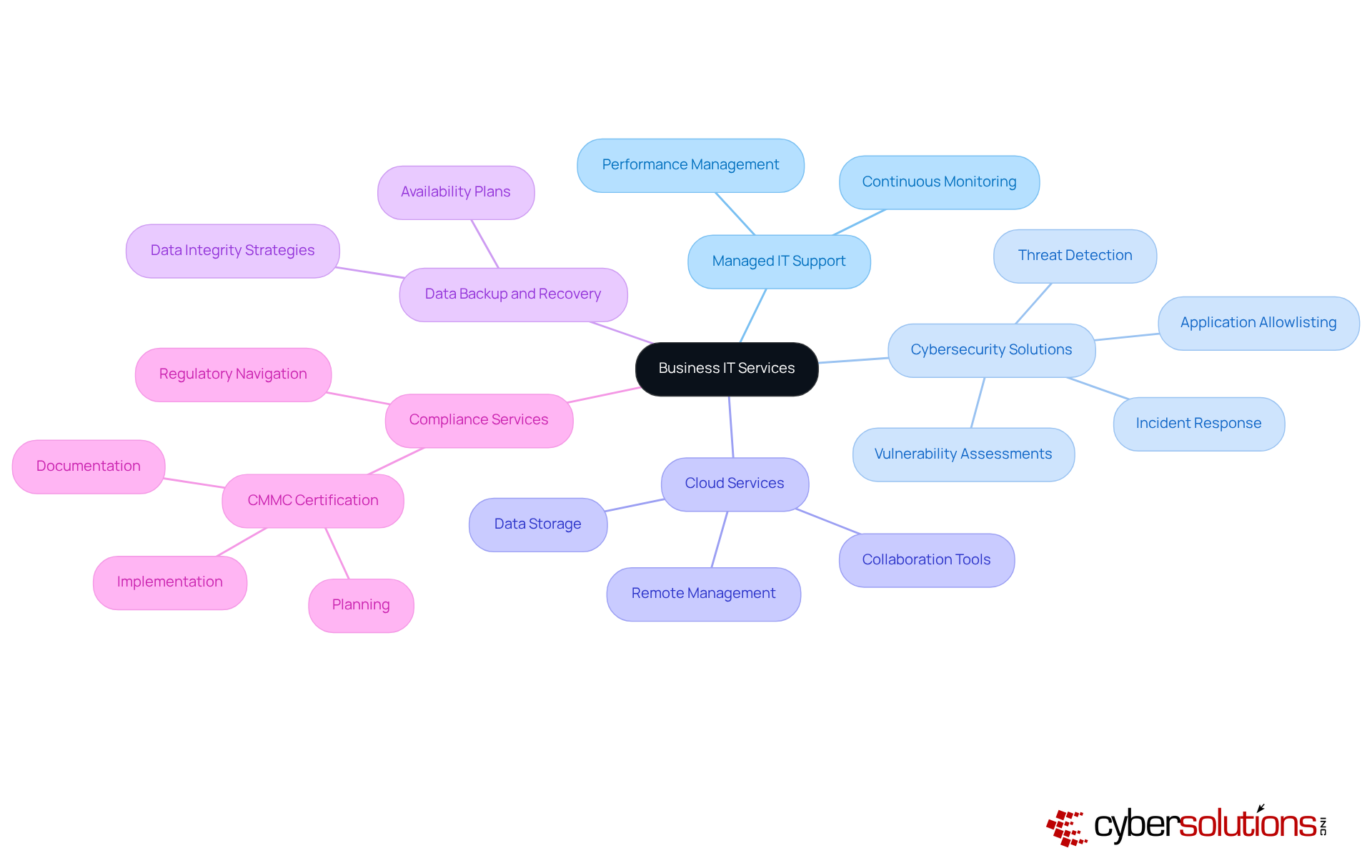
Key features of a business IT services company encompass a comprehensive range of offerings tailored to meet the distinct needs of various sectors. In today's digital landscape, where cybersecurity is paramount, these solutions are not just beneficial—they are essential. Common services offered include:
These offerings from a business IT services company are designed to enhance operational efficiency, reduce downtime, and mitigate risks associated with technology use, ultimately empowering organizations to thrive in a complex digital environment.
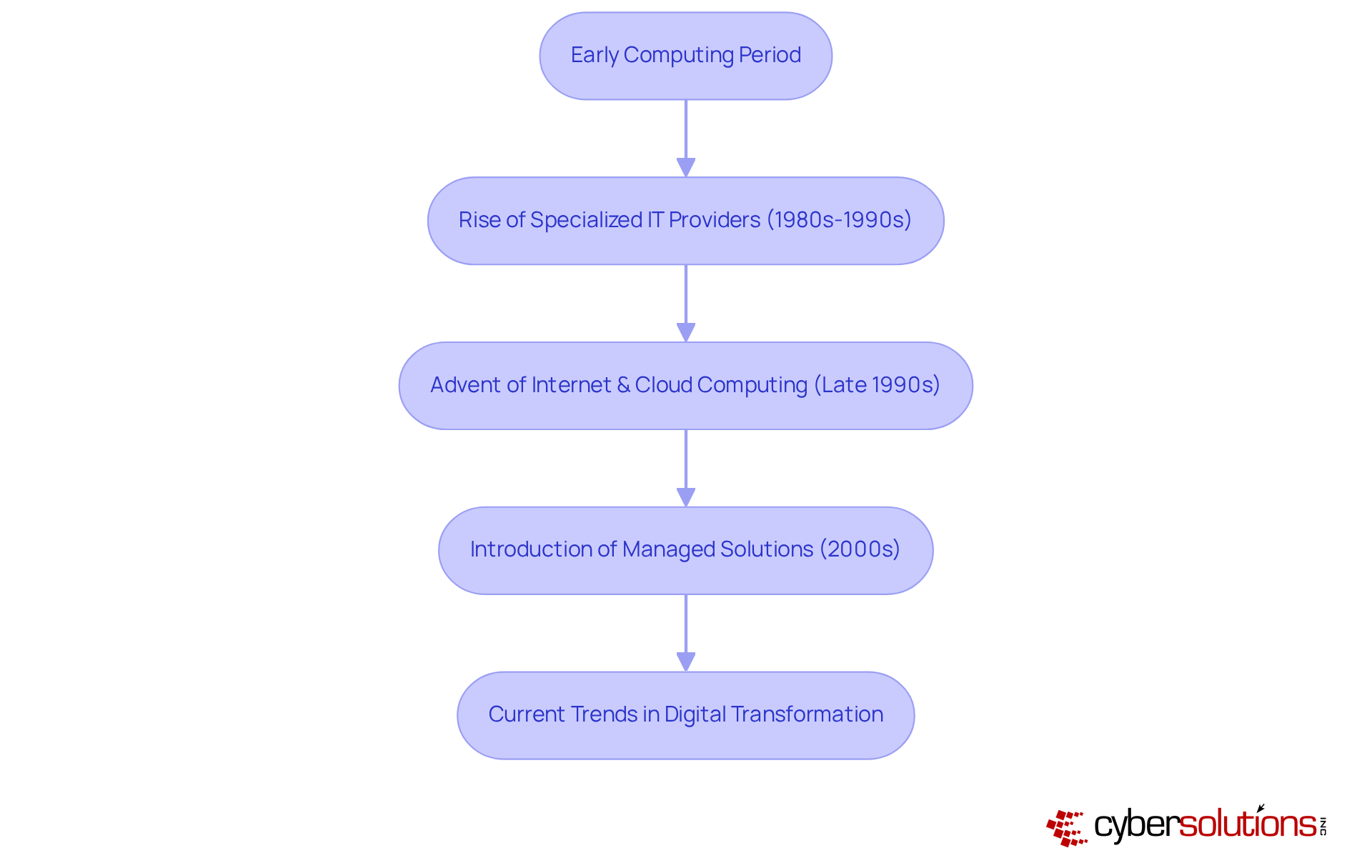
The evolution of IT firms has been pivotal in shaping the landscape of cybersecurity, especially in healthcare. Initially, during the early computing period, companies primarily relied on internal IT departments. However, as technology advanced, the complexity of IT systems increased, leading to the rise of specialized IT providers in the 1980s and 1990s. The late 1990s marked a significant transformation with the advent of the internet and cloud computing, which revolutionized service delivery by enabling remote assistance and enhancing scalability.
The 2000s heralded a critical shift with the introduction of managed solutions. Organizations began opting for outsourced IT support to improve efficiency. This trend has continued to grow, with the industry expanding significantly over the decades. Today, a managed IT service is essential for businesses, providing innovative solutions that leverage data analytics and machine learning.
A cornerstone of this transformation is the implementation of [robust digital security measures](https://techwize.com/case_studies/Streamlining IT Services and Knowledge Sharing through a Managed Services Site), including firewalls and intrusion detection systems. This proactive approach effectively prevents malware and unauthorized software from executing, thereby minimizing the attack surface. It also aids organizations in adhering to stringent compliance requirements such as GDPR, ensuring the protection of sensitive data.
The COVID-19 pandemic has further accelerated this trend, with 97 percent of companies acknowledging that it expedited their initiatives. This ongoing evolution underscores the necessity for businesses to adapt to technological advancements and highlights the growing significance of cybersecurity in safeguarding sensitive information.
As technology historians assert, "You can’t delegate cybersecurity for your company… You and your executives have to own it!" This statement emphasizes the vital role of leadership in navigating these changes. Moreover, case studies, such as the transition of Workforce Extensions to a Modern Workplace architecture, showcase how organizations are effectively evolving their IT services to meet contemporary demands. This evolution not only enhances operational efficiency but also ensures that robust security measures, such as encryption and multi-factor authentication, are implemented to guard against emerging threats.
In today's business environment, the role of business IT services companies is paramount for ensuring operational efficiency and security. These firms deliver a diverse array of technology-related solutions that empower organizations to navigate the complexities of the digital world while minimizing disruptions from IT challenges. By leveraging managed IT support, cybersecurity measures, cloud services, and compliance assistance, businesses can concentrate on their core objectives and drive growth.
Key insights throughout this discussion underscore the significance of these services across various sectors, especially in maintaining compliance with regulations and safeguarding sensitive data. The evolution of IT services companies illustrates their adaptability to technological advancements, transitioning from internal IT departments to specialized providers that offer innovative solutions tailored to meet the distinct needs of modern enterprises. The focus on robust cybersecurity, including proactive measures like application allowlisting, highlights the necessity of these services in defending against emerging threats.
Ultimately, the importance of business IT services companies cannot be overstated. As organizations increasingly embrace digital transformation, investing in reliable IT support becomes essential for sustaining competitive advantage. Companies are urged to prioritize their IT strategies, ensuring alignment with industry standards and effective risk mitigation. By doing so, businesses not only enhance their operational capabilities but also position themselves for long-term success in an ever-evolving digital landscape.
What is a business IT services company?
A business IT services company provides a comprehensive range of technology-related services aimed at enhancing the operational capabilities of enterprises. These services include managed IT assistance, security solutions, cloud computing, data management, and IT consulting.
What is the primary goal of business IT services companies?
The primary goal is to empower clients to operate efficiently and securely, allowing them to navigate the complexities of technology without the distractions of IT challenges.
Can you provide an example of a business IT services company?
Cyber Solutions is an example of a business IT services company that offers extensive IT and security packages designed to protect enterprises, enhance operational efficiency, and reduce costly downtime.
What cybersecurity solutions does Cyber Solutions offer?
Cyber Solutions offers cybersecurity solutions that include endpoint protection, threat detection, and compliance simplification, specifically tailored for small to medium enterprises.
Why is the demand for corporate IT solutions expected to grow?
The demand for corporate IT solutions is projected to experience significant growth by 2025, as organizations seek to remain competitive and compliant in a rapidly evolving technological environment.
What factors should companies consider when evaluating managed IT providers?
Companies should consider factors such as customer support history and compatibility with existing infrastructure when evaluating managed IT providers.
How can effective IT services impact operational efficiency?
Successful IT services firms can bolster operational efficiency and security. For example, prompt incident management can lead to a 30% reduction in downtime, significantly improving operational continuity.
What are the risks of neglecting cybersecurity?
Neglecting cybersecurity can create substantial liabilities for organizations, especially as they expand, highlighting the necessity of prioritizing robust IT support and a layered cybersecurity approach.