Introduction
Understanding the intricacies of the Cybersecurity Maturity Model Certification (CMMC) is increasingly vital for organizations within the Defense Industrial Base. As mandatory compliance looms on the horizon, businesses must navigate a complex landscape of security requirements to safeguard sensitive information effectively. This guide provides a comprehensive roadmap to achieving CMMC compliance, detailing essential steps and best practices that not only ensure adherence but also enhance overall cybersecurity posture. As the deadline approaches, organizations must consider:
- How can they prepare to meet these stringent requirements?
- How can they secure their competitive edge in the defense contracting arena?
Understand CMMC: The Cybersecurity Maturity Model Certification
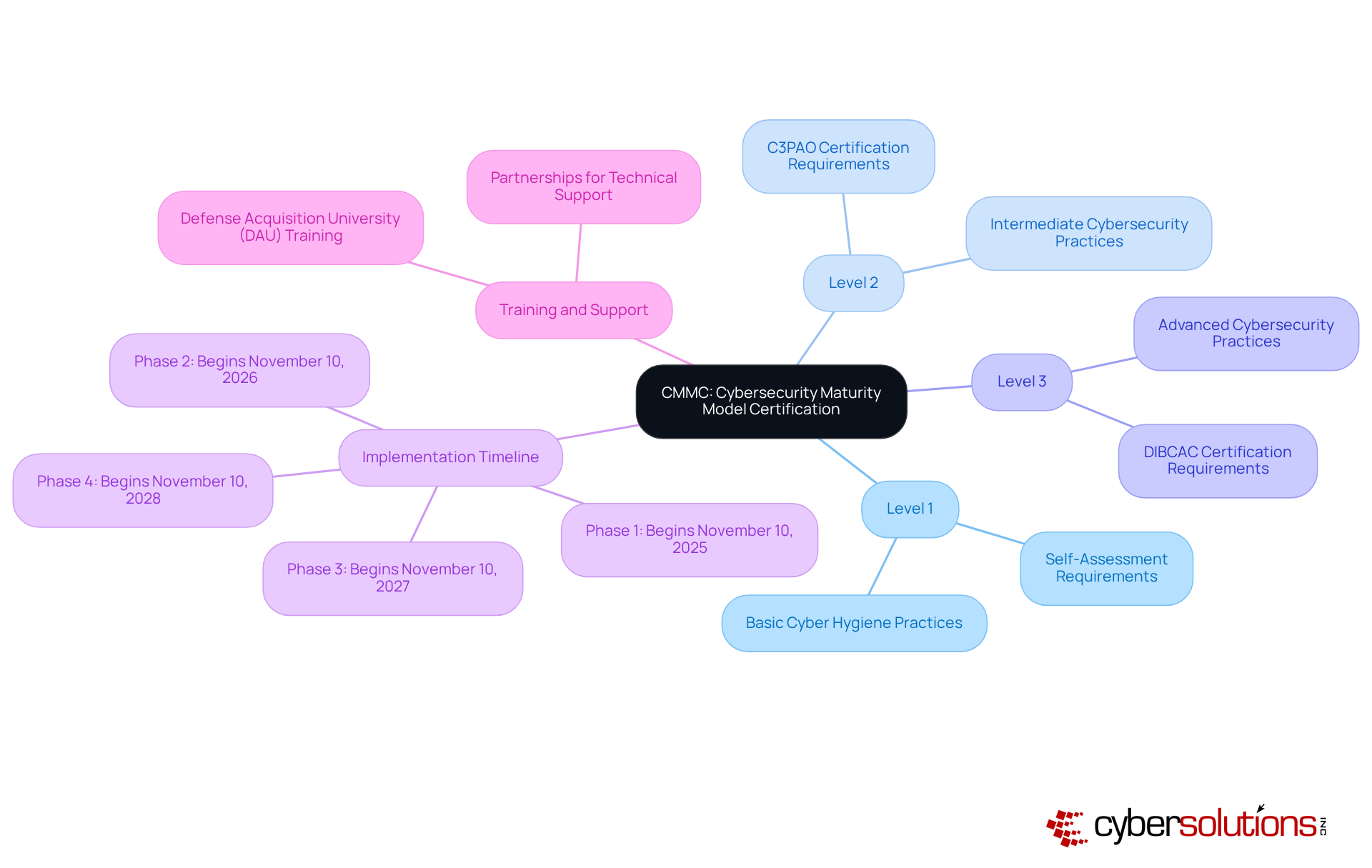
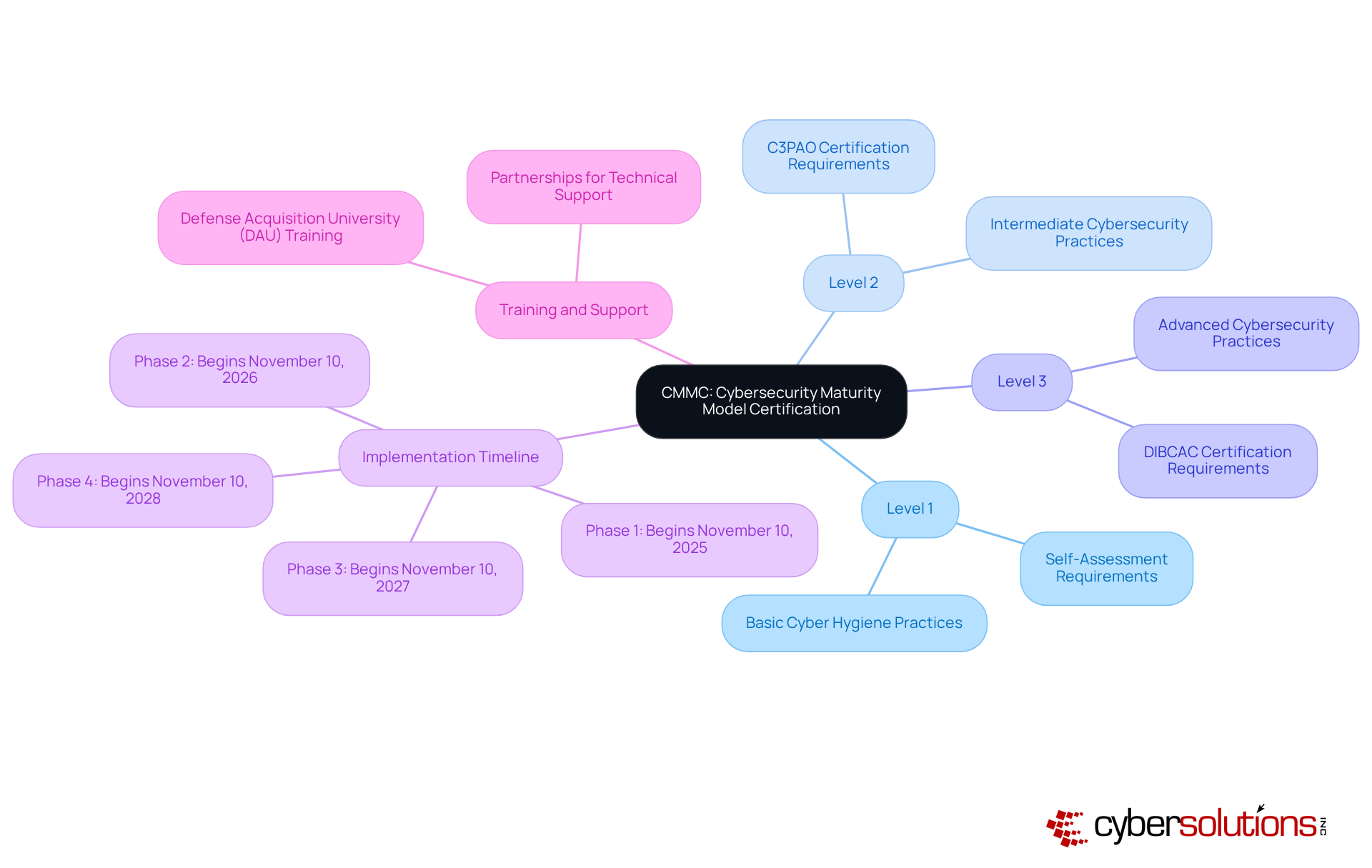
The Cybersecurity Maturity Model Certification (CMMC) represents a critical framework established by the Department of Defense, aimed at fortifying the cybersecurity posture of entities within the Defense Industrial Base. This initiative is imperative for contractors tasked with protecting sensitive information, including Controlled Unclassified Information (CUI) and Federal Contract Information (FCI).
The framework delineates various levels, each accompanied by specific criteria that entities must fulfill to achieve certification. Compliance is mandatory; it will become obligatory for all contractors starting November 10, 2025.
Understanding the CMMC framework is vital for organizations aiming to navigate the intricate landscape of security requirements and prepare for forthcoming changes. As emphasized by the DoD, adherence to CMMC standards is essential for maintaining eligibility and competitiveness in the evolving defense contracting arena.
Explore CMMC Levels: Foundational to Expert Compliance
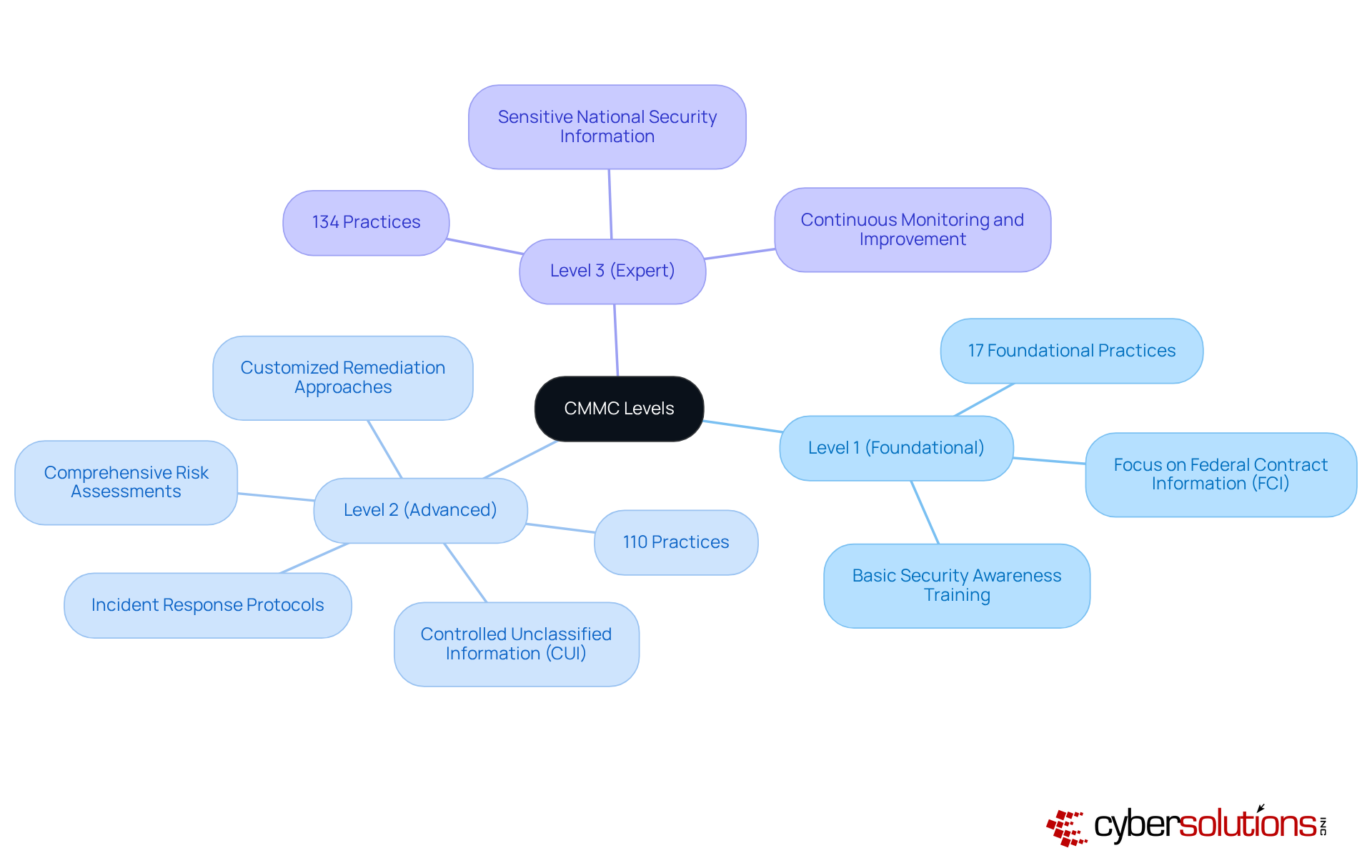
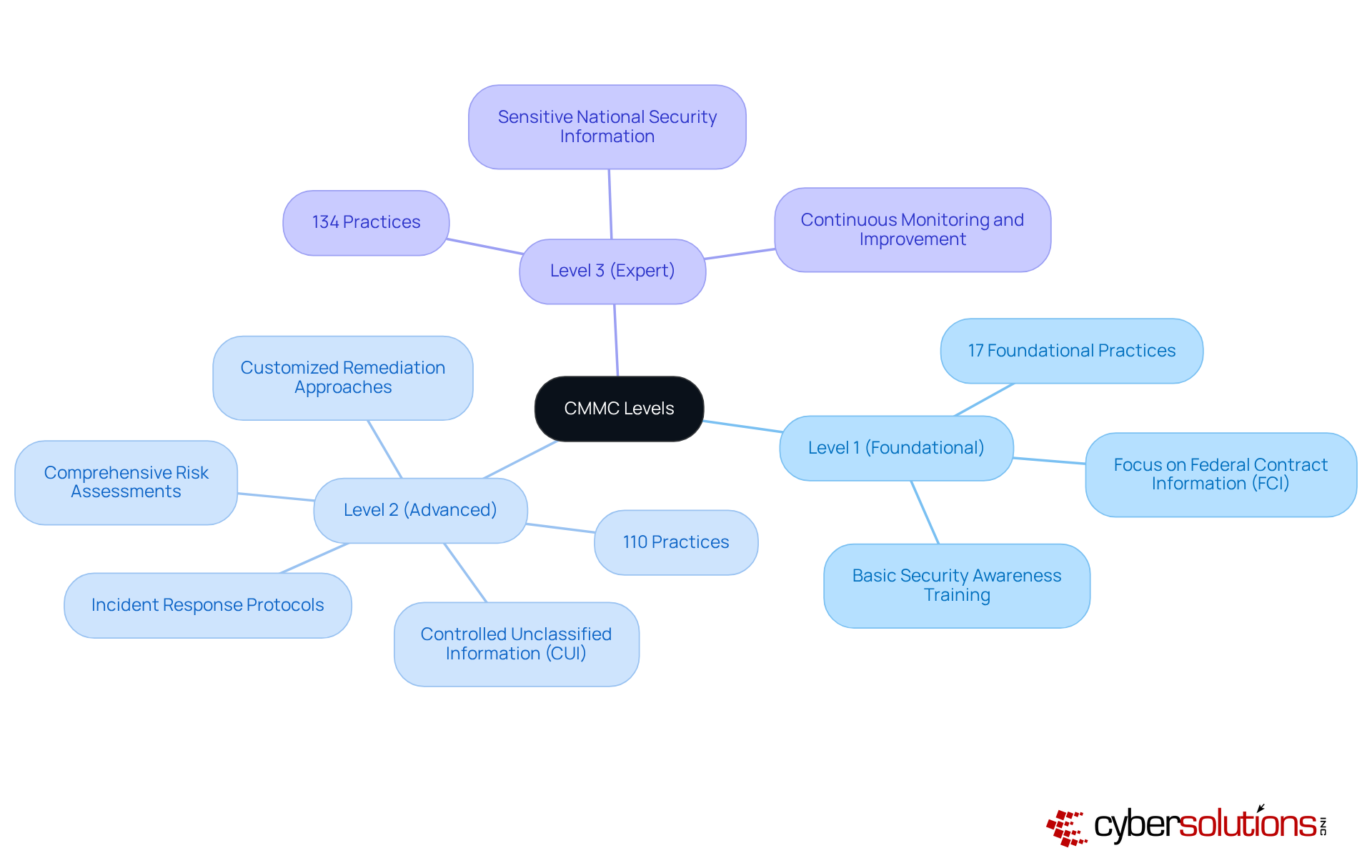
CMMC encompasses three distinct levels of compliance, each meticulously designed to meet varying security requirements:
- Level 1 (Foundational): This entry-level tier prioritizes essential safeguarding measures for Federal Contract Information (FCI). Organizations must implement 17 foundational practices, including access control and basic security awareness training.
- Level 2 (Advanced): Targeted at entities managing Controlled Unclassified Information (CUI), Level 2 mandates the execution of 110 practices in alignment with security standards. Key components include risk management and comprehensive risk assessments, ensuring a more robust security framework. Customized remediation approaches are vital at this level, as companies must address regulatory gaps through policy updates and system enhancements.
- Level 3 (Expert): Tailored for entities managing sensitive national security information, Level 3 incorporates 134 practices that substantially elevate security measures. This level requires continuous monitoring and improvement to effectively safeguard critical data.
Understanding these levels is crucial for companies aiming to assess their current security posture and identify necessary actions for compliance. For instance, case studies illustrate that entities actively engaging in assessments and seeking expert guidance during evaluations not only meet regulatory requirements but also enhance their overall security posture. Alarmingly, over 16% of Defense Industrial Base contractors reported minimal to no preparedness for certification standards, underscoring the urgency of addressing these challenges. Furthermore, the staged implementation schedule commences on November 10, 2025, highlighting the importance for organizations to seek and assess subcontractor compliance to mitigate potential legal risks under the False Claims Act for erroneous attestations. Specialized guidance and support during the official assessment are imperative for achieving certification and ensuring ongoing management.
Follow the Steps to Achieve CMMC Compliance: A Practical Guide
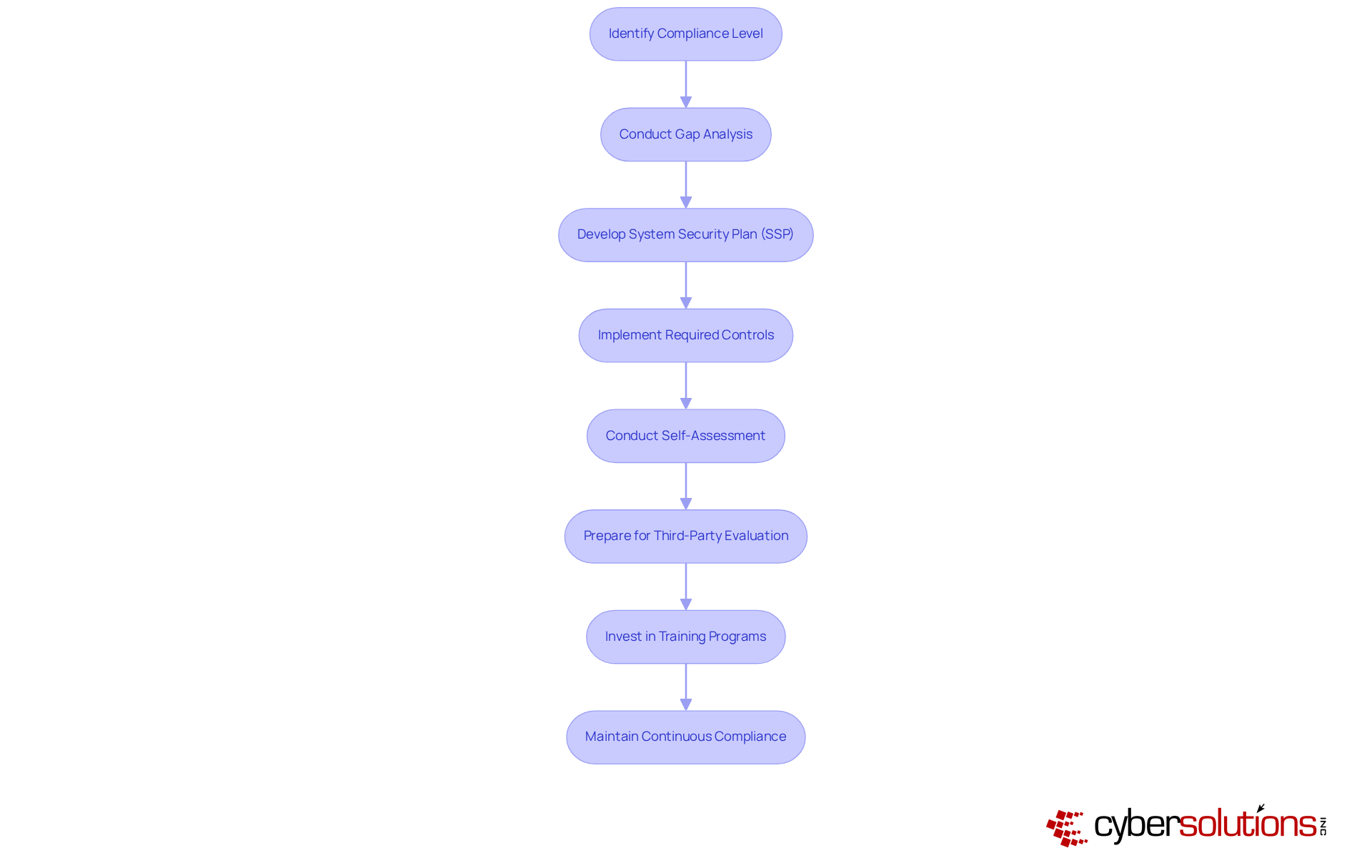
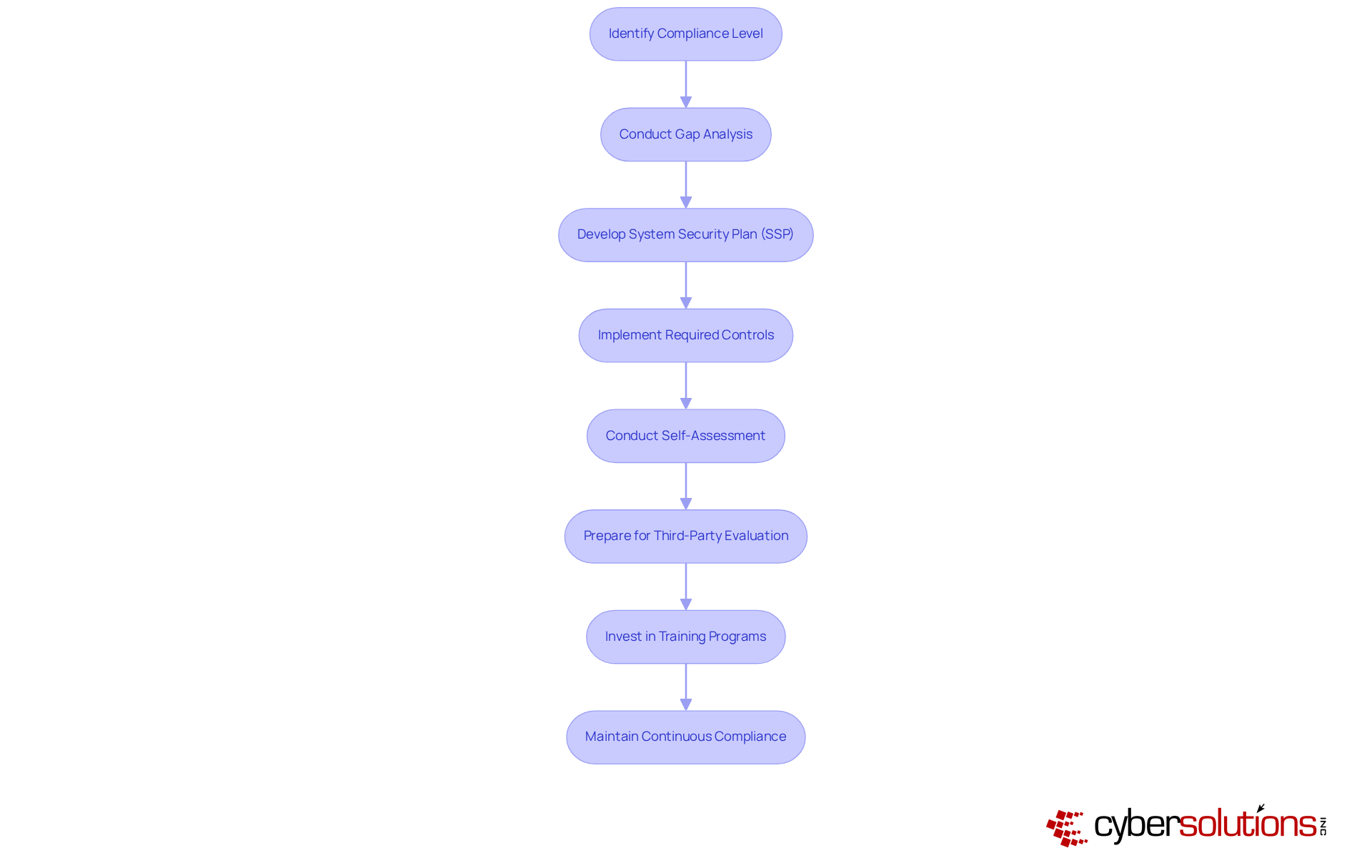
To achieve compliance, it is imperative to follow these essential steps:
- Identify Your Necessary Compliance Level: Evaluate the kind of information your entity manages to ascertain the suitable compliance tier. Comprehending the specific requirements for each level is essential; entities at Level 1 must meet basic security practices, while those at Level 3 need to implement advanced measures.
- Conduct a Gap Analysis: Assess your existing cybersecurity practices in relation to the criteria of the selected certification level. This analysis is vital for identifying areas for improvement and prioritizing actions based on their impact and complexity. A thorough gap analysis assists entities in aligning their practices with CMMC cybersecurity maturity model certification standards, ensuring they are well-prepared for certification.
- Develop a System Security Plan: Create a detailed SSP that outlines how your organization will meet the compliance requirements, including specific policies and procedures. This plan should reflect the findings from your gap analysis and serve as a roadmap for compliance.
- Implement Required Controls: Based on your gap analysis, implement the necessary security controls and practices to meet the requirements of your designated CMMC level. This may involve enhancing existing measures or adopting new technologies to bolster your CMMC cybersecurity posture. Remember, achieving Level 3 certification involves implementing advanced security measures such as continuous monitoring, incident response, and a formal risk management strategy. Cyber Solutions provides resources to streamline this process, offering risk evaluations and continuous regulatory monitoring customized to your requirements.
- Conduct a Self-Assessment: Perform a self-assessment to ensure that all controls are in place and functioning effectively. Frequent self-evaluations assist in sustaining momentum and responsibility throughout the adherence process, enabling organizations to recognize and tackle any gaps proactively.
- Schedule an Official Assessment: Collaborate with a Certified Third-Party Assessment Organization (C3PAO) to arrange your official assessment. Early engagement with accredited bodies can provide valuable insights and guidance on the assessment expectations, facilitating a smoother certification process.
- Invest in Training Programs: To foster a security-conscious culture, invest in training programs for employees at all levels. Employees must comprehend their responsibilities in protecting sensitive information and following security policies, which is essential for ensuring adherence.
- Maintain Compliance: After achieving certification, establish processes for ongoing monitoring and improvement to maintain compliance with CMMC standards. Ongoing monitoring and routine evaluations are crucial for detecting vulnerabilities and guaranteeing the effectiveness of security measures, which are essential components of CMMC cybersecurity, fostering long-term resilience in your security practices. As Perry Keating highlights, the aim is not merely to pass an evaluation but to foster a culture of ongoing enhancement in digital security. Furthermore, Cyber Solutions offers services to assist organizations in swiftly recognizing and addressing threats, ensuring business continuity and adherence to security standards.
Overcome Compliance Challenges: Tips and Best Practices
Achieving compliance is crucial yet challenging. To navigate these challenges, consider the following strategies:
- Educate Your Team: It is essential that all employees recognize their vital role in upholding cybersecurity standards. Regular training sessions not only enhance awareness but also equip your workforce to respond adeptly to potential threats. Research indicates that organizations with robust training programs see a significant improvement in adherence outcomes.
- Document Everything: Meticulous record-keeping of all security practices, policies, and assessments is paramount. Comprehensive documentation is critical for demonstrating adherence during evaluations and inspections, as inadequate records can hinder certification efforts.
- Utilize Technology: Implement tools and software designed to automate regulatory processes, monitor systems, and provide real-time alerts for potential security breaches. This strategy not only streamlines adherence to regulations but also bolsters your overall security posture.
- Engage Experts: Hiring consultants or managed service providers with a specialization in cybersecurity standards can be invaluable. Their expertise will guide your organization through the complexities of compliance, ensuring that all necessary requirements are met efficiently.
- Stay Informed: Keeping up with changes in regulations and best practices is essential. Follow industry news and engage in relevant training and workshops, as ongoing education is vital in an ever-evolving regulatory landscape.
By proactively addressing these challenges, your organization can significantly enhance its compliance efforts and meet the requirements. Companies that prepare now for compliance, particularly as CMMC requirements are poised to be enforced in forthcoming contract solicitations.

Conclusion
Achieving compliance with the Cybersecurity Maturity Model Certification (CMMC) is not merely a regulatory requirement; it is a crucial step for organizations within the Defense Industrial Base to protect sensitive information and maintain competitiveness in a rapidly evolving landscape. The CMMC framework, with its structured levels from foundational to expert, provides a clear pathway for organizations to enhance their cybersecurity measures and ensure they are adequately prepared for the upcoming compliance mandates.
The article outlines essential steps to navigate the complexities of CMMC compliance effectively. Key actions include:
- Identifying the appropriate compliance level based on the information handled
- Conducting a thorough gap analysis
- Developing a comprehensive System Security Plan
- Implementing necessary controls
Additionally, fostering a culture of continuous compliance through ongoing training and monitoring is vital for long-term success. By addressing challenges such as team education, meticulous documentation, and leveraging technology, organizations can significantly bolster their cybersecurity posture.
In light of the impending CMMC requirements set to take effect in 2025, proactive engagement in compliance efforts is imperative. Organizations that invest in understanding and achieving CMMC standards not only safeguard their operations but also position themselves favorably in the competitive defense contracting arena. Embracing the CMMC journey is an opportunity to not only meet regulatory expectations but to cultivate a resilient cybersecurity culture that prioritizes the protection of sensitive data.
Frequently Asked Questions
What is the Cybersecurity Maturity Model Certification (CMMC)?
The CMMC is a framework established by the Department of Defense to enhance the cybersecurity posture of entities within the Defense Industrial Base, particularly those tasked with protecting sensitive information like Controlled Unclassified Information (CUI) and Federal Contract Information (FCI).
Why is CMMC important for contractors?
CMMC is crucial for contractors as it sets mandatory cybersecurity standards that must be met to safeguard sensitive information, ensuring that entities remain eligible and competitive for Department of Defense contracts.
What are the compliance requirements for CMMC?
Compliance with CMMC is mandatory, and all contractors seeking DoD contracts must achieve certification by November 10, 2025. The framework includes various levels, each with specific criteria that organizations must fulfill.
How does CMMC affect eligibility for DoD contracts?
Adherence to CMMC standards is essential for maintaining eligibility for DoD contracts. Organizations must comply with the framework to remain competitive in the defense contracting landscape.
When will CMMC certification become mandatory for contractors?
CMMC certification will become mandatory for all contractors seeking Department of Defense contracts starting November 10, 2025.
List of Sources
- Understand CMMC: The Cybersecurity Maturity Model Certification
- Department of Defense Releases Long-Anticipated Final Rule Implementing the Cybersecurity Maturity Model Certification Program | Insights | Mayer Brown (https://mayerbrown.com/en/insights/publications/2025/09/department-of-defense-releases-long-anticipated-final-rule-implementing-the-cybersecurity-maturity-model-certification-program)
- With CMMC rule final, DoD focused on training, small business relief | Federal News Network (https://federalnewsnetwork.com/acquisition-policy/2025/09/with-cmmc-rule-final-dod-focused-on-training-small-business-relief)
- DoD Releases Long-Awaited Final Rule Implementing Cybersecurity Maturity Model Certification Contract Clause // Cooley // Global Law Firm (https://cooley.com/news/insight/2025/2025-09-25-dod-releases-long-awaited-final-rule-implementing-cybersecurity-maturity-model-certification-contract-clause)
- CMMC Goes Live: New Cybersecurity Requirements for Defense Contractors | Insights | Holland & Knight (https://hklaw.com/en/insights/publications/2025/09/cmmc-goes-live-new-cybersecurity-requirements)
- business.defense.gov (https://business.defense.gov/Engage/News/Article/4303493/its-official-cmmc-has-landed)
- Explore CMMC Levels: Foundational to Expert Compliance
- Countdown to CMMC Compliance: Are You Ready? (https://cohnreznick.com/insights/countdown-to-cmmc-compliance-are-you-ready)
- jdsupra.com (https://jdsupra.com/legalnews/leveling-up-will-cmmc-contract-1317179)
- natlawreview.com (https://natlawreview.com/article/recapping-cmmc-level-3-considerations-government-contractors-0)
- gentrylocke.com (https://gentrylocke.com/article/pentagon-announces-final-rule-implementing-cmmc-effective-november-10-2025)
- DoD Releases Long-Awaited Final Rule Implementing Cybersecurity Maturity Model Certification Contract Clause // Cooley // Global Law Firm (https://cooley.com/news/insight/2025/2025-09-25-dod-releases-long-awaited-final-rule-implementing-cybersecurity-maturity-model-certification-contract-clause)
- Follow the Steps to Achieve CMMC Compliance: A Practical Guide
- Pentagon to officially implement CMMC 2.0 requirements in contracts by Nov. 10 | News & Events | Clark Hill PLC (https://clarkhill.com/news-events/news/pentagon-to-officially-implement-cmmc-2-0-requirements-in-contracts-by-nov-10)
- CMMC Goes Live: New Cybersecurity Requirements for Defense Contractors | Insights | Holland & Knight (https://hklaw.com/en/insights/publications/2025/09/cmmc-goes-live-new-cybersecurity-requirements)
- What you need to know to achieve CMMC compliance | Federal News Network (https://federalnewsnetwork.com/commentary/2025/08/what-you-need-to-know-to-achieve-cmmc-compliance)
- Pentagon finalizes CMMC rule, requiring continuous compliance across defense supply chain in three-year rollout - Industrial Cyber (https://industrialcyber.co/regulation-standards-and-compliance/pentagon-finalizes-cmmc-rule-requiring-continuous-compliance-across-defense-supply-chain-in-three-year-rollout)
- Overcome Compliance Challenges: Tips and Best Practices
- dnv.us (https://dnv.us/assurance/articles/the-new-era-of-cmmc-compliance-is-no-longer-optional)
- exostar.com (https://exostar.com/blog/cmmc-compliance/overcoming-common-challenges-in-nist-cmmc-self-assessments-2)
- businesswire.com (https://businesswire.com/news/home/20251016636565/en/Strike-Graph-Launches-Free-Guided-CMMC-Self-Assessment-and-Compliance-Toolkit-to-Help-DoD-Contractors-Navigate-Upcoming-DFARS-Final-Rule)
- CMMC Compliance Made Practical: Strategies That Actually Work For Contractors (https://cybersecinvestments.com/2025/09/cmmc-compliance-strategies-for-contractors)
- quzara.com (https://quzara.com/blog/cmmc-compliance-checklist-2025-edition)