Introduction
Local IT serves as the backbone of modern organizations, playing a pivotal role in managing essential technology resources that drive productivity and security. In an era where cyber threats are becoming increasingly sophisticated, C-suite leaders must acknowledge the immense value of local IT strategies—not only for safeguarding sensitive data but also for enhancing operational efficiency. Yet, the path to effective local IT management is fraught with challenges. Resource constraints, compliance issues, and the need for continuous employee training all present significant hurdles. How can leaders navigate these complexities to unlock the full potential of their local IT infrastructure and drive organizational success?
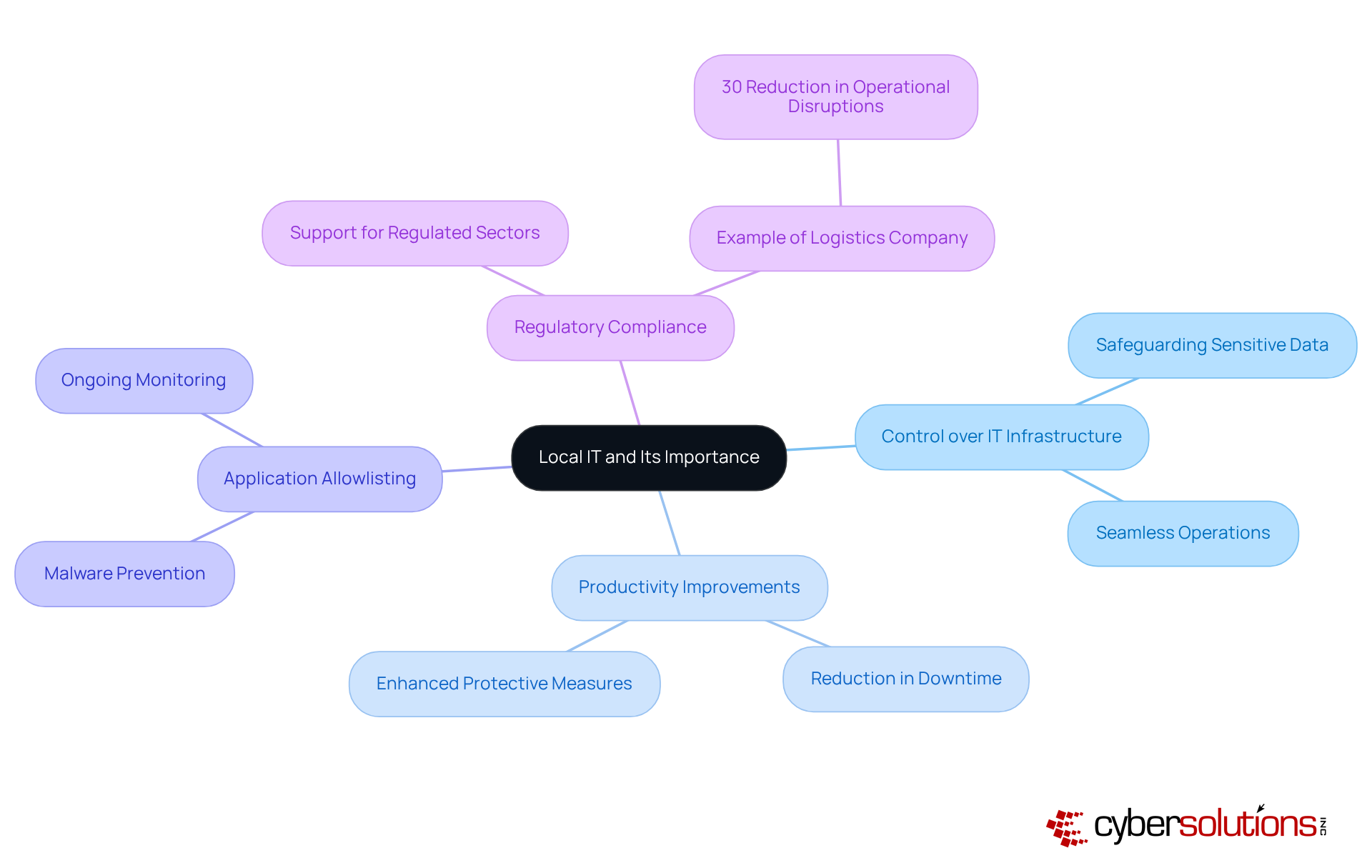
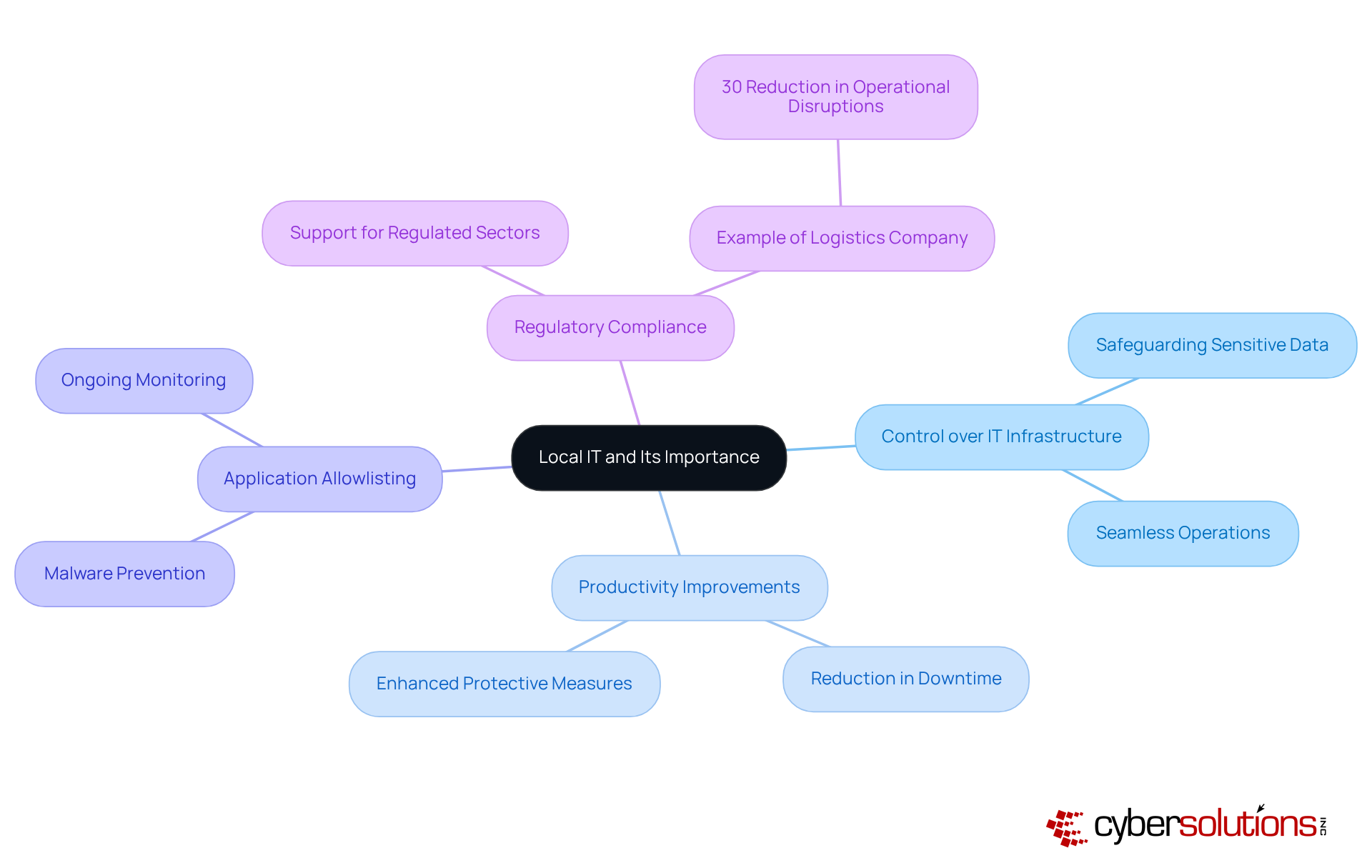
Define Local IT and Its Importance for Organizations
Local IT is crucial for managing the information technology resources and services that operate within a company's premises, which include hardware, software, networks, and data handling systems. Its significance is underscored by the control it provides organizations over their operations—an essential element for efficiency and ensuring seamless operations. Efficient local IT oversight results in substantial advancements in productivity, reduced downtime, and cost savings, which are critical in today's landscape where technologies are increasingly sophisticated.
A key component of this protection is antivirus software, which proactively prevents unauthorized software from executing, thereby mitigating the risk of malware and ensuring data integrity. The capabilities of firewalls facilitate ongoing monitoring of application activity and network traffic, further bolstering security. Additionally, local IT plays a crucial role in helping organizations in regulated industries, such as healthcare and finance, comply with industry regulations.
For example, a logistics company that adopted a robust IT security framework alongside reported a 30% reduction in operational disruptions, which directly correlates with improved service delivery and customer satisfaction. By grasping the nuances of local IT and the intricacies of technology management, C-suite leaders can make decisions that align with their organizational objectives and risk management strategies, ultimately fostering success in local IT in their respective domains.
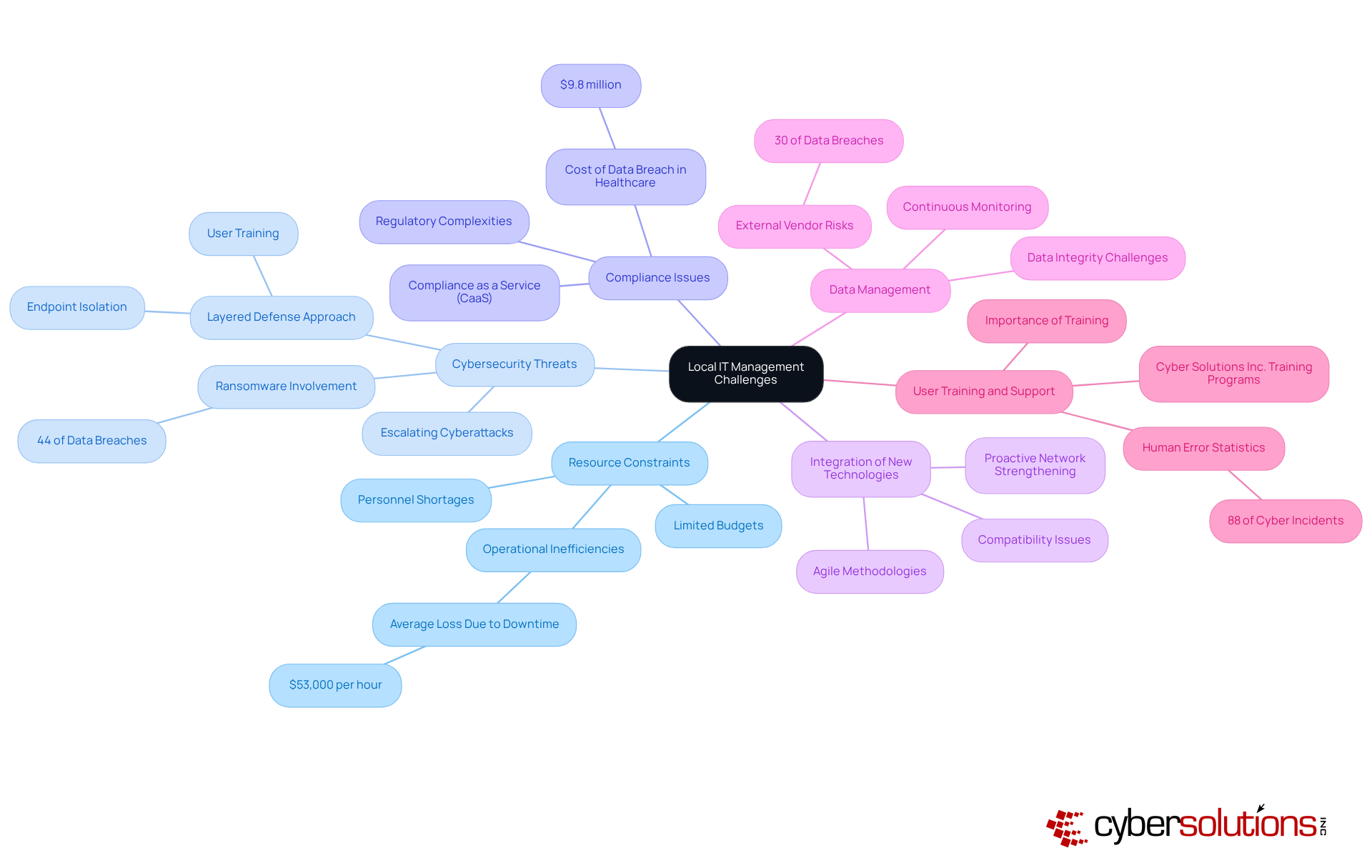
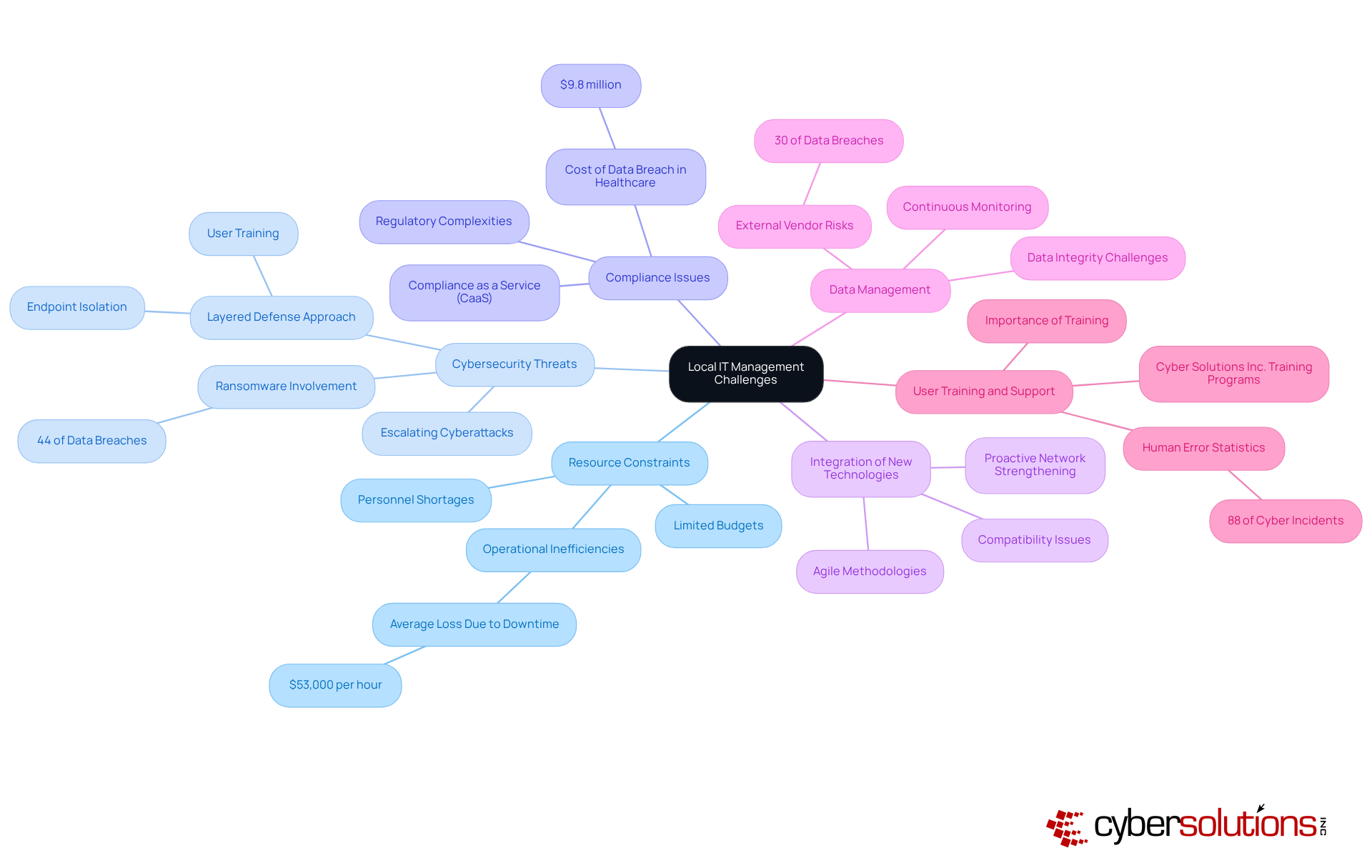
Identify Common Challenges in Local IT Management
Local IT management presents several significant challenges that C-suite leaders must navigate to ensure the success of local IT.
- Resource Constraints: Organizations frequently grapple with resource limitations, which hinders their ability to maintain and upgrade IT systems effectively. This limitation can lead to increased downtime and operational inefficiencies, with businesses losing an average of $53,000 per hour due to ransomware-related downtime. The need for immediate action and specialized expertise is critical, as demonstrated by Cyber Solutions Inc.'s rapid deployment strategies that have proven effective in minimizing damage during incidents.
- Cybersecurity Threats: The sophistication of cyberattacks continues to escalate, with ransomware involved in 44% of data breaches in 2025. Organizations must remain vigilant, continuously updating their defenses to protect sensitive data and mitigate risks associated with evolving threats. A layered approach, including endpoint isolation and threat detection, is essential for enhancing recovery and maintaining robust cybersecurity.
- Compliance Issues: Navigating the complexities of regulatory compliance is particularly daunting for entities in highly regulated sectors such as healthcare and finance. The average cost of non-compliance reached $9.8 million, underscoring the importance of compliance and robust security measures. Cyber Solutions Inc.'s compliance solutions offer end-to-end services that simplify compliance processes, helping organizations avoid potential penalties while ensuring they meet strict standards like HIPAA and PCI-DSS.
- Integration of New Technologies: As technology evolves, integrating new solutions with existing systems can lead to compatibility issues and operational disruptions. Organizations must adopt agile methodologies to enhance project success rates, as traditional project management approaches often fall short. Proactive network strengthening approaches can enable smoother transitions and improved configurations.
- Data Management Challenges: Ensuring data integrity and security while managing large volumes of information remains a persistent challenge. With around 30% of organizations experiencing data breaches, effective approaches are essential to protect against outside threats. Continuous monitoring and proactive risk assessments, as part of Cyber Solutions Inc.'s CaaS offerings, can help organizations maintain compliance and protect sensitive information.
- Training and Support: Providing adequate training and support for employees to effectively utilize IT resources is often overlooked. This oversight can lead to inefficiencies, as untrained staff may struggle with technology, highlighting the need for comprehensive training programs. Cyber Solutions Inc. emphasizes the significance of employee training as a component of their recovery plans, ensuring that staff are prepared to identify and react to potential threats.
By acknowledging and tackling these challenges, C-suite leaders can implement strategies that enhance local IT, ultimately fostering organizational success.
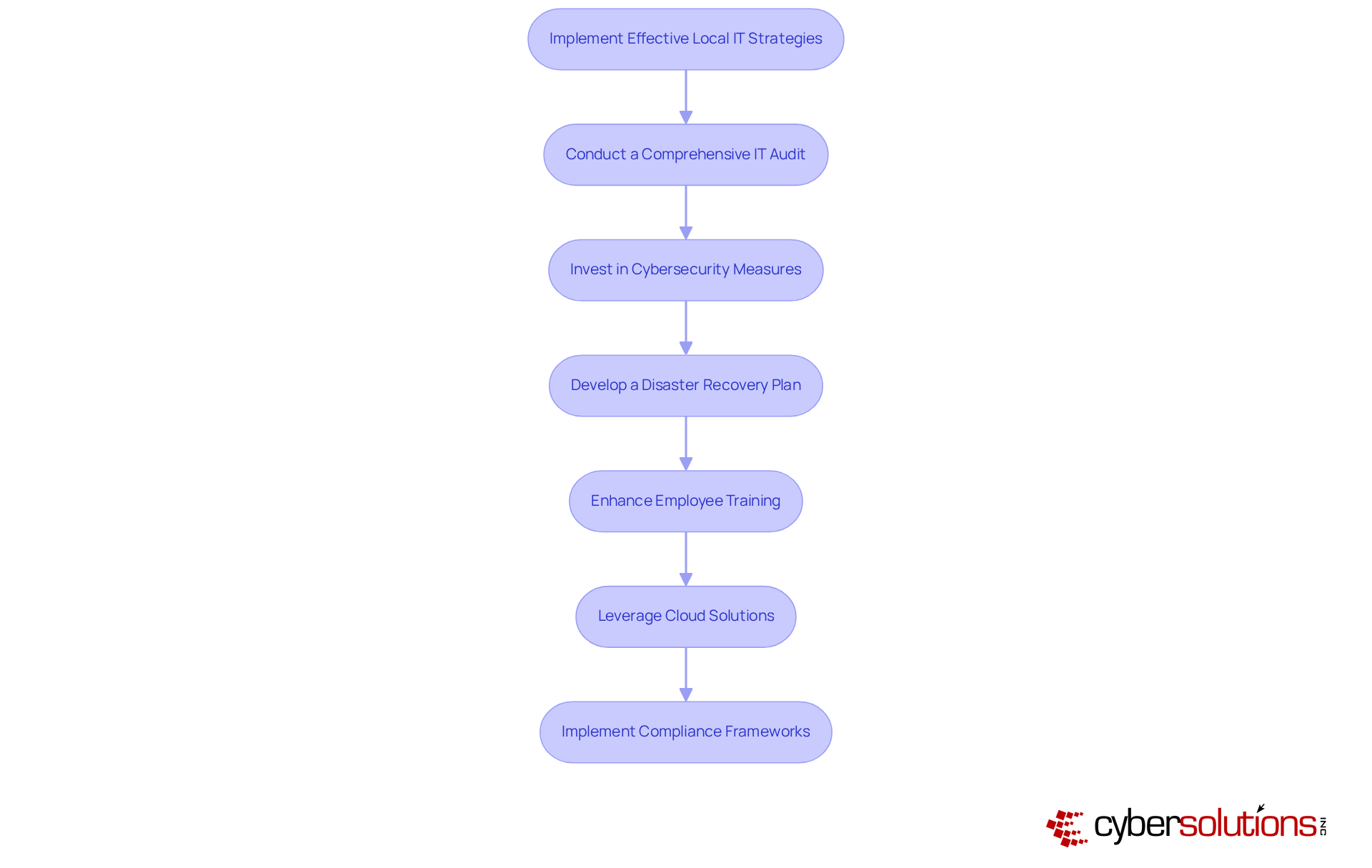
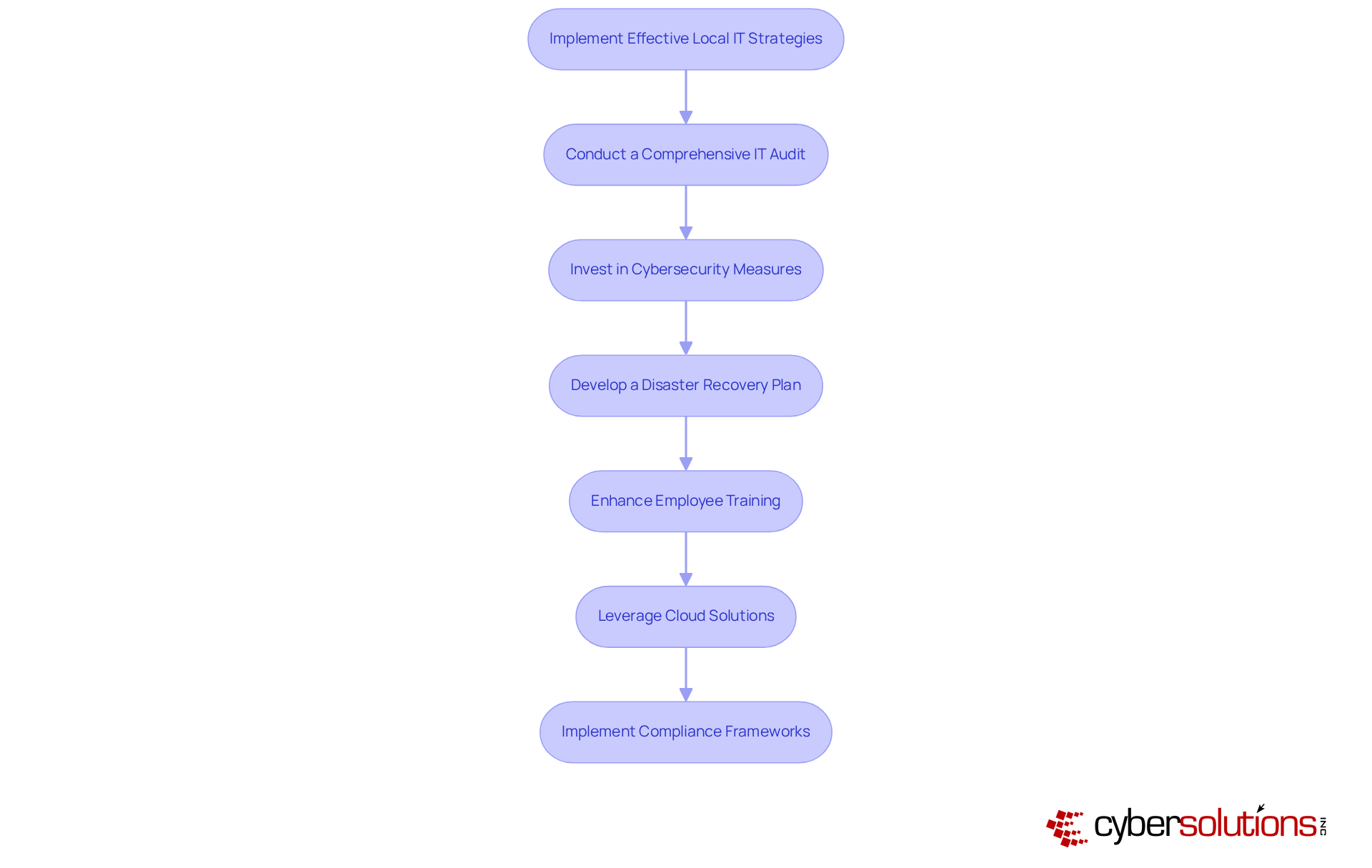
Implement Effective Local IT Strategies and Solutions
To implement effective local IT strategies, C-suite leaders must prioritize several critical actions:
- Conduct Regular Assessments: Regular assessments of IT infrastructure are essential to identify vulnerabilities and areas for improvement. A well-executed audit can uncover critical weaknesses, allowing entities to strengthen their defenses against cyber threats.
- Invest in Cybersecurity: Allocating budget for advanced cybersecurity solutions is crucial. These investments can save an average of $2.22 million annually, underscoring the financial benefits of robust cybersecurity investments.
- Develop a Backup Plan: Establishing protocols for data backup and recovery is vital to minimize downtime during incidents. With losses on companies with more than 1,000 employees surpassing $53,000, a robust recovery plan is a crucial element of risk oversight. Ongoing management for CMMC alterations can further improve these recovery approaches.
- Provide Employee Training: Ongoing training for employees on cybersecurity best practices is essential. Given that 88% of cyber incidents are attributed to human error, equipping staff with the knowledge to recognize threats can significantly reduce vulnerabilities. Cyber Solutions provides tailored remediation strategies that include training as part of compliance preparation.
- Leverage Cloud Solutions: Hybrid cloud solutions offer enhanced flexibility and scalability while maintaining control over sensitive data. As businesses increasingly move to the cloud, ensuring security in these environments is crucial.
- Implement Compliance Measures: Developing and maintaining compliance with industry regulations mitigates legal risks. Organizations that prioritize compliance not only protect themselves from potential fines but also enhance their reputation in the marketplace. Cyber Solutions provides expert guidance and support throughout the CMMC assessment process, ensuring that entities are audit-ready and can demonstrate compliance with regulations.
By implementing these approaches, organizations can significantly enhance their local IT and fortify their defenses against potential risks and obstacles.
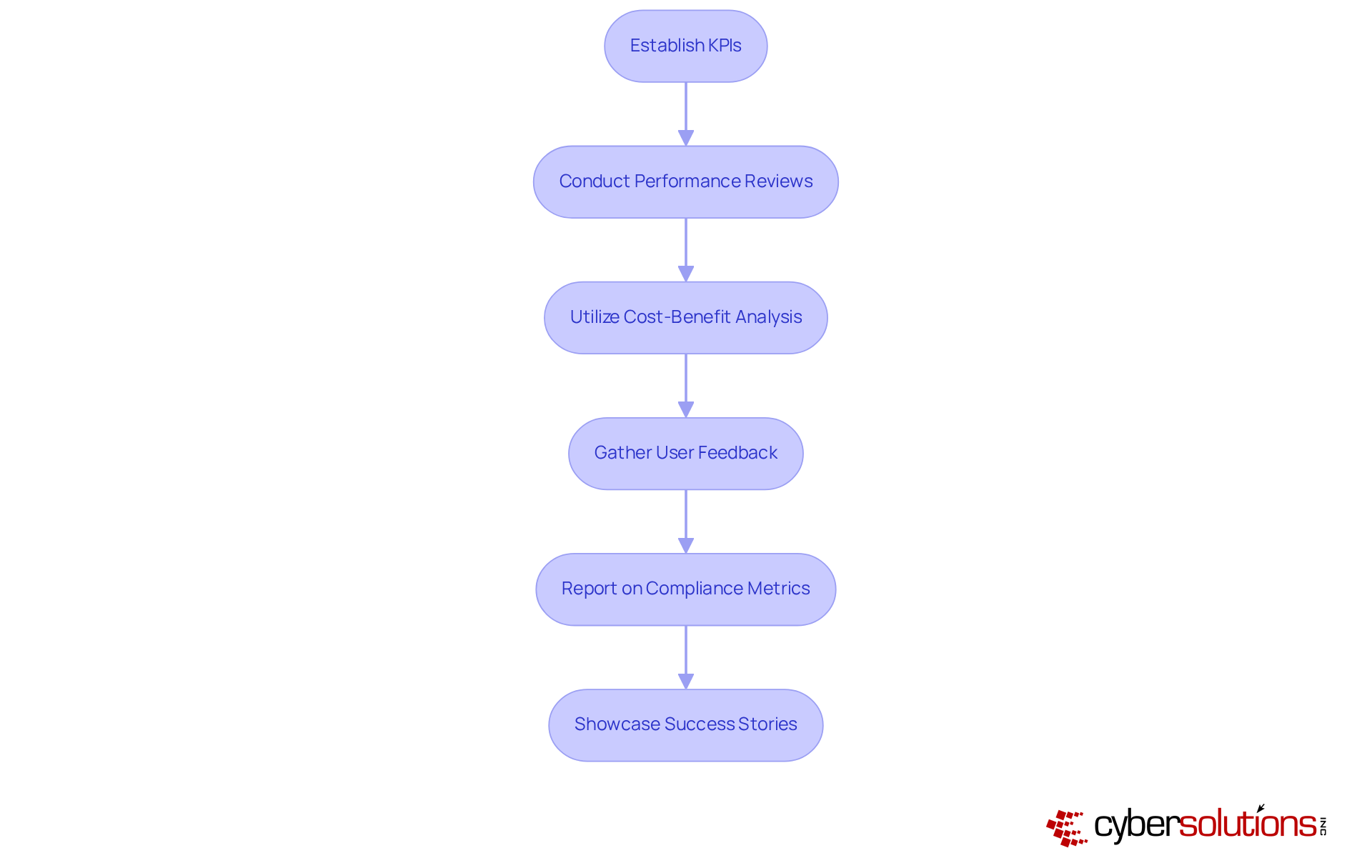
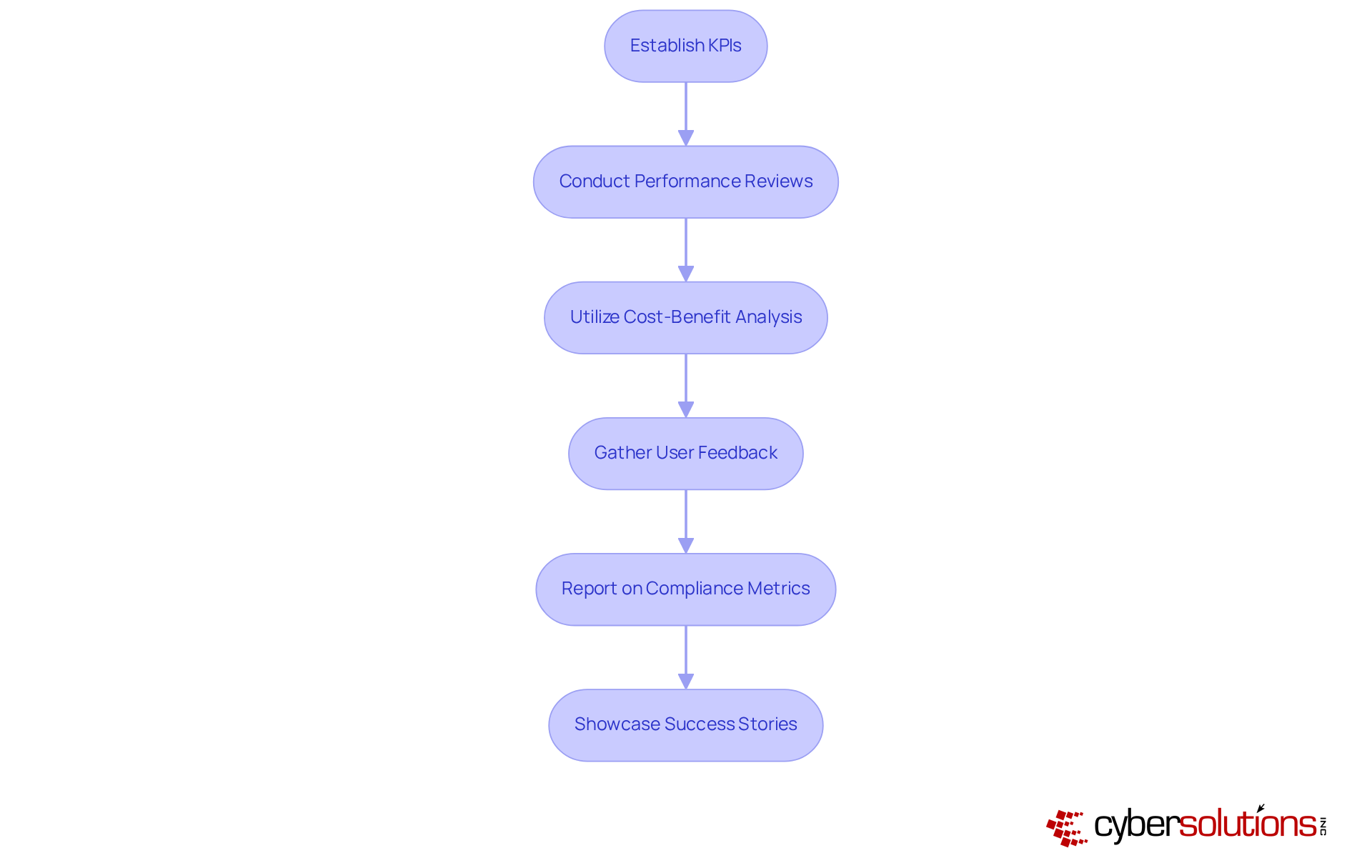
To effectively evaluate local IT performance and demonstrate ROI, C-suite leaders must take decisive steps:
- Establish KPIs: Define specific KPIs that align with overarching business objectives, such as system uptime, response times, and user satisfaction metrics. These indicators provide quantifiable measures of IT effectiveness. As Peter Drucker famously stated, "What gets measured gets managed," emphasizing the critical role of measurement in IT management.
- Schedule Reviews: Implement a schedule for periodic reviews to assess IT performance against the established KPIs. This practice not only identifies areas for improvement but also ensures that IT strategies remain aligned with business goals. Regular KPI measurement enables leaders to pinpoint strengths and weaknesses, allowing for efficient resource allocation.
- Cost-Benefit Analysis: Perform a thorough analysis of the costs associated with IT investments compared to the benefits realized, including enhanced productivity and mitigated risks. This analysis is crucial for justifying IT expenditures. For instance, entities that effectively monitor KPIs often experience substantial enhancements in operational efficiency and minimized downtime, which can lead to increased revenue.
- Collect Feedback: Actively collect feedback from employees regarding IT services to assess satisfaction levels and identify potential enhancements. User insights are invaluable for refining IT offerings and improving service delivery. Engaging employees in this process can lead to higher satisfaction rates and better alignment of IT services with user needs.
- Monitor Compliance: Monitor compliance with industry regulations such as HIPAA, PCI DSS, and GDPR, and document any incidents or breaches. Reporting on these metrics demonstrates the effectiveness of protective measures and the organization’s commitment to regulatory adherence. This is essential for maintaining trust and credibility with stakeholders.
- Highlight Success Stories: Highlight specific examples where IT initiatives have resulted in measurable improvements in efficiency or security. For example, Navistar's comprehensive health and wellness program led to over $300 million in net savings, illustrating the tangible benefits of effective performance management. These success stories reinforce the value of ongoing IT investments and serve as compelling evidence for future funding.
By systematically evaluating local IT performance and demonstrating ROI, C-suite leaders can make informed decisions regarding future local IT investments and strategies, ultimately driving organizational success.
Conclusion
Mastering local IT is not just beneficial; it is essential for C-suite leaders who aim to drive organizational success and safeguard sensitive data. In understanding the intricacies of local IT management, leaders can implement strategies that enhance operational efficiency while mitigating risks associated with cybersecurity threats and compliance issues. This proactive approach is vital in today’s landscape, where the stakes are high, and the consequences of poor IT management can be detrimental.
Key challenges such as resource constraints, evolving cybersecurity threats, and the complexities of compliance have been highlighted throughout this discussion. Effective strategies include:
- Conducting comprehensive IT audits
- Investing in cybersecurity
- Enhancing employee training
By systematically evaluating local IT performance through KPIs and user feedback, organizations can demonstrate the ROI of their IT investments, reinforcing the importance of local IT in achieving business objectives.
Ultimately, the significance of local IT extends beyond mere management; it is a cornerstone of organizational resilience and success. C-suite leaders are strongly encouraged to prioritize local IT strategies and embrace innovative solutions to navigate the complexities of modern technology. By doing so, they not only protect their organizations from potential threats but also position themselves for sustained growth and competitive advantage in an ever-evolving digital landscape.
Frequently Asked Questions
What is Local IT?
Local IT refers to the management of information technology resources and services that operate within a company's premises, including hardware, software, networks, and data handling systems.
Why is Local IT important for organizations?
Local IT is important because it provides organizations with control over their IT infrastructure, which is essential for safeguarding sensitive data and ensuring seamless operations. It leads to improved productivity, reduced downtime, and enhanced security measures.
What is application allowlisting and how does it contribute to security?
Application allowlisting is a security measure that proactively prevents unauthorized software from executing, thereby mitigating the risk of malware and ensuring compliance with industry regulations. It allows for ongoing monitoring of application activity and centralized management of allowlists.
How does Local IT support compliance in regulated sectors?
Local IT helps organizations in highly regulated sectors, such as healthcare and finance, comply with industry regulations by implementing robust IT infrastructure and security measures like application allowlisting.
Can you provide an example of the impact of Local IT on operational efficiency?
Yes, a logistics company that adopted a robust local IT infrastructure along with application allowlisting reported a 30% reduction in operational disruptions, which improved service delivery and customer satisfaction.
How can C-suite leaders benefit from understanding Local IT and application allowlisting?
By understanding Local IT and application allowlisting, C-suite leaders can make informed decisions that align with their organizational objectives and risk management strategies, ultimately fostering success in their respective domains.
List of Sources
- Define Local IT and Its Importance for Organizations
- techbullion.com (https://techbullion.com/the-role-of-a-local-it-company-in-supporting-small-businesses)
- +20 Tech & IT Quotes to Find Inspiration (https://blog.invgate.com/it-quotes)
- researchgate.net (https://researchgate.net/publication/222721166_Exploring_service_issues_within_the_IT_organisation_Four_mini-case_studies)
- spidergroup.com (https://spidergroup.com/blog/is-it-better-to-have-local-it-support)
- Enterprise Data Management: Statistics and Emerging Trends (https://passivesecrets.com/data-management-statistics)
- Identify Common Challenges in Local IT Management
- 25+ IT Project Management Statistics to Help You Grasp this PM Niche | Runn (https://runn.io/blog/it-project-management-statistics)
- Resource Management Statistics: What the Numbers Reveal | Runn (https://runn.io/blog/resource-management-statistics)
- Cybersecurity statistics 2025: trends, costs & insights (https://nordlayer.com/blog/cybersecurity-statistics-of-2025)
- 205 Cybersecurity Stats and Facts for 2026 (https://vikingcloud.com/blog/cybersecurity-statistics)
- Implement Effective Local IT Strategies and Solutions
- dlcinc.com (https://dlcinc.com/insights/mitigating-cybersecurity-risks-the-importance-of-it-audit-for-your-organization)
- 101 Cybersecurity Statistics and Trends for 2026 | NU (https://nu.edu/blog/cybersecurity-statistics)
- Case Studies – Custom IT Solutions for Businesses | Suretek Infosoft (https://suretekinfosoft.com/case_studies.html)
- 205 Cybersecurity Stats and Facts for 2026 (https://vikingcloud.com/blog/cybersecurity-statistics)
- Key Cyber Security Statistics for 2026 (https://sentinelone.com/cybersecurity-101/cybersecurity/cyber-security-statistics)
- Evaluate Local IT Performance and Demonstrate ROI
- Information Technology KPI Examples | Spider Strategies (https://spiderstrategies.com/kpi/department/information-technology)
- 101 Performance Management Quotes To Inspire Employees (https://blog.darwinbox.com/performance-management-quotes)
- Top 20 KPI Quotes - Metrics, Wisdom, and a Dash of Humor (https://pliabledynamics.com/top-20-kpi-quotes)
- researchgate.net (https://researchgate.net/publication/276275800_Beyond_Wellness_ROI_Part_II_The_Case_Study_Of_A_Major_Self-Funded_Employer)
- Key Performance Indicators Every IT Strategic Plan Needs | Dynamic Edge (https://dynedge.com/indicators-every-it-strategic-plan-needs)