
In a rapidly evolving business landscape, the necessity for tailored software solutions has reached unprecedented levels. Customized business software not only addresses the unique challenges that organizations encounter but also drives them toward enhanced efficiency and growth. As companies endeavor to maintain a competitive edge, one pivotal question emerges: how can these personalized solutions transform operational capabilities and drive profitability amidst the complexities of implementation?
This article explores seven powerful ways in which customized business software can revolutionize operations and foster sustainable success.
In today's digital landscape, the significance of cybersecurity cannot be overstated. Cyber Solutions Inc. excels in crafting software solutions designed to meet the distinct needs of various industries. By thoroughly understanding the unique challenges businesses face—such as compliance with regulations and the pursuit of efficiency—Cyber Solutions creates solutions that not only address these critical issues but also significantly enhance overall performance.
A key aspect of our approach is the integration of application allowlisting, which proactively prevents malware and unauthorized software from executing. This ensures that organizations can operate effectively while adhering to stringent security protocols. Our tailored approaches through customized software enable entities to reduce risks and improve security, allowing them to concentrate on growth without the weight of standard offerings that may not meet their needs.
Additionally, our services include:
These services provide comprehensive support for navigating regulatory complexities and minimizing the impact of cyber threats. By utilizing data analytics and insights into sector-specific challenges, Cyber Solutions enables entities to succeed in a competitive environment, ultimately fostering growth and profitability through innovative solutions.

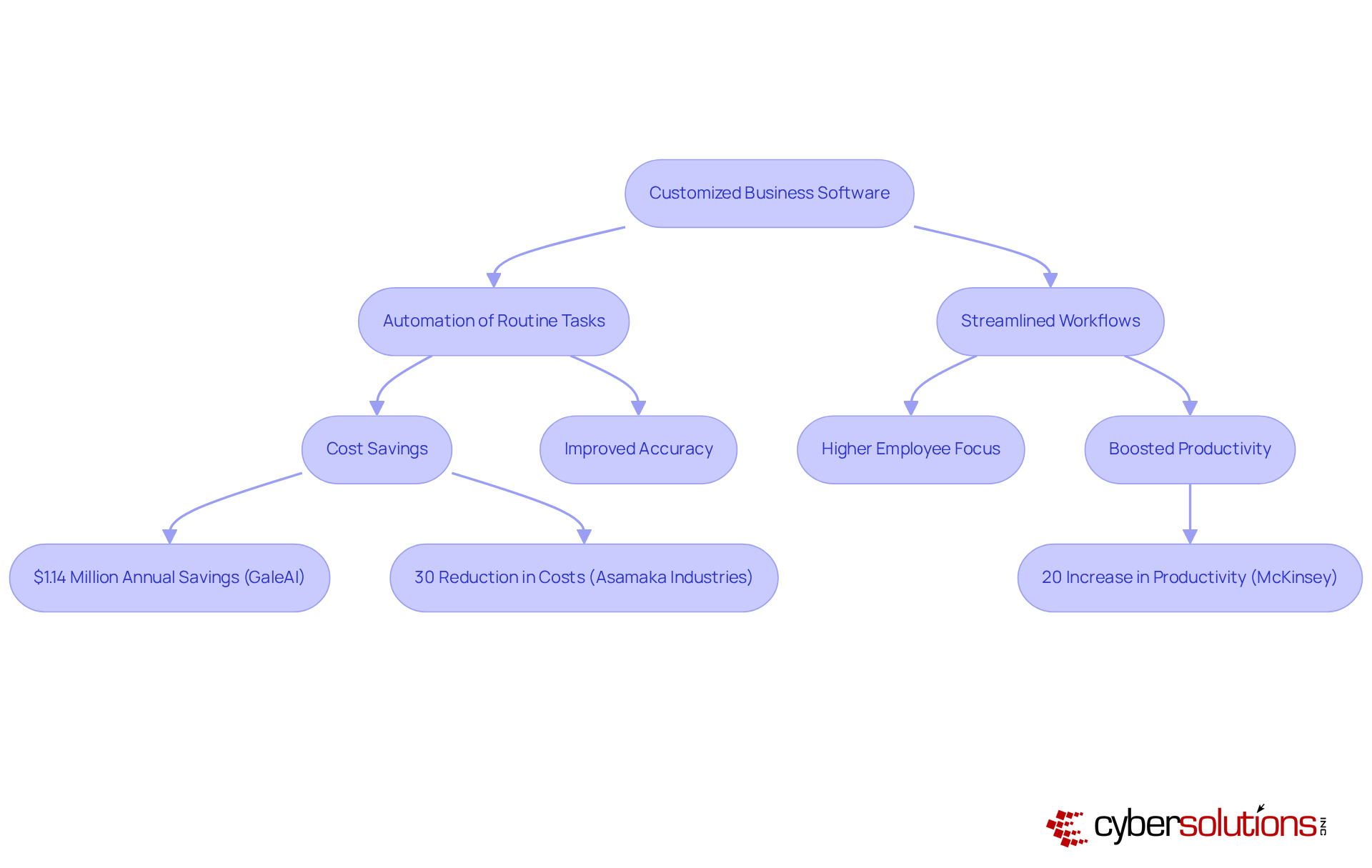
Automation is crucial in enhancing productivity by automating routine tasks and streamlining workflows. By eliminating time-consuming manual processes, businesses empower employees to concentrate on higher-value activities.
For instance, a healthcare provider that implements a tailored patient management system can improve operational efficiency, leading to improved patient care and satisfaction.
Case studies reveal that automation in healthcare has yielded significant benefits; one entity saved over $1.14 million annually through process optimization, and automation can enhance accuracy while reducing expenses by up to 30%.
Furthermore, companies that fully embrace automation technologies can boost productivity by as much as 20%, as noted by McKinsey, underscoring the significant impact of automation on their operations.
Organizations recognize these advantages, with many noting that not only does automation improve efficiency but also fosters a culture of innovation and adaptability within their teams.
However, it is vital to address the challenges associated with implementing automation, such as high initial costs and employee resistance. To navigate these challenges effectively, organizations should consider training programs to mitigate resistance to automation, ensuring a smoother transition to tailored technological solutions.
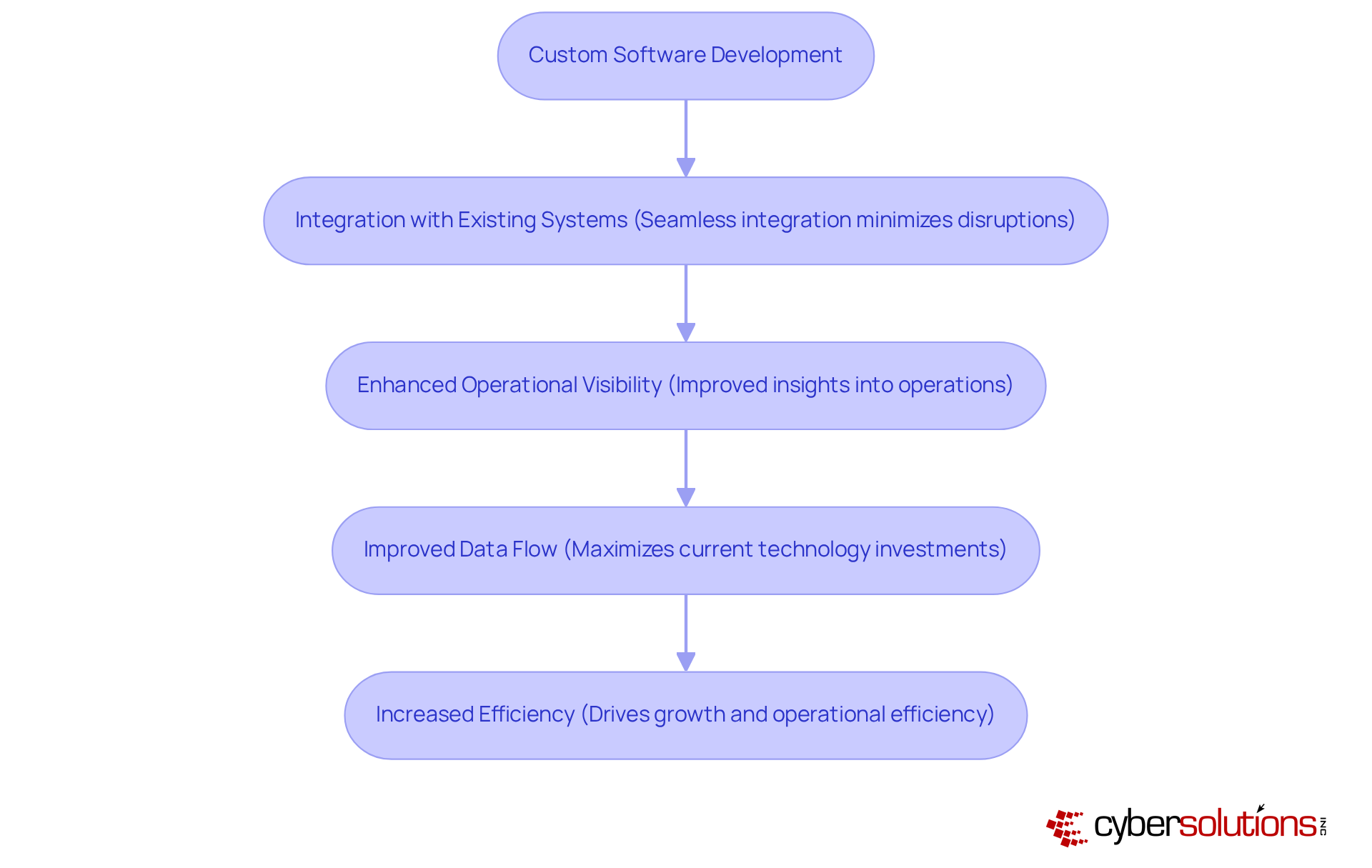
A significant advantage of customized software is their seamless integration with existing systems, a crucial factor for minimizing disruptions during implementation. This compatibility enables businesses to improve operational efficiency.
For example, a manufacturing company can enhance operational visibility and data flow by integrating a customized solution with its existing ERP platform.
Statistics indicate that organizations prioritizing compatibility with software applications experience improved productivity, highlighting the importance of integration.
IT professionals assert that effective integration not only streamline processes but also facilitate a smoother transition, ultimately driving growth and efficiency across the organization.
Insights from industry leaders, such as those from Cigna and ActiveDocs, further illustrate the practical advantages of tailored system integration.
Companies aiming to thrive in a dynamic market need customized technological solutions. By considering scalability from the outset, these organizations can utilize software that empower them to grow, eliminating the need for constant replacements.
As a company expands, its applications can evolve to accommodate an increasing number of users, data, and features. For instance, a startup may initially implement a basic customer relationship management system, which can subsequently expand to encompass advanced analytics and marketing automation as the company scales.
This adaptability not only enhances efficiency but also positions the organization for sustained growth by utilizing tailored software solutions.

In today's digital landscape, dependable assistance stands as a cornerstone of successful business operations, especially in the realm of customized software. Cyber Solutions Inc. provides continuous support, ensuring that businesses can effectively tackle challenges and keep their applications updated with the latest features and security measures. This support is particularly vital in industries like healthcare, where security measures are not just important—they are paramount.
By integrating security protocols into our cybersecurity strategy, we deliver protection against unauthorized programs. This approach guarantees that only authorized applications operate on your systems, significantly reducing vulnerabilities and assisting organizations in meeting compliance requirements. The emphasis on security is crucial for sustaining a secure and compliant operational environment, particularly in the face of evolving cybersecurity threats.
Ultimately, Cyber Solutions Inc. stands ready to address these challenges effectively, reinforcing the importance of a reliable support system. Are you prepared to enhance your organization's security posture and ensure compliance? Let us guide you through the complexities of cybersecurity, providing the dependable support you need to thrive.

Tailored applications are crucial in fortifying security against the specific vulnerabilities faced by various sectors. Financial institutions, for example, often demand solutions to protect sensitive customer data. By integrating these measures from the design phase, organizations can significantly reduce their exposure to threats.
Moreover, implementing application allowlisting within these systems can proactively prevent unauthorized program execution, further mitigating the risk of malware and ransomware attacks. This approach encompasses:
These measures enhance security and ensure compliance. Studies reveal that adopting robust security practices can reduce incidents, highlighting the imperative for companies to prioritize security in their development processes.
As we approach 2025, the emphasis on cybersecurity will intensify, with experts predicting that organizations will increasingly rely on tailored solutions to adeptly navigate the evolving threat landscape. This comprehensive approach not only cultivates trust among clients but also propels growth and efficiency.

In today’s competitive landscape, businesses navigating challenges find that customization is essential. Cyber Solutions Inc. understands that every organization, regardless of size, deserves access to tailored software solutions. By collaborating closely with clients to understand their unique needs, we create software that delivers efficiency without sacrificing quality or functionality.
Our approach not only simplifies budgeting but also eliminates unexpected IT expenses, empowering organizations to implement strategies that fosters growth without straining their resources. This comprehensive support and security package significantly enhances operational efficiency, making it an optimal choice for businesses.
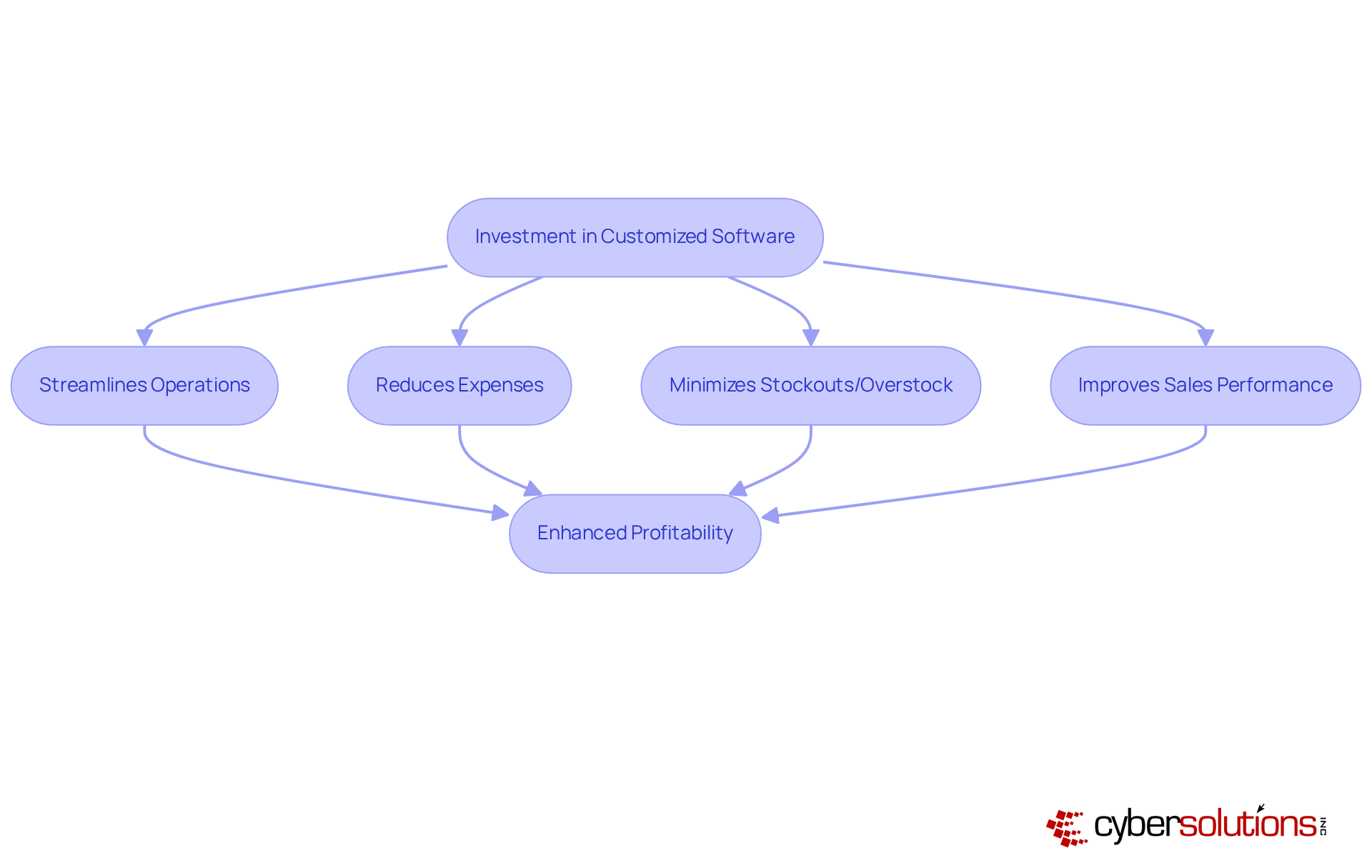
Investing in tailored applications is crucial for enhancing profitability by increasing revenue and reducing expenses. Consider a retail operation that utilizes customized software for inventory management; it can effectively minimize stockouts and overstock situations, leading to improved sales performance and reduced holding costs. Research indicates that companies utilizing customized software have reported increases in profitability of up to 30%, significantly impacting their bottom line. As Peter Drucker famously stated, "What gets measured gets managed," underscoring the importance of aligning program functionalities with specific organizational goals.
Furthermore, case studies on value stream reduction illustrate how organizations can enhance efficiency and drive profitability. To maximize the advantages of customized software, C-Suite leaders must evaluate their current system capabilities against their organizational goals, ensuring that their investments in technology are strategically aligned.
Customization is essential for companies seeking a competitive edge, as it enhances their responsiveness to market trends and client needs.
Consider logistics companies that leverage customized tracking systems; they can provide clients with real-time updates, which significantly boosts customer satisfaction and loyalty. This not only sets companies apart in saturated markets but also attracts a broader customer base.
Industry leaders assert that the ability to adapt swiftly to changing conditions is crucial for maintaining relevance and competitiveness. Organizations investing in customized solutions frequently report increased efficiency and a stronger market position, illustrating the benefits of tailored software.

The transformative effect of customized software on business growth is not just significant; it is essential. By strategically implementing technology solutions, companies can enhance their operations, improve customer experiences, and foster innovation.
Consider healthcare providers that adopt customized software; they can streamline patient care processes, resulting in improved health outcomes and heightened patient satisfaction. This alignment is crucial for long-term success.
Insights from industry leaders reveal that organizations with well-aligned technology strategies are more likely to report higher productivity and innovation rates. Furthermore, case studies indicate that firms adopting customized software have witnessed significant enhancements in productivity and reductions in operational expenses.
As C-suite leaders recognize the importance of technology integration, the role of customized software becomes increasingly vital in driving and sustaining a competitive advantage.
To effectively implement customized software solutions, C-suite leaders should prioritize:

Customized business software is essential for organizations seeking growth and efficiency. By delivering tailored solutions that meet specific business needs, companies can significantly enhance operational performance, streamline processes, and fortify their competitive advantage. The importance of adopting customized software cannot be overstated; it equips businesses to effectively navigate challenges and seize opportunities in an ever-evolving market landscape.
Key insights throughout this discussion reveal that customized software not only automates routine tasks and integrates seamlessly with existing systems but also offers scalability and ongoing support. From bolstering cybersecurity measures to enhancing productivity and profitability, the benefits are substantial. Organizations investing in tailored solutions frequently experience notable cost savings, increased customer satisfaction, and improved operational efficiency, further underscoring the transformative power of customized software.
In conclusion, embracing customized business software is not merely a strategic choice; it is a necessity for organizations aiming to thrive. By prioritizing tailored solutions, companies can foster innovation, enhance agility, and ultimately drive sustainable growth. The call to action is clear:
What is the primary focus of Cyber Solutions Inc. in relation to cybersecurity?
Cyber Solutions Inc. focuses on crafting customized business software tailored to meet the unique cybersecurity needs of various industries, particularly healthcare, by addressing challenges like regulatory compliance and operational efficiency.
How does Cyber Solutions Inc. enhance security for its clients?
The company enhances security by integrating application allowlisting, which prevents malware and unauthorized software from executing, ensuring compliance with regulations such as HIPAA, PCI-DSS, and GDPR.
What additional services does Cyber Solutions Inc. provide?
Cyber Solutions Inc. offers Compliance as a Service (CaaS) and Incident Response services to help clients navigate regulatory complexities and mitigate the impact of cyber threats.
How does customized business software improve productivity?
Customized business software automates routine tasks and streamlines workflows, allowing employees to focus on higher-value activities, which enhances overall productivity.
Can you provide an example of productivity gains from customized software in healthcare?
A tailored patient management system can automate appointment scheduling and billing, leading to improved patient care and operational efficiency. One healthcare entity saved over $1.14 million annually through automated medical coding.
What are the potential productivity boosts from embracing automation technologies?
Companies that fully embrace automation technologies can boost productivity by as much as 20%, as noted by McKinsey.
What challenges might organizations face when implementing customized software?
Organizations may encounter challenges such as high initial costs and compliance issues. Comprehensive training programs can help mitigate resistance to automation and facilitate a smoother transition.
Why is seamless integration of customized software with existing systems important?
Seamless integration minimizes disruptions during implementation, allowing businesses to maximize their current technology investments and improve operational efficiency.
Can you give an example of how customized software can integrate with existing systems?
A manufacturing company can enhance operational visibility and data flow by integrating a custom inventory management system with its existing ERP platform.
What do successful case studies reveal about customized software integration?
Insights from successful case studies, such as those from Cigna and ActiveDocs, demonstrate that effective integration strategies streamline processes and drive growth and efficiency across organizations.