
In an age where cyber threats loom larger than ever, the importance of robust network security cannot be overstated. Managed firewalls serve as a critical line of defense, protecting sensitive data and ensuring compliance with industry standards.
However, with numerous options available, how can organizations select the right managed firewall service provider that meets their security needs while enhancing operational efficiency? Understanding the key benefits and considerations in choosing a managed firewall service empowers businesses to fortify their defenses against the ever-evolving landscape of cyber threats.
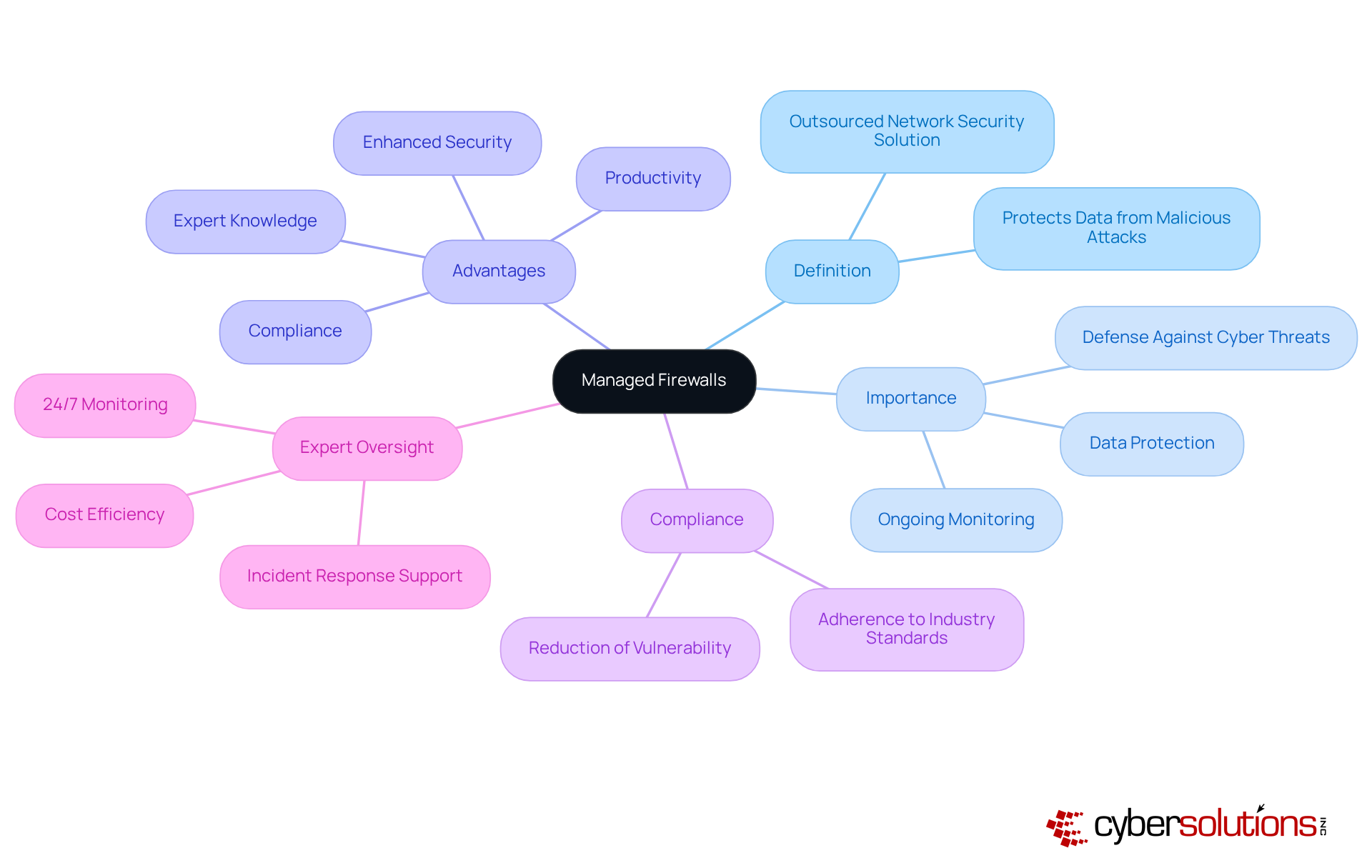
Managed firewalls are essential protective tools that oversee and regulate incoming and outgoing network traffic in accordance with established security guidelines. Acting as a protective barrier between trusted internal networks and untrusted external networks, such as the internet, they play a pivotal role in cybersecurity. The importance of controlled security systems is underscored by their ability to provide ongoing defense against unauthorized entry, data breaches, and various cyber threats. As cyberattacks become increasingly sophisticated, organizations must prioritize security measures to mitigate risks.
The advantages of managed firewall services extend beyond enhanced security; they also ensure compliance, making them indispensable for companies that handle sensitive data. For instance, organizations in sectors like healthcare and finance, which are frequently targeted by cybercriminals, can significantly reduce their vulnerability by employing managed firewall services. These services not only aid in preventing data loss but also offer real-time monitoring, ensuring that potential threats are identified and addressed swiftly.
Outsourcing security system management to a managed firewall provider enables organizations to leverage expert knowledge, allowing internal teams to concentrate on core operations. This strategic approach not only strengthens security but also improves productivity, as employees can focus on their responsibilities without the distraction of security concerns. Furthermore, statistics reveal that up to 99% of network security breaches stem from misconfigurations, highlighting the importance of expert oversight in maintaining a secure environment. By investing in managed security services, businesses can adeptly navigate the complexities of modern cybersecurity, ensuring robust protection against evolving threats.
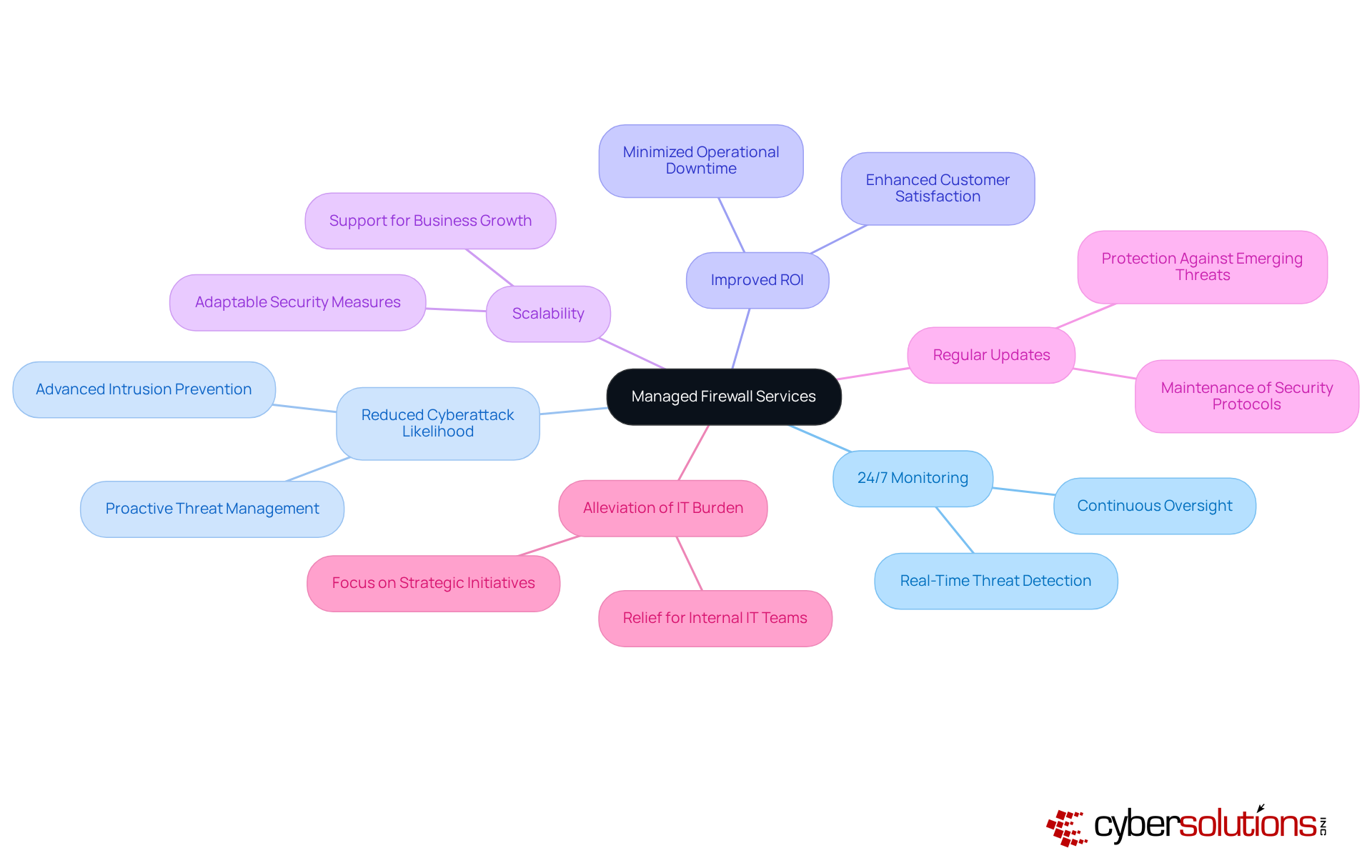
The advantages offered by a managed firewall service can significantly enhance a company's security posture. A pivotal aspect is the provision of real-time monitoring, ensuring that threats are detected and addressed in real-time. This proactive approach not only reduces the likelihood of successful cyberattacks but also minimizes operational downtime, ultimately contributing to improved ROI for small to medium businesses. For instance, companies utilizing managed protection services report increased security effectiveness, underscoring the impact of these services.
Moreover, managed firewall systems are scalable, enabling organizations to adjust their protective measures in response to evolving requirements. This adaptability is crucial for businesses experiencing growth or shifts in their operational landscape. Regular updates and maintenance are fundamental components of these services, ensuring that protective measures remain robust against emerging threats.
By utilizing a managed service provider for the management of network security, companies can alleviate the burden on internal IT teams, allowing them to concentrate on strategic initiatives rather than routine security tasks. This transition enhances operational efficiency and supports compliance efforts, safeguarding the organization against potential legal and financial repercussions. Ultimately, investing in managed firewall services is a strategic decision that can lead to a more secure and resilient operational environment.
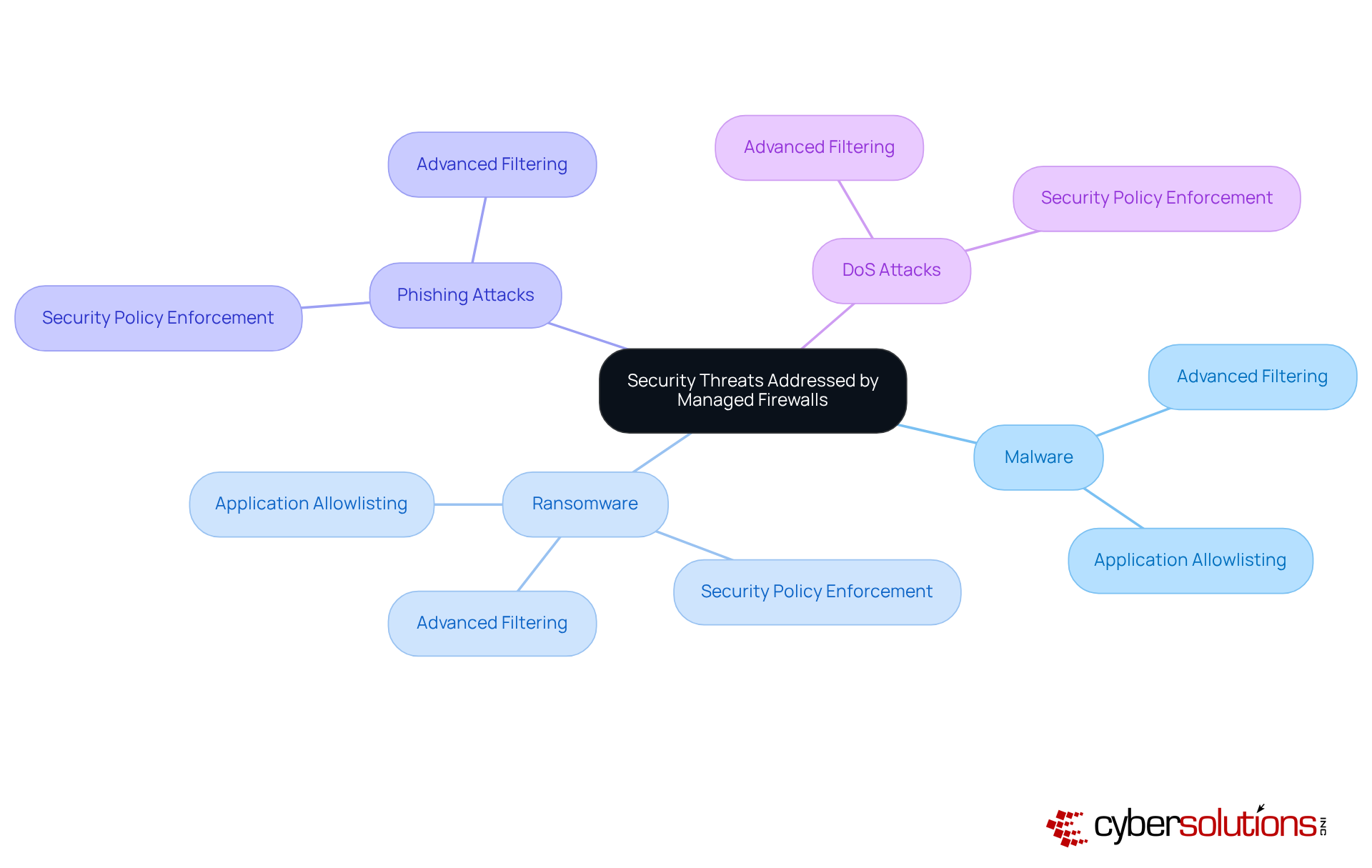
Managed firewall systems, particularly those offered by a service provider, are indispensable in safeguarding against a myriad of threats that can compromise an organization's network integrity. These threats include:
By employing advanced filtering methods, managed firewalls effectively prevent harmful traffic from infiltrating the network, significantly mitigating the risk of infection. Furthermore, these systems excel at detecting and responding to threats, which is vital for protecting sensitive data from breaches.
A fundamental attribute of managed firewalls is their ability to enforce security policies, ensuring that only authorized users and devices can access specific resources. This capability is particularly crucial for organizations operating within stringent regulatory frameworks, as it aids in preserving data confidentiality and integrity. Recent trends reveal that phishing attacks have become increasingly sophisticated and personalized, often utilizing AI to mislead even the most experienced professionals. In this evolving landscape, managed firewalls act as a primary line of defense, delivering robust protection against these dynamic threats.
Moreover, allowlisting is pivotal in bolstering cybersecurity. By proactively preventing unauthorized or malicious applications from executing, allowlisting diminishes the attack surface and reduces vulnerabilities. Key features of managed firewalls encompass:
This ensures the immediate identification and blocking of threats. This strategy not only aids in thwarting malware and ransomware but also supports compliance with regulations such as HIPAA, PCI-DSS, and GDPR. Organizations that have embraced both controlled security solutions and managed firewalls, along with a proactive security strategy, report a marked decrease in successful attacks, underscoring their combined efficacy in enhancing overall cybersecurity posture. In 2023, over 630 data breaches impacted organizations, underscoring the urgent need for robust defenses. By addressing these critical risks, controlled barriers and managed firewalls collaboratively fortify a more resilient protective framework, enabling entities to navigate the complexities of contemporary cyber threats with confidence.
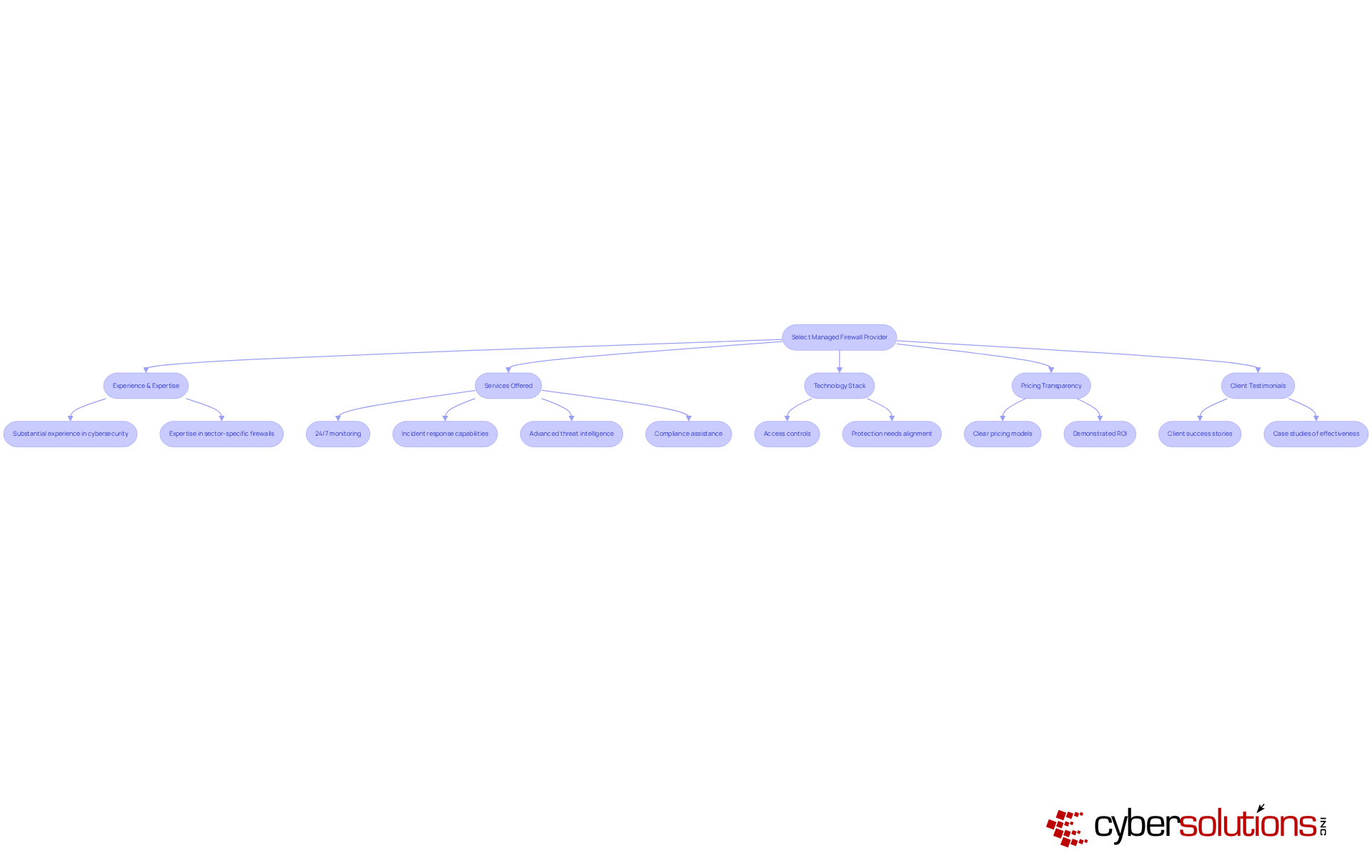
Selecting the right is essential for strengthening a company's security posture. In an era where cybersecurity threats are increasingly sophisticated, organizations must prioritize a that has substantial experience and expertise in cybersecurity, especially those adept at managing firewalls for entities in similar sectors. The breadth of services offered is critical; organizations should favor providers like Cyber Solutions, which deliver:
Furthermore, assessing the provider's technology stack is vital to ensure it meets specific protection needs, including access controls that mitigate unauthorized access. Transparency in pricing is equally important; businesses should seek suppliers that present and demonstrate a tangible return on investment through effective risk management strategies. For instance, organizations leveraging supervised barrier services can expect to save an average of $3.81 million per breach due to enhanced protective measures.
Client testimonials and case studies are invaluable resources, offering insights into the provider's reliability and efficacy. For example, entities that have integrated Cyber Solutions' and response capabilities have reported significant improvements in their security frameworks, resulting in measurable reductions in incidents. By thoroughly evaluating these elements, organizations can that not only strengthens their security but also aligns with their overarching business objectives.
Choosing a managed firewall service provider is a critical decision that can significantly enhance an organization’s cybersecurity posture. In today's increasingly complex digital landscape, these services not only provide robust protection against a myriad of cyber threats but also streamline security management, allowing businesses to focus on their core functions. By outsourcing firewall management, organizations can ensure continuous monitoring and expert oversight, which is essential for maintaining a strong defense against evolving threats.
The advantages of managed firewall services are numerous and compelling. They include:
Furthermore, the proactive approach to managing security threats—such as malware, ransomware, and phishing attacks—demonstrates the necessity of these services in safeguarding sensitive data and maintaining operational integrity. Selecting a provider with experience, advanced technology, and transparent pricing is crucial for maximizing the benefits of managed firewall services.
Ultimately, the choice to invest in a managed firewall service provider transcends mere security enhancement; it is a strategic move that can lead to improved operational efficiency and peace of mind. Organizations must recognize the evolving nature of cybersecurity threats and the importance of having a reliable partner to navigate these challenges. By prioritizing robust managed firewall solutions, businesses can fortify their defenses, protect their data, and ensure compliance with industry standards, paving the way for a more secure future.
What is a managed firewall?
A managed firewall is a protective tool that oversees and regulates incoming and outgoing network traffic based on established security guidelines, acting as a barrier between trusted internal networks and untrusted external networks.
Why are managed firewalls important?
Managed firewalls are important because they provide ongoing defense against unauthorized entry, data breaches, and various cyber threats, thereby safeguarding sensitive data and ensuring compliance with industry standards.
How do managed firewalls benefit organizations in sensitive sectors?
Organizations in sensitive sectors, such as healthcare and finance, can significantly reduce their vulnerability to cyberattacks by employing managed security services, which help prevent data loss and offer 24/7 monitoring for swift threat identification and response.
What are the advantages of outsourcing firewall management?
Outsourcing firewall management to a managed service provider allows organizations to leverage expert knowledge and advanced tools, enabling internal teams to focus on core operations while strengthening security.
How do managed firewalls enhance productivity?
By outsourcing security management, employees can concentrate on their responsibilities without the distraction of cybersecurity issues, leading to enhanced productivity within the organization.
What is the significance of expert oversight in network security?
Expert oversight is significant because statistics indicate that up to 99% of network security breaches stem from misconfigurations, emphasizing the need for professional management to maintain a secure environment.
How do managed firewalls help in navigating modern cybersecurity challenges?
By investing in managed security services, businesses can effectively navigate the complexities of modern cybersecurity, ensuring robust protection against evolving threats.