
The escalating threat of cyber attacks has positioned the protection of Controlled Unclassified Information (CUI) as a paramount concern for organizations, especially those collaborating with the U.S. Department of Defense. The Cybersecurity Maturity Model Certification (CMMC) and NIST 800-171 frameworks stand out as critical instruments for bolstering cybersecurity practices and achieving compliance.
As organizations gear up for the impending 2026 certification deadline, a pivotal question emerges: how do these two frameworks stack up against each other in terms of requirements and compliance strategies? Grasping their similarities and distinctive features is essential for organizations striving to adeptly navigate the intricate landscape of cybersecurity.
The CMMC serves as a crucial framework established by the U.S. Department of Defense (DoD) to enhance the cybersecurity posture of organizations that manage Controlled Unclassified Information (CUI). This structured certification model rigorously evaluates an organization's cybersecurity maturity across various levels, each necessitating specific practices and processes that must be implemented and verified through third-party assessments.
In contrast, NIST 800-171 provides a comprehensive set of guidelines from the National Institute of Standards and Technology, detailing the essential requirements for protecting CUI within non-federal systems. This framework comprises 110 security controls organized into 14 families, addressing vital areas such as access control, incident response, and security assessment. Unlike CMMC, which mandates third-party evaluations, the NIST 800-171 allows entities to perform self-assessments, offering greater flexibility for compliance.
As we approach January 2026, adherence to NIST 800-171 remains critical, especially as organizations gear up for the impending certification requirements. A recent survey revealed that a mere 1% of Defense Industrial Base contractors are fully prepared for compliance, underscoring the pressing need for businesses to align their practices with both frameworks. Case studies demonstrate that organizations have significantly enhanced their protective measures, illustrating the effectiveness of these guidelines in mitigating risks associated with CUI.

In today's digital landscape, the protection of Controlled Unclassified Information (CUI) is paramount, especially against the backdrop of escalating cyber threats. The frameworks are designed to safeguard sensitive data from unauthorized access, underscoring the critical need for robust protective measures. Organizations must recognize that the establishment of a compliance program is not just a compliance requirement; it is a foundational step in implementing effective security protocols.
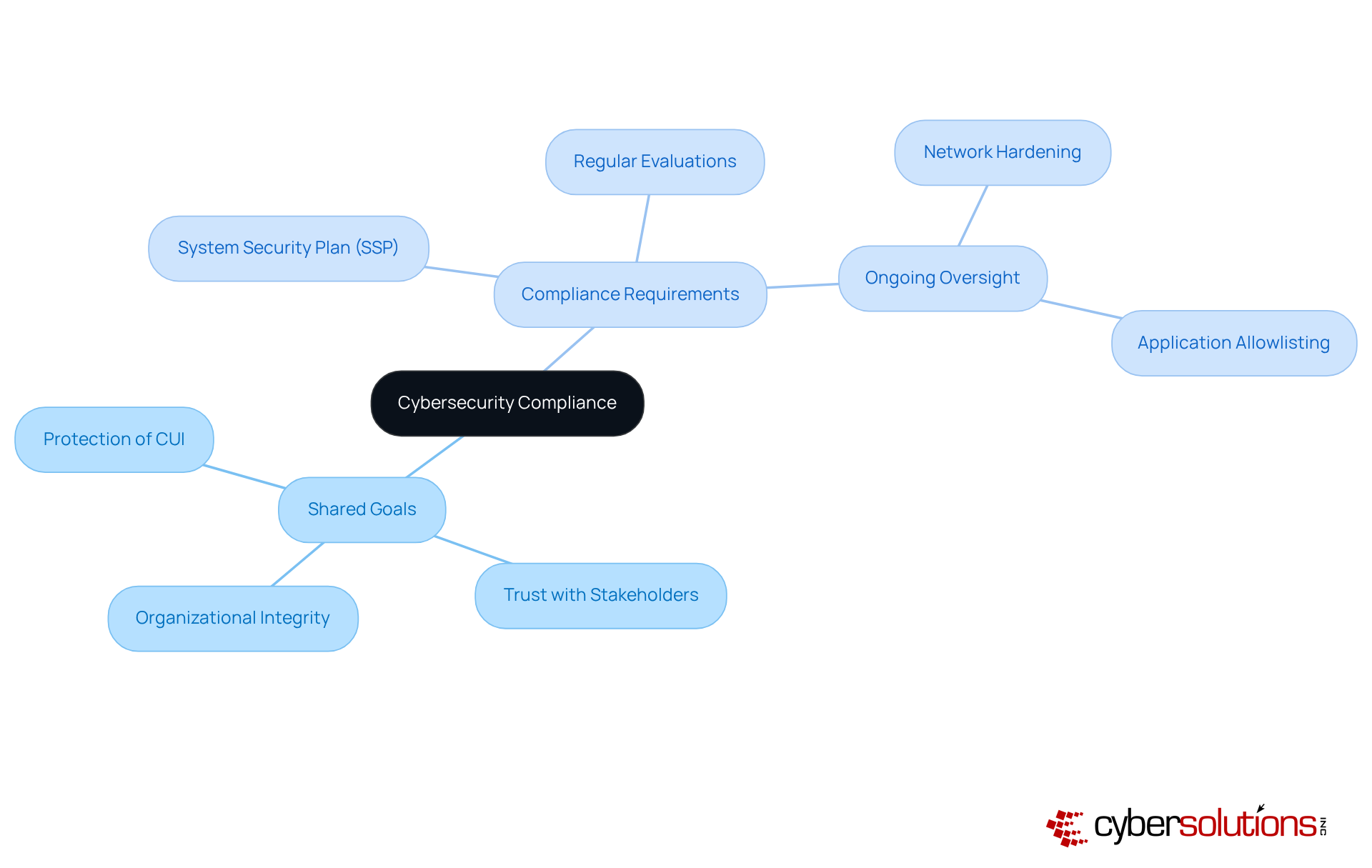
Regular evaluations and ongoing oversight are essential components of both frameworks, ensuring that protective measures remain effective over time. For organizations striving for compliance, this commitment reflects a dedication to maintaining a secure environment for handling sensitive information. In an era where cybersecurity is increasingly vital, this commitment not only fulfills regulatory obligations but also fosters trust with stakeholders and protects organizational integrity.
To achieve and ensure compliance, organizations must take proactive steps. Consider the following:
Moreover, prompt training for personnel on identifying suspicious emails and upholding proper cybersecurity practices significantly bolsters a company's defenses. By adopting these strategies, organizations can effectively navigate the complexities of cybersecurity and safeguard their critical information.
Understanding the differences between the cybersecurity framework and NIST 800-171 is crucial for organizations aiming to secure DoD contracts. The certification program mandates third-party evaluations to ensure compliance, making it a requirement for those pursuing these contracts. In contrast, NIST 800-171 allows for self-evaluation, providing entities with greater flexibility in demonstrating their compliance.
Moreover, the CMMC categorizes entities into various tiers based on their cybersecurity practices, while the NIST 800-171 framework focuses solely on compliance. This distinction means that organizations must not only meet the criteria of CMMC but also demonstrate a commitment in their cybersecurity practices to achieve certification. Additionally, the CMMC Certification introduces practices not covered by NIST 800-171, such as planning and assessment, further differentiating the two frameworks.
In today's landscape, where cyber threats are prevalent, understanding these frameworks is essential for healthcare organizations. How prepared is your organization to navigate these challenges? Cyber Solutions can help you enhance your cybersecurity posture and ensure compliance.

In today's digital landscape, the importance of cybersecurity in healthcare cannot be overstated. To achieve compliance, organizations must conduct a thorough assessment to identify deficiencies in their current practices compared to the required standards. This analysis should encompass a detailed examination of existing systems, policies, and procedures, ensuring alignment with the regulations.
Following this, organizations should develop a comprehensive strategy that outlines their strategy for implementing compliance. The SSP must clearly specify how each requirement will be addressed, including timelines and designated responsibilities. Moreover, regular training for employees are crucial to ensure that all staff members understand their roles in maintaining compliance.
Establishing an evaluation process is vital for consistently evaluating the effectiveness of compliance measures and making necessary adjustments. This proactive approach not only aids in sustaining compliance but also fortifies the overall security posture of the organization. Engaging with third-party assessors can significantly enhance readiness for audits, ensuring that organizations are well-prepared for the assessment process.

The Cybersecurity Maturity Model Certification (CMMC) and NIST 800-171 are not just frameworks; they are essential pillars in the fight against cyber threats for organizations handling Controlled Unclassified Information (CUI). With the increasing sophistication of cyber attacks, understanding these frameworks is vital for protecting sensitive data from unauthorized access. While both aim to secure information, CMMC mandates third-party evaluations and a structured certification process, while NIST 800-171 offers the flexibility of self-assessments. This distinction is crucial for organizations striving to meet compliance requirements.
Key insights from this discussion highlight the necessity of establishing a robust System Security Plan (SSP) and conducting regular evaluations to maintain compliance. Organizations are urged to adopt proactive strategies, such as:
These measures are essential to strengthen defenses against the ever-evolving landscape of cyber threats. For those aiming to secure Department of Defense contracts, grasping the differences between these frameworks is not just beneficial; it’s imperative for enhancing their cybersecurity posture.
As the cybersecurity landscape continues to shift, the urgency for organizations to align with both CMMC and NIST 800-171 frameworks cannot be overstated. Taking decisive action now not only ensures compliance but also builds trust among stakeholders and fortifies the overall security of sensitive information. Organizations must prioritize these frameworks to protect their operations and effectively navigate the complexities of cybersecurity. The time to act is now-secure your future by embracing these critical standards.
What is the Cybersecurity Maturity Model Certification (CMMC)?
The CMMC is a certification model established by the U.S. Department of Defense to enhance the cybersecurity posture of organizations managing Controlled Unclassified Information (CUI). It evaluates an organization's cybersecurity maturity across various levels, requiring specific practices and processes verified through third-party assessments.
What is NIST 800-171?
NIST 800-171 is a set of guidelines from the National Institute of Standards and Technology that outlines essential requirements for protecting Controlled Unclassified Information (CUI) within non-federal systems. It includes 110 security controls organized into 14 families, addressing areas such as access control, incident response, and risk assessment.
How do CMMC and NIST 800-171 differ in terms of assessment?
CMMC requires third-party evaluations to verify compliance, while NIST 800-171 allows entities to perform self-assessments, providing greater flexibility for compliance.
Why is adherence to NIST 800-171 critical as we approach January 2026?
Adherence to NIST 800-171 is essential because organizations need to prepare for impending certification requirements. A survey indicated that only 1% of Defense Industrial Base contractors are fully prepared for compliance audits related to CMMC NIST 800-171, highlighting the urgency for businesses to align their practices with both frameworks.
What evidence supports the effectiveness of NIST 800-171 controls?
Case studies have shown that organizations implementing NIST 800-171 controls have significantly enhanced their protective measures, demonstrating the effectiveness of these guidelines in mitigating risks associated with Controlled Unclassified Information (CUI).