
In an era where cyber threats loom large, the healthcare sector faces unprecedented challenges in safeguarding sensitive data. Organizations must navigate the complex terrain of information security services with precision and foresight. The stakes are particularly high in sectors like healthcare and finance, where protecting sensitive data is not just a regulatory requirement but a critical component of operational integrity.
To navigate these challenges, organizations must:
Choosing the right partner can mean the difference between security and vulnerability.
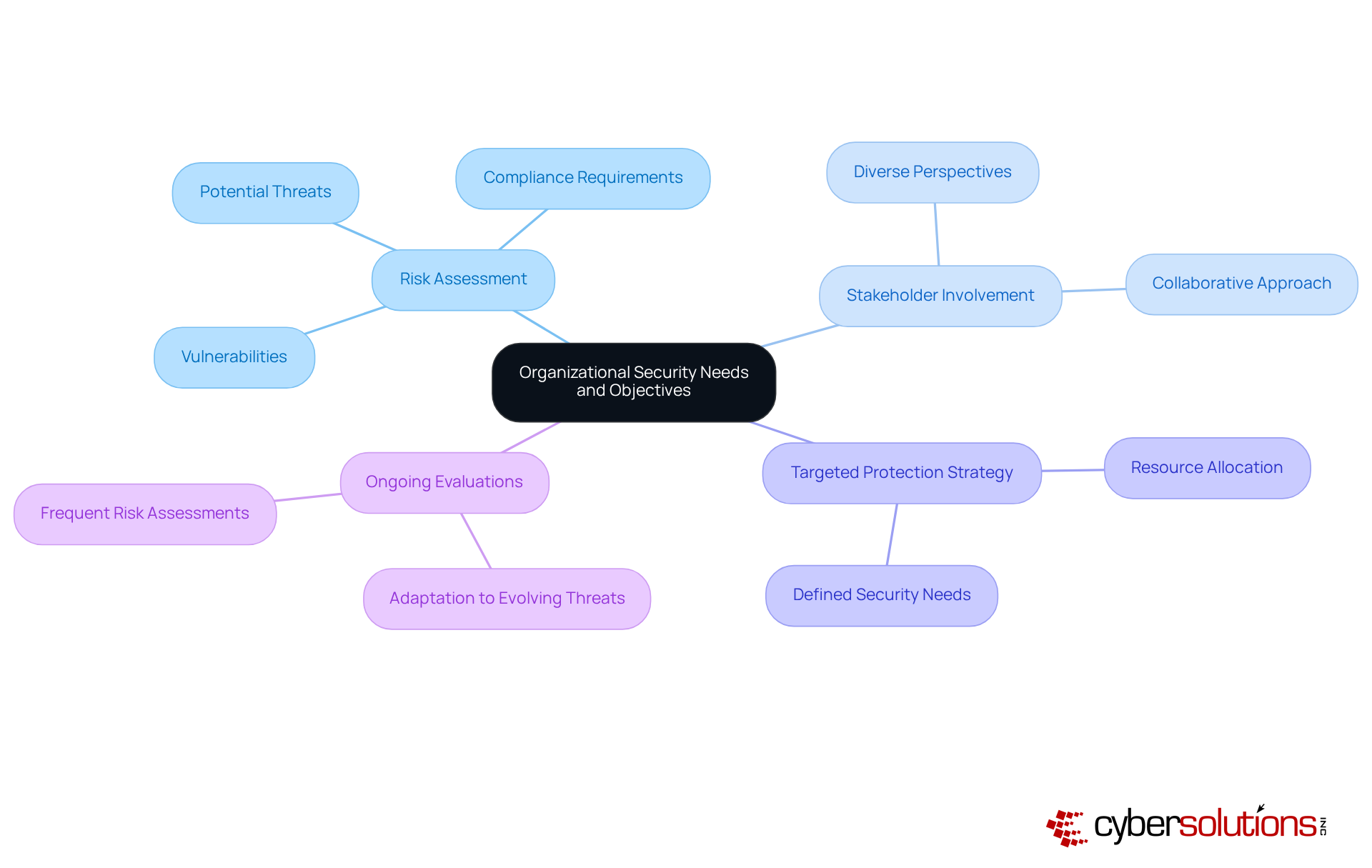
In an era where cyber threats loom large, the healthcare sector faces unique challenges that demand immediate attention and action. To effectively choose information security services companies, organizations must first articulate their specific security needs and objectives. It all starts with a thorough risk assessment that pinpoints vulnerabilities, potential threats, and compliance requirements specific to the industry. For instance, healthcare organizations prioritize the protection of patient data in accordance with HIPAA regulations, while financial institutions focus on safeguarding sensitive financial information. By clearly defining these needs, businesses can develop a targeted protection strategy that aligns with their operational goals and regulatory obligations.
Involving key stakeholders ensures diverse perspectives are considered, resulting in a more robust and comprehensive protection strategy. Frequent risk evaluations are crucial, as they help organizations adapt to evolving threats and maintain compliance with stringent regulations. This collaborative approach not only enhances security but also fosters a culture of awareness across the organization.
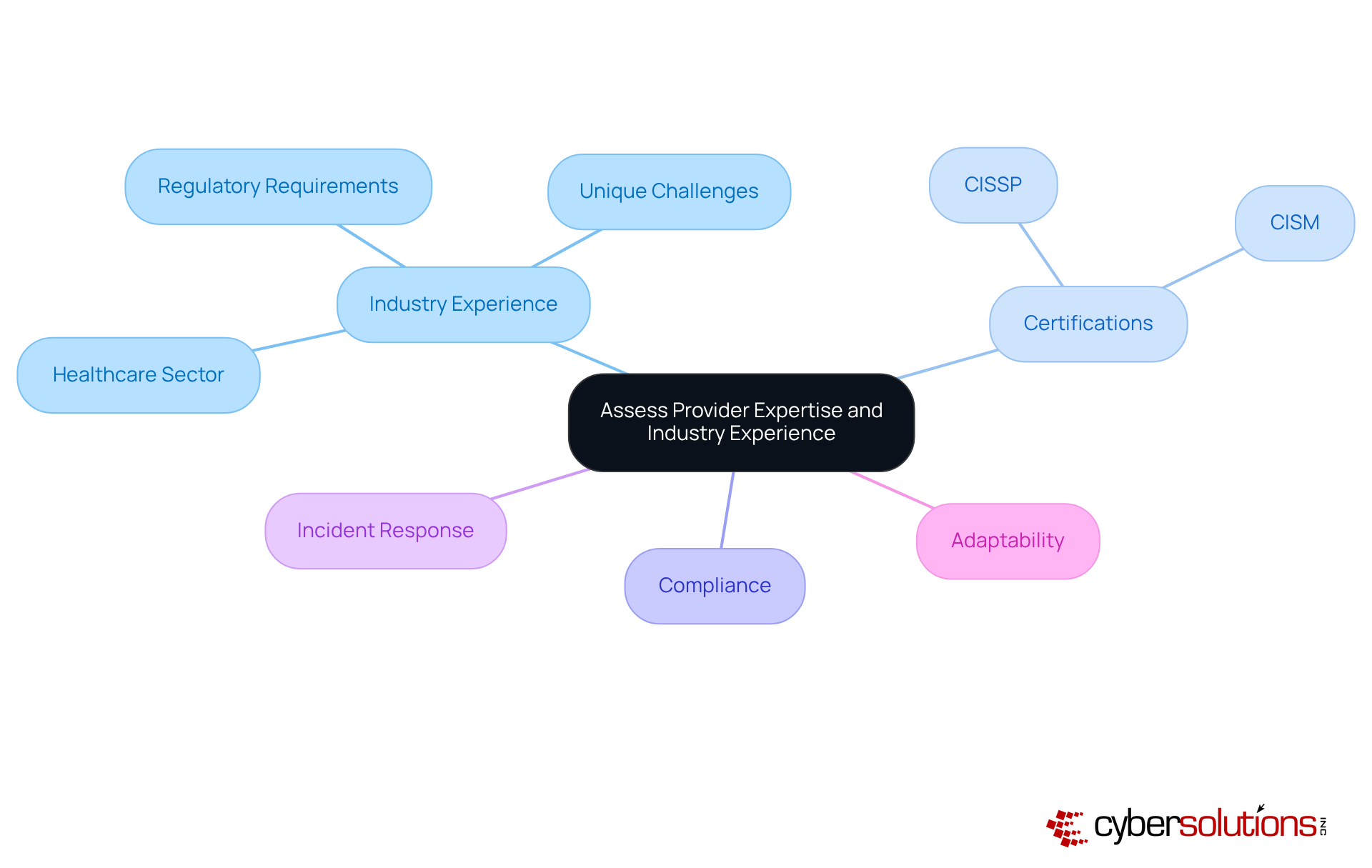
In an era where healthcare organizations face unprecedented cybersecurity threats, the stakes have never been higher. When assessing potential information security services companies, it’s crucial to evaluate their expertise and experience within your specific industry. Look for suppliers who have worked with entities like yours; they’ll be more familiar with the unique challenges and regulatory requirements you face. For instance, a professional with extensive experience in the healthcare sector will grasp the intricacies of HIPAA compliance and patient data protection.
Consider a ransomware attack on a healthcare organization: it highlights the urgent need for rapid incident response and effective cybersecurity training. The organization’s network was compromised, affecting approximately 4,500 endpoints and putting patient data and operational continuity at risk. This situation underscores the importance of having a partner, specifically information security services companies, capable of swift remediation efforts, such as the immediate mobilization of an incident response team that can assess threats and begin remediation promptly.
Additionally, verify their certifications, like CISSP or CISM, which indicate a commitment to industry best practices. It’s also essential to evaluate the MSSP's compliance service offerings to ensure they meet current and future regulatory compliance needs. Engaging with references or case studies can provide valuable insights into the provider's capabilities and reliability, especially in managing incidents like ransomware attacks.
Furthermore, confirm that the MSSP stays updated on new threats, regulations, and innovations in cybersecurity tooling and technologies. This adaptability is vital for effective risk management. Taking this thorough approach not only helps you manage risks but also ensures you’re working with information security services companies that truly understand the cybersecurity landscape in your industry. Choosing the right MSSP can be the difference between a secure future and a catastrophic breach that jeopardizes everything you’ve worked for.
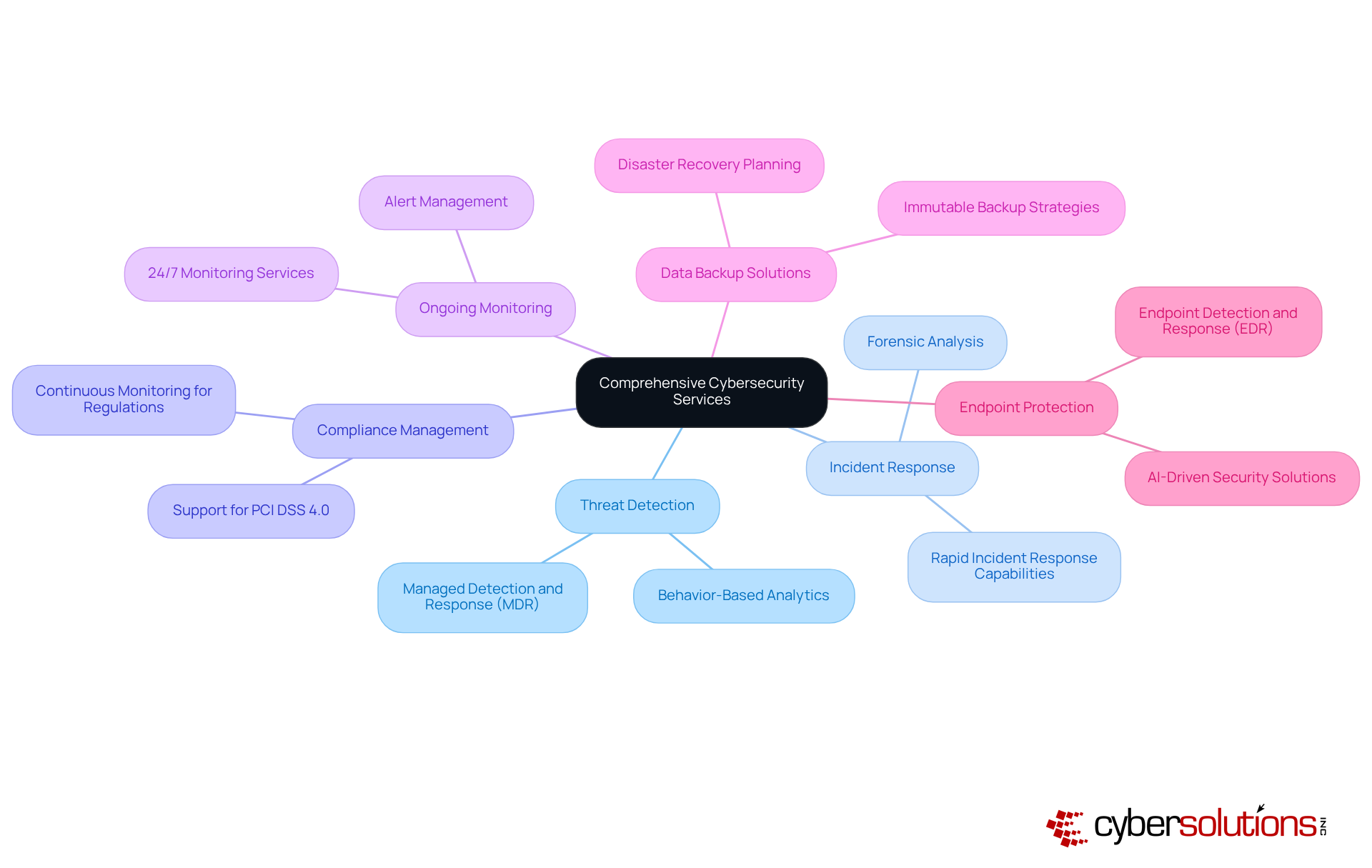
In an era where cyber threats loom larger than ever, healthcare organizations must prioritize robust cybersecurity measures to safeguard sensitive patient data. A comprehensive assessment of potential information security services companies is crucial for organizations seeking to improve their cybersecurity stance. Providers should offer a complete suite of services, including:
This comprehensive strategy guarantees that every facet of cybersecurity is fortified, from proactive prevention to effective remediation. For instance, managed detection and response (MDR) services are vital as they proactively identify and mitigate threats before they escalate into significant incidents. Cybersecurity experts assert that effective threat detection and incident response are essential to sustaining a strong protection framework.
Furthermore, organizations ought to evaluate if the supplier can tailor their services to fulfill particular requirements, as adaptability is crucial in effectively tackling changing safety challenges. Companies such as FIMBank have effectively improved their defensive stance by adopting MDR services, gaining from round-the-clock monitoring and swift incident response capabilities. These cases underscore the critical importance of choosing a vendor that not only meets your operational needs but also adeptly navigates the complexities of the cybersecurity landscape. Choosing the right cybersecurity partner from information security services companies could mean the difference between a secure future and a costly breach that jeopardizes patient trust and organizational integrity.
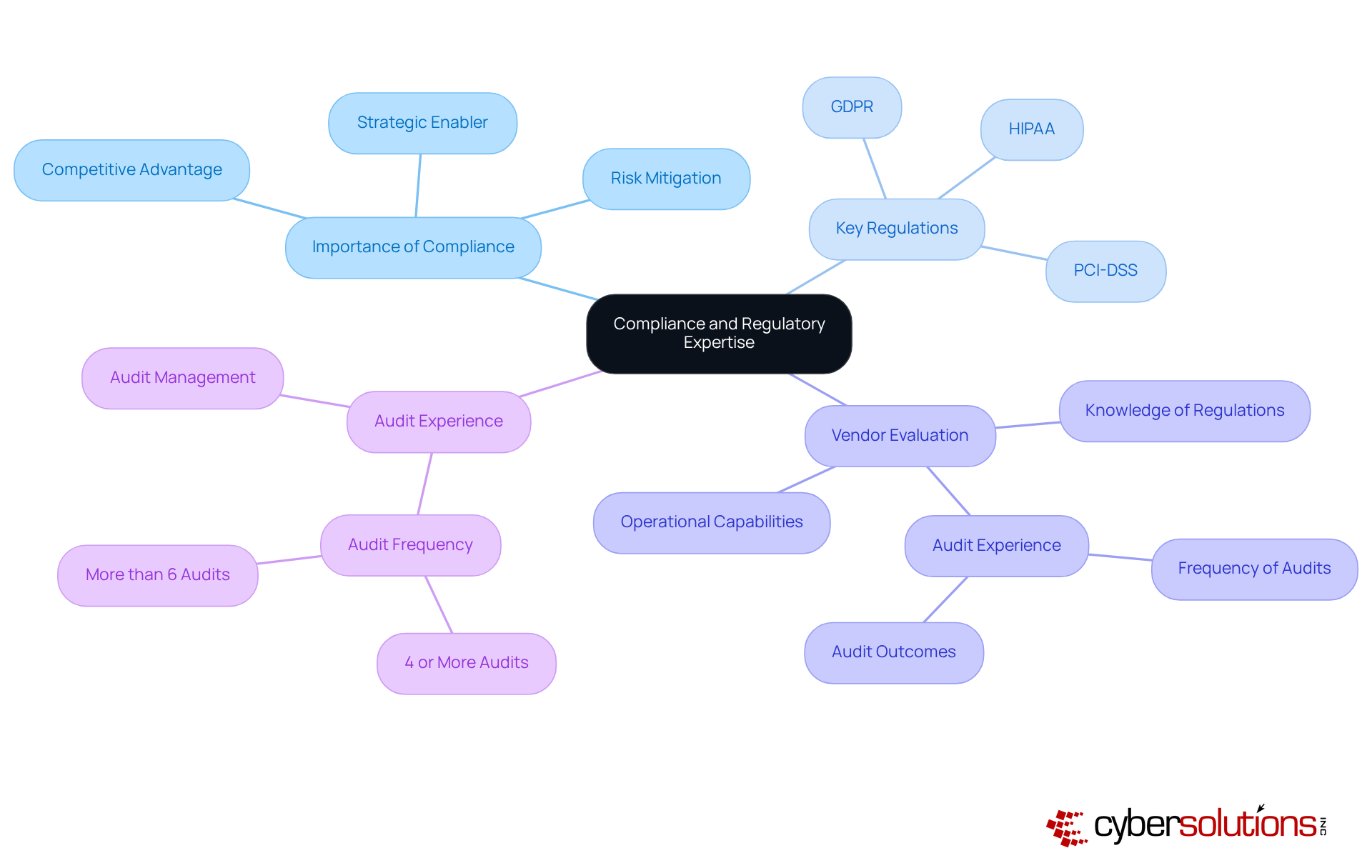
In an era where regulatory compliance is paramount, the choice of information security services companies can make or break an organization’s success. In industries like healthcare, finance, and government, where stringent regulations dictate data protection and privacy practices, selecting vendors with strong adherence to these regulations is essential. Organizations must evaluate potential suppliers for their knowledge of critical regulations such as GDPR, HIPAA, and PCI-DSS, as well as their ability to assist in meeting these requirements efficiently.
Assessing a vendor's experience with audits and evaluations is vital; it reveals their operational capabilities and commitment to compliance. For instance, 58% of organizations performed four or more audits in 2025, underscoring the increasing focus on regulatory management. A provider with a proven track record in managing regulatory challenges becomes an invaluable partner for information security services companies, helping to mitigate potential legal and financial risks while ensuring adherence to standards.
Industry leaders emphasize that upholding regulations is not merely a checkbox exercise; it requires ongoing diligence and strategic alignment with business objectives. As organizations increasingly adopt purpose-built technology for compliance management, those that prioritize transparency and accountability in their compliance efforts will not only meet regulatory demands but also gain a competitive edge in their industry.
In an era where cyber threats are increasingly sophisticated, selecting the right information security services company is more than just a choice - it's a necessity. This decision can significantly impact an organization's ability to safeguard sensitive data and maintain compliance with industry regulations. By clearly defining organizational security needs and objectives, businesses can create a targeted strategy that addresses their unique vulnerabilities and aligns with their operational goals. This foundational step sets the stage for a comprehensive approach to cybersecurity, ensuring that the chosen partner is well-equipped to meet specific challenges.
Key considerations include:
Engaging with vendors who have a proven track record in your specific sector can lead to more effective incident responses and better alignment with regulatory standards. A thorough evaluation process, including a review of certifications and case studies, enhances the likelihood of selecting a partner capable of navigating the complexities of the cybersecurity landscape.
As the digital landscape evolves, the right partner will not only safeguard your data but also empower your organization to thrive amidst uncertainty. Organizations that prioritize these best practices not only protect their assets but also foster a culture of security awareness and compliance. As cyber threats continue to evolve, investing in a knowledgeable and adaptable partner will be crucial in maintaining trust with stakeholders and ensuring long-term success in an increasingly digital world.
Why is it important for healthcare organizations to define their security needs and objectives?
It is crucial for healthcare organizations to define their security needs and objectives to effectively protect patient data, comply with HIPAA regulations, and develop a targeted protection strategy that aligns with their operational goals.
What is the first step in choosing information security services companies?
The first step is to conduct a thorough risk assessment that identifies vulnerabilities, potential threats, and compliance requirements specific to the healthcare industry.
How do stakeholder involvement and diverse perspectives contribute to security strategies?
Involving key stakeholders ensures that diverse perspectives are considered, resulting in a more robust and comprehensive protection strategy.
Why are frequent risk evaluations important for organizations?
Frequent risk evaluations are important because they help organizations adapt to evolving threats and maintain compliance with stringent regulations.
What role does a culture of awareness play in organizational security?
A culture of awareness fosters vigilance among employees, enhancing overall security and ensuring that everyone is engaged in protecting the organization's assets.