In the healthcare sector, the stakes of cybersecurity have never been higher, as cybercriminals relentlessly target sensitive data. Phishing attacks pose a significant threat, and as these criminals become increasingly sophisticated, the financial ramifications can be staggering. Losses average nearly $4.88 million per successful breach, highlighting the urgent need for effective strategies.
Let’s explore some key strategies leaders can implement to effectively combat phishing:
How can organizations actively safeguard their assets while fostering a vigilant culture that empowers their workforce against these deceptive tactics?
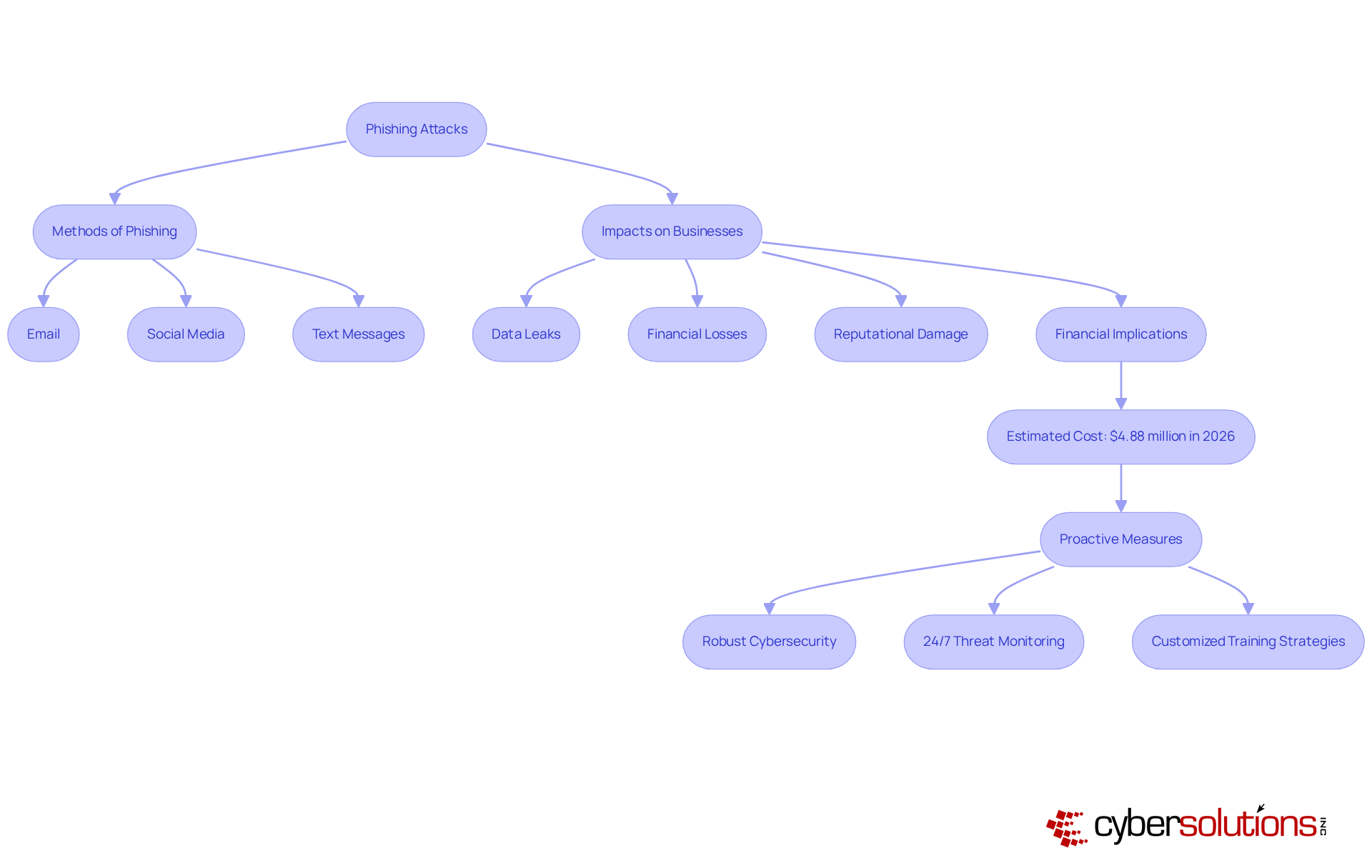
In an era where cyber threats loom large, the healthcare sector faces unprecedented challenges that demand immediate attention. Phishing is a cyberattack method where attackers impersonate trusted entities to trick individuals into disclosing sensitive information, such as passwords or financial details. This deception can occur through various channels, including email, social media, and text messages.
Online scams can severely impact businesses, often resulting in data leaks, significant financial losses, and lasting reputational damage. In 2026, the average expense of a successful online scam is estimated at $4.88 million, encompassing recovery costs, lost income, and regulatory fines. Such financial implications underscore the necessity for leaders to prioritize robust cybersecurity measures and foster a culture of vigilance within their organizations.
With Cyber Solutions' 24/7 threat monitoring, businesses can catch suspicious activities early, effectively safeguarding against ransomware, scams, and other malware issues. Furthermore, the growing complexity of fraudulent schemes, especially those employing AI, emphasizes the necessity for customized training strategies based on industry and employee roles to effectively counter these risks. Without proactive measures, organizations risk not only financial loss but also their very credibility in the eyes of patients and stakeholders.
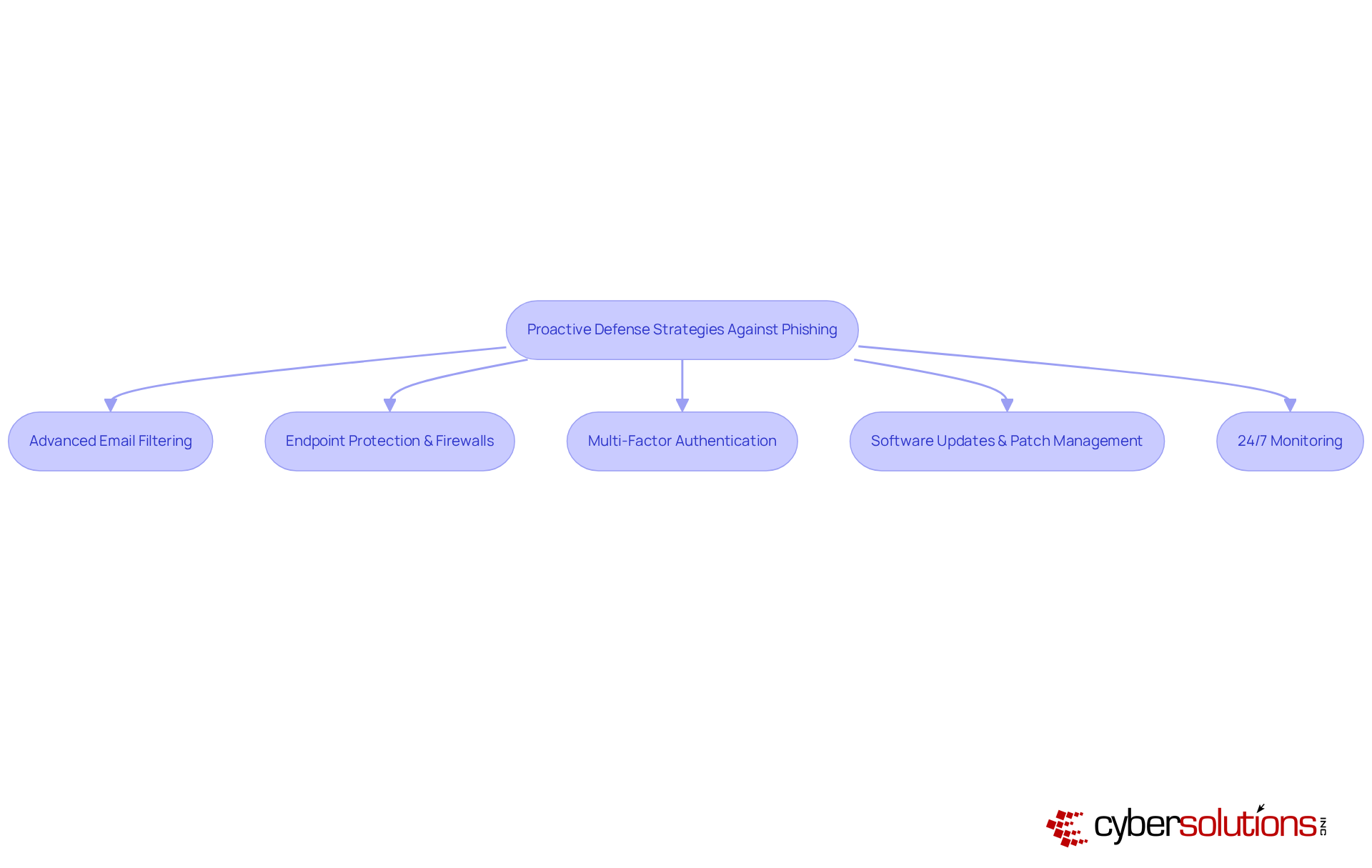
Organizations are increasingly targeted by sophisticated online scams that threaten their security and integrity. To counteract these threats effectively, a multi-layered defense strategy is essential. This includes:
This safeguards your business from ransomware, social engineering, and other malicious software. Carrying out simulated deceptive practices can also aid in evaluating the efficiency of these defenses and pinpointing areas for enhancement. Investing in these proactive measures not only fortifies defenses but also preserves the trust and safety of your organization in an increasingly perilous digital landscape.
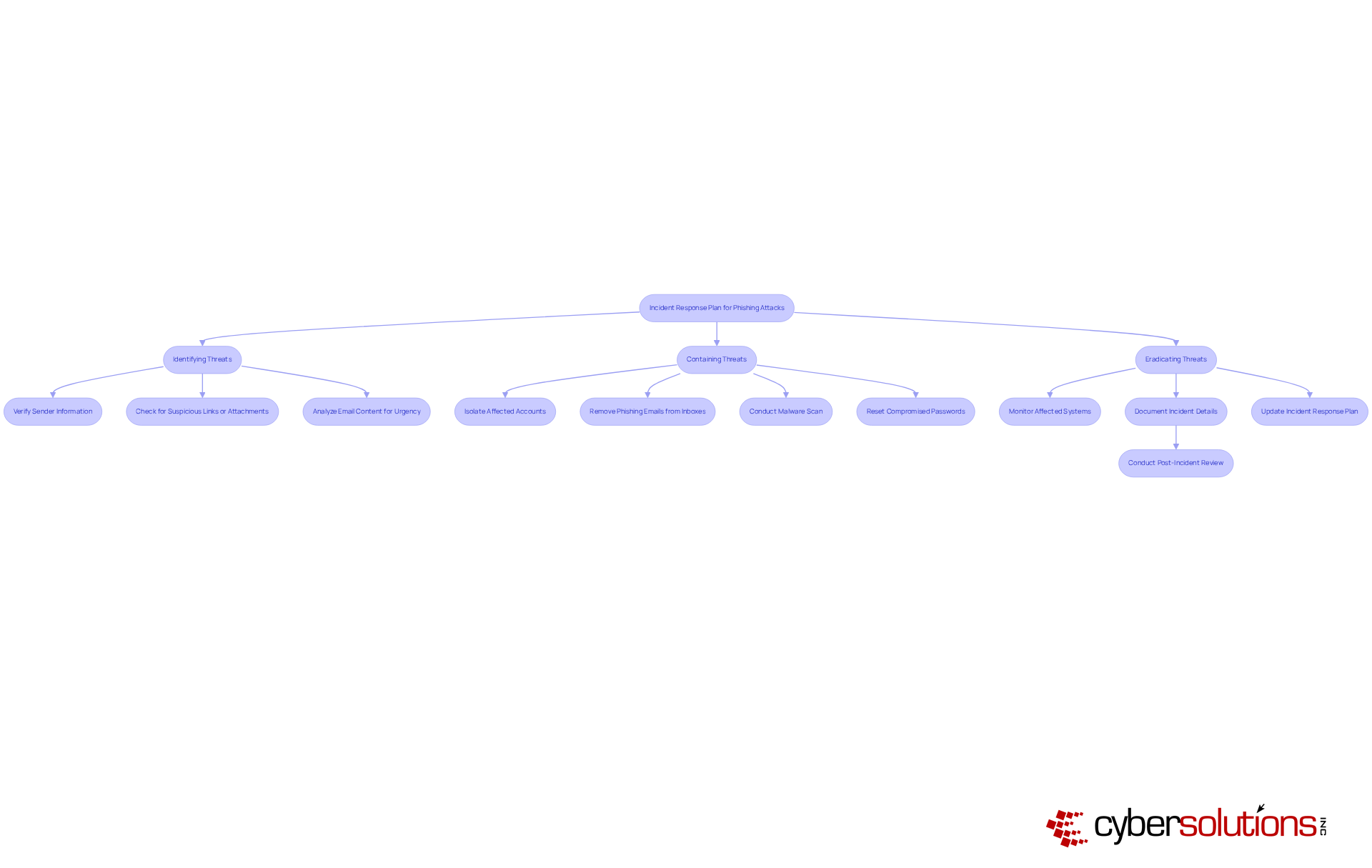
In an era where deceptive email attacks are on the rise, the importance of a robust incident response plan cannot be overstated. An effective incident response plan must encompass well-defined protocols for:
Creating a dedicated incident response team is crucial; this team needs clear roles and responsibilities to ensure a quick and coordinated response when a phishing attempt surfaces. Communication plays a vital role; organizations should implement a plan to promptly inform affected parties and stakeholders about the incident.
Once containment is achieved, a thorough investigation is essential to dissect the attack vector and formulate strategies that prevent future incidents. Regular reviews and updates of the incident response plan, informed by lessons learned from previous incidents, are vital for continuous improvement.
Ultimately, a proactive approach to incident response not only mitigates risks but also fortifies an organization’s resilience against future cyber threats.
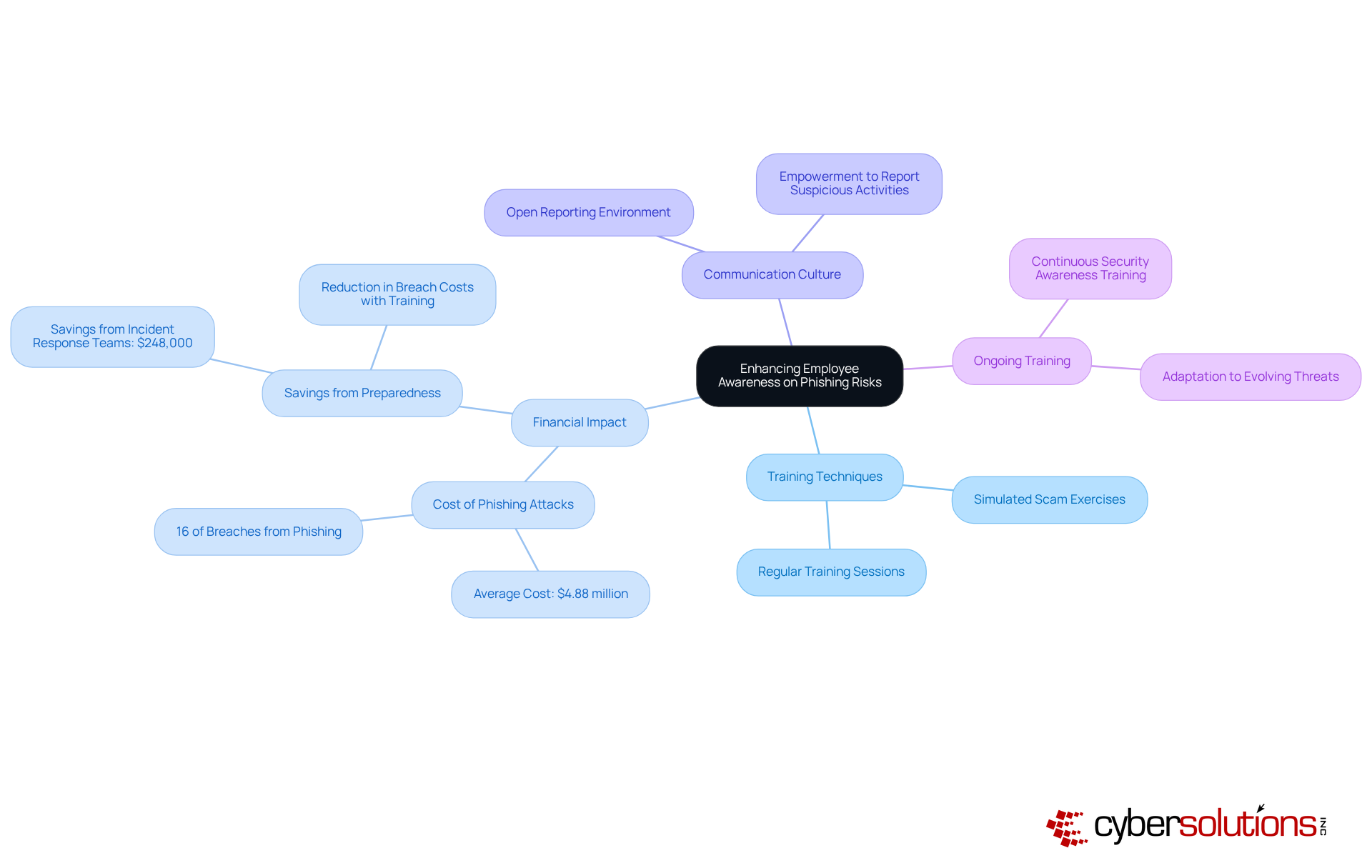
In an era where cyber threats are increasingly sophisticated, the need for robust employee training in fraud prevention has never been more critical. Companies must prioritize thorough staff training and awareness initiatives. Regular training sessions must focus on the latest online deception tactics. This includes sophisticated schemes such as AI-driven impersonation and Business Email Compromise (BEC) tactics. Engaging training techniques, like simulated scam exercises, have proven effective in enhancing learning. Companies report substantial advancements in employee awareness of threats. For instance, ongoing security awareness training can decrease vulnerability to deceptive emails by up to 86%.
Furthermore, fostering a culture of open communication is essential. Employees should feel empowered to report suspicious activities without fear of repercussions. With cyber threats evolving rapidly, how can organizations keep pace? By consistently training their employees and promoting alertness, businesses build a workforce that can effectively thwart fraudulent attempts and minimize financial losses from data breaches. Phishing attacks cost an average of $4.88 million and account for nearly 16% of breaches, underscoring the financial impact of phishing and the necessity for effective training. Additionally, organizations with incident response teams and regular testing save approximately $248,000 annually, further emphasizing the importance of ongoing training and preparedness. Investing in comprehensive training not only safeguards your organization but also fortifies its financial future against the looming threat of cyber fraud.
In the high-stakes world of healthcare, the threat of phishing looms larger than ever. Leaders must recognize the urgency of implementing effective strategies to combat this pervasive cyber threat. By fostering vigilance and prioritizing strong cybersecurity measures, businesses shield themselves from the severe impacts of phishing attacks.
The article outlines essential strategies for leaders, including the importance of proactive defense mechanisms such as:
Additionally, establishing a well-defined incident response plan is crucial for quickly addressing phishing attempts and minimizing damage. Not taking action can result in substantial financial losses and harm to reputation. By continuously updating these strategies based on evolving threats, organizations can enhance their resilience against cyber attacks.
Ultimately, the fight against phishing requires a collective effort from all members of an organization. When leaders invest in thorough training and encourage open communication, they empower employees to spot and report suspicious activities. This proactive approach not only safeguards the organization’s assets but also preserves its reputation in an increasingly digital world. Decisive action today can mean the difference between security and vulnerability tomorrow.
What is phishing?
Phishing is a cyberattack method where attackers impersonate trusted entities to trick individuals into disclosing sensitive information, such as passwords or financial details.
Through what channels can phishing occur?
Phishing can occur through various channels, including email, social media, and text messages.
What are the potential impacts of phishing on businesses?
Phishing can lead to severe impacts on businesses, including data leaks, significant financial losses, and lasting reputational damage.
What is the estimated average expense of a successful online scam in 2026?
The estimated average expense of a successful online scam in 2026 is $4.88 million, which includes recovery costs, lost income, and regulatory fines.
Why is it important for leaders to prioritize cybersecurity measures?
It is important for leaders to prioritize cybersecurity measures to mitigate the financial implications of phishing and to foster a culture of vigilance within their organizations.
How can Cyber Solutions help businesses with cybersecurity?
Cyber Solutions offers 24/7 threat monitoring, which helps businesses catch suspicious activities early and effectively safeguard against ransomware, scams, and other malware issues.
Why is customized training necessary for countering phishing risks?
Customized training is necessary because of the growing complexity of fraudulent schemes, especially those employing AI, and it should be tailored based on industry and employee roles to effectively address these risks.
What risks do organizations face without proactive cybersecurity measures?
Organizations that do not implement proactive cybersecurity measures risk financial loss and damage to their credibility in the eyes of patients and stakeholders.