
In an era where data breaches are increasingly common, the stakes for healthcare organizations have never been higher when it comes to cybersecurity and HIPAA compliance. HIPAA sets forth essential guidelines to protect sensitive patient information, and at the heart of this compliance lies the necessity for robust firewall management. As cyber threats grow more sophisticated, healthcare organizations face mounting pressure to protect sensitive patient data effectively.
How can they ensure their firewalls not only meet HIPAA requirements but also defend against unauthorized access? Let’s explore the essential components of HIPAA compliant firewall requirements and discover best practices to enhance cybersecurity in the healthcare sector.
In an era where healthcare data breaches are on the rise, understanding HIPAA compliance is not just important - it's essential for safeguarding patient information. HIPAA, or the Health Insurance Portability and Accountability Act, establishes national standards for the protection of health information. For any entity dealing with protected health information (PHI), grasping its core components is crucial. The key elements of HIPAA compliance include:
Understanding these essentials is crucial because they directly influence how firewalls are set up and managed to comply with HIPAA compliant firewall requirements, serving as a frontline defense against unauthorized access to sensitive health data. As cybersecurity threats evolve, organizations must prioritize adherence to HIPAA to protect patient information and avoid substantial penalties. Without a robust understanding of HIPAA, healthcare organizations risk not only patient trust but also their very operational integrity.

In an era where cyber threats are increasingly sophisticated, the healthcare sector must prioritize cybersecurity to protect sensitive patient information. To keep ePHI safe, firewalls must adhere to HIPAA compliant firewall requirements by enforcing strict access rules, ensuring that only authorized personnel can view sensitive information. Implementing role-based permissions and considering multi-factor authentication (MFA) can significantly enhance protection.
Keeping detailed logs of who accesses what and when is crucial for spotting potential breaches and staying compliant. This practice not only supports compliance but also strengthens overall safety monitoring. Organizations should establish a routine for reviewing logs and documenting follow-up actions to demonstrate adherence to security policies.
Data transmitted over the network must be encrypted to safeguard against interception. Firewalls should support secure communication protocols such as SSL/TLS, ensuring that ePHI remains confidential during transmission. Regular assessments of encryption methods can help organizations stay ahead of potential vulnerabilities.
Effective network segmentation is crucial for isolating ePHI from less secure areas, thereby reducing the risk of unauthorized access. This practice helps contain potential breaches and limits exposure. Organizations should conduct regular vulnerability scans to identify areas needing segmentation improvements.
To adhere to HIPAA compliant firewall requirements, firewalls must be regularly updated to defend against emerging vulnerabilities. This includes timely application of patches and updates to both hardware and software components, ensuring robust protection against threats. Neglecting these updates could expose organizations to significant regulatory penalties and data breaches.
By adhering to these requirements and implementing proactive strategies, healthcare organizations not only comply with HIPAA but also fortify their defenses against the ever-evolving landscape of cyber threats.

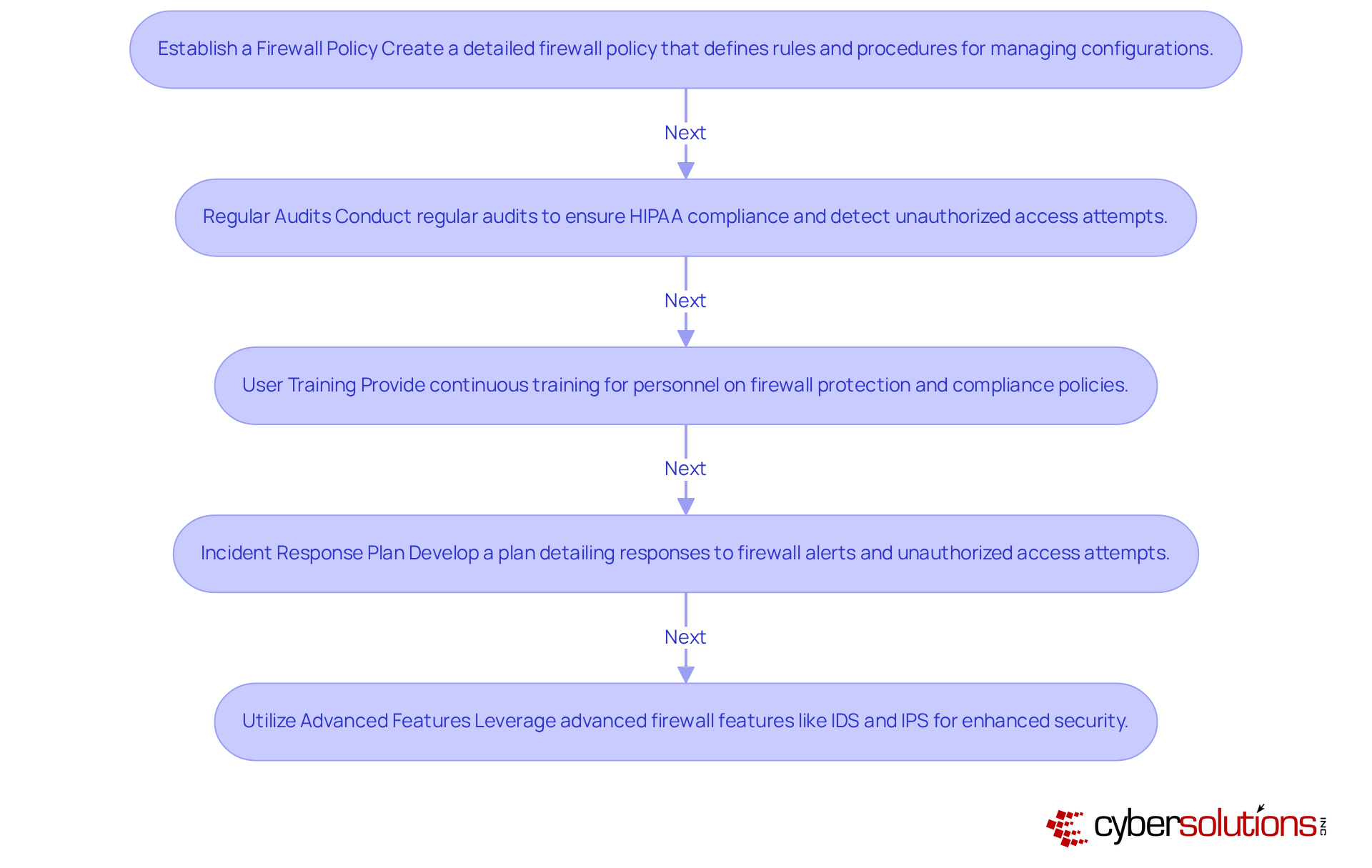
In an era where healthcare data breaches are on the rise, managing firewalls effectively is not just a regulatory requirement; it's a critical component of safeguarding patient information. To effectively manage firewalls in a HIPAA-compliant manner, organizations should adopt the following best practices:
By prioritizing these best practices, organizations can not only comply with HIPAA but also fortify their defenses against the ever-evolving landscape of cyber threats.
In an era where cyber threats are increasingly sophisticated, understanding HIPAA compliant firewall requirements is not just important; it's essential for safeguarding patient data. The significance of protecting patient information is paramount; non-compliance can result in severe penalties and erode trust. By grasping the fundamentals of HIPAA compliance, organizations can establish robust firewalls that serve as a primary defense against unauthorized access to sensitive information.
We’ve explored several key components of HIPAA compliance that are crucial for your organization, including the following:
Each of these elements plays a vital role in shaping the firewall requirements necessary to protect electronic PHI. Additionally, best practices for firewall management, such as the following, are essential strategies that organizations must adopt to enhance their cybersecurity posture:
The evolving landscape of cyber threats necessitates a proactive approach to HIPAA compliance. Many organizations struggle to keep up with the evolving regulations and threats. Organizations must prioritize the implementation of these firewall requirements and best practices to not only meet regulatory standards but also ensure the safety and confidentiality of patient information. Failure to comply not only risks penalties but also jeopardizes patient trust and safety. By prioritizing these firewall requirements, healthcare organizations can not only comply with regulations but also build a fortress around patient trust and data integrity.
What is HIPAA and why is it important?
HIPAA, or the Health Insurance Portability and Accountability Act, establishes national standards for the protection of health information, making it essential for safeguarding patient information in the face of rising healthcare data breaches.
What are the key components of HIPAA compliance?
The key components of HIPAA compliance include the Privacy Rule, Security Rule, Breach Notification Rule, and Enforcement Rule.
What does the Privacy Rule entail?
The Privacy Rule governs the use and disclosure of protected health information (PHI), ensuring confidentiality and requiring entities to obtain patient consent for data use while providing patients with rights regarding their health information.
What is the purpose of the Security Rule?
The Security Rule outlines the necessary technical, administrative, and physical safeguards to protect electronic PHI (ePHI), requiring organizations to implement measures such as encryption, access controls, and regular security audits.
What must entities do under the Breach Notification Rule?
Under the Breach Notification Rule, entities are required to notify affected individuals and the Department of Health and Human Services (HHS) in the event of a data breach, emphasizing timely communication and transparency.
What does the Enforcement Rule cover?
The Enforcement Rule provides guidelines for compliance and outlines penalties for violations. It indicates that entities must be prepared for increased scrutiny and potential audits starting in 2026.
Why is understanding HIPAA compliance essential for healthcare organizations?
Understanding HIPAA compliance is crucial because it influences how firewalls are set up and managed to protect sensitive health data from unauthorized access, helping organizations maintain patient trust and avoid substantial penalties.