
In today's healthcare landscape, the stakes of cybersecurity have never been higher, with threats evolving at an alarming rate. The vulnerability scanning process stands out as a vital defense mechanism for organizations, particularly in healthcare. This proactive approach not only identifies potential weaknesses but also enhances compliance with industry regulations, safeguarding sensitive data.
As vulnerabilities multiply, how can organizations tackle the complexities of vulnerability management to fortify their defenses? Mastering vulnerability management is not just a best practice; it's a critical necessity for safeguarding patient data and maintaining trust in healthcare systems.
In an era where cyber threats are escalating, the vulnerability scanning process has become a critical line of defense for healthcare organizations. This proactive approach is crucial for spotting weaknesses that cybercriminals could exploit. By providing a comprehensive view of a company's security posture, risk assessments enable prompt remediation of potential threats, significantly reducing the likelihood of data breaches.
Recent trends indicate a rise in security disclosures, with projections suggesting that close to 59,000 Common Vulnerabilities and Exposures (CVEs) could be published in 2026. With the increasing number of vulnerabilities, how can organizations ensure they are protected? Implementing regular threat assessments as part of their cybersecurity strategy is essential. The vulnerability scanning process not only enhances security but also facilitates compliance with industry regulations, thereby mitigating legal and financial repercussions associated with data breaches.
For example, entities in the healthcare field have reported a staggering 168% rise in security attacks, emphasizing the critical need for strong examination practices to safeguard sensitive patient information. How can ongoing security assessments help these entities manage compliance obligations like HIPAA more effectively? By employing these assessments, organizations can ensure their defenses are aligned with emerging threats.
Expert opinions stress that security scanning is not just a technical requirement but a strategic necessity. It enables entities to prioritize their security measures efficiently, concentrating on high-severity weaknesses that present the greatest danger. Organizations risk not only their data but also their reputation and financial stability without a robust vulnerability scanning process. As the threat environment evolves, the ability to swiftly recognize and address vulnerabilities will be essential for maintaining compliance and enhancing overall cybersecurity resilience.
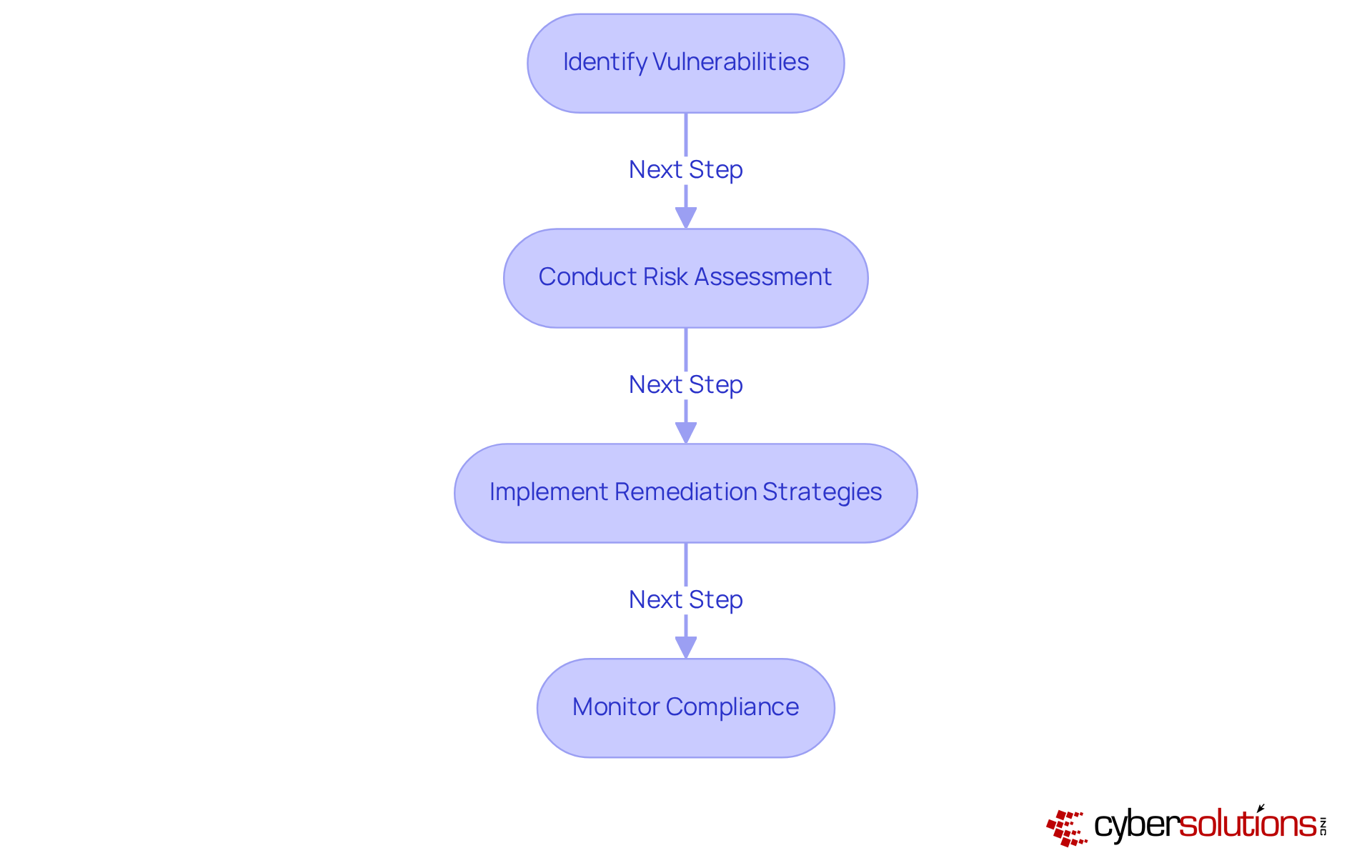
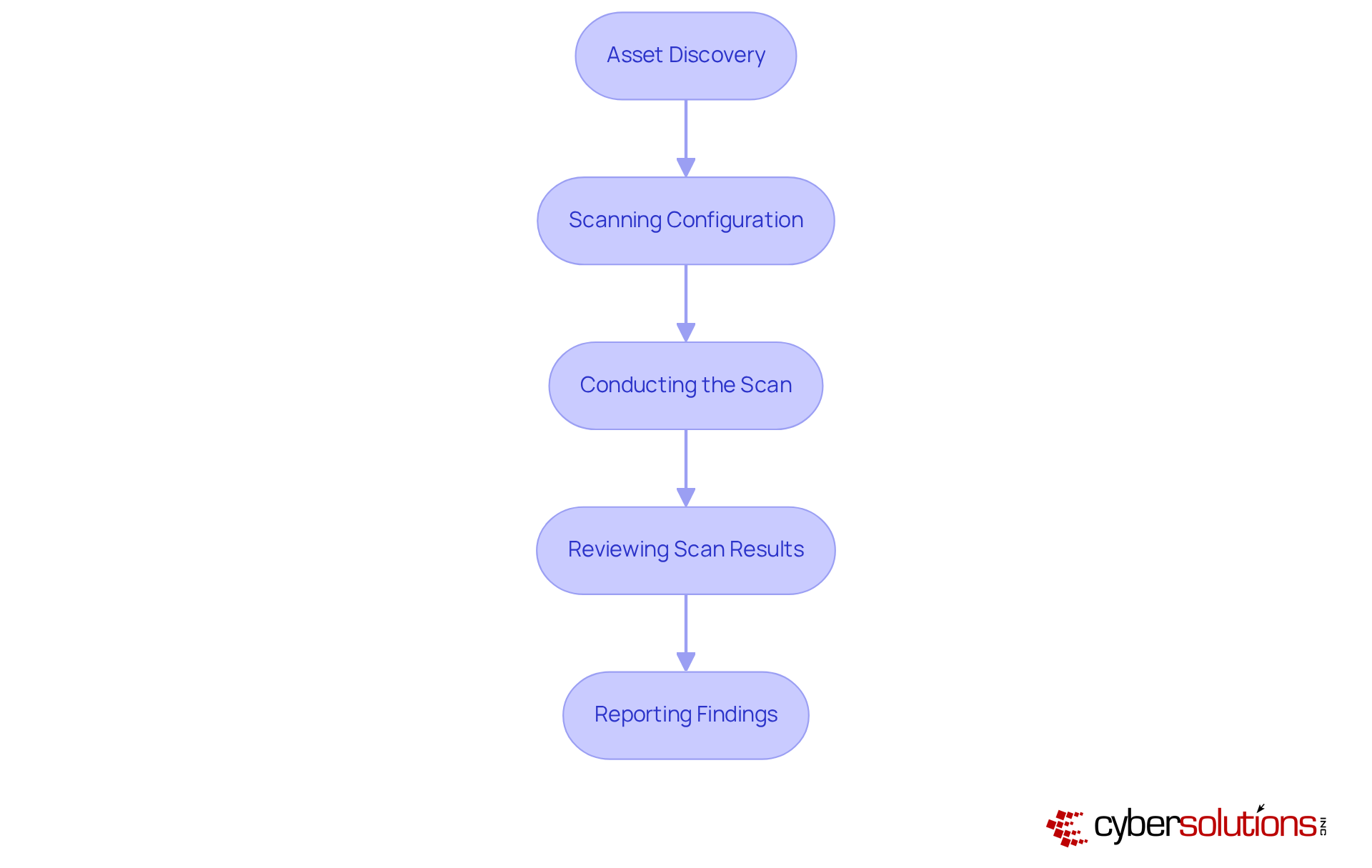
In an era where cyber threats loom larger than ever, the healthcare sector stands at a critical juncture, facing unprecedented challenges in safeguarding sensitive information. The vulnerability scanning process is crucial for recognizing and reducing security threats within a company. It typically involves several key steps:
Organizations are urged to implement best practices during the vulnerability scanning process, including the incorporation of threat intelligence feeds to enhance weakness detection and prioritization. Regular security assessments, including the vulnerability scanning process, not only aid in sustaining a robust protective stance but also guarantee adherence to industry standards, ultimately protecting essential information and operational integrity.
In 2025, a record 48,185 CVEs were published, highlighting the necessity of performing regular security scans. The typical mean duration to address high and critical issues was 54.81 days, emphasizing the need for effective resolution strategies. Additionally, the CISA Known Exploited Vulnerabilities catalog grew to 1,484 entries, underscoring the importance of addressing known threats promptly. As Dima Potekhin, CTO and Co-Founder of CyCognito, suggests, integrating real-time threat intelligence feeds with your security scanner can significantly enhance detection capabilities. Organizations must also navigate challenges such as legacy systems blocking patches and high rates of false positives, which complicate the remediation process. Without a proactive approach to risk management, organizations risk not only their data but also their reputation and operational viability in an increasingly hostile digital landscape.
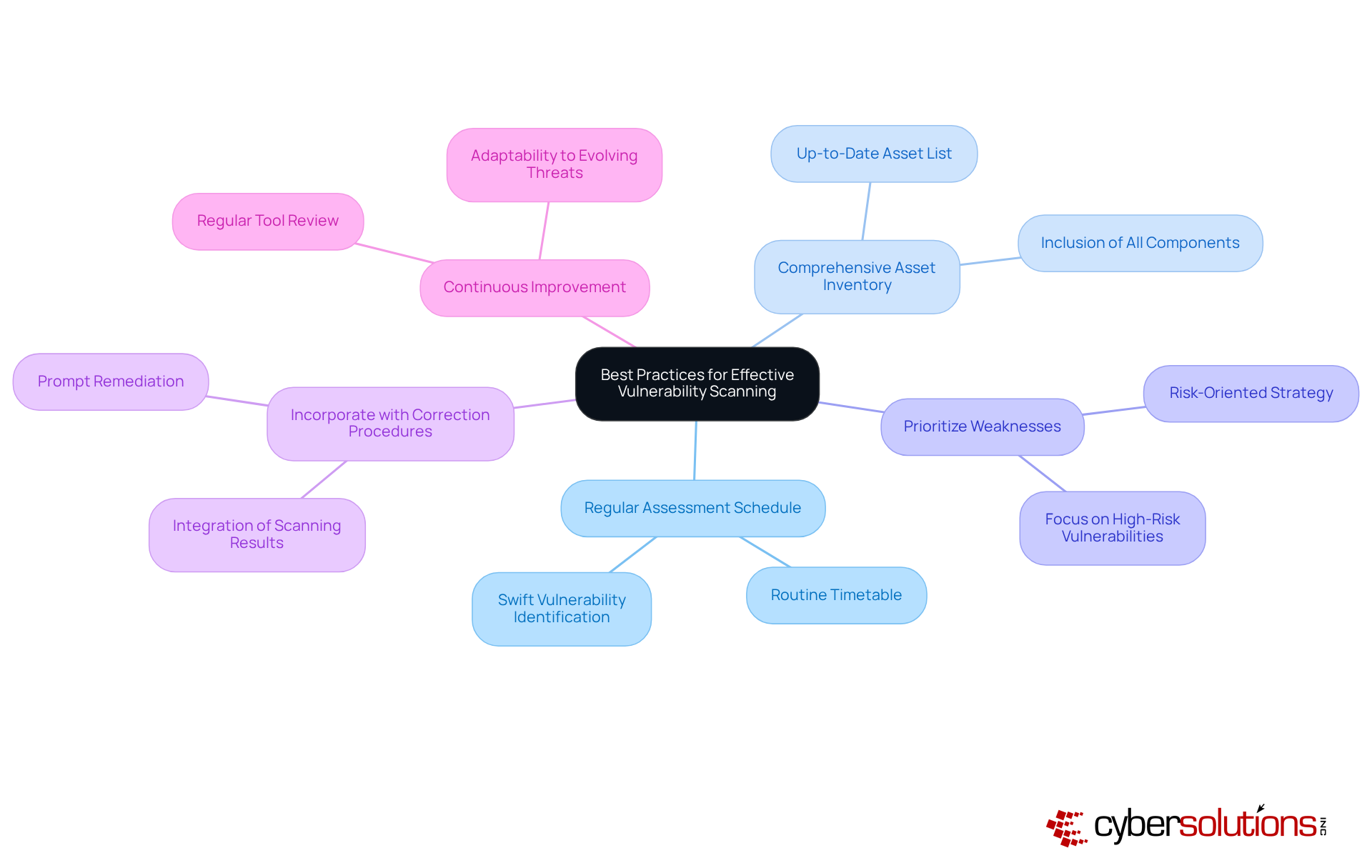
In an era where cyber threats loom larger than ever, healthcare organizations must prioritize cybersecurity to safeguard sensitive patient data and maintain trust. To ensure effective vulnerability scanning, organizations should adhere to the following best practices:
By adopting these best practices, organizations can not only protect their assets but also enhance their overall security posture in an increasingly hostile digital landscape.
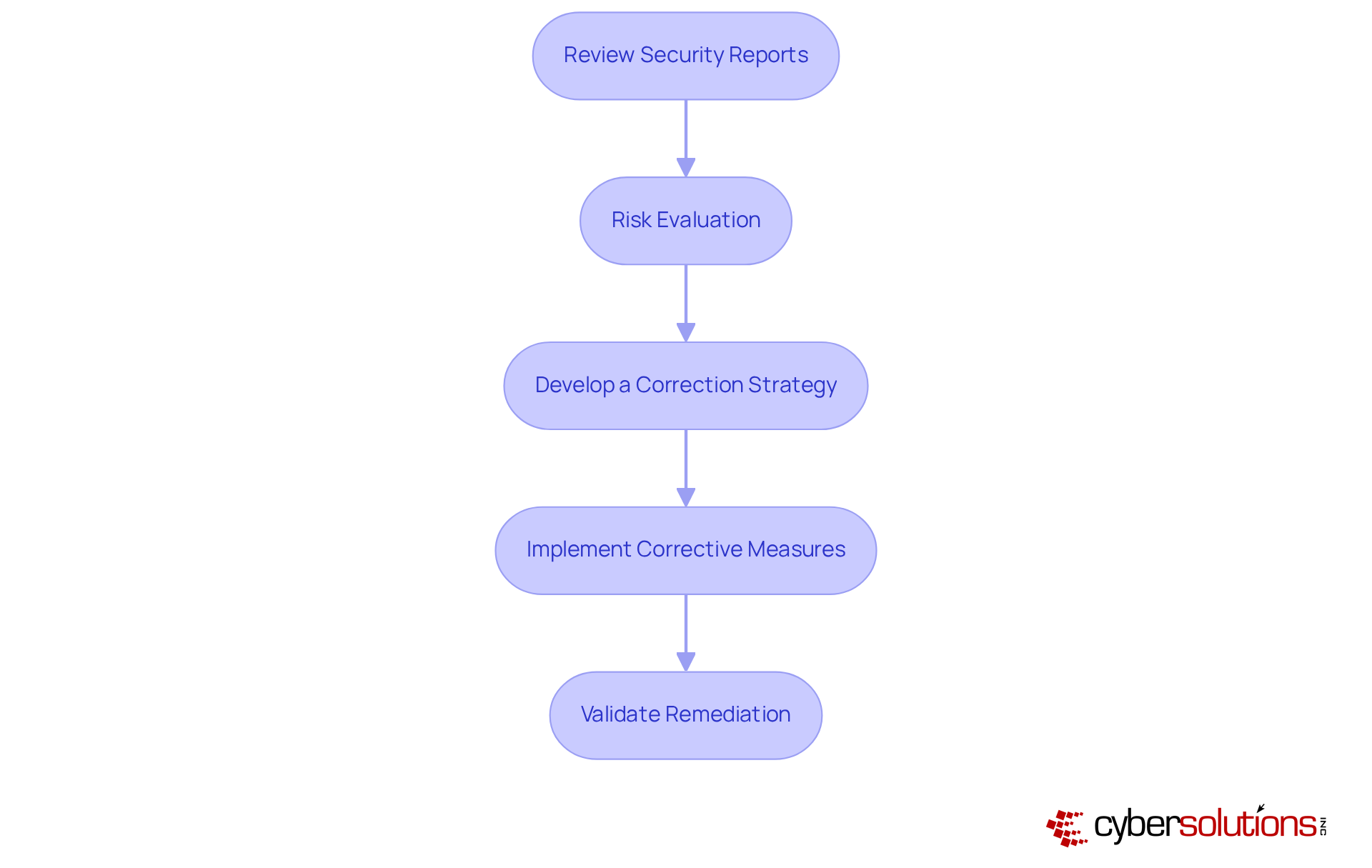
In an era where healthcare data breaches are on the rise, understanding cybersecurity vulnerabilities is not just important - it's imperative for safeguarding patient information and organizational integrity. After completing a vulnerability scan, the next essential step is to analyze the results and formulate a remediation strategy:
By proactively addressing vulnerabilities, organizations not only protect their data but also fortify their reputation in an increasingly scrutinized industry.
In an era where cyber threats loom larger than ever, the vulnerability scanning process is crucial for healthcare organizations. By systematically identifying and addressing potential weaknesses, organizations can significantly strengthen their defenses against the growing threat of cyber attacks. This proactive approach is vital for safeguarding sensitive information and meeting regulatory standards, which ultimately protects your organization’s reputation and operational integrity.
Throughout this article, we’ve outlined key steps in mastering the vulnerability scanning process:
Regular assessments and prioritizing high-risk vulnerabilities are critical strategies for organizations aiming to stay ahead of potential threats. Moreover, integrating real-time threat intelligence and continuous validation processes is essential for maintaining a robust security posture.
With cyber threats evolving at an alarming rate, adopting a comprehensive and proactive vulnerability scanning strategy is not just important; it’s imperative. Organizations are encouraged to embrace these best practices, ensuring their cybersecurity measures are not only reactive but also anticipatory. By committing to regular vulnerability assessments and remediation planning, organizations can enhance their resilience in an increasingly hostile digital landscape, ultimately protecting their most valuable assets: data and trust. Only through a commitment to proactive vulnerability management can organizations truly safeguard their data and maintain the trust of those they serve.
What is vulnerability scanning?
Vulnerability scanning is a proactive process used to identify weaknesses in a company's security posture that cybercriminals could exploit. It provides a comprehensive view of security risks and facilitates prompt remediation of potential threats.
Why is vulnerability scanning important for healthcare organizations?
Vulnerability scanning is crucial for healthcare organizations as it helps them spot weaknesses that could lead to data breaches, enhances security, and ensures compliance with industry regulations, thereby mitigating legal and financial repercussions.
What recent trends have been observed in security disclosures?
Recent trends indicate a significant rise in security disclosures, with projections suggesting that close to 59,000 Common Vulnerabilities and Exposures (CVEs) could be published in 2026.
How can organizations protect themselves from increasing vulnerabilities?
Organizations can protect themselves by implementing regular threat assessments as part of their cybersecurity strategy, which helps to identify and address vulnerabilities effectively.
How have security attacks in the healthcare field changed recently?
Entities in the healthcare field have reported a staggering 168% rise in security attacks, highlighting the urgent need for strong examination practices to safeguard sensitive patient information.
How do ongoing security assessments help organizations manage compliance obligations like HIPAA?
Ongoing security assessments help organizations align their defenses with emerging threats, ensuring they meet compliance obligations such as HIPAA more effectively.
What do experts say about the necessity of security scanning?
Experts emphasize that security scanning is not just a technical requirement but a strategic necessity that allows entities to prioritize security measures and focus on high-severity weaknesses.
What are the risks of not having a robust vulnerability scanning process?
Without a robust vulnerability scanning process, organizations risk compromising their data, damaging their reputation, and threatening their financial stability.