Introduction
In an era where data breaches are rampant, cybersecurity has emerged as a critical priority for organizations, especially in the financial sector. As the FTC Safeguards Rule establishes a framework for protecting sensitive information, organizations must recognize that understanding and implementing these requirements is vital for maintaining client trust and avoiding severe penalties.
Organizations often struggle to align their existing frameworks with the FTC Safeguards Rule, leading to potential compliance gaps. What are the best practices for navigating this complex landscape? To navigate this complex landscape, organizations must adopt best practices that not only ensure compliance but also fortify their defenses against evolving cyber threats. Without a robust strategy for compliance and resilience, organizations risk not just penalties, but their very reputation in the marketplace.
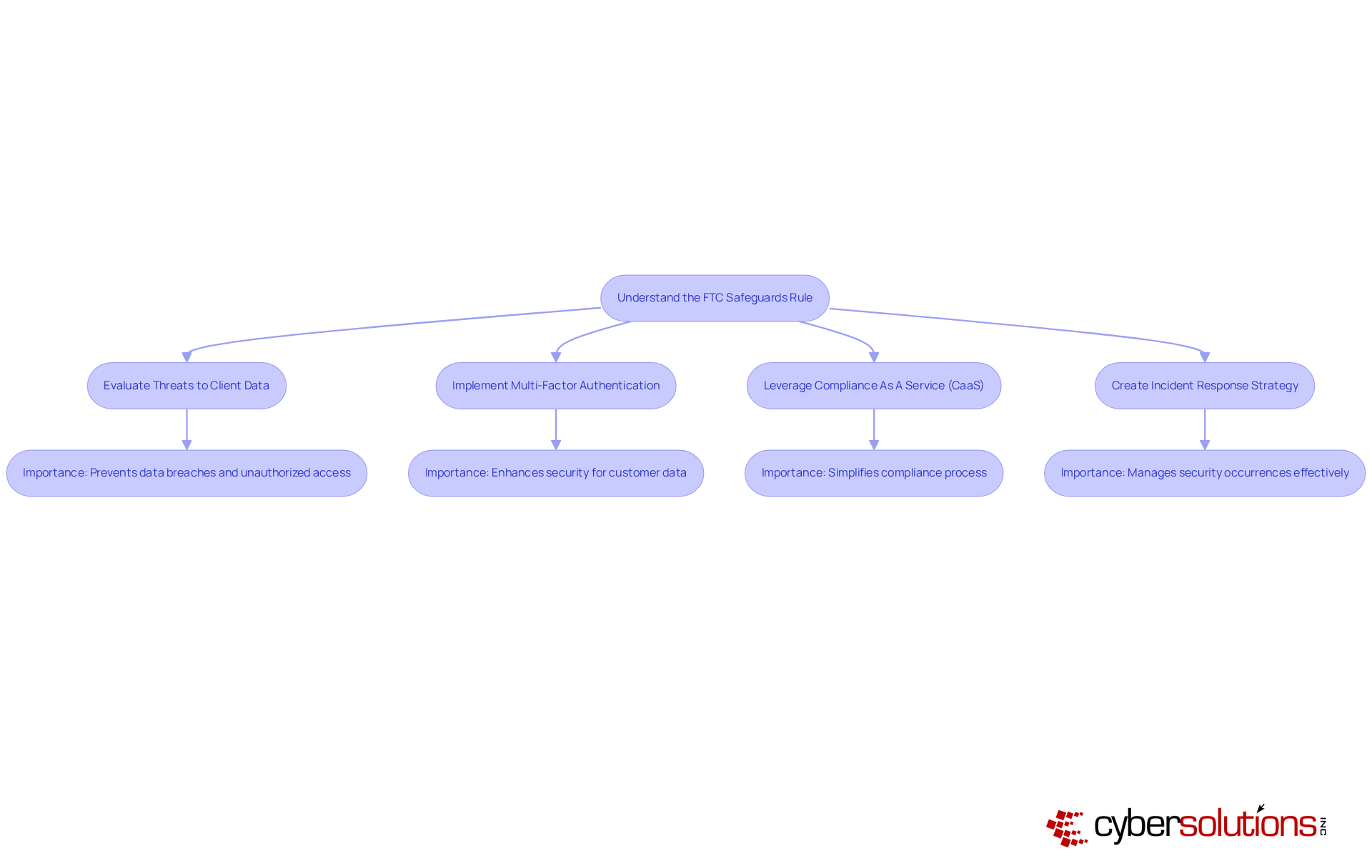
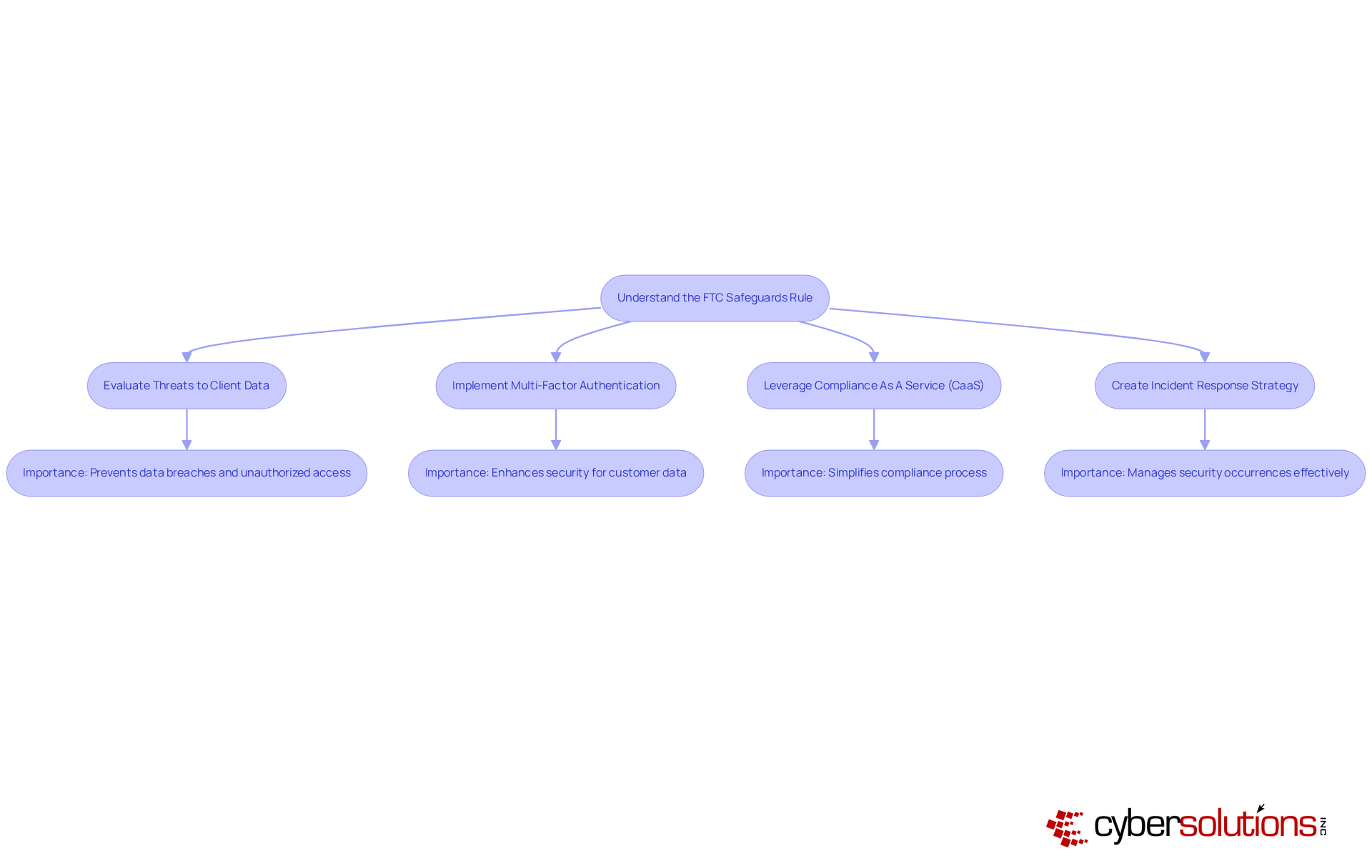
Understand the FTC Safeguards Rule and Its Importance
In an era where data breaches can cripple organizations, the FTC Safeguards Rule emerges as a critical mandate for financial institutions handling sensitive information. This regulation is designed to prevent data breaches and unauthorized access, which can lead to crippling financial penalties - potentially reaching up to $46,517 per violation per day - and significant reputational harm. By 2026, grasping and following the Safeguards Rule will be essential for organizations that want to keep client trust and stand out in a competitive market. Compliance safeguards client information and is a key part of a comprehensive management strategy.
Organizations should regularly evaluate threats to client data using the FTC Safeguards Rule risk assessment template to stay ahead of potential risks and create a documented incident response strategy to manage security occurrences. Implementing multi-factor authentication for accessing customer data is a critical compliance measure. Additionally, leveraging Compliance As A Service (CaaS) solutions can simplify the compliance process, providing businesses with the necessary expertise and ongoing monitoring to ensure adherence to the FTC Safeguards Rule risk assessment template.
As businesses navigate the complexities of data protection, the Safeguards Rule stands out as a pivotal framework that enhances operational integrity and fosters consumer confidence. Ultimately, embracing the Safeguards Rule is not just about compliance; it's about securing a competitive edge in a data-driven world.
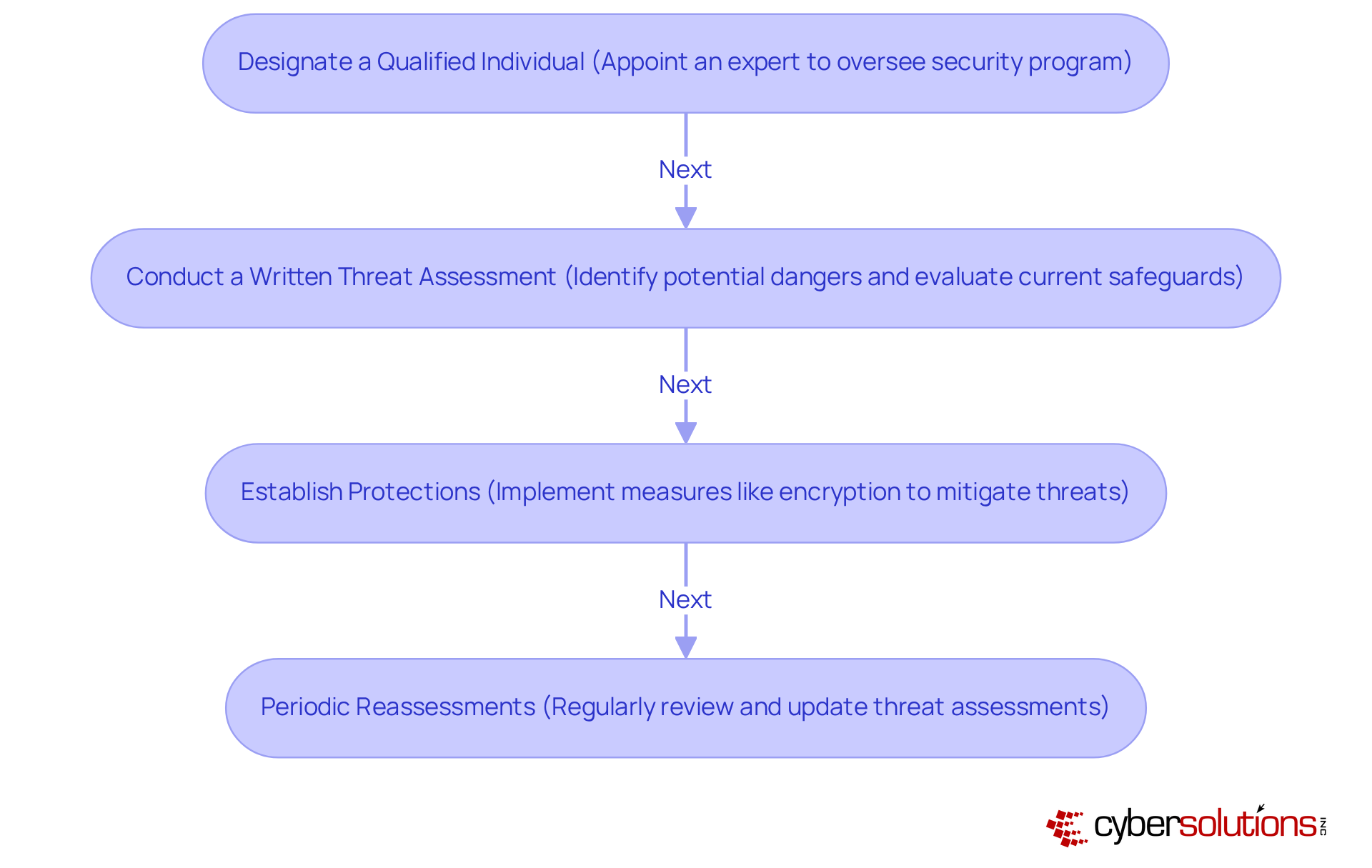
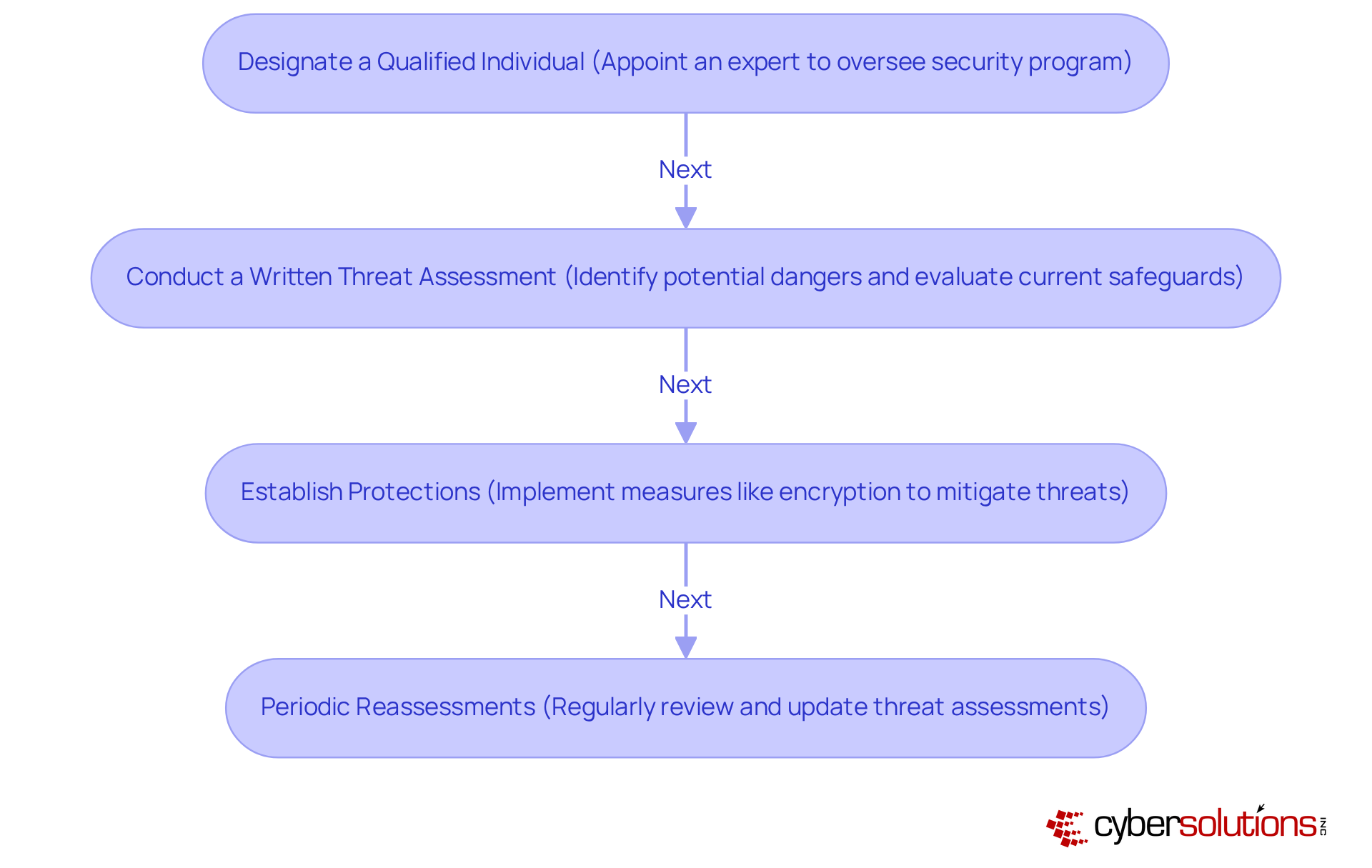
Identify Key Compliance Requirements for Risk Assessment
In an era where cybersecurity threats loom large, healthcare organizations must prioritize compliance with the FTC Safeguards Rule to protect sensitive patient data.
To comply with the FTC Safeguards Rule, organizations must establish several critical requirements for their risk assessment templates:
- Designating a Qualified Individual: Appointing a Qualified Individual to oversee your security program is not just essential; it's a critical step in safeguarding your organization. This person should possess relevant expertise to effectively manage compliance efforts.
- Conducting a thorough written threat assessment is crucial; it not only identifies potential dangers to customer information but also evaluates how well your current safeguards hold up against these threats, following the FTC Safeguards Rule risk assessment template. This evaluation should be recorded and encompass criteria for assessing dangers and threats.
- Establishing Protections: Based on your vulnerability assessment, it's imperative to implement robust measures that effectively mitigate identified threats. This includes ensuring that customer information is encrypted both in transit and at rest.
- Periodic Reassessments: Regularly reviewing and updating your threat assessment is vital to stay ahead of emerging dangers and adapt to the ever-changing business landscape. This ongoing assessment aids in preserving the effectiveness of the protective measures in place.
By addressing these requirements, organizations not only comply with regulations but also fortify their defenses against the ever-evolving landscape of cyber threats.
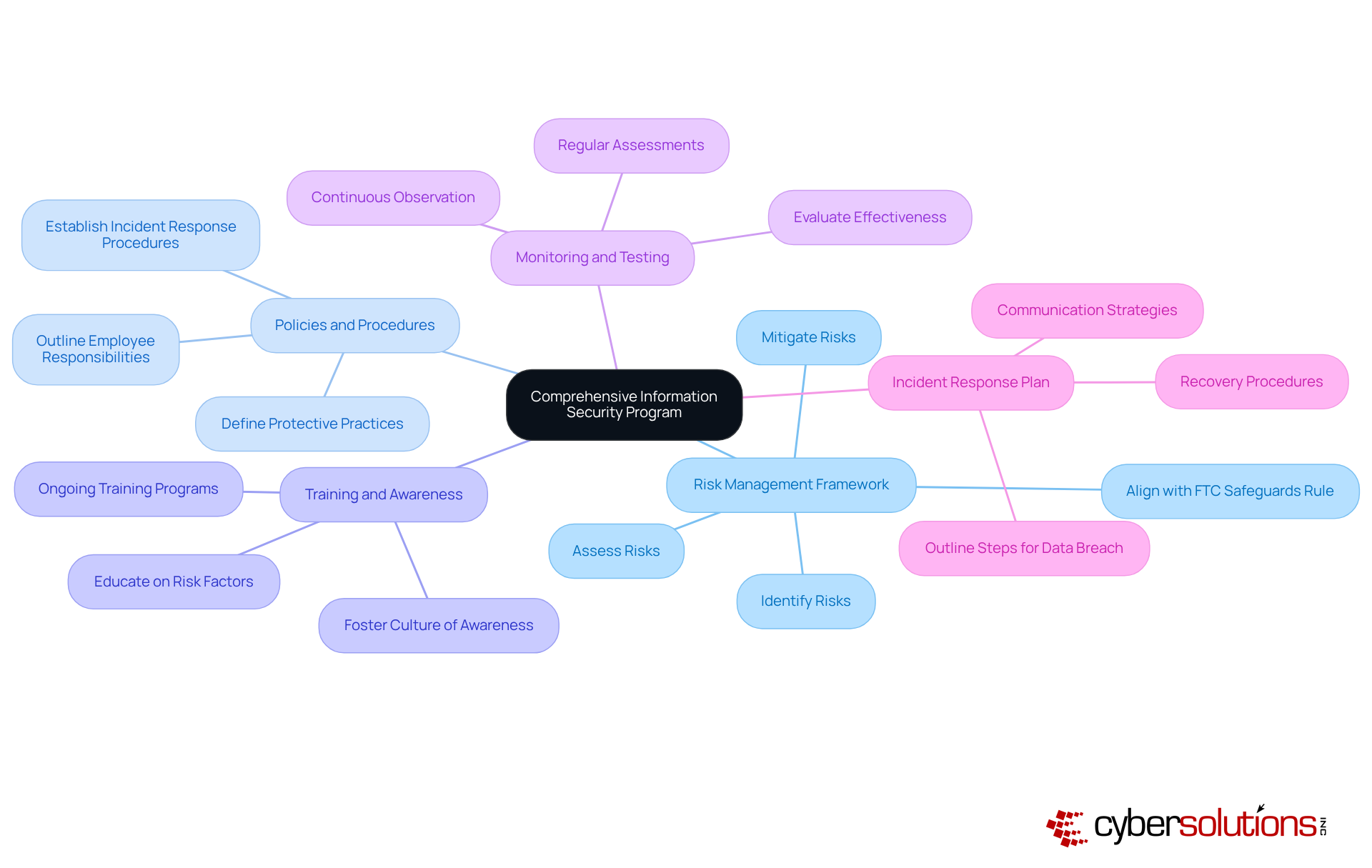
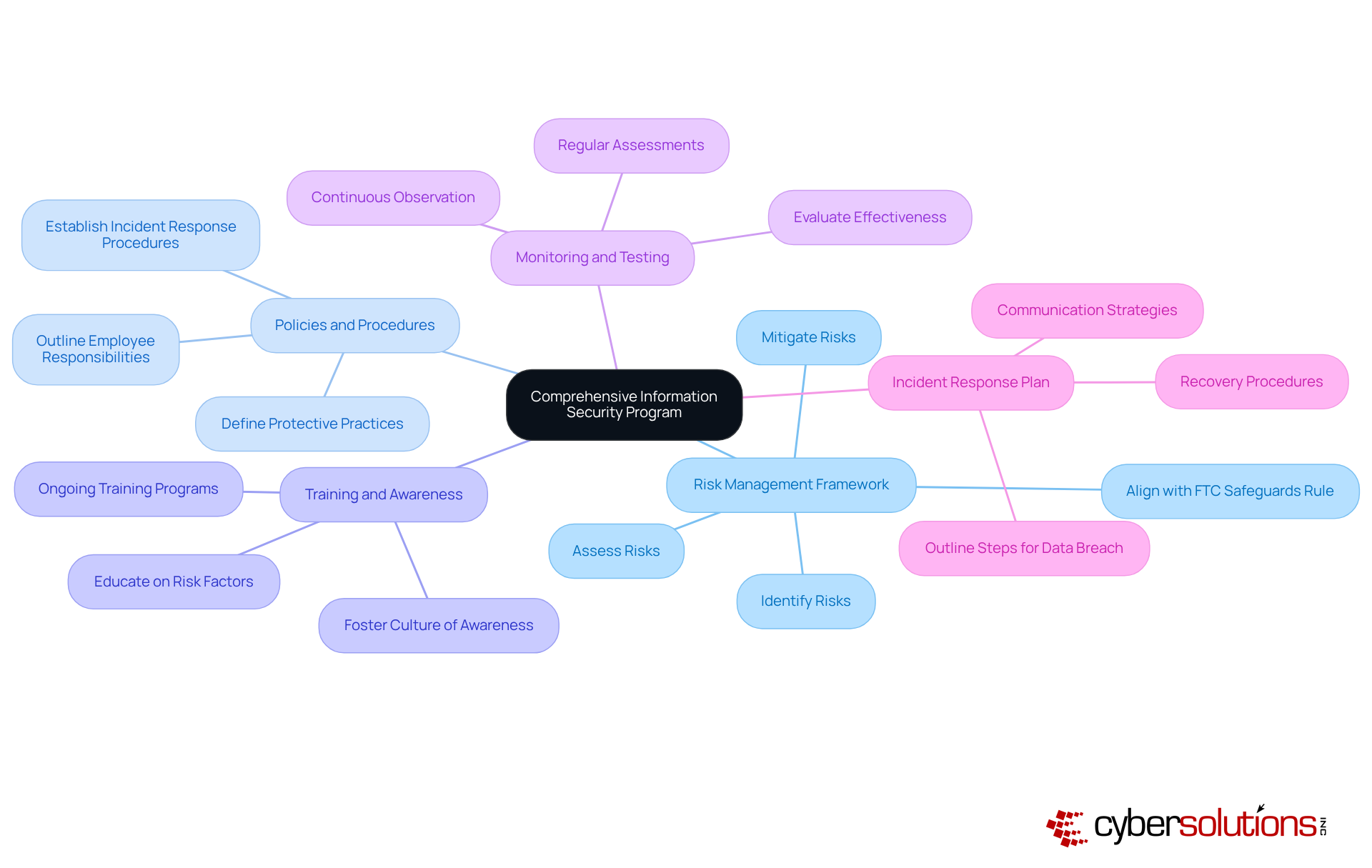
In an era where healthcare data breaches are on the rise, the need for robust cybersecurity measures has never been more critical. A comprehensive information security program must include several essential components to effectively safeguard customer information:
- Risk Management Framework: Establish a comprehensive framework that identifies, assesses, and mitigates risks associated with customer information. This framework should align with the FTC Safeguards Rule risk assessment template to ensure that all potential vulnerabilities are addressed.
- Policies and Procedures: Create clear and concise guidelines and protocols that define protective practices, outline employee responsibilities, and establish incident response procedures. These documents form the foundation of an organizational safety culture.
- Training and Awareness: Implement ongoing training programs to educate employees about risk factors and best practices. Consistent training fosters a culture of awareness, enabling staff to identify and respond to potential threats effectively.
- Monitoring and Testing: Continuously observe protective measures and conduct regular assessments to evaluate their effectiveness. This proactive approach helps identify weaknesses and ensures compliance with the evolving requirements outlined in the FTC Safeguards Rule risk assessment template.
- Incident Response Plan: Develop a detailed incident response plan that outlines specific steps to take in the event of a data breach. This plan should include communication strategies, roles and responsibilities, and recovery procedures to minimize impact.
By integrating these components, organizations can develop a resilient information security program that utilizes the FTC Safeguards Rule risk assessment template to ensure compliance and effectively protect customer information. Without a proactive approach to cybersecurity, healthcare organizations risk not only their reputation but also the trust of their patients.
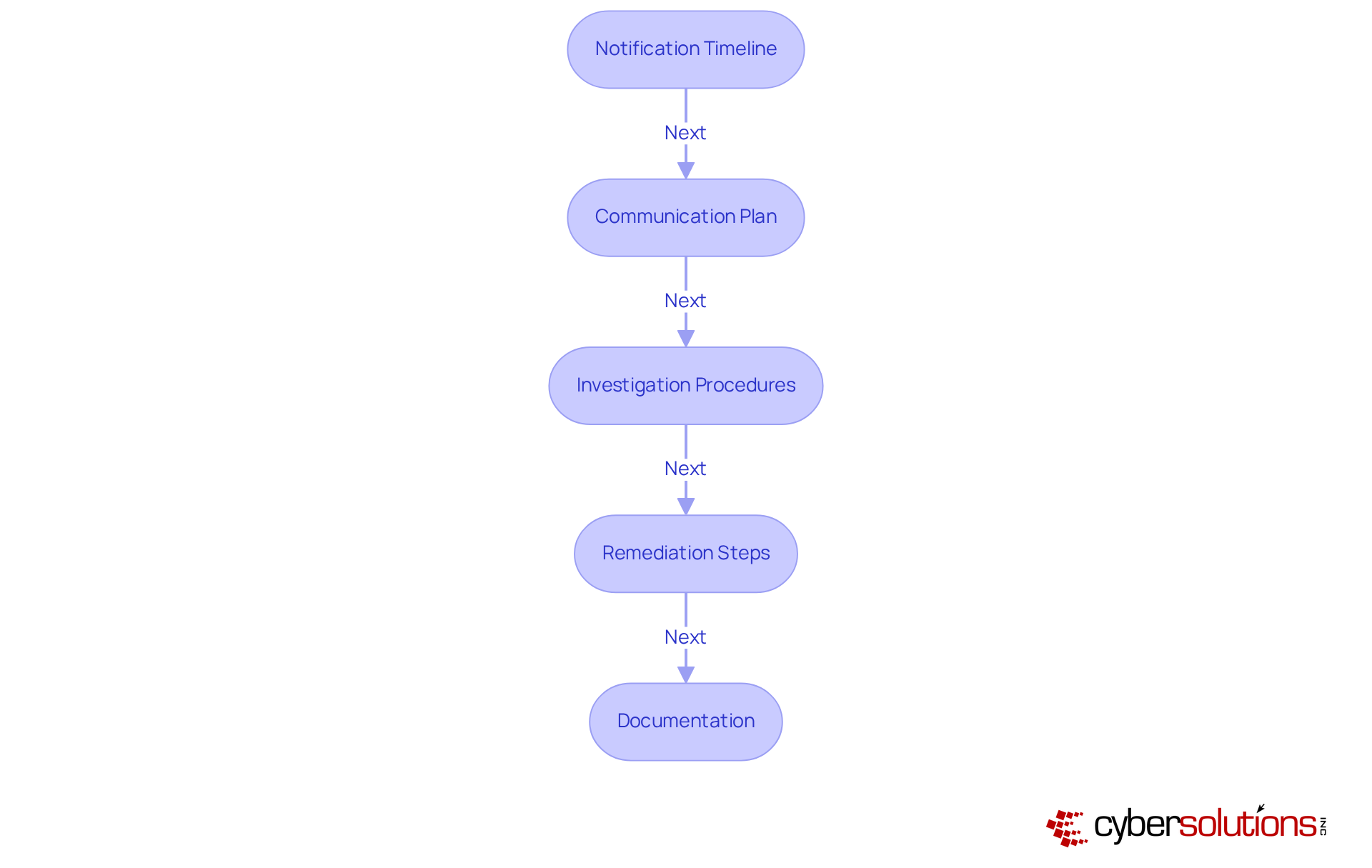
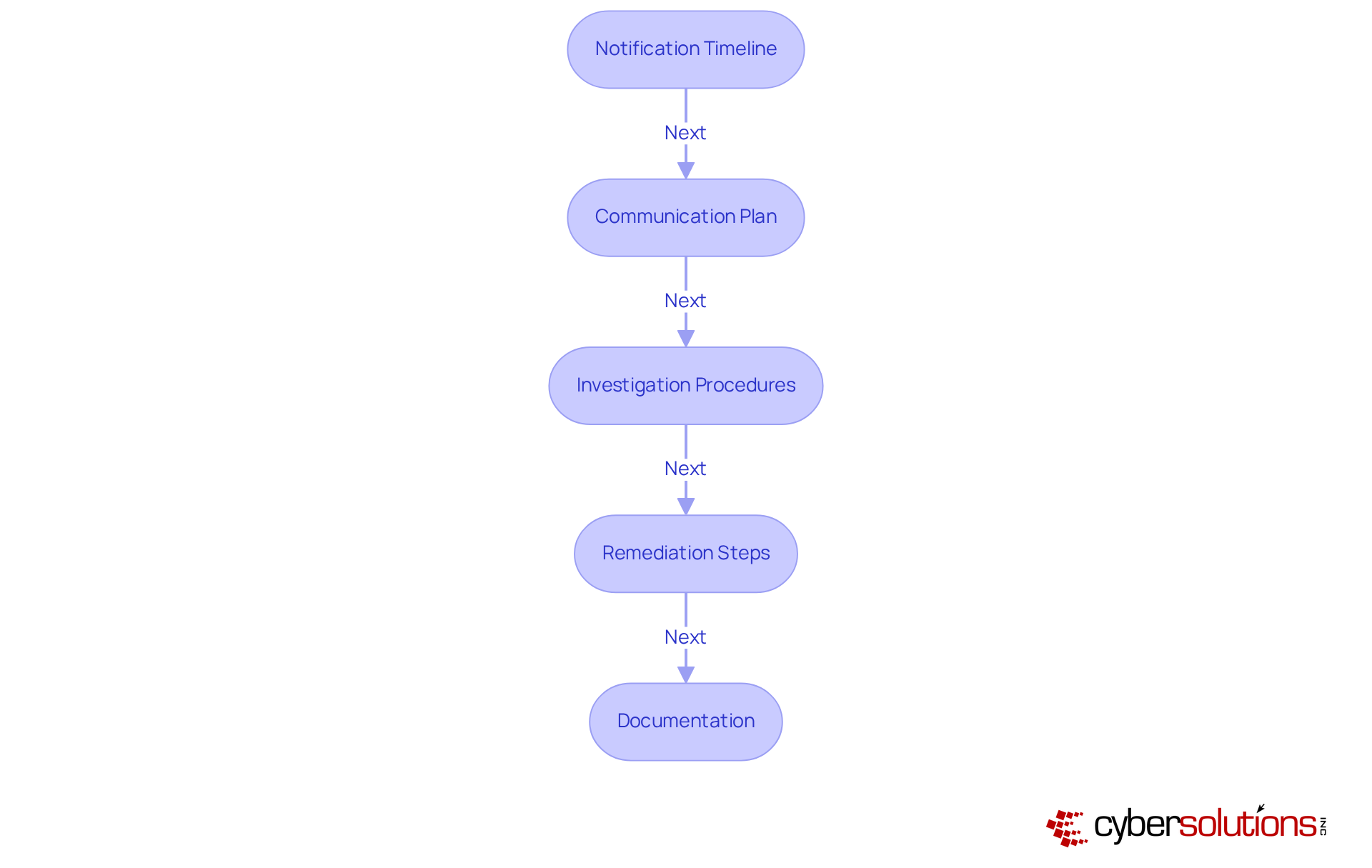
Incorporate Breach Notification Protocols into Your Template
In an era where data breaches can jeopardize not just finances but also reputations, having robust breach notification protocols is non-negotiable for healthcare organizations. Organizations should incorporate the following key elements:
- Notification Timeline: Establish a clear timeline for notifying affected individuals and regulatory bodies after a breach. Financial institutions must inform the FTC within 30 days if the breach involves unauthorized acquisition of unprotected data affecting 500 or more individuals.
- Communication Plan: Create a thorough communication strategy that outlines how to inform stakeholders, including clients and employees, about the breach. Effective communication is essential for preserving stakeholder confidence and ensuring that individuals comprehend the possible dangers linked to the compromised data.
- Investigation Procedures: Define procedures for investigating the breach, including identifying the cause and assessing the impact. This should entail a comprehensive risk assessment to evaluate potential risks and threats to client data, utilizing the FTC safeguards rule risk assessment template.
- Remediation Steps: Outline specific steps to remediate the breach and prevent future incidents. This includes implementing necessary safeguards, such as updating security policies and conducting regular monitoring and testing of security measures to ensure their effectiveness. Tailored remediation strategies should be developed to address compliance gaps, including process improvements and technology upgrades.
- Documentation: Maintain thorough documentation of the breach and the response actions taken. This documentation should include all communications, investigation findings, and remediation efforts, as well as compliance with state and federal notification laws. Preparing detailed documentation is essential for demonstrating compliance during audits and should be maintained for at least seven years as a best practice.
By prioritizing these protocols, organizations not only comply with regulations but also build a resilient framework that safeguards their most valuable asset: trust.
Conclusion
In an era where data breaches can cripple organizations, understanding the FTC Safeguards Rule is not just important - it's essential for survival in the healthcare and financial sectors. This regulation safeguards client data and is vital for building trust and integrity in a fiercely competitive market. Adhering to the Safeguards Rule not only mitigates data breach risks but also positions businesses for a competitive edge in the market.
Key components of compliance include:
- Appointing a Qualified Individual
- Conducting thorough threat assessments
- Establishing robust protections
- Maintaining an ongoing review process
Additionally, developing a comprehensive information security program that encompasses policies, training, monitoring, and incident response plans ensures that organizations are well-equipped to handle potential threats. Incorporating effective breach notification protocols further strengthens an organization’s resilience and commitment to safeguarding client trust.
In today's data-driven landscape, embracing the FTC Safeguards Rule is more than just compliance - it's a strategic necessity for success. Organizations must prioritize these best practices to not only avoid costly penalties but also foster a culture of security and trust. By embracing these practices, organizations can transform compliance into a strategic advantage, ensuring they thrive in a data-centric world.
Frequently Asked Questions
What is the FTC Safeguards Rule?
The FTC Safeguards Rule is a regulation designed to prevent data breaches and unauthorized access to sensitive information handled by financial institutions.
Why is the FTC Safeguards Rule important?
It is important because it helps protect client information, prevents data breaches that can lead to significant financial penalties (up to $46,517 per violation per day), and mitigates reputational harm for organizations.
What are the potential consequences of not complying with the FTC Safeguards Rule?
Non-compliance can result in hefty financial penalties and damage to an organization’s reputation, which can undermine client trust.
What should organizations do to comply with the FTC Safeguards Rule?
Organizations should regularly evaluate threats to client data, use the FTC Safeguards Rule risk assessment template, create a documented incident response strategy, and implement multi-factor authentication for accessing customer data.
How can Compliance As A Service (CaaS) solutions help organizations?
CaaS solutions can simplify the compliance process by providing businesses with the necessary expertise and ongoing monitoring to ensure adherence to the FTC Safeguards Rule.
What is the significance of the year 2026 in relation to the FTC Safeguards Rule?
By 2026, understanding and following the Safeguards Rule will be essential for organizations that aim to maintain client trust and remain competitive in the market.
How does the FTC Safeguards Rule contribute to operational integrity and consumer confidence?
The Safeguards Rule enhances operational integrity by establishing a framework for data protection, which fosters consumer confidence in organizations' ability to safeguard their sensitive information.
List of Sources
- Understand the FTC Safeguards Rule and Its Importance
- Everything to Know About the Updated FTC Safeguards Rule (https://hyperproof.io/resource/updated-ftc-safeguards-rule-2023)
- FTC Safeguards Rule: What Your Business Needs to Know (https://ftc.gov/business-guidance/resources/ftc-safeguards-rule-what-your-business-needs-know)
- FTC Safeguards Rule 2026: Avoid Costly Compliance Mistakes (https://alphacis.com/ftc-safeguards-rule-2026-avoid-costly-compliance-mistakes)
- How to Comply with The FTC Safeguards Rule (5 Strategies) | UpGuard (https://upguard.com/blog/complying-with-the-ftc-safeguards-rule)
- FTC safeguards rule explained: Accountant's guide to creating a data security plan | OnPay (https://onpay.com/ledger/ftc-safeguards-rule-explained)
- Identify Key Compliance Requirements for Risk Assessment
- Everything to Know About the Updated FTC Safeguards Rule (https://hyperproof.io/resource/updated-ftc-safeguards-rule-2023)
- FTC Safeguards Rule: What Your Business Needs to Know (https://ftc.gov/business-guidance/resources/ftc-safeguards-rule-what-your-business-needs-know)
- How to Comply with The FTC Safeguards Rule (5 Strategies) | UpGuard (https://upguard.com/blog/complying-with-the-ftc-safeguards-rule)
- Develop a Comprehensive Information Security Program
- FTC Provides Guidance on Updated Safeguards Rule (https://ftc.gov/news-events/news/press-releases/2025/06/ftc-provides-guidance-updated-safeguards-rule)
- FTC Safeguards Rule - Cynomi (https://cynomi.com/frameworks/ftc-safeguards-rule)
- Everything to Know About the Updated FTC Safeguards Rule (https://hyperproof.io/resource/updated-ftc-safeguards-rule-2023)
- FTC Safeguards Rule: What Your Business Needs to Know (https://ftc.gov/business-guidance/resources/ftc-safeguards-rule-what-your-business-needs-know)
- New FTC Guidance Clarifies Safeguards Rule Obligations (https://compliancescorecard.com/2025/06/new-ftc-guidance-clarifies-safeguards-rule-obligations)
- Incorporate Breach Notification Protocols into Your Template
- FTC Safeguards Rule: What Your Business Needs to Know (https://ftc.gov/business-guidance/resources/ftc-safeguards-rule-what-your-business-needs-know)
- FTC safeguards rule explained: Accountant's guide to creating a data security plan | OnPay (https://onpay.com/ledger/ftc-safeguards-rule-explained)
- GLBA Data Breach Notification Requirements: Complete Guide [2026] (https://saltycloud.com/blog/glba-data-breach-notification)
- Navigating the FTC's Updated Data Breach Reporting Requirements - RadarFirst (https://radarfirst.com/webinar/navigating-the-ftcs-updated-data-breach-reporting-requirements)
- Data Breach Response: A Guide for Business (https://ftc.gov/business-guidance/resources/data-breach-response-guide-business)