
In today's healthcare landscape, the stakes of cybersecurity have never been higher, making it imperative for executives to grasp the financial implications of network firewall pricing. The costs associated with firewalls can be daunting, influenced by factors such as:
Navigating the complexities of firewall pricing can be challenging for executives, especially when balancing security needs with budget constraints. Making uninformed decisions can result in significant financial setbacks that could have been avoided. Understanding these elements is not just a matter of compliance; it's essential for safeguarding your organization's financial health and operational integrity.
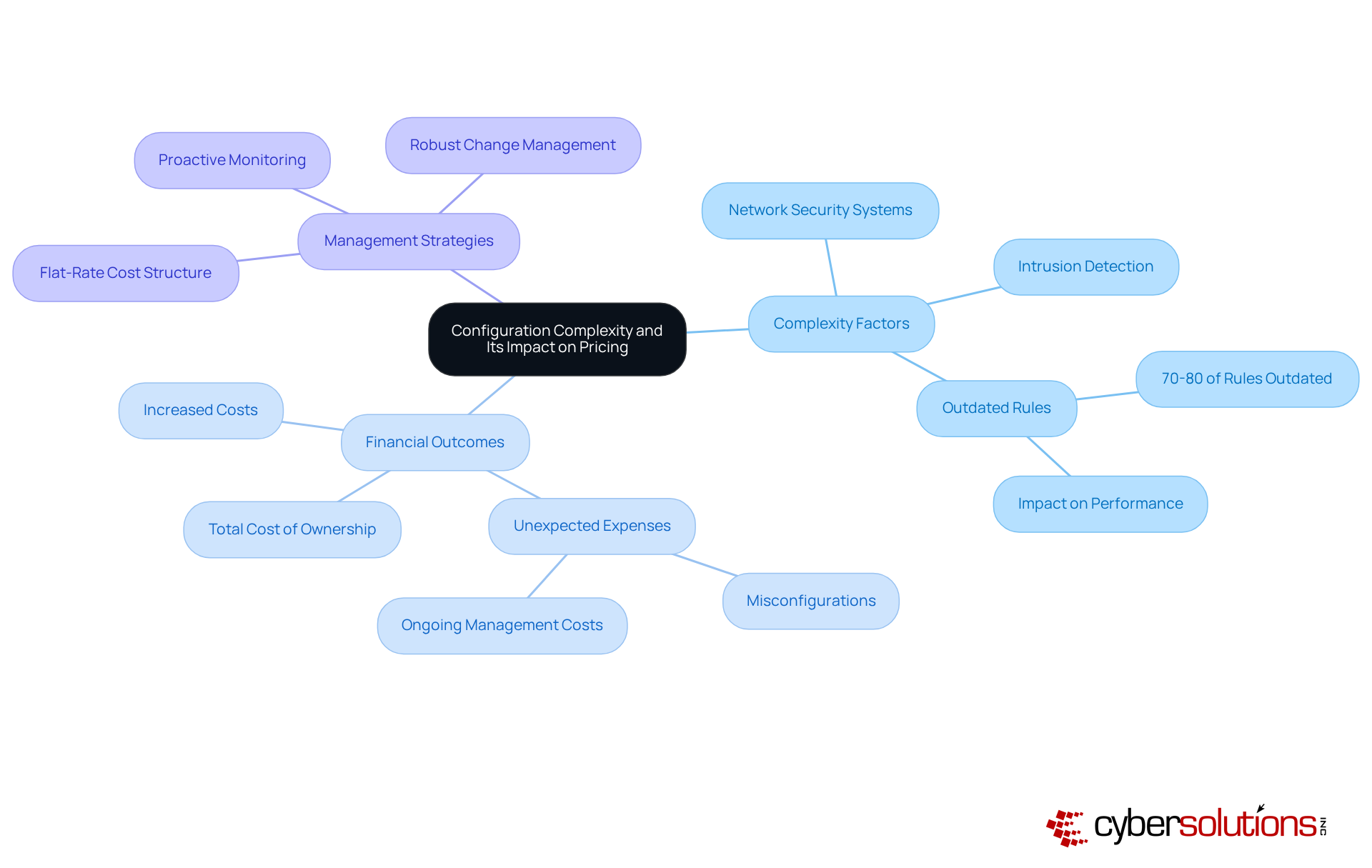
In the intricate landscape of cybersecurity, the configuration of network security systems can dramatically influence financial outcomes. The complexity of a network security system's configuration plays a crucial role in determining its network firewall pricing. More complex arrangements often require additional resources for both setup and ongoing management, leading to higher expenses. For instance, security barriers that connect with various systems or provide advanced functionalities like intrusion detection systems typically incur greater costs.
In fact, 70-80% of security rules in large enterprises are often outdated or redundant. This can lead to outages, decreased productivity, and increased administrative burdens. Executives should thoughtfully assess the long-term consequences of configuration complexity when reviewing security options, as these elements can lead to unforeseen financial challenges, including expenses related to misconfigurations. The total cost of ownership for firewalls, which includes network firewall pricing, encompasses both acquisition and ongoing management costs. Many organizations overlook these ongoing expenses, leading to unexpected financial strain.
Cybersecurity experts often point out that expenses vary based on your specific business needs. With Cyber Solutions' 24/7 threat monitoring, businesses can proactively safeguard against ransomware and phishing attacks, ensuring that suspicious activities are detected and stopped before they escalate into threats. To simplify budgeting, Cyber Solutions provides a flat-rate cost structure that removes unforeseen IT expenses, offering peace of mind in one comprehensive package. This model enables organizations to manage their IT budgets more effectively, as they can foresee expenses without the concern of hidden charges or abrupt price hikes. By understanding these complexities, organizations can avoid costly pitfalls and ensure robust cybersecurity measures are in place.
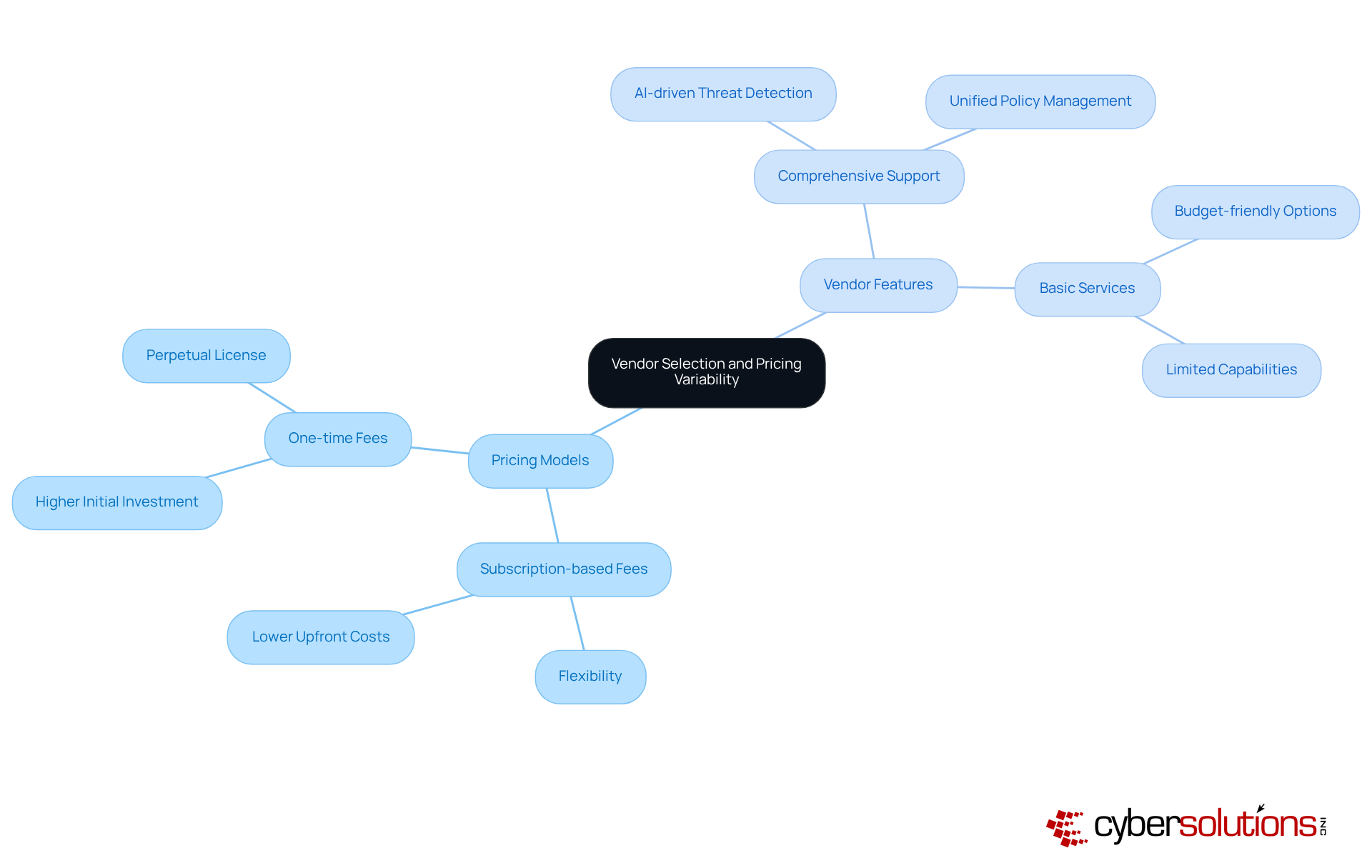
In the complex landscape of cybersecurity, selecting the right vendor is crucial for safeguarding healthcare organizations against evolving threats. Different vendors employ diverse pricing models for network firewall pricing that can significantly impact overall costs. Common models include:
The level of support and features included also varies widely among vendors. For instance, those providing comprehensive support and advanced features, such as AI-driven threat detection and unified policy management, typically reflect higher network firewall pricing. In contrast, vendors offering basic services may present a more budget-friendly option but could lack essential capabilities needed for robust security.
Executives need to carefully evaluate vendor options to ensure they align with security requirements and budget constraints. After all, the right vendor choice can mean the difference between robust security and vulnerability to costly breaches.
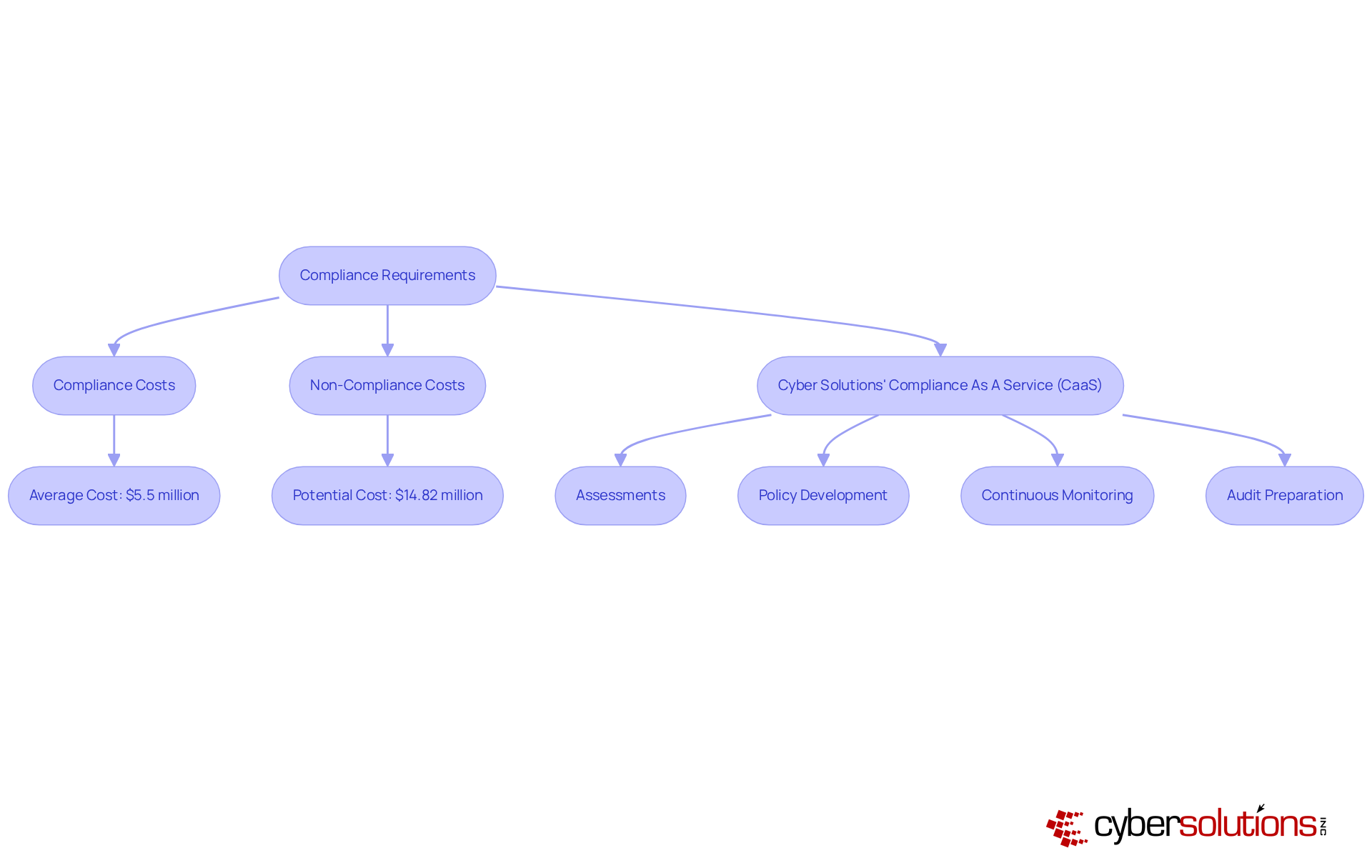
In the high-stakes world of healthcare, cybersecurity compliance isn't just a checkbox - it's a critical investment that can make or break an organization. Meeting stringent standards requires significant investment in advanced features like logging, monitoring, and reporting capabilities.
For instance, network firewall pricing can be impacted by the essential enhanced logging functionalities required for compliance, resulting in higher upfront and ongoing costs.
Cyber Solutions' Compliance As A Service (CaaS) offers businesses comprehensive services to fulfill these regulatory requirements, including:
Industry insights reveal that compliance costs can average $5.5 million, while non-compliance expenses can skyrocket to $14.82 million, highlighting the critical financial stakes.
Executives must thoughtfully evaluate these compliance-related expenses when planning for security measures to avoid unforeseen financial pressures and guarantee their organizations stay compliant and protected.
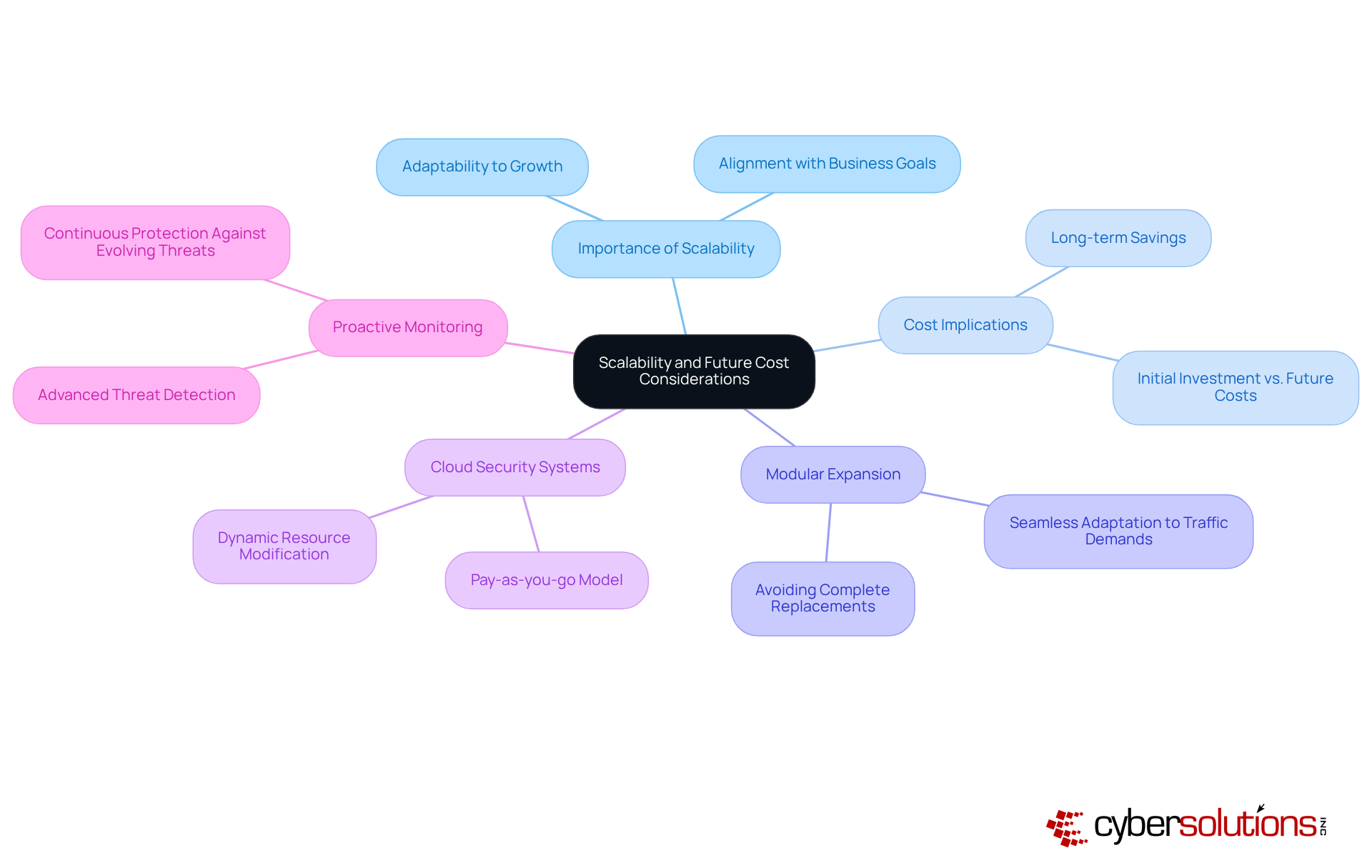
In an era where cybersecurity threats are escalating, the need for scalable security solutions in healthcare has never been more critical. Scalability is a crucial element in determining network firewall pricing, as organizations must consider their future growth when choosing a protection option. Scalable security systems might have higher initial costs. However, they can lead to significant long-term savings by minimizing the need for frequent upgrades.
For instance, security systems designed for modular expansion can seamlessly adapt to fluctuating traffic demands or a growing number of users, thus avoiding the costly process of complete replacements. With nearly 82% of organizations adopting next-generation security measures, how can executives ensure they prioritize scalability in their assessments? This trend underscores the growing importance of adaptable security solutions that align with long-term business goals and budget forecasts.
Additionally, Cyber Solutions provides cloud network security systems that offer scalability and elasticity, enabling organizations to dynamically modify resources according to traffic load, improving cost-effectiveness. The pay-as-you-go model for cloud security systems further supports this by ensuring that organizations only pay for the resources they use.
To protect investments and boost operational efficiency, executives need to think about scalability, future growth, and network firewall pricing when evaluating network security options. Furthermore, Cyber Solutions' proactive monitoring and advanced threat detection services ensure that businesses are protected against evolving cybersecurity threats, reinforcing the importance of scalability in decision-making.
As Martin L. Abbott noted, 'Management means measurement, and a failure to measure is a failure to manage.' Executives who overlook scalability may find themselves facing unexpected costs and vulnerabilities that could jeopardize their organizations.
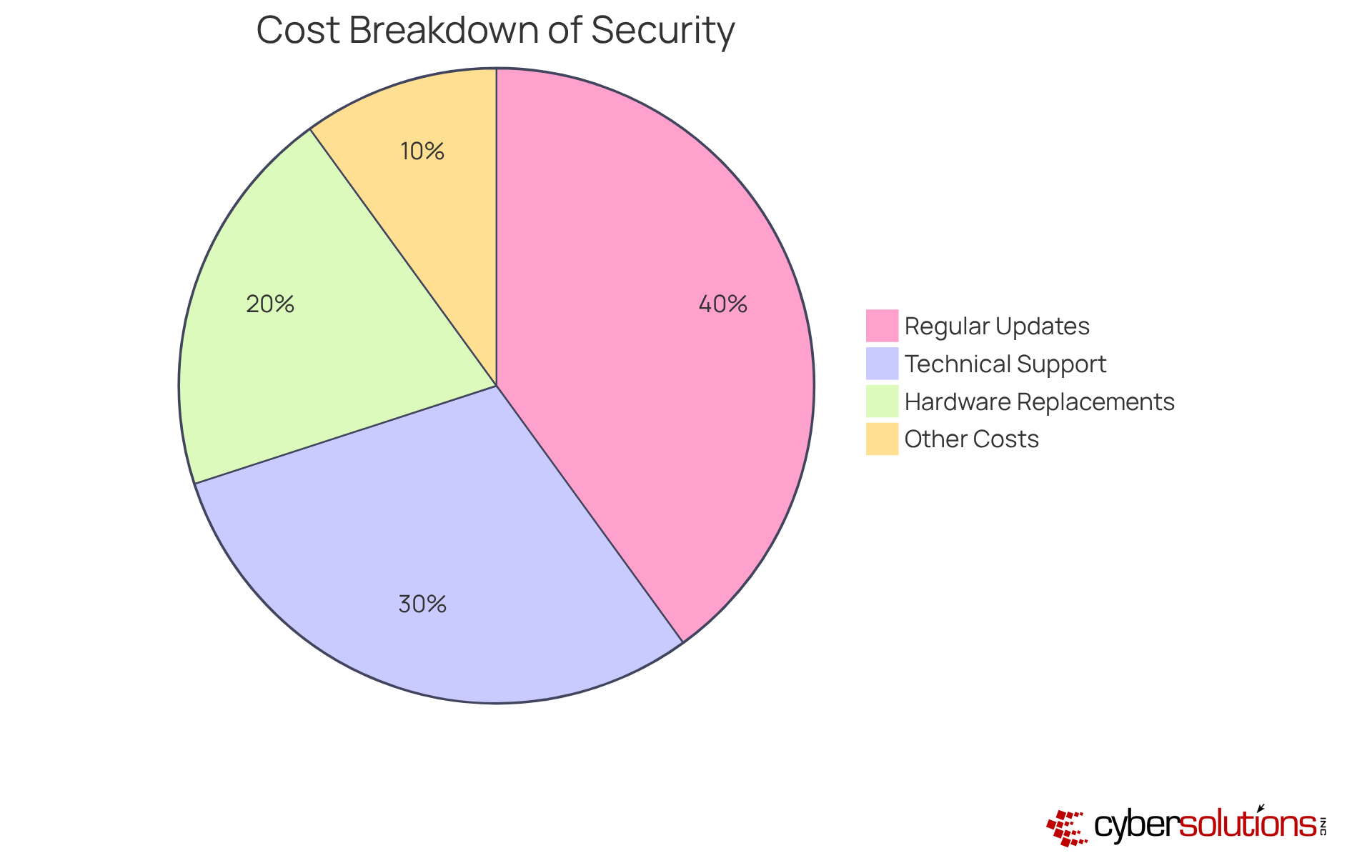
In an era where cybersecurity threats loom large, healthcare organizations must navigate the complexities of budgeting for effective security solutions. The total cost of a security solution, reflecting network firewall pricing, encompasses ongoing support and maintenance services, which can significantly impact overall expenses. Organizations need to plan for:
It's all part of the game. Managed security services typically charge a monthly fee that includes comprehensive support and maintenance, allowing for predictable budgeting. For instance, the network firewall pricing for ongoing maintenance and subscription fees can range from $100 to $1,000 annually, depending on the complexity of the system and the level of service required. In contrast, relying on in-house IT personnel can lead to fluctuating expenses, as costs vary based on the specific needs of the organization. Executives should assess the support alternatives available, taking into account both the expenses and the extent of coverage offered. Ultimately, a strategic approach to evaluating support options can safeguard both patient data and financial resources, ensuring long-term stability.
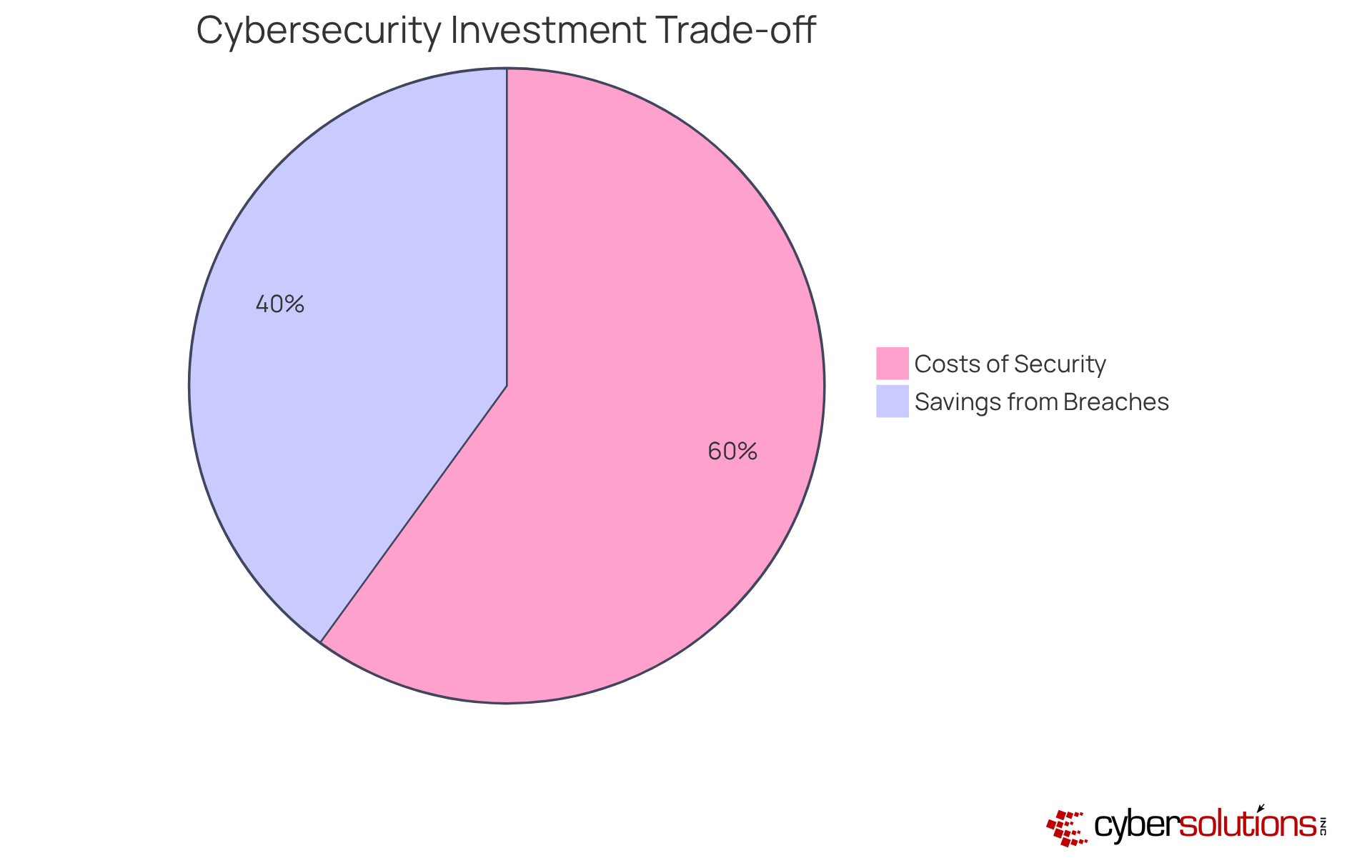
In an era where cyber threats loom large, healthcare organizations must prioritize robust cybersecurity measures to protect sensitive data and maintain trust. Investing in advanced security features like intrusion prevention systems (IPS) and threat detection can significantly boost protection. However, these enhancements often come with increased costs.
Consider this: a security system with built-in IPS may have a higher upfront cost, but it can save organizations significant amounts by preventing costly data breaches - averaging around $1.57 million in reputational damages alone. Organizations need to carefully weigh the risks of cyber threats against the costs of advanced security features to make informed investment decisions.
This strategic approach not only protects sensitive data but also aligns with long-term financial objectives, ensuring that cybersecurity investments deliver measurable returns.
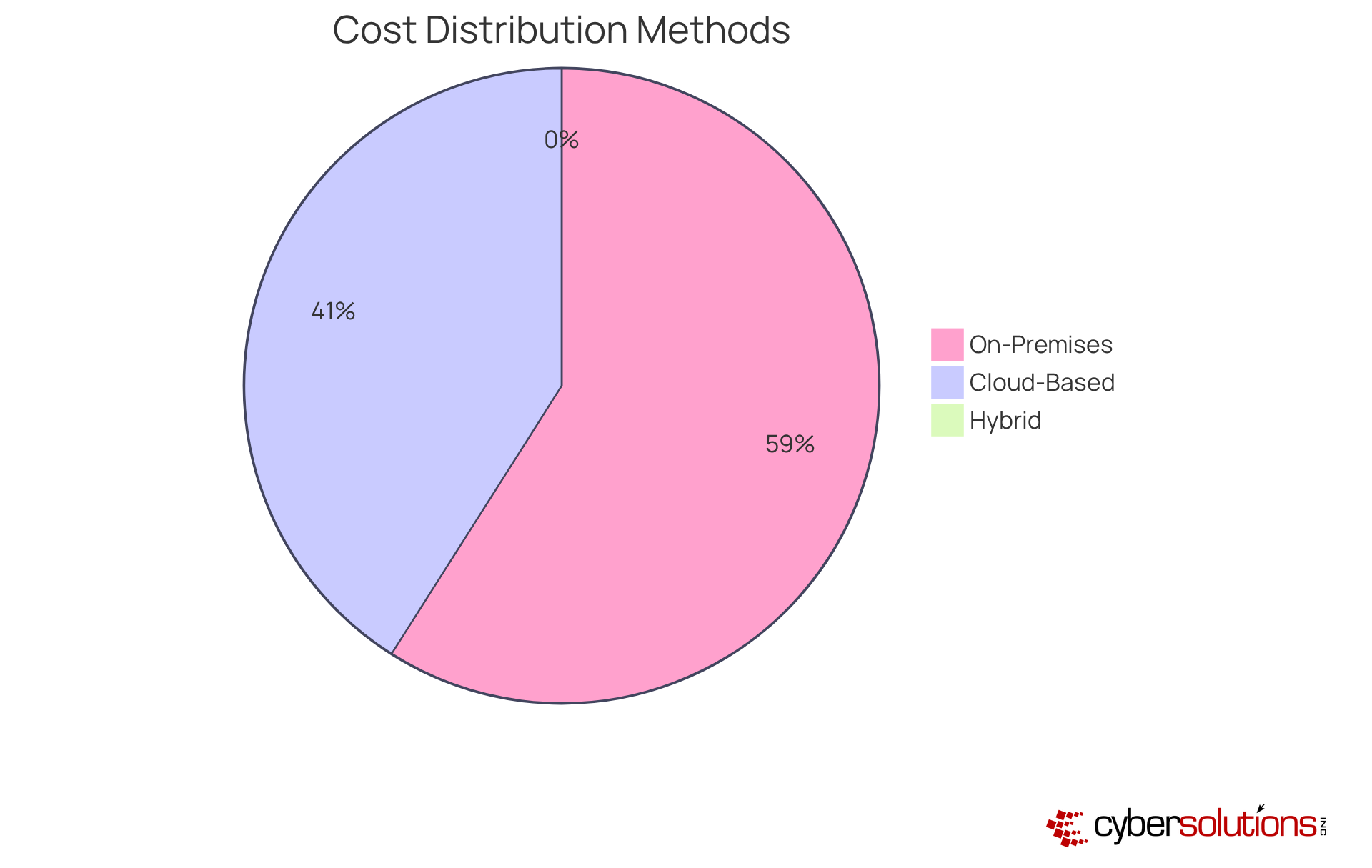
In an era where cybersecurity threats loom large, healthcare organizations must prioritize their security strategies to safeguard sensitive patient data and maintain trust. The choice of security system deployment - whether on-premises, cloud-based, or hybrid - significantly influences network firewall pricing.
When it comes to on-premises solutions, expect to make a hefty initial investment, with costs for hardware, installation, and ongoing maintenance potentially exceeding $522,000 over five years. On the flip side, cloud-based security systems often follow a subscription model, which reduces initial expenses but can lead to ongoing charges that accumulate over time. For instance, native cloud firewalls can offer 40-60% savings for basic protection needs, yet they may lack the advanced threat prevention capabilities essential for comprehensive security.
Hybrid approaches aim to strike a balance between the two models, providing flexibility but potentially complicating cost structures due to the need to manage both on-prem and cloud components. CFOs face the daunting challenge of navigating complex financial decisions that can impact their organization's security posture and budget, particularly in relation to network firewall pricing. Ultimately, the right choice in security system deployment can mean the difference between robust protection and costly breaches that threaten both finances and reputation.
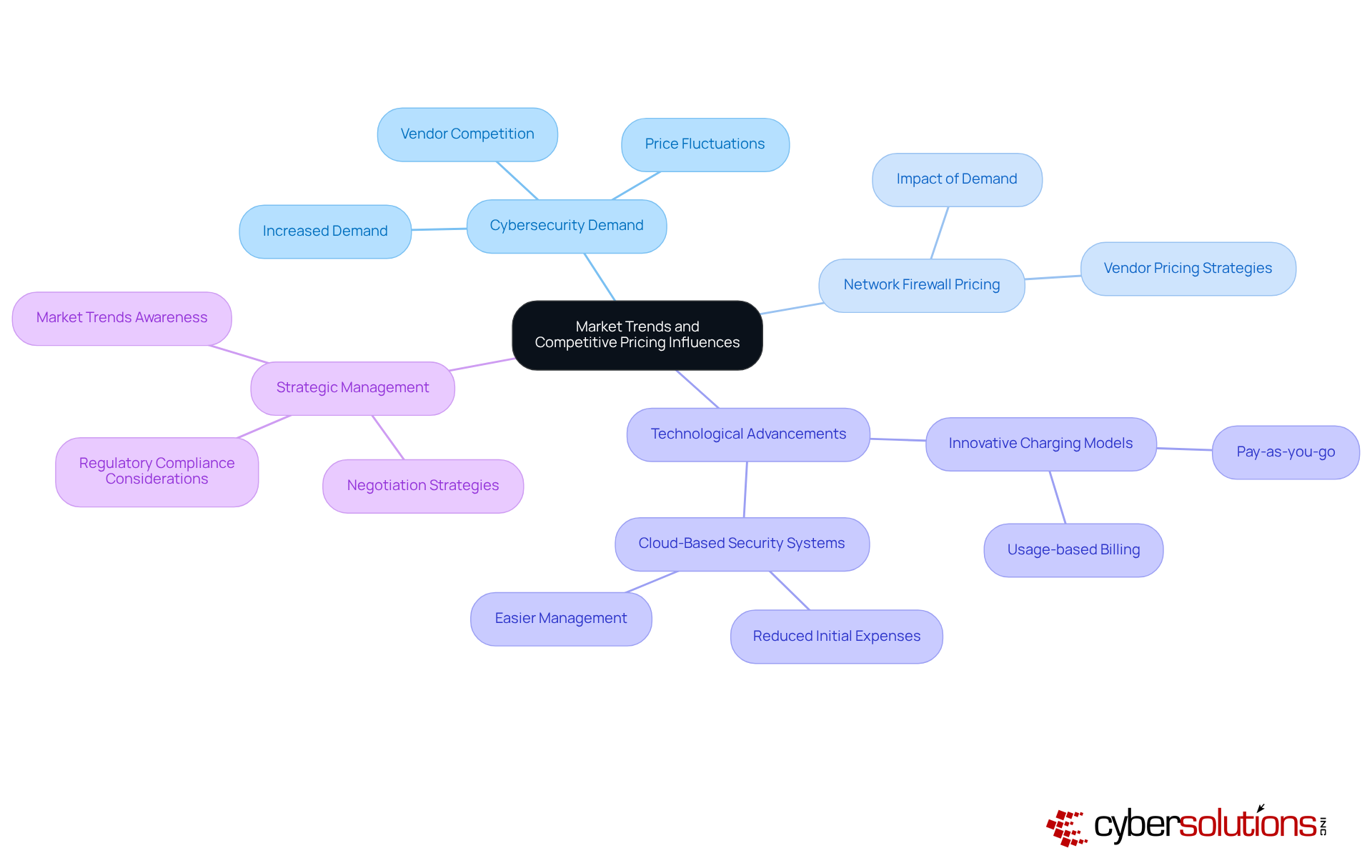
In an era where cyber threats loom larger than ever, the financial implications for healthcare organizations are profound and far-reaching. The increasing demand for cybersecurity solutions is causing an increase in network firewall pricing. As organizations prioritize robust security measures, the competition among vendors intensifies, potentially impacting network firewall pricing and leading to price fluctuations. The next-generation security system market is projected to increase from USD 5.0 billion in 2023 to USD 8.6 billion by 2028, reflecting this heightened demand.
Advancements in technology are paving the way for innovative charging models, such as pay-as-you-go and usage-based billing, which offer flexibility and economic efficiency. For instance, cloud-based security systems are gaining traction due to their reduced initial expenses and easier management, making them an appealing choice for numerous companies.
Executives must stay alert to these market trends. By staying informed, they can strategically manage their security investments and negotiate favorable network firewall pricing with vendors. Understanding the competitive landscape, including factors such as regulatory compliance and the need for advanced features like intrusion prevention and threat intelligence, is crucial for making informed decisions in this evolving market. Navigating this complex landscape requires vigilance and strategic foresight to safeguard both assets and patient trust.
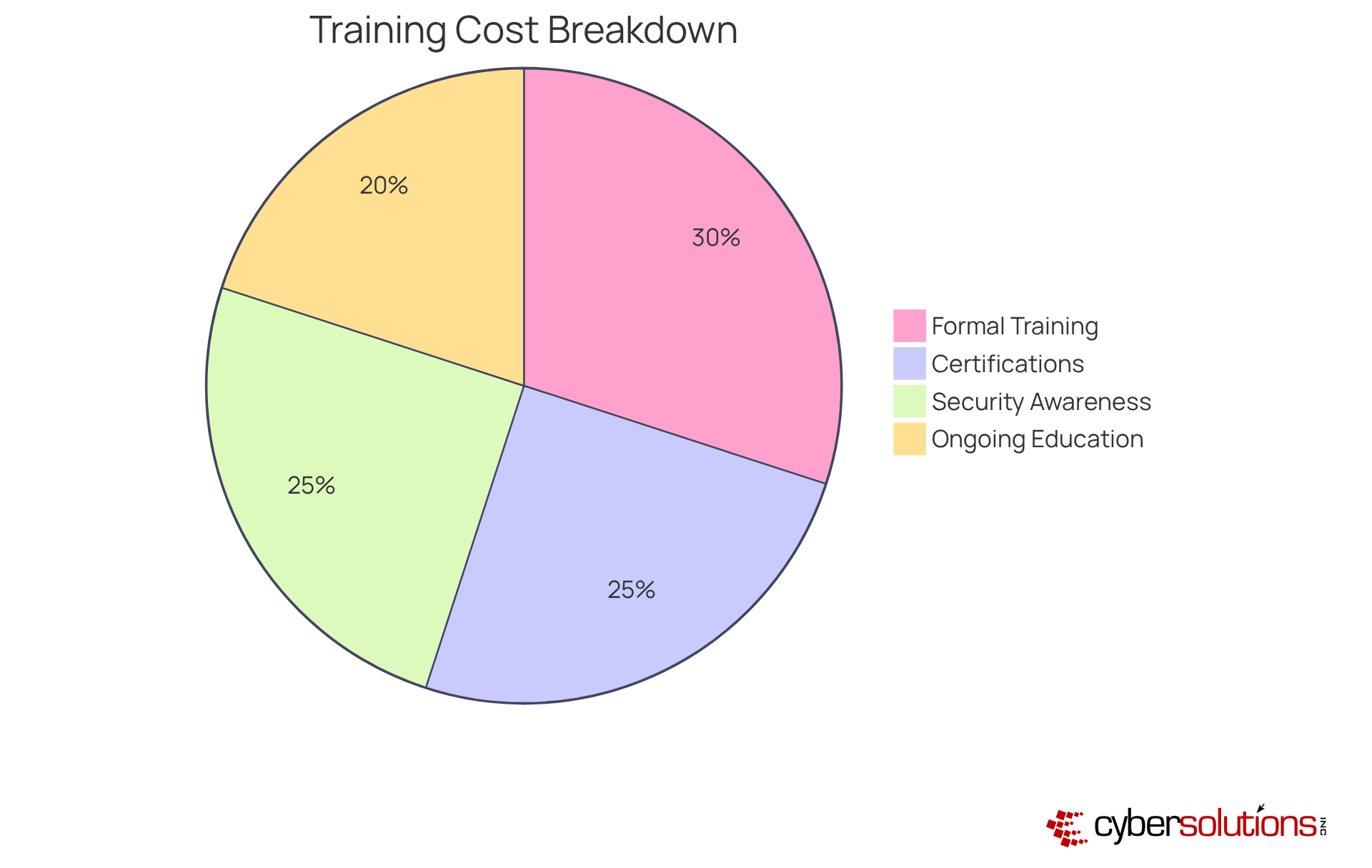
In an era where cybersecurity breaches can cost healthcare organizations millions, the importance of a well-trained workforce cannot be overstated. Efficient security system implementation requires extensive training for both IT personnel and end-users. It's crucial for organizations to budget for formal training programs, certifications, or ongoing education to ensure their teams are skilled in managing and operating network security systems. Training costs can fluctuate significantly, generally ranging from several hundred to several thousand dollars per individual, depending on the system's complexity and the necessary knowledge depth.
For instance, the average expense of cybersecurity breaches is approximately $4.88 million per incident. With human error accounting for a significant number of breaches, how can organizations ensure their teams are prepared? This underscores the financial necessity of well-trained personnel. Executives must include these training expenses in their budgeting for security measures to ensure successful implementation and continuous management.
A reasonable budget for Security Awareness Training is estimated at $12-$36 per user per year, with potential add-ons increasing costs by $0.20-$1.50+ per user per month. Investing in training not only mitigates these risks but also enhances overall security posture. Ultimately, the investment in training is not just a cost; it's a critical strategy for safeguarding the future of healthcare organizations against evolving cyber threats.
In an era where cyber threats loom large, healthcare organizations must prioritize robust cybersecurity measures to safeguard sensitive patient data. Tailored firewall options, such as those provided by Cyber Solutions, offer organizations customized security that aligns with their specific needs. These approaches incorporate essential features like application allowlisting, which proactively prevents malware and unauthorized software from executing. This not only enhances overall security effectiveness but also ensures compliance with regulations such as HIPAA and GDPR. Application allowlisting allows for centralized management and continuous monitoring of application activity, enabling immediate identification and blocking of threats.
While tailored solutions offer enhanced security, they often lead to network firewall pricing that can strain budgets due to higher costs. For instance, a tailored approach may incorporate extra features or specialized assistance that can raise expenses but also greatly improve security. However, the investment in tailored solutions can lead to significant long-term savings by preventing costly breaches. With a flat-rate pricing model, Cyber Solutions helps organizations manage network firewall pricing to avoid unexpected IT expenses, making budgeting straightforward and transparent. This enables executives to assess network firewall pricing of tailored solutions in relation to their specific security requirements and budget constraints to ensure they receive optimal value.

In today's healthcare landscape, the stakes of cybersecurity have never been higher, especially for CFOs navigating the intricate web of network firewall pricing. Understanding the complexities of this pricing is essential for executives as they face a myriad of challenges. Factors such as:
all contribute to the total cost of ownership. By assessing these elements, organizations can make informed decisions that align their security needs with budget constraints.
The article highlights critical insights, including:
Each factor not only influences pricing but also impacts the long-term effectiveness of cybersecurity measures. Moreover, training and education costs further emphasize the need for a well-prepared workforce to manage these systems effectively. This reinforces the notion that investments in security are investments in organizational resilience.
In a rapidly evolving threat landscape, executives must remain vigilant and proactive in their approach to cybersecurity. By prioritizing tailored solutions that meet specific needs while considering the broader implications of cost and security, organizations can safeguard their assets and maintain trust. Ultimately, the choices made today will determine not only the security posture of healthcare organizations but also their financial viability in the face of evolving threats.
How does configuration complexity impact network firewall pricing?
Configuration complexity significantly influences network firewall pricing, as more complex setups require additional resources for both initial setup and ongoing management, leading to higher costs.
What percentage of security rules in large enterprises are often outdated or redundant?
In large enterprises, 70-80% of security rules are often outdated or redundant, which can result in outages, decreased productivity, and increased administrative burdens.
What should executives consider regarding configuration complexity?
Executives should assess the long-term consequences of configuration complexity when reviewing security options, as it can lead to unforeseen financial challenges, including costs related to misconfigurations.
What does the total cost of ownership for firewalls include?
The total cost of ownership for firewalls encompasses both acquisition costs and ongoing management expenses.
How does Cyber Solutions help businesses with cybersecurity expenses?
Cyber Solutions offers a flat-rate cost structure for their services, which helps businesses manage their IT budgets effectively by removing unforeseen expenses and providing a comprehensive package.
What are the different pricing models used by cybersecurity vendors?
Common pricing models include subscription-based fees, which offer flexibility and lower upfront costs, and one-time fees for perpetual licenses, which may require higher initial investments.
How do vendor features and support levels affect pricing?
Vendors that provide comprehensive support and advanced features, such as AI-driven threat detection, typically have higher network firewall pricing compared to those offering basic services.
Why is cybersecurity compliance important for healthcare organizations?
Cybersecurity compliance is critical for healthcare organizations as it requires significant investment in features like logging, monitoring, and reporting, which can impact network firewall pricing.
What services does Cyber Solutions' Compliance As A Service (CaaS) offer?
Cyber Solutions' CaaS includes assessments, policy development, continuous monitoring, and audit preparation to help businesses meet regulatory compliance requirements.
What are the financial implications of compliance and non-compliance?
Compliance costs can average $5.5 million, whereas non-compliance expenses can soar to $14.82 million, underscoring the financial stakes involved in maintaining compliance.