
In an era where cyber threats are not just a possibility but a reality, the healthcare sector must prioritize the protection of sensitive information. CFOs are confronted with the daunting task of navigating the complexities of Cybersecurity Maturity Model Certification (CMMC) documentation, a challenge that demands both strategic insight and operational diligence.
This article explores five essential steps that guide organizations through the documentation process while highlighting the strategic advantages of robust cybersecurity practices.
How can healthcare entities not only meet regulatory compliance but also stay ahead of the ever-evolving nature of cyber threats? Exploring these steps reveals the proactive measures necessary for achieving compliance success and fortifying defenses against potential breaches.
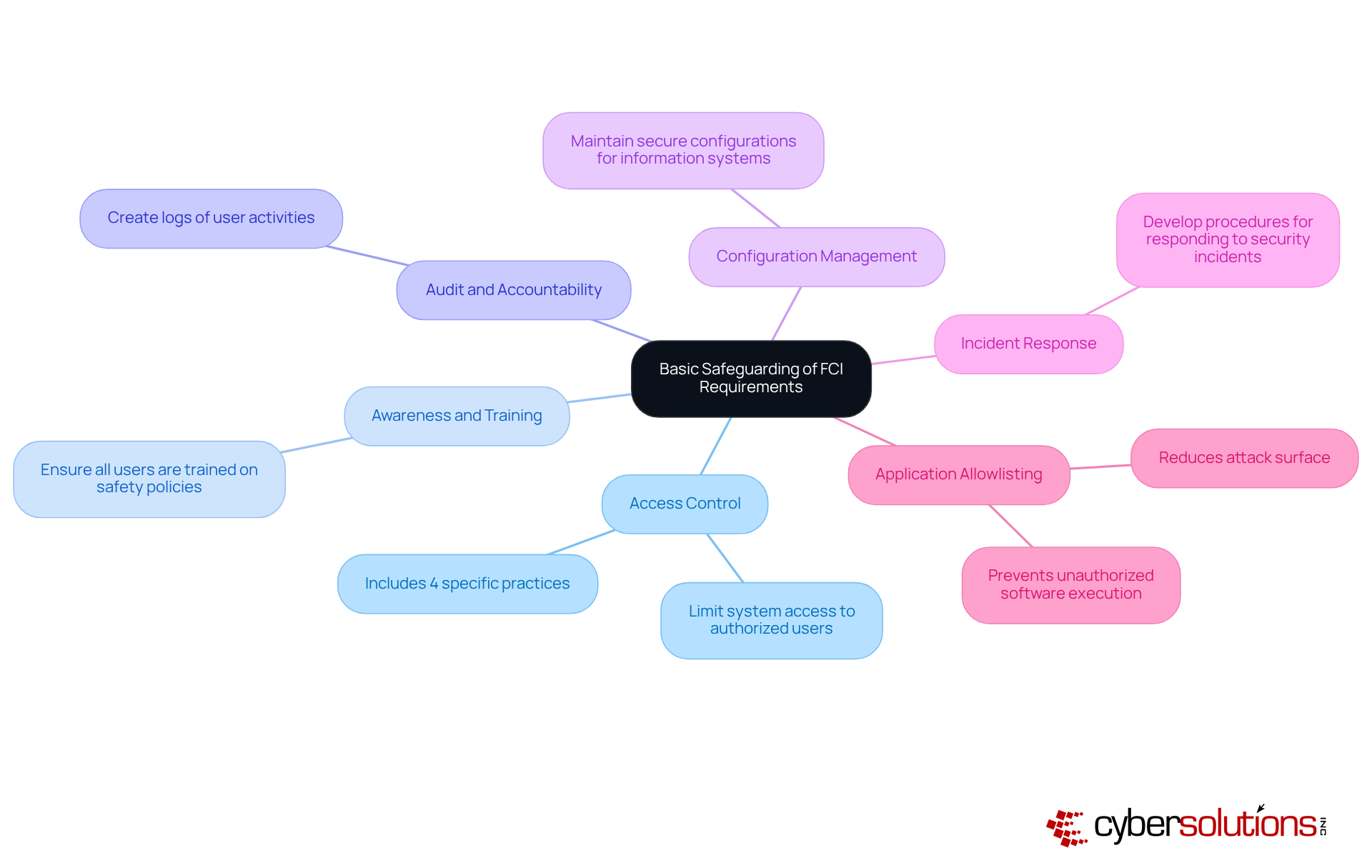
In an era where cyber threats loom large, the safeguarding of Federal Contract Information (FCI) has never been more critical for healthcare organizations. According to CMMC documentation, Level 1 focuses on the basic safeguarding of FCI, requiring organizations to implement 17 specific protective measures as outlined in FAR clause 52.204-21. These controls include:
In addition to these foundational practices, application allowlisting plays a crucial role in protecting sensitive information from unauthorized access. By ensuring that only pre-approved and trusted software can execute, application allowlisting proactively prevents malware and unauthorized applications from running. This approach not only reduces the attack surface but also helps organizations comply with the stringent cybersecurity standards detailed in the CMMC documentation, which are necessary for maintaining eligibility for lucrative government contracts.
Without these measures, organizations risk losing access to critical government contracts and facing severe penalties. Implementing these foundational practices is not just a regulatory requirement; it’s a strategic imperative for securing the future of your organization in a competitive landscape.
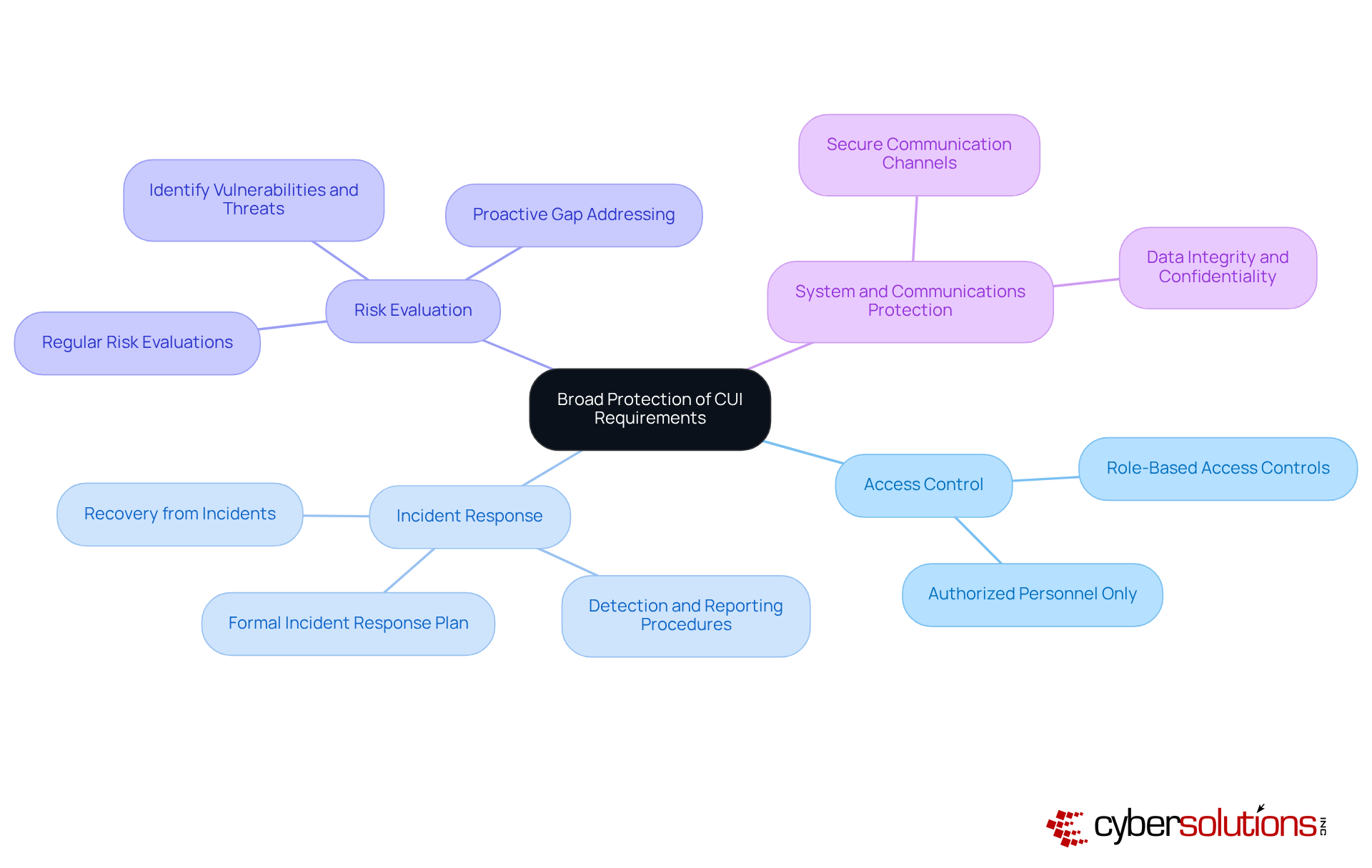
In an era where cyber threats loom larger than ever, the healthcare sector must prioritize cybersecurity and refer to CMMC documentation to protect sensitive patient information, including the 110 protective measures outlined in CMMC Level 2 derived from NIST SP 800-171. These measures are specifically aimed at safeguarding Controlled Unclassified Information (CUI) and include:
These measures are crucial for improving the safety stance of entities that handle sensitive information. Without these protective measures, organizations not only jeopardize their compliance but also expose themselves to devastating breaches that could compromise patient trust.
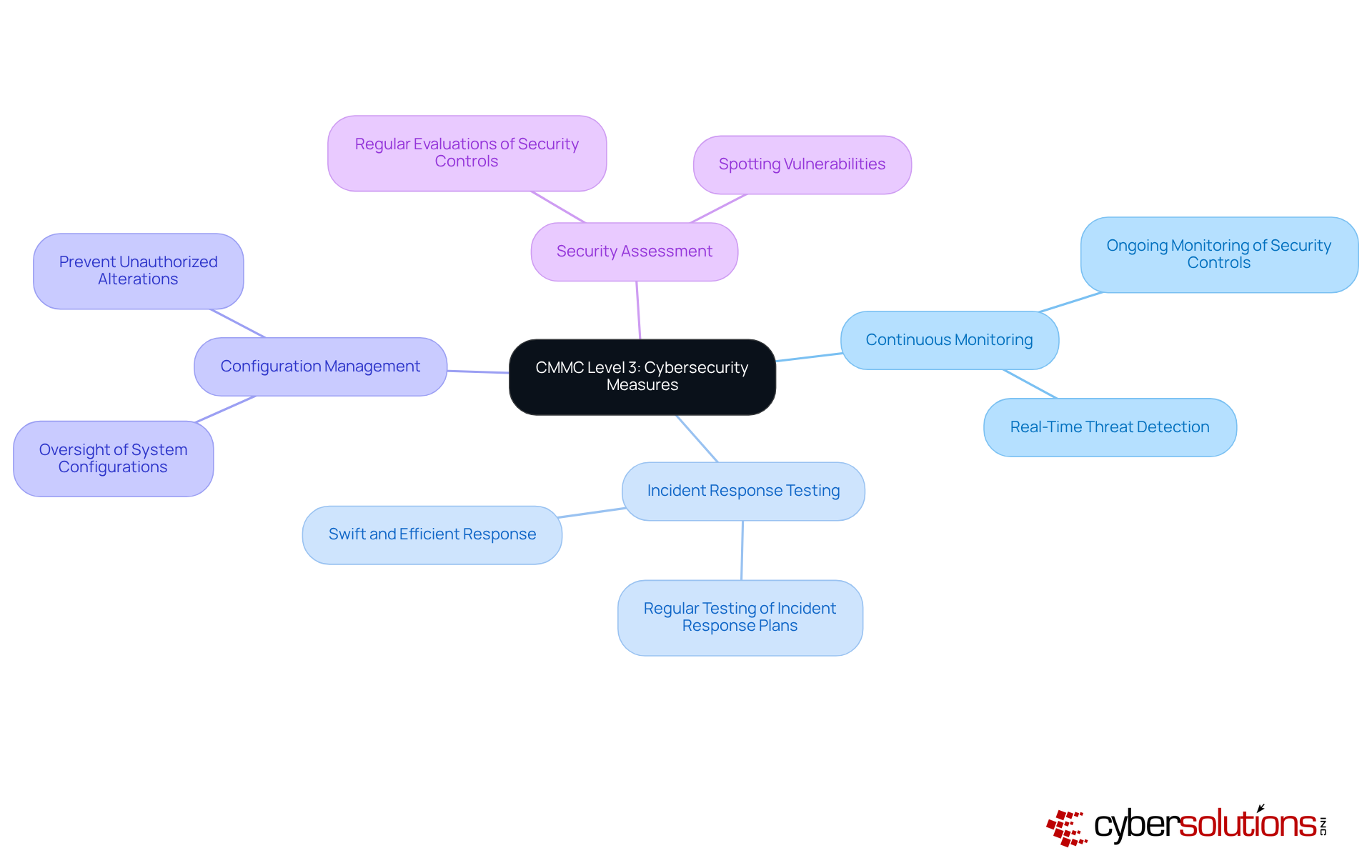
In an era where cyber threats are increasingly sophisticated, the healthcare sector must prioritize cybersecurity to protect sensitive patient information and maintain trust. CMMC Level 3 requires entities to implement enhanced protective measures to safeguard Controlled Unclassified Information (CUI) from complex threats. To achieve compliance, organizations must diligently follow all 110 controls specified in NIST SP 800-171, ensuring robust protection against threats. This compliance is not just a checkbox; it’s a commitment to security that can make or break an organization’s reputation.
Key requirements include:
These advanced measures are essential for entities responsible for protecting sensitive information against the constantly changing environment of cyber threats. With cyber threats evolving daily, how can organizations ensure they are truly protected? Ongoing supervision not only enhances cybersecurity efficiency but also corresponds with the regulatory standards established by the Department of Defense, ensuring that entities remain robust against rising threats. Without these advanced measures, organizations risk not only their data but also their reputation and operational integrity in a landscape fraught with cyber challenges.
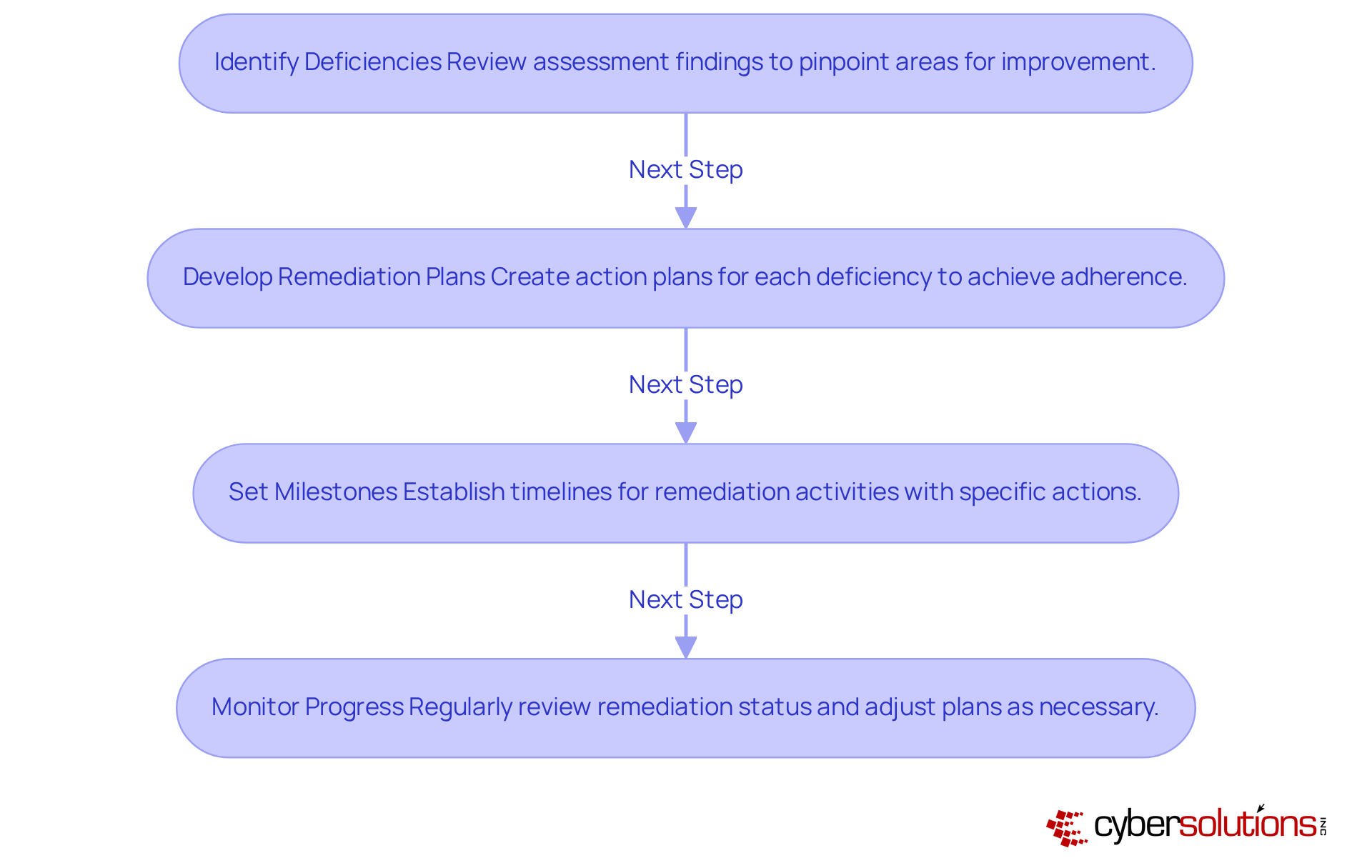
In an era where cyber threats loom large, the healthcare sector must prioritize robust cybersecurity measures to safeguard sensitive patient data and maintain trust. After a CMMC assessment, organizations must create CMMC documentation, specifically a Plan of Action and Milestones (POA&M), to effectively address identified deficiencies. This process involves several critical steps:
To truly strengthen their cybersecurity posture, organizations must take effective steps after an assessment to address regulatory gaps identified in the CMMC documentation. Did you know that organizations often spend 6 to 12 months preparing for a Level 2 audit? This highlights just how crucial timely and structured remediation efforts are. By following these best practices, entities can greatly enhance their preparedness for regulations and resilience against threats. Without a proactive approach to remediation, organizations risk not only regulatory penalties but also the integrity of their operations and patient trust.
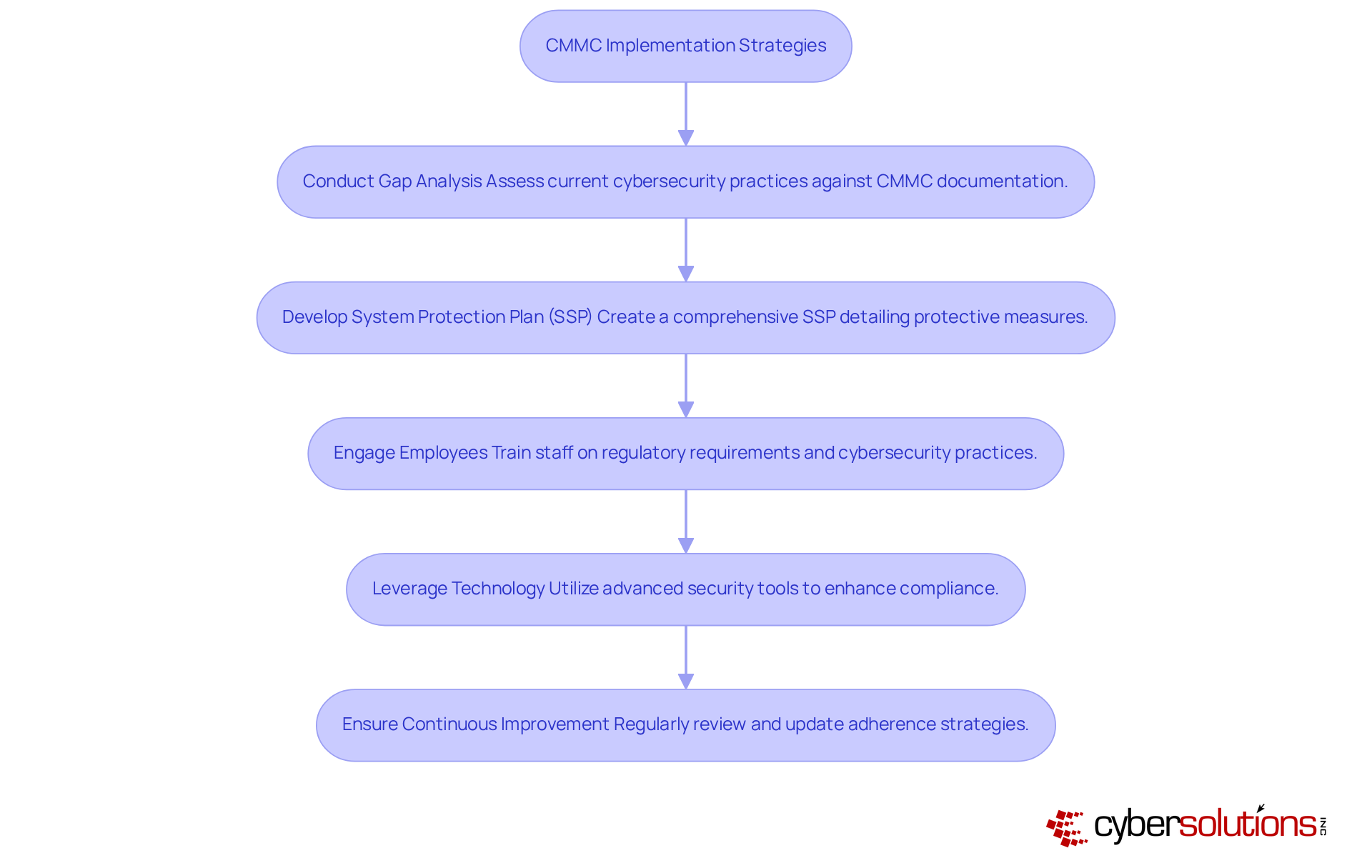
In an era where cyber threats loom larger than ever, the healthcare sector must prioritize robust cybersecurity measures to safeguard sensitive patient data and maintain trust. Conducting a gap analysis is a crucial first step in preparing the CMMC documentation. Organizations should assess their current cybersecurity practices against CMMC documentation to identify specific areas needing improvement. Notably, many organizations face significant challenges in accurately assessing their cybersecurity compliance, often leading to costly missteps, with an average discrepancy of 133 points between self-assessed scores and actual evaluations. By involving all stakeholders early, organizations can bridge the gap between perceived and actual compliance, ensuring a more robust cybersecurity framework.
Developing a comprehensive System Protection Plan (SSP) is essential for CMMC documentation that details how protective measures will be implemented and maintained. CMMC documentation mandates an SSP that details the execution of 110 protective measures for Level 2. Organizations must ensure that their CMMC documentation includes an SSP that reflects their current protective stance and is regularly updated to accommodate changes in systems and controls.
Engaging employees is another critical aspect. Training staff on regulatory requirements and the significance of cybersecurity practices fosters a culture of safety and ensures that everyone is aligned with the organization's regulatory objectives. A thorough understanding among staff promotes vigilance and accountability.
Leveraging technology can also play a pivotal role. Utilizing advanced security tools and solutions automates regulatory processes and enhances security measures. Organizations should document how these technologies are configured and managed to meet control objectives, including monitoring and review processes.
Finally, continuous improvement is vital. Regularly reviewing and updating adherence strategies helps organizations adapt to changing regulations and emerging threats. Implementing procedures for continuous monitoring and maintenance of security measures, including risk assessments and internal audits, ensures ongoing adherence and resilience against cyber threats.
As CMMC enforcement approaches, organizations that proactively enhance their cybersecurity strategies will not only comply but also fortify their defenses against evolving threats.
In an era where cyber threats loom large, healthcare organizations must prioritize CMMC compliance to protect sensitive data and secure their future. Implementing CMMC documentation is essential for healthcare organizations aiming to secure sensitive data and maintain government contract eligibility. Adhering to the CMMC framework's structured guidelines allows organizations to build a strong cybersecurity posture. This not only meets compliance requirements but also boosts operational integrity.
Key steps for achieving compliance success include:
From establishing basic safeguarding practices at Level 1 to implementing advanced strategies at Level 3, each step is critical for mitigating cyber threats and ensuring a secure environment. Additionally, the necessity of post-assessment remediation and continuous improvement highlights the ongoing commitment required to uphold compliance.
CMMC compliance is more than just following rules; it's about actively protecting sensitive information from ever-evolving cyber threats. Organizations are encouraged to take decisive action by leveraging technology, engaging employees, and continuously refining their cybersecurity strategies. By embracing CMMC compliance, organizations not only shield their data but also position themselves as trustworthy stewards of patient information in a volatile digital landscape.
What is the focus of Level 1 in safeguarding Federal Contract Information (FCI)?
Level 1 focuses on the basic safeguarding of FCI, requiring organizations to implement 17 specific protective measures as outlined in FAR clause 52.204-21.
What are some of the protective measures required at Level 1?
Some of the protective measures include Access Control, Awareness and Training, Audit and Accountability, Configuration Management, and Incident Response.
What role does application allowlisting play in safeguarding FCI?
Application allowlisting ensures that only pre-approved and trusted software can execute, preventing malware and unauthorized applications from running and reducing the attack surface.
Why is it important for organizations to implement Level 1 safeguards?
Implementing Level 1 safeguards is crucial to maintain eligibility for government contracts and to avoid severe penalties, making it a strategic imperative for securing the organization's future.
What does Level 2 in the CMMC documentation focus on?
Level 2 focuses on the broad protection of Controlled Unclassified Information (CUI), requiring organizations to implement 110 protective measures derived from NIST SP 800-171.
What are some of the key protective measures at Level 2?
Key protective measures include Access Control with role-based restrictions, a formal Incident Response plan, regular Risk Evaluation, and System and Communications Protection for secure data transmission.
Why are the protective measures in Level 2 important for healthcare organizations?
These measures are crucial for improving the safety stance of organizations handling sensitive patient information and for preventing compliance issues and potential breaches that could compromise patient trust.