Introduction
In an era where cyber threats are not just a possibility but a reality, effective firewall testing is essential for safeguarding sensitive data in healthcare organizations. Organizations stand to gain not only enhanced security but also compliance with regulatory standards and significant cost savings by implementing robust testing methodologies.
With cyber threats evolving rapidly, many organizations struggle to keep pace with necessary security measures. How can businesses ensure they are adequately protected against potential breaches? Failing to implement robust firewall testing can lead to devastating financial and reputational damage, making it crucial for organizations to adopt best practices that fortify their defenses.
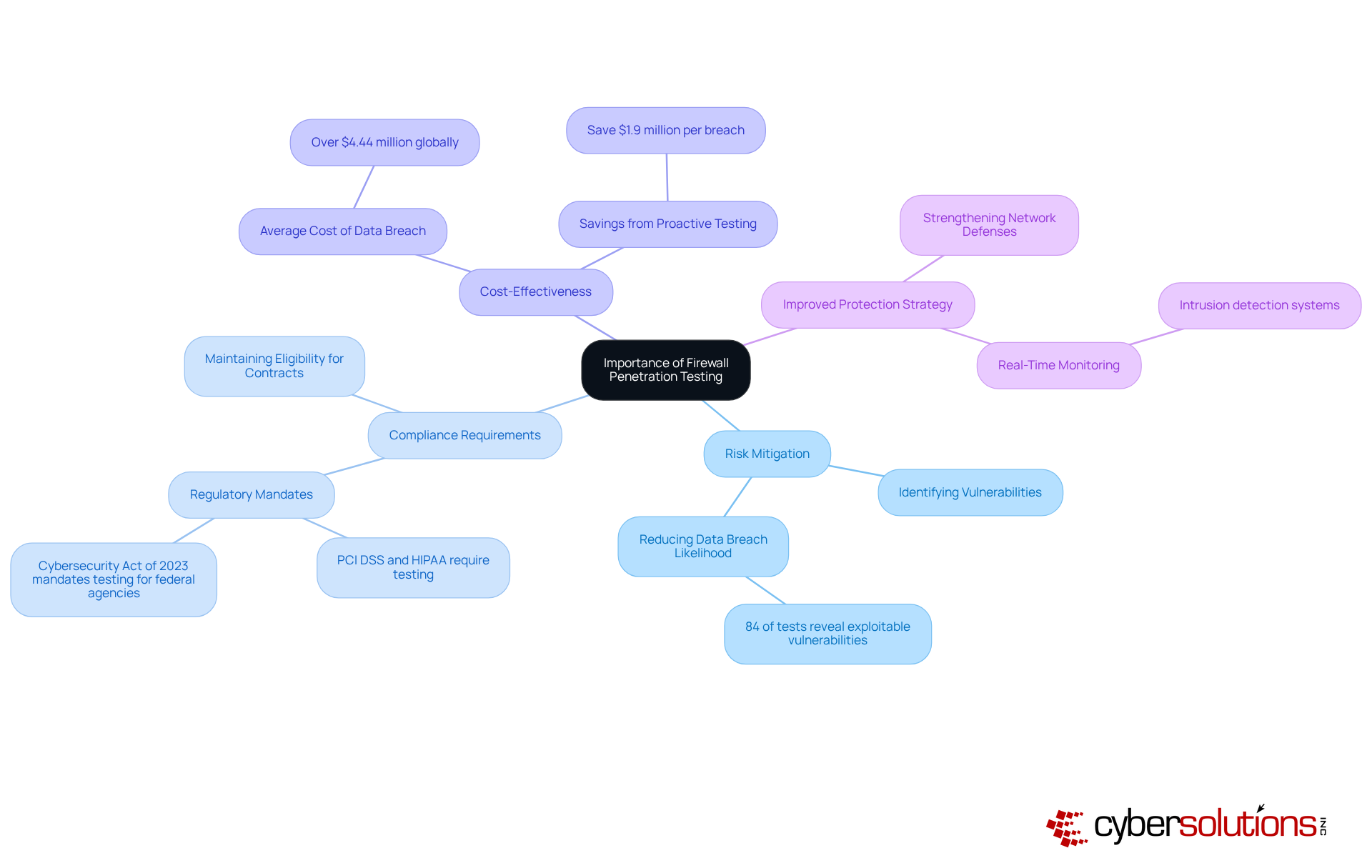
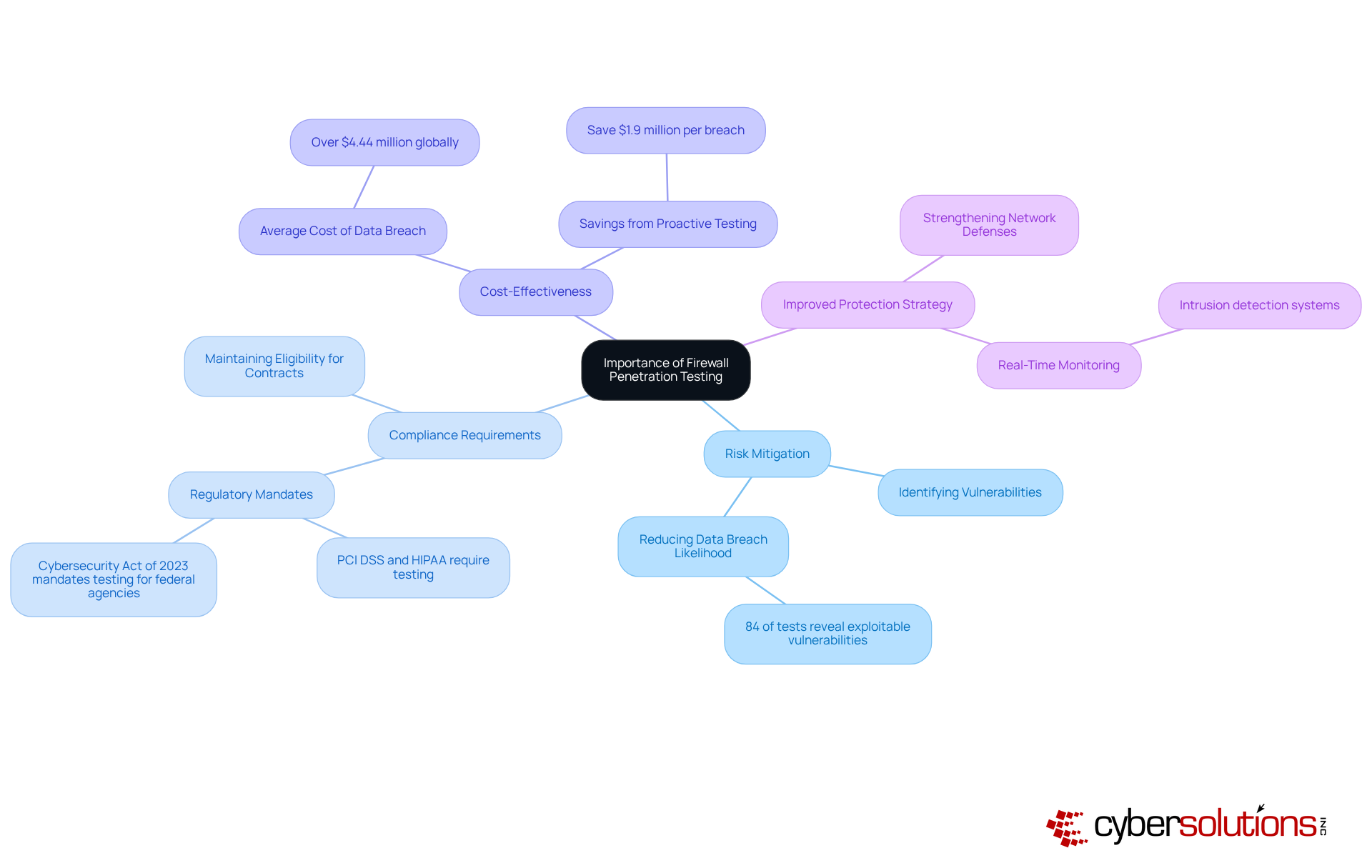
Understand the Importance of Firewall Penetration Testing
In an era where cyber threats are increasingly sophisticated, the importance of robust firewall testing cannot be overstated. Firewall testing is a proactive approach aimed at discovering weaknesses within a network's firewall setup. Simulating real-world attacks helps companies find weaknesses that cybercriminals could exploit. This practice is essential for several reasons:
- Risk Mitigation: Regular penetration testing allows organizations to detect and address weaknesses before they can be exploited, significantly lowering the likelihood of data breaches. Industry data indicates that at least one exploitable vulnerability exists in 84% of all penetration testing engagements. With such a high percentage of vulnerabilities, how can organizations afford to ignore penetration testing? Cyber Solutions offers advanced threat detection and proactive monitoring to ensure that your network remains protected against evolving threats.
- Compliance Requirements: Numerous regulatory frameworks, including PCI DSS and HIPAA, mandate regular assessments of safety, such as penetration testing, to ensure adherence and protect sensitive information. The Cybersecurity Act of 2023 further emphasizes the necessity for federal agencies to conduct these tests on high-value assets. Cyber Solutions ensures that your systems meet stringent cybersecurity standards, helping maintain eligibility for lucrative government contracts and compliance with regulatory requirements.
- Cost-Effectiveness: Investing in penetration testing can save organizations from the substantial financial repercussions of a data breach, which can average over $4.44 million globally. Organizations that perform proactive testing save an average of $1.9 million per breach compared to those that do not. Can your organization really afford to skip penetration testing and risk devastating financial losses? By utilizing Cyber Solutions' extensive protective measures and network defense services, businesses can improve their defense stance and decrease potential expenses related to breaches.
- Improved Protection Strategy: By comprehending weaknesses in their network configurations, entities can bolster their overall protection strategy, making it more difficult for attackers to obtain unauthorized access. Cyber Solutions' intrusion detection and prevention systems monitor network traffic in real-time, identifying and blocking suspicious activity before it can harm your business. Additionally, our secure remote access solutions ensure that sensitive company data is protected, even when accessed from outside the office.
Incorporating these insights into a cybersecurity strategy not only enhances security but also aligns with financial prudence, ensuring that resources are allocated effectively to mitigate risks. Ignoring these proactive measures could leave your organization vulnerable to attacks that could cost millions and compromise sensitive data.
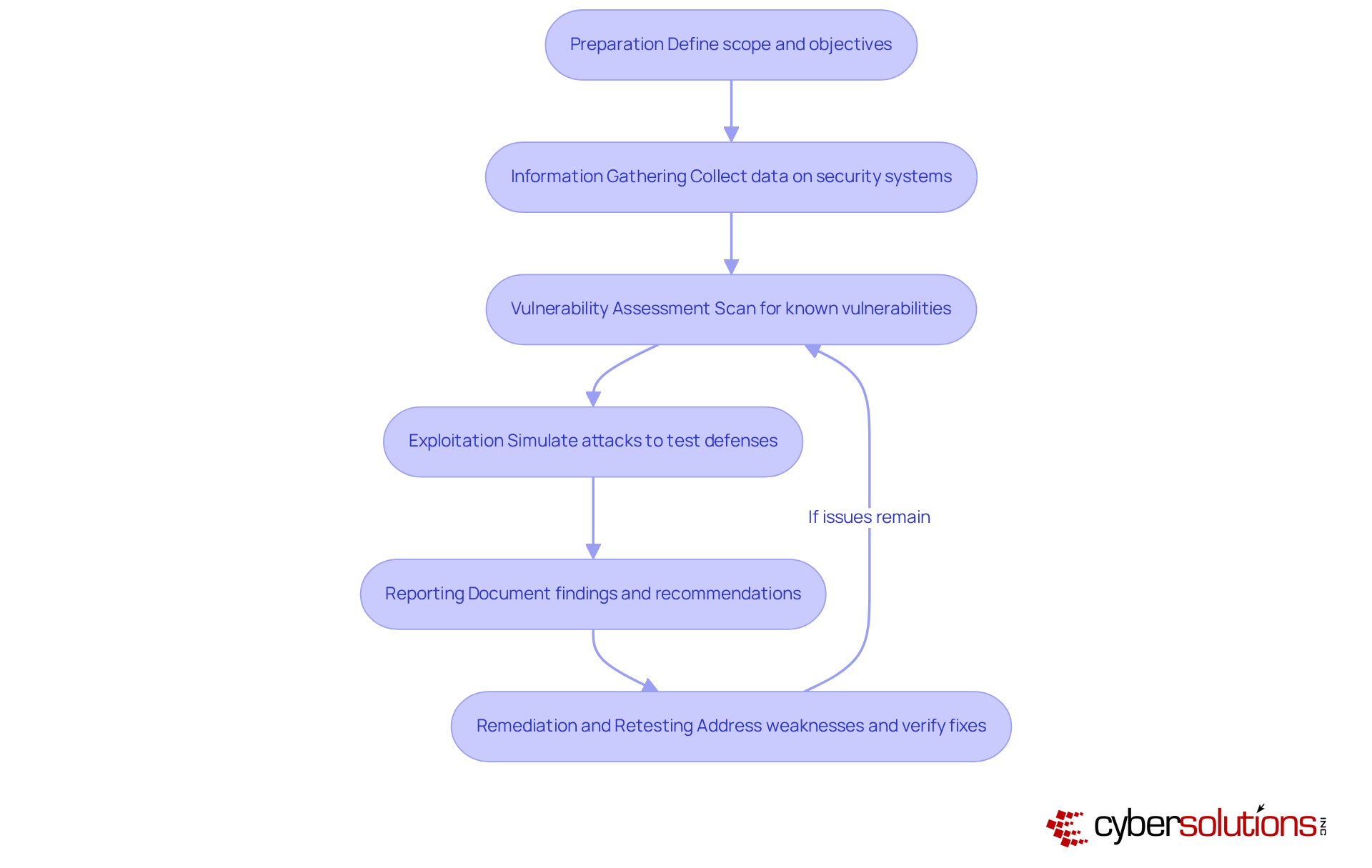
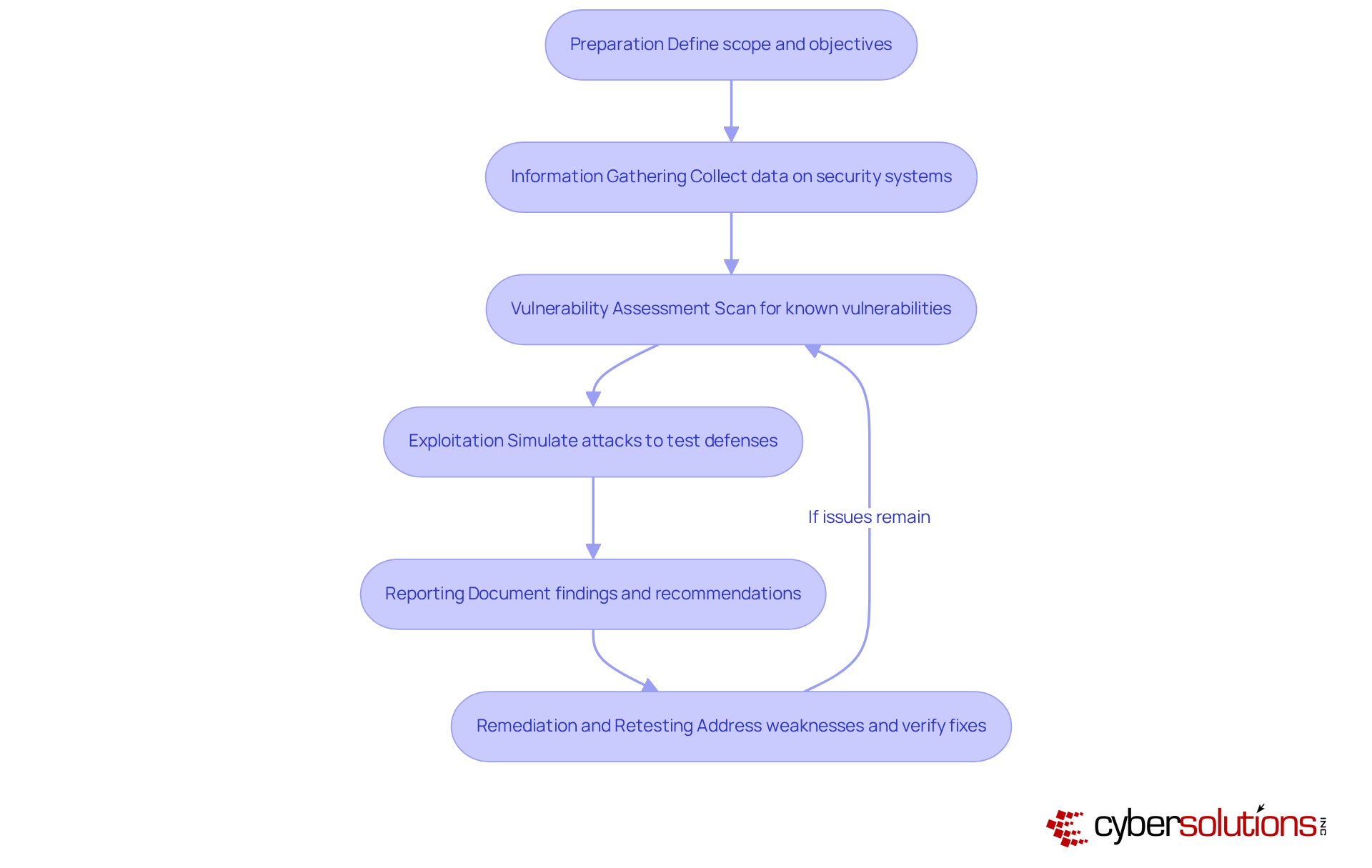
Implement a Structured Methodology for Firewall Testing
In an era where cyber threats loom larger than ever, the integrity of healthcare data relies heavily on effective firewall testing. To effectively test firewalls, organizations should adopt a structured methodology that encompasses the following steps:
- Preparation: Clearly define the scope of testing, specifying which network security devices will be assessed and the objectives of the test. This alignment ensures all stakeholders understand the goals and expectations.
- Information Gathering: Collect comprehensive data regarding the security system configuration, including rulesets, access controls, and network architecture. This essential information helps in recognizing possible weaknesses.
- Vulnerability Assessment: Utilize automated tools to scan for known vulnerabilities within the network security settings. This step is crucial for uncovering weaknesses that could be exploited by attackers.
- Exploitation: Simulate attacks to assess the defenses of the security system, including attempts to bypass rules or exploit misconfigurations. This phase involves firewall testing to assess its resilience against real-world threats.
- Reporting: Document findings meticulously, detailing identified weaknesses, the methods used for exploitation, and recommendations for remediation. This report ought to be distributed to pertinent stakeholders to inform future safety strategies.
- Remediation and Retesting: After addressing weaknesses, conduct retesting to verify the effectiveness of the fixes and ensure no new issues have been introduced.
Implementing this structured approach not only fortifies defenses but also instills confidence in stakeholders regarding the organization's security posture. Routine assessments are recommended, especially when modifications occur in network structure or access control lists, as it aids in detecting new weaknesses before they can be exploited.
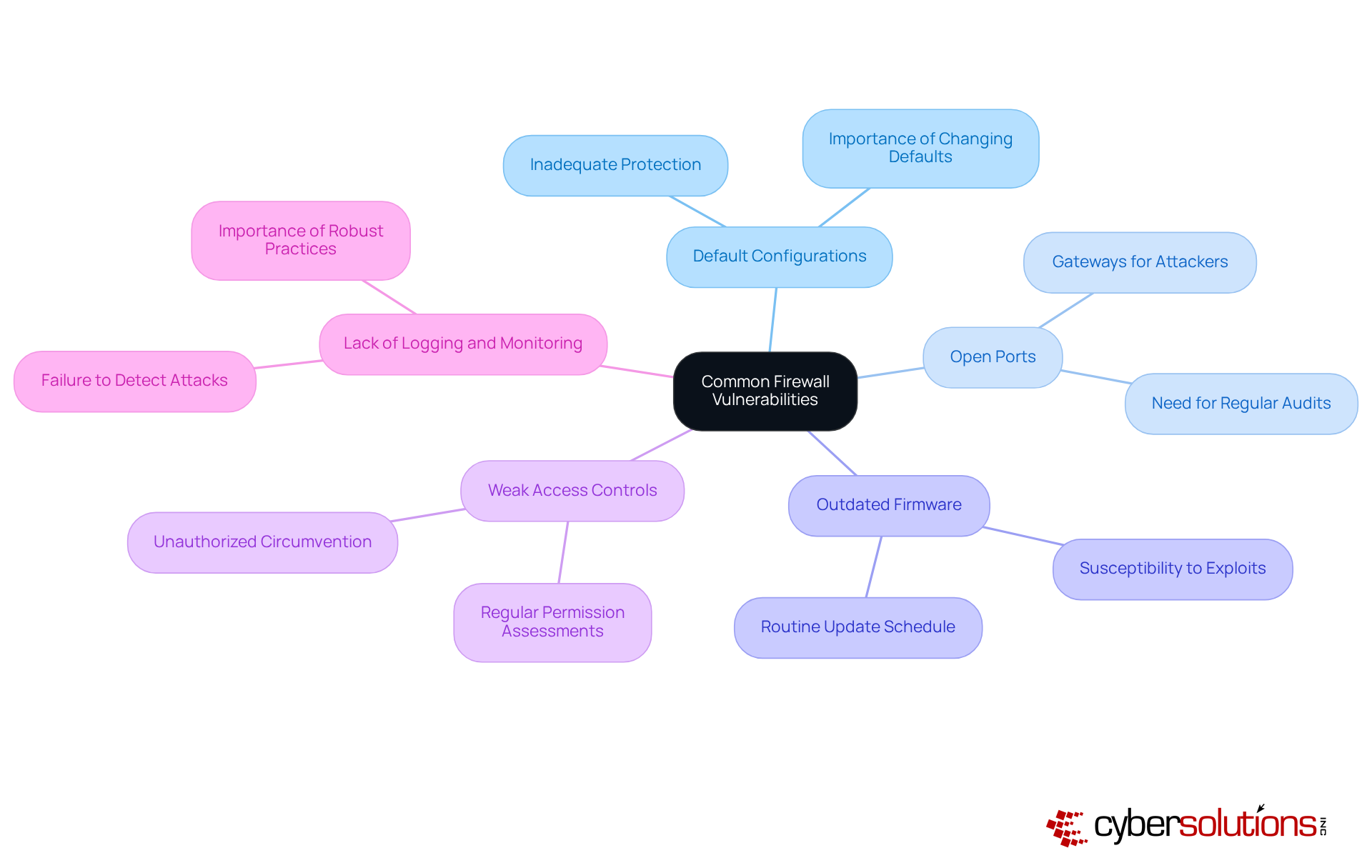
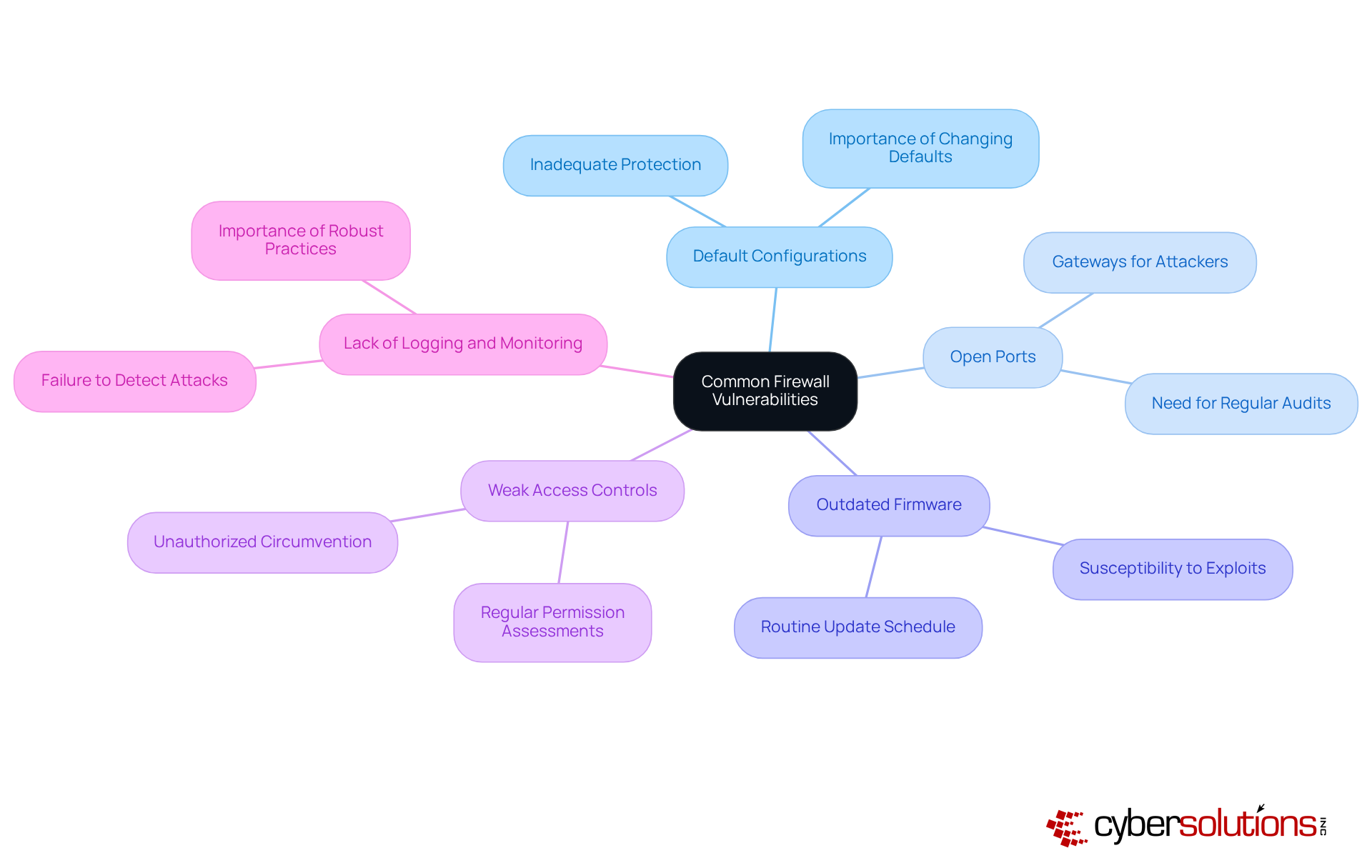
Identify and Address Common Vulnerabilities in Firewalls
In an era where cyber threats loom large, the integrity of healthcare networks hangs in the balance, making robust cybersecurity measures more critical than ever. Firewalls are essential for protecting network integrity, but firewall testing is necessary to identify weaknesses that could expose organizations to considerable dangers. Key vulnerabilities include:
These vulnerabilities can lead to devastating breaches, compromising sensitive patient data and financial stability. By addressing these vulnerabilities, organizations can not only enhance their security posture but also build trust with patients and stakeholders. Ignoring these vulnerabilities could lead to catastrophic breaches, but proactive measures can safeguard not just data, but the very trust patients place in healthcare systems.
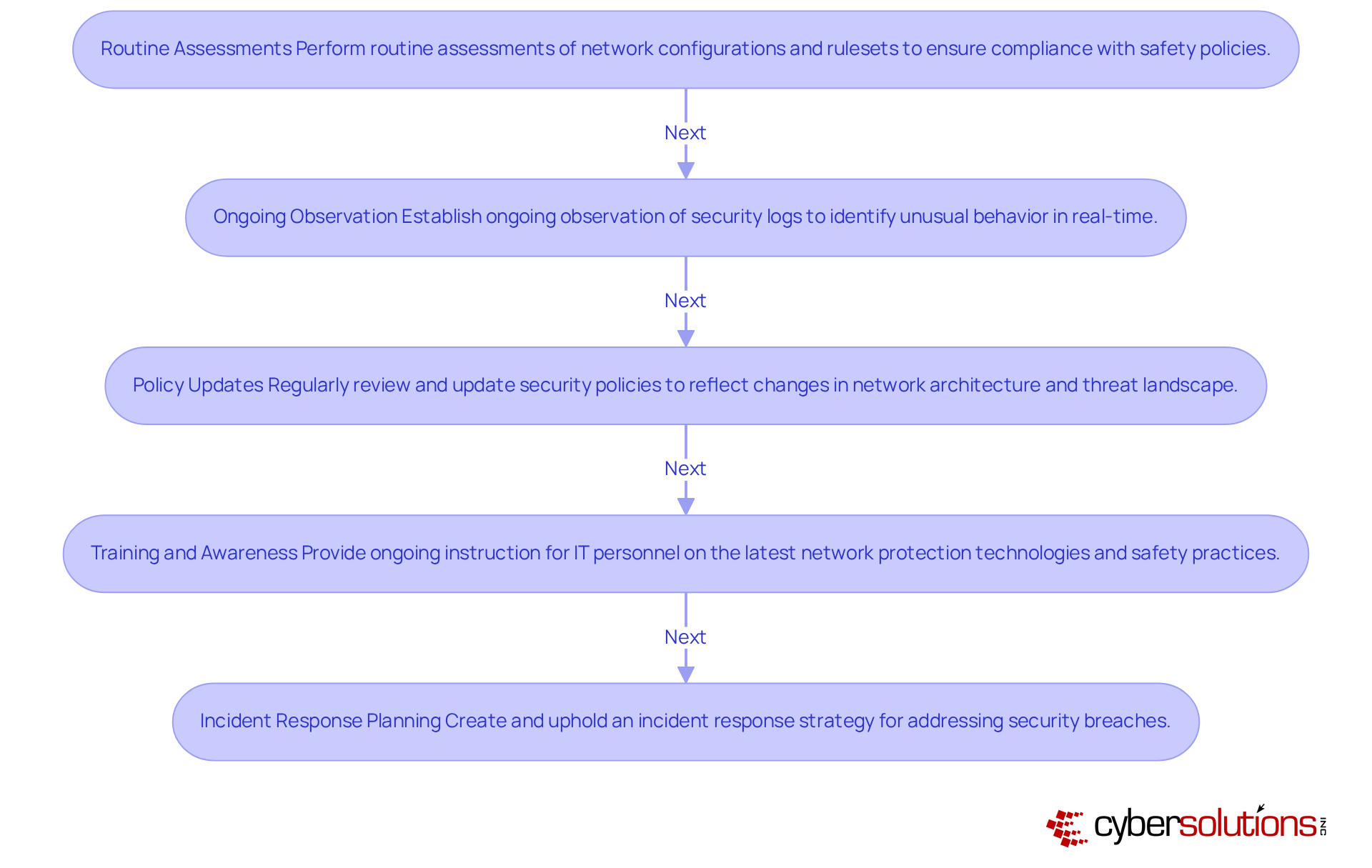
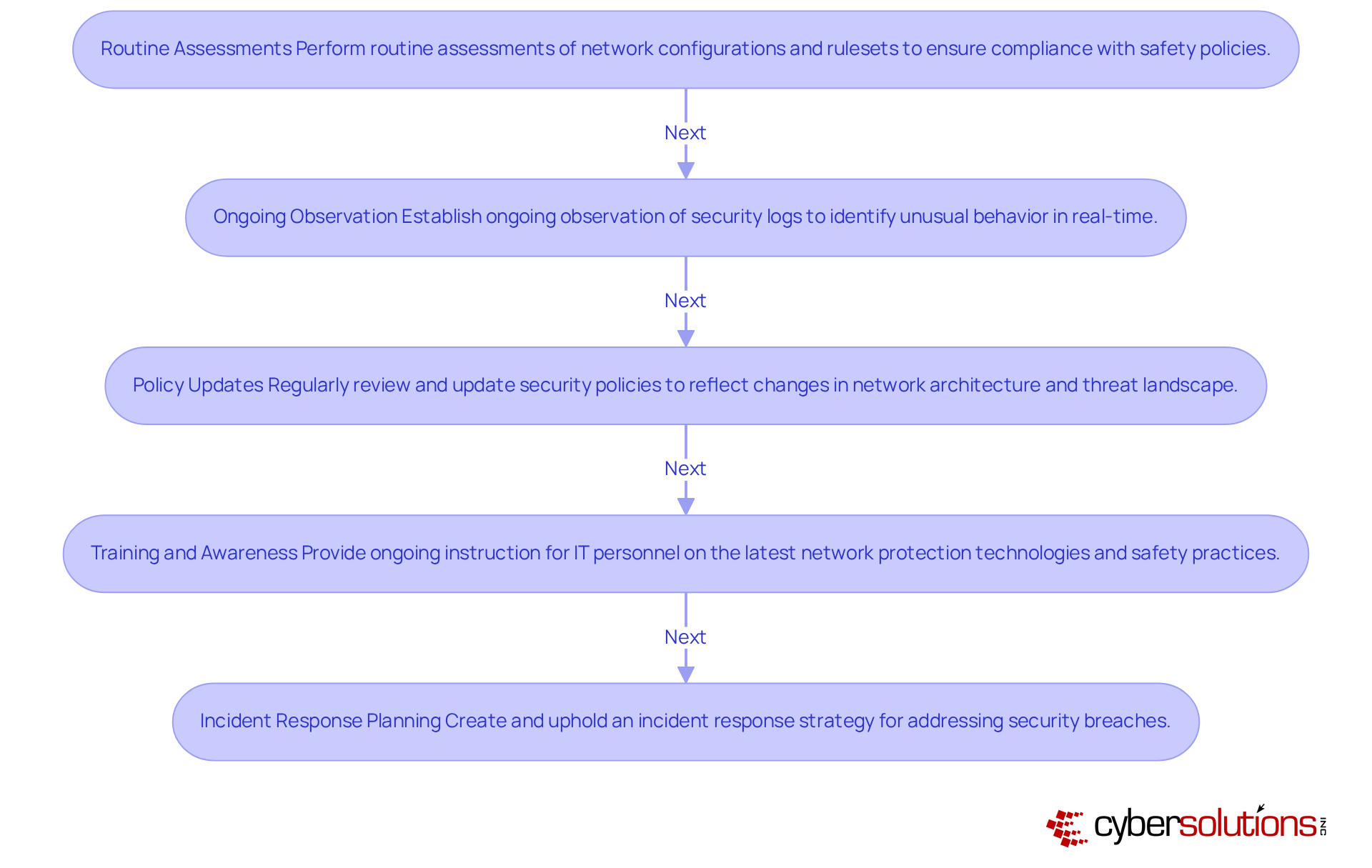
Adopt Best Practices for Ongoing Firewall Security and Compliance
In an era where cyber threats loom larger than ever, the healthcare sector must prioritize robust cybersecurity measures to safeguard sensitive patient data. To maintain robust firewall security and ensure compliance, organizations should adopt the following best practices:
- Routine Assessments: Perform routine assessments of network configurations and rulesets to guarantee they conform to safety policies and compliance obligations, such as those specified in Cyber Solutions' Compliance as a Service (CaaS), including standards like HIPAA, PCI-DSS, and GDPR. Identifying deviations early is crucial to addressing potential vulnerabilities.
- Ongoing Observation: Establish ongoing observation of security logs to identify unusual behavior in real-time. Automated tools can aid in examining logs for anomalies, enhancing the ongoing compliance monitoring offered by CaaS and substantially decreasing the chances of incidents.
- Policy Updates: Regularly review and update security policies to reflect changes in the organization’s network architecture and threat landscape. This proactive method guarantees that firewall testing ensures protective measures remain effective and compliant with regulations.
- Training and Awareness: Provide ongoing instruction for IT personnel on the latest network protection technologies and safety practices, including the significance of application allowlisting. This equips personnel to manage and respond to security incidents effectively.
- Incident Response Planning: Create and uphold an incident response strategy that encompasses protocols for addressing security breaches. Leveraging Cyber Solutions' rapid incident response services ensures that entities can react swiftly and effectively to mitigate damage.
Without these essential practices, organizations risk not only their data but also their reputation and trust with patients.
Conclusion
In today's digital landscape, the importance of robust firewall testing in cybersecurity cannot be overstated. By proactively testing and strengthening firewall defenses, organizations can boost their security against ever-changing cyber threats. Embracing best practices in firewall testing helps identify and address vulnerabilities before they can be exploited, safeguarding sensitive data and ensuring compliance with regulatory standards.
This article highlights essential strategies for effective firewall testing, including:
- The significance of penetration testing
- Implementing a structured methodology
- Identifying common vulnerabilities
- Adopting ongoing security practices
Each of these components plays a vital role in mitigating risks, ensuring compliance, and ultimately protecting the integrity of organizational networks. Regular assessments, combined with proactive monitoring and training, create a robust defense against potential breaches.
Organizations must recognize that neglecting firewall testing can lead to serious risks, including:
- Exposing sensitive data to breaches
- Facing hefty fines
- Losing stakeholder trust
By prioritizing firewall security and integrating these best practices into their cybersecurity strategies, businesses can create a strong defense that protects against today’s threats and adapts to future challenges. By taking decisive action now, organizations can secure their future against the relentless tide of cyber threats.
Frequently Asked Questions
What is firewall penetration testing?
Firewall penetration testing is a proactive approach aimed at discovering weaknesses within a network's firewall setup by simulating real-world attacks to identify vulnerabilities that cybercriminals could exploit.
Why is firewall penetration testing important?
It is important for risk mitigation, compliance with regulatory requirements, cost-effectiveness, and improving protection strategies. Regular testing helps organizations detect and address weaknesses, ensuring network security against evolving threats.
How does firewall penetration testing help mitigate risks?
Regular penetration testing allows organizations to identify and address weaknesses before they can be exploited, significantly lowering the likelihood of data breaches. Data indicates that at least one exploitable vulnerability exists in 84% of penetration testing engagements.
What compliance requirements are associated with penetration testing?
Regulatory frameworks such as PCI DSS and HIPAA mandate regular assessments like penetration testing to protect sensitive information. The Cybersecurity Act of 2023 also emphasizes the need for federal agencies to conduct these tests on high-value assets.
How can penetration testing be cost-effective for organizations?
Investing in penetration testing can save organizations from substantial financial repercussions of data breaches, which average over $4.44 million globally. Organizations performing proactive testing save an average of $1.9 million per breach compared to those that do not.
How does penetration testing improve an organization's protection strategy?
By understanding weaknesses in network configurations, organizations can enhance their overall protection strategy, making it more difficult for attackers to gain unauthorized access. This includes utilizing intrusion detection and prevention systems to monitor and block suspicious activity.
What additional services does Cyber Solutions provide to enhance network security?
Cyber Solutions offers advanced threat detection, proactive monitoring, intrusion detection and prevention systems, and secure remote access solutions to protect sensitive company data and improve overall network defense.
List of Sources
- Understand the Importance of Firewall Penetration Testing
- 83 Penetration Testing Statistics: Key Facts and Figures (https://getastra.com/blog/penetration-testing/statistics)
- The Importance Of Firewall Penetration Testing In Your Security Strategy (https://pentestpeople.com/blog-posts/the-importance-of-firewall-penetration-testing-in-your-security-strategy)
- Penetration testing statistics, vulnerabilities and trends in 2026 – Cyphere (https://thecyphere.com/blog/penetration-testing-statistics)
- Penetration Testing Requirement: What U.S. Rules Mandate It in 2026? (https://halock.com/penetration-testing-requirement-what-u-s-rules-mandate-it-in-2026)
- Why Penetration Testing is Important for Your Business in 2026 (https://brightdefense.com/resources/why-penetration-testing-is-important)
- Implement a Structured Methodology for Firewall Testing
- Firewall Testing: Ensuring Your Firewall Functions Properly (https://cymulate.com/blog/firewall-testing)
- Firewall Penetration Testing: Processes and Benefits - OnSecurity (https://onsecurity.io/article/firewall-penetration-testing-processes-and-benefits)
- How to Run a Firewall Test: A Guide | FireMon (https://firemon.com/blog/how-to-run-a-firewall-test)
- Firewall Penetration Testing: A Complete Guide (https://linkedin.com/pulse/firewall-penetration-testing-complete-guide-vikingcloud-xvpwf)
- Firewall Penetration Testing: Strengthen Your Network Security (https://blog.securelayer7.net/firewall-penetration-testing)
- Identify and Address Common Vulnerabilities in Firewalls
- FortiGate Devices Exploited to Breach Networks and Steal Service Account Credentials (https://thehackernews.com/2026/03/fortigate-devices-exploited-to-breach.html)
- SonicWall releases firmware updates for three CVEs (https://scworld.com/news/sonicwall-releases-firmware-updates-for-3-cves)
- Top Cyber Risks in 2026: How to Avoid Hidden Network Vulnerabilities (https://zeronetworks.com/blog/top-cyber-risks-in-2026-how-to-avoid-hidden-network-vulnerabilities)
- Vulnerability Statistics 2026: Key Trends & Data | Indusface (https://indusface.com/blog/key-vulnerability-statistics)
- Cisco Drops 48 New Firewall Vulnerabilities, 2 Critical (https://darkreading.com/vulnerabilities-threats/cisco-48-firewall-vulnerabilities-2-critical)
- Adopt Best Practices for Ongoing Firewall Security and Compliance
- 60% of Enterprise Firewalls Fail Critical Compliance Checks, According to FireMon Insights | FireMon (https://firemon.com/press-room/press-releases/insights-firewall-failure-report)
- Firewall Configuration Best Practices 2026 (https://itsupportguy.au/best-practices-for-firewall-configuration-in-2026)
- Why is Firewall Audit Important? | Valency Networks (https://valencynetworks.com/blogs/why-is-firewall-audit-important)
- How a firewall audit can enhance your security posture | SystemLabs… (https://systemlabs.io/news-and-insights/firewall-audit-security-posture)
- 7 Firewall Management Best Practices in 2026 (https://infraon.io/blog/7-firewall-management-best-practices)