Introduction
In today's digital landscape, the threat of data breaches looms larger than ever, making effective data backup and recovery strategies essential for organizational survival. C-suite leaders can really step up and protect their organizations from the threat of data loss by understanding the critical components of effective data management.
Navigating the complex landscape of data management can be overwhelming for C-suite leaders, especially with the constant evolution of regulations and threats. How can they ensure their strategies not only comply but also enhance business resilience?
Exploring best practices in data backup and recovery reveals the essential steps leaders must take to safeguard their most valuable asset: information.
Understand Data Backup Fundamentals
In an era where data breaches can cripple organizations overnight, safeguarding information is not just a precaution - it's a necessity. Implementing data backup and recovery creates copies of information that protect against loss, corruption, or disasters, ensuring business continuity and compliance with regulatory standards. Key concepts include:
- Types of Data: Identify critical data that requires protection, such as customer information, financial records, and operational data. Comprehending what information is crucial aids in prioritizing recovery efforts.
- Copy Frequency: Determine how frequently copies should take place based on the significance of the information and the organization's operational requirements. Frequent data backup and recovery copies are essential, as 93% of companies that lose access to their information for over 10 days declare bankruptcy within a year. Furthermore, human mistakes are the primary reason for information loss, emphasizing the necessity for strong data backup and recovery plans.
- Storage Solutions: Familiarize yourself with various storage options, including on-premises, cloud, and hybrid solutions. Each has its benefits and drawbacks; for example, cloud solutions provide scalability but necessitate regular assessments to ensure information protection. Significantly, 91% of Managed Service Providers (MSPs) express a need for new tools to improve their data backup and recovery strategies, indicating a consensus on the necessity for ongoing enhancement in backup practices.
- Compliance Requirements: Grasp industry regulations that require specific information protection measures, such as HIPAA for healthcare and GDPR for entities functioning in Europe. Compliance is not just a differentiator; it is a necessity, as nearly 5% of MSPs view compliance effectiveness as a requirement. Compliance As A Service (CaaS) provides businesses with end-to-end solutions to meet these regulatory requirements, including assessments, policy development, monitoring, and audit preparation. This is particularly beneficial for small and medium-sized businesses (SMBs) that need access to enterprise-level compliance expertise without the high cost of hiring in-house compliance staff.
Understanding these fundamentals empowers C-suite leaders to make informed decisions about their information management strategies, including data backup and recovery, to prepare for potential data loss scenarios. As Munu Gandhi, President of IT Solutions at Xerox, asserts, "Achieving true resilience requires a modern strategy that integrates recovery, security, and infrastructure across all platforms." This holistic approach is essential for navigating the complexities of today's regulatory landscape. As we approach World Backup Day, it's crucial to reassess your data backup and recovery strategies to ensure your organization is not just compliant, but also resilient against potential data loss.

Develop a Comprehensive Disaster Recovery Plan
In an era where data breaches and cyber threats are rampant, a robust disaster recovery plan (DRP) is not just an option; it's a necessity for healthcare organizations. A thorough disaster recovery plan (DRP) is crucial for entities to efficiently react to information loss incidents. Key components of an effective DRP include:
- Risk Assessment: This involves identifying potential threats to data integrity, such as cyberattacks, natural disasters, and hardware failures. In 2026, entities must prioritize risk assessment as a foundational element of their disaster recovery strategy, as it aids in anticipating future risks and preparing accordingly.
- Business Impact Analysis: Assessing the potential effects of information loss on business operations is crucial. This analysis allows organizations to focus on what matters most, ensuring that the essential operations are back up and running first.
- Recovery Objectives: Clearly defined Recovery Time Objectives (RTO) and Recovery Point Objectives (RPO) establish the goals for information recovery timelines and acceptable levels of loss. Organizations that implement documented DRPs are better positioned to meet these objectives, with over 80% of IT leaders expressing confidence in their plans.
- Roles and Responsibilities: Assigning specific roles to team members ensures accountability during a disaster recovery scenario. This clarity helps streamline the recovery process and minimizes confusion during critical moments.
- Communication Plan: Creating a strong communication strategy is essential for keeping stakeholders informed during an information loss event. Timely updates can help manage perceptions and maintain trust among employees, customers, and partners.
By integrating these components, C-suite leaders can establish a robust DRP that not only protects information but also enhances overall business continuity. Ultimately, the absence of a well-defined DRP could jeopardize not only sensitive data but also the very trust that underpins healthcare operations.

Implement the 3-2-1 Backup Strategy
In an era where cyber threats loom large, the integrity of healthcare data hangs in the balance, making robust backup strategies essential for survival. The 3-2-1 backup strategy is a widely recommended approach to data protection that involves:
- Three Copies of Data: Maintain three total copies of your data: the original and two backups.
- Two Different Media Types: Store these copies on at least two different types of media (e.g., hard drives, cloud storage) to protect against hardware failure.
- One Off-Site Copy: Keep one spare copy off-site to protect against local disasters, such as fires or floods.
Without a robust backup strategy, organizations risk catastrophic data loss that can cripple operations and damage reputations. By executing this strategy, organizations not only bolster their information security but also ensure they can bounce back quickly from any data loss incidents. Regularly reassessing and updating your data protection processes is crucial to keep pace with evolving business needs and technological advancements.

Regularly Test and Validate Backup Systems
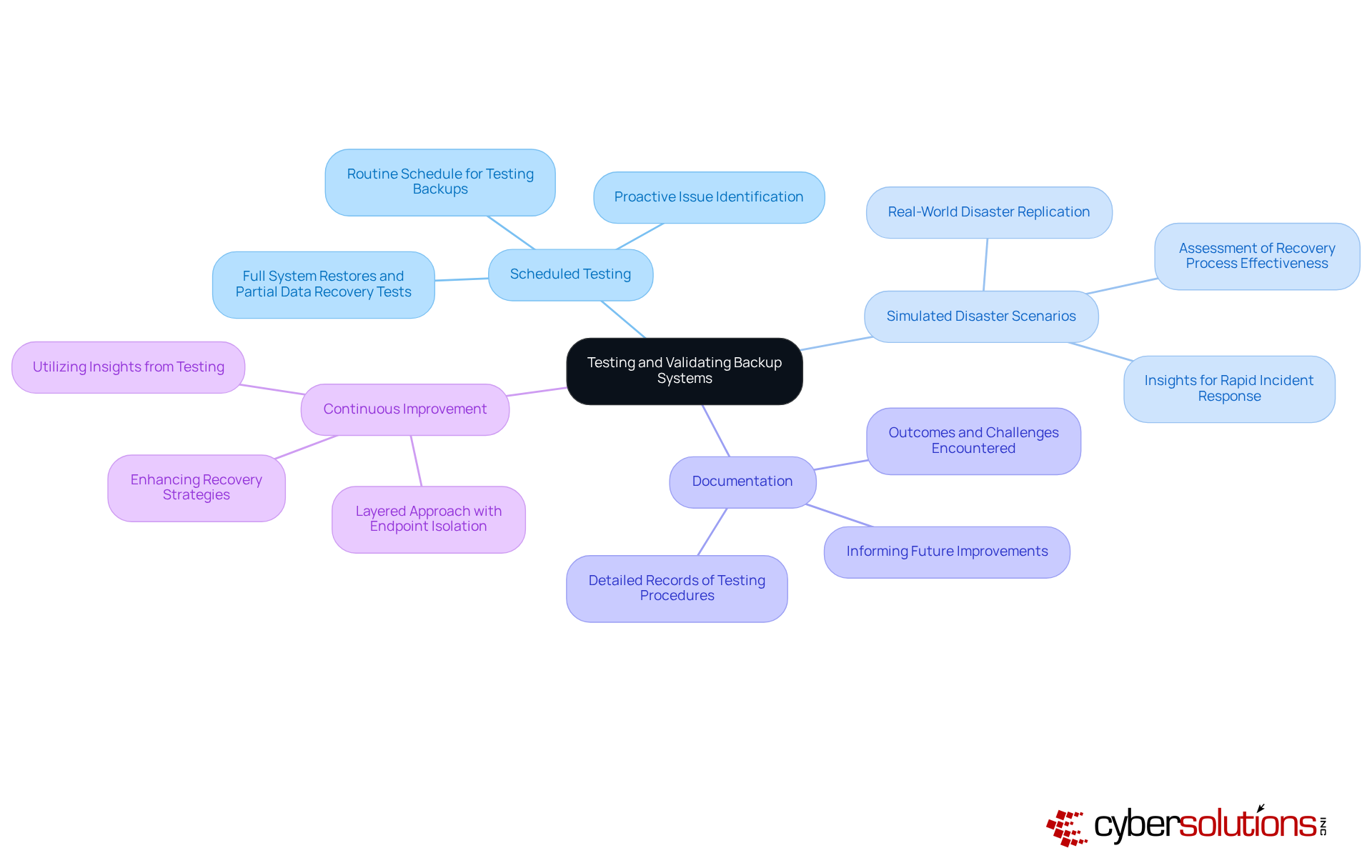
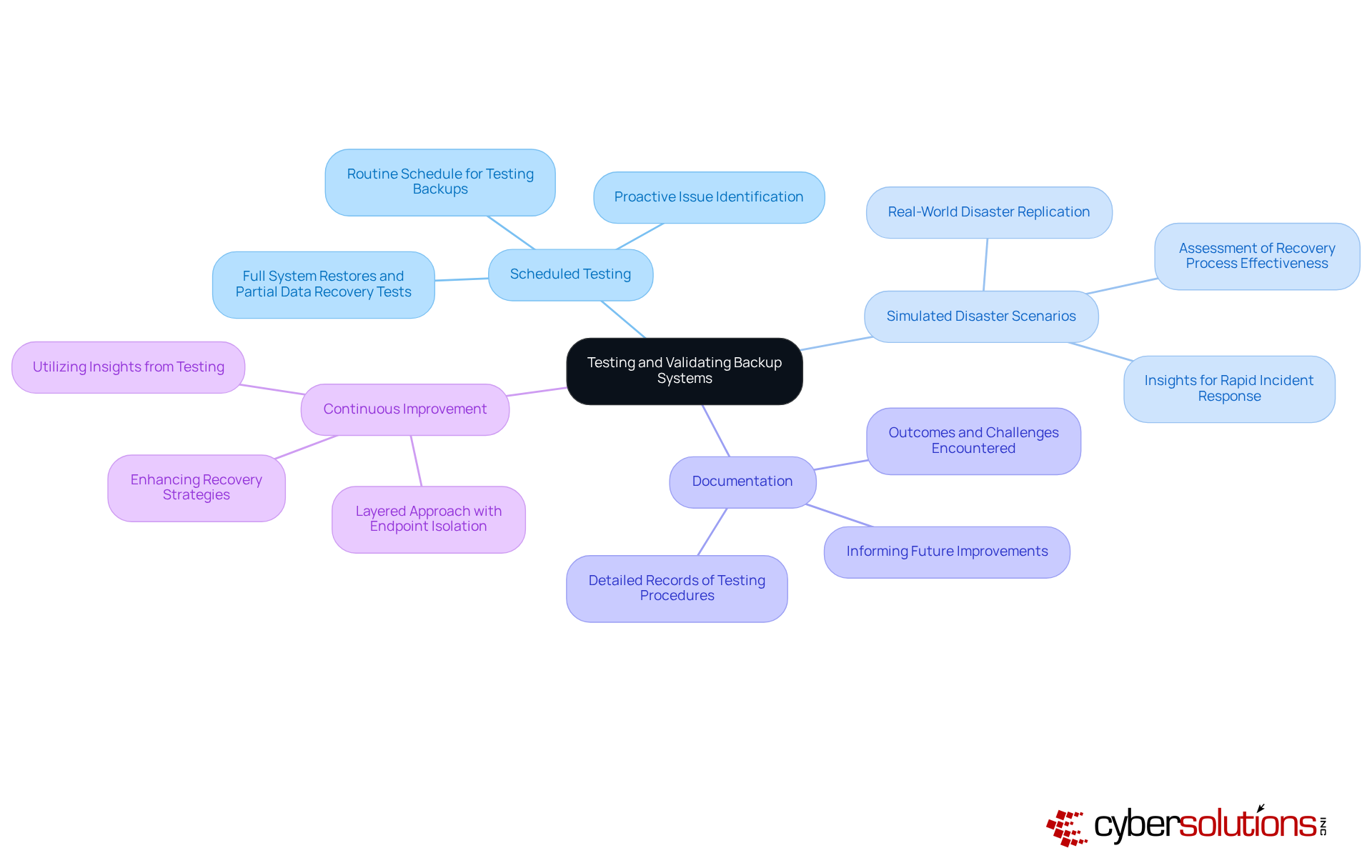
In an era where data breaches are rampant, the integrity of recovery systems is non-negotiable for healthcare organizations. Regular testing and validation of these systems are essential for ensuring data backup and recover integrity and recoverability. Best practices include:
- Scheduled Testing: Implement a routine schedule for testing backups, encompassing both full system restores and partial data recovery tests. This proactive approach helps identify potential issues before they escalate.
- Simulated Disaster Scenarios: Conduct tests that replicate real-world disaster scenarios to assess the effectiveness of the recovery process. Such simulations provide valuable insights into how well the organization can respond under pressure, especially when rapid incident response is critical.
- Documentation: Keep detailed records of testing procedures, outcomes, and any challenges encountered. This documentation is vital for informing future improvements and ensuring accountability.
- Continuous Improvement: Utilize insights gained from testing to enhance recovery strategies and address identified weaknesses. Regular assessments and revisions to the recovery strategy enhance overall resilience, particularly when combined with a layered approach that includes endpoint isolation and malware removal.
Consider this: 76% of organizations are aware they’re not performing data backup and recover for all essential information, a glaring vulnerability that underscores the need for regular testing and validation. With 89% of IT and security professionals indicating heightened worry regarding data security because of AI-driven cyberattacks, the necessity for strong recovery strategies is evident. C-suite executives must guarantee transparency regarding what is safeguarded and how frequently data is saved, as this clarity is crucial for efficient risk management. Furthermore, it is a common misconception that successful backup jobs guarantee recovery; thorough validation beyond just job completion is necessary to avoid potential pitfalls.
By embracing these proactive measures, C-suite leaders can transform potential vulnerabilities into robust defenses against data loss.
Conclusion
In an era where data breaches can cripple organizations overnight, the importance of robust data backup and recovery strategies cannot be overstated. CFOs face unique challenges in safeguarding vital information, balancing compliance with the need for operational efficiency. Executives can strengthen their organizations by:
- Grasping the fundamentals of data backup
- Crafting disaster recovery plans
- Implementing the 3-2-1 backup strategy
Regular testing of these systems is essential to ensure effectiveness.
Key insights covered in this article highlight the importance of:
- Identifying critical data
- Establishing a clear recovery plan
- Employing robust backup methods
Compliance with industry regulations is crucial; it directly affects an organization's reputation and ability to operate effectively. Furthermore, the emphasis on regular testing and validation of backup systems ensures that organizations remain prepared for unforeseen challenges, ultimately enhancing resilience in the face of evolving threats.
With the ever-evolving landscape of data security, C-suite leaders must act decisively to enhance their data management strategies. Ultimately, the choice to invest in data backup and recovery strategies is not just about compliance; it's about securing the future of the organization in an unpredictable digital landscape.
Frequently Asked Questions
Why is data backup important for organizations?
Data backup is crucial for safeguarding information against loss, corruption, or disasters, ensuring business continuity and compliance with regulatory standards.
What types of data should organizations prioritize for backup?
Organizations should identify and prioritize critical data such as customer information, financial records, and operational data for protection.
How often should data backups occur?
The frequency of data backups should be determined based on the significance of the information and the organization's operational requirements, as frequent backups are essential to mitigate the risk of data loss.
What are the consequences of not having a data backup plan?
Companies that lose access to their information for over 10 days declare bankruptcy within a year, highlighting the critical need for strong data backup and recovery plans.
What storage solutions are available for data backup?
Various storage options include on-premises, cloud, and hybrid solutions, each with its benefits and drawbacks. For instance, cloud solutions offer scalability but require regular assessments for information protection.
What is the importance of compliance in data backup?
Compliance with industry regulations, such as HIPAA for healthcare and GDPR for entities in Europe, is essential for protecting information. Nearly 5% of Managed Service Providers view compliance effectiveness as a requirement.
What is Compliance As A Service (CaaS)?
Compliance As A Service (CaaS) provides businesses with end-to-end solutions to meet regulatory requirements, including assessments, policy development, monitoring, and audit preparation, particularly beneficial for small and medium-sized businesses.
How can C-suite leaders benefit from understanding data backup fundamentals?
Understanding data backup fundamentals empowers C-suite leaders to make informed decisions about their information management strategies to prepare for potential data loss scenarios.
What is a holistic approach to data backup and recovery?
A holistic approach integrates recovery, security, and infrastructure across all platforms, which is essential for navigating the complexities of today’s regulatory landscape and achieving true resilience.
List of Sources
- Understand Data Backup Fundamentals
- March 31 Is World Backup Day. Here’s How To Protect Your Data Now (https://forbes.com/sites/tomcoughlin/2026/03/31/march-31-is-world-backup-day-protect-your-data-now)
- World Backup Day 2026: Strengthen Business Data Protection Strategy (https://dsbls.com/resources/world-backup-day)
- World Backup Day 2026: Do You Really Know Your Backup Basics? (https://gosymply.com/world-backup-day-2026-do-you-really-know-your-backup-basics)
- Data Backup Solutions Statistics: USA 2025 / Infrascale (https://infrascale.com/data-backup-solutions-statistics-usa)
- Develop a Comprehensive Disaster Recovery Plan
- Press Releases | DRI International (https://drii.org/pressreleases/details/f9ea6da53c32/dri-international-releases-11th-annual-predictions-report-highlighting-risk-and-resilience-trends-for-2026)
- 96% of Organizations With Disaster Recovery Plan Fully Recover Afterward (https://eiscg.com/96-of-organizations-with-a-disaster-recovery-plan-fully-recover-afterward)
- Future of Disaster Recovery: Key Trends in 2026 | TierPoint, LLC (https://tierpoint.com/blog/data-protection/future-of-disaster-recovery-as-a-service)
- Disaster Recovery Statistics You Can’t Ignore (https://rcor.com/disaster-recovery-statistics)
- Disaster Recovery Plan for Businesses in 2026 (https://geekssolutions.io/disaster-recovery-plan-2026-guide)
- Implement the 3-2-1 Backup Strategy
- 3-2-1 Backup Strategy Rule and Effectiveness / Infrascale (https://infrascale.com/how-the-3-2-1-backup-strategy-protects-your-data-infrascale)
- World Backup Day: Is the 3-2-1 backup rule still relevant? (https://blog.barracuda.com/2026/03/31/world-backup-day--is-the-3-2-1-backup-rule-still-relevant-)
- Only One in Five Organizations Follow the 3-2-1 Rule for Data Backups (https://hipaajournal.com/only-one-in-five-organizations-follow-the-3-2-1-rule-for-data-backups)
- The backup rule people wish they followed sooner (https://blog.mega.io/the-3-2-1-backup-rule)
- Why the 3-2-1 Backup Rule Still Matters in 2026 (https://itworksme.com/blog/129/itworks-news)
- Regularly Test and Validate Backup Systems
- World Backup Day 2026: 5 backup myths to retire this year (https://wasabi.com/blog/data-management/world-backup-day-2026-5-backup-myths-to-retire-this-year)
- World Backup Day 2026: Expert Insights from the Field (https://solutionsreview.com/backup-disaster-recovery/world-backup-day-2026-expert-insights-from-the-field)
- 2026 Cyber Resilience Trends: Where Confidence Meets Reality (https://solved.scality.com/cyber-resilience-trends-2026)
- What a Real Backup Strategy Looks Like in 2026 - Fantastic IT Solutions (https://fantasticit.com/what-a-real-backup-strategy-looks-like-in-2026)
- World Backup Day 2026: Industry Experts Share Their Insights on Data Protection, Resilience, and the Importance of Backup - VMblog (https://vmblog.com/bylines/world-backup-day-2026-industry-experts-share-their-insights-on-data-protection-resilience-and-the-importance-of-backup)